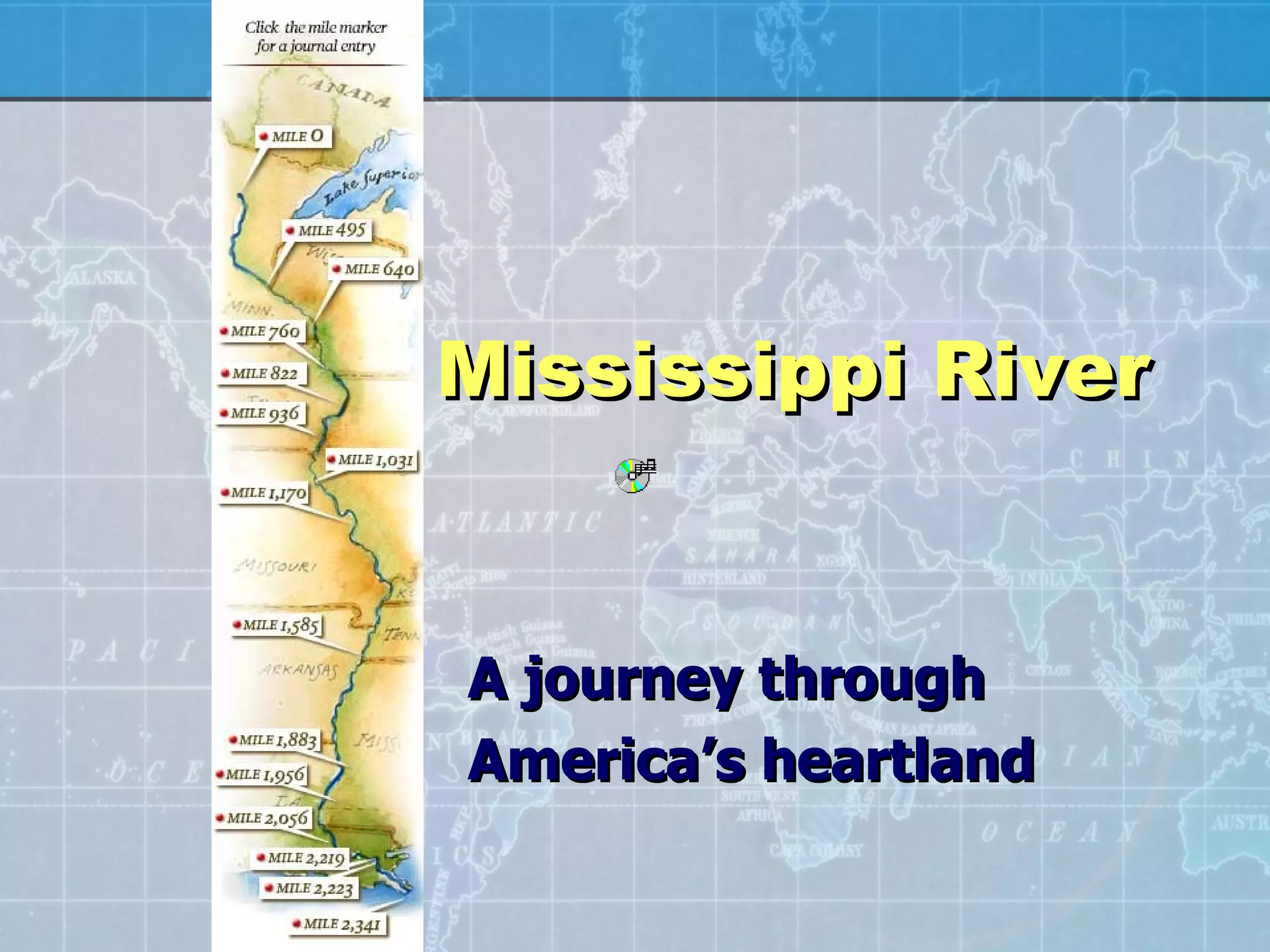
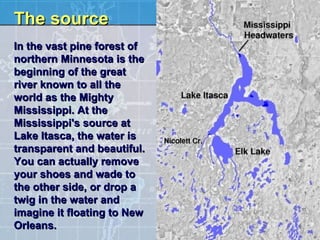
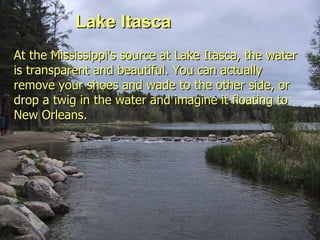
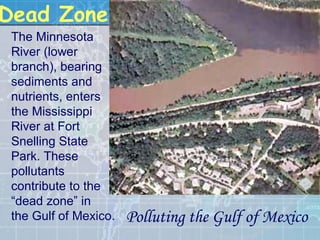
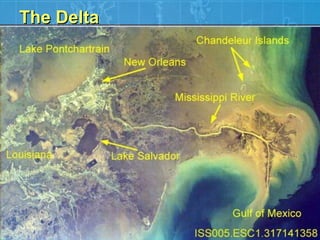
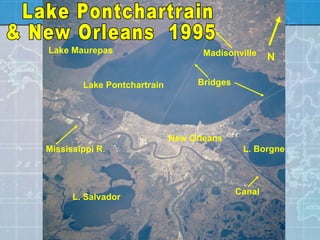
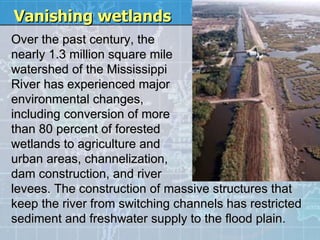
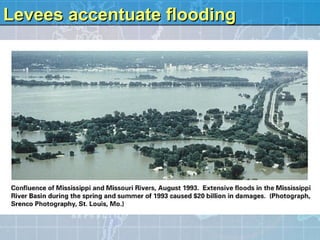
The document summarizes the journey of the Mississippi River from its source at Lake Itasca in Minnesota to its mouth at the Gulf of Mexico. It describes the river's source as clear water where you can wade across. It also tells the legend of Paul Bunyan creating Lake Itasca and the Mississippi River. Additionally, it mentions how development has damaged wetlands and contributed to their disappearance of 25 square miles per year in the Mississippi River delta region.