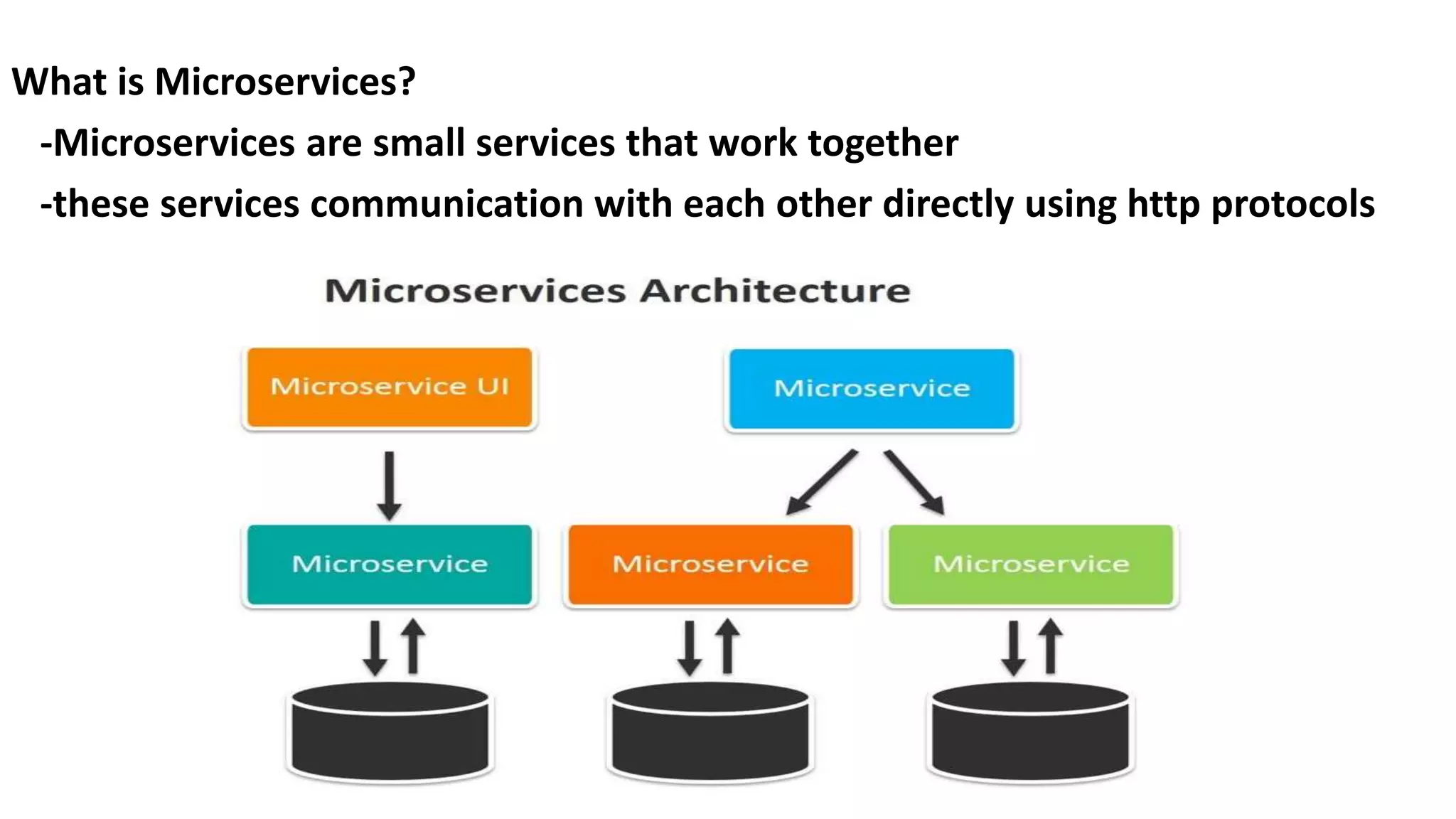
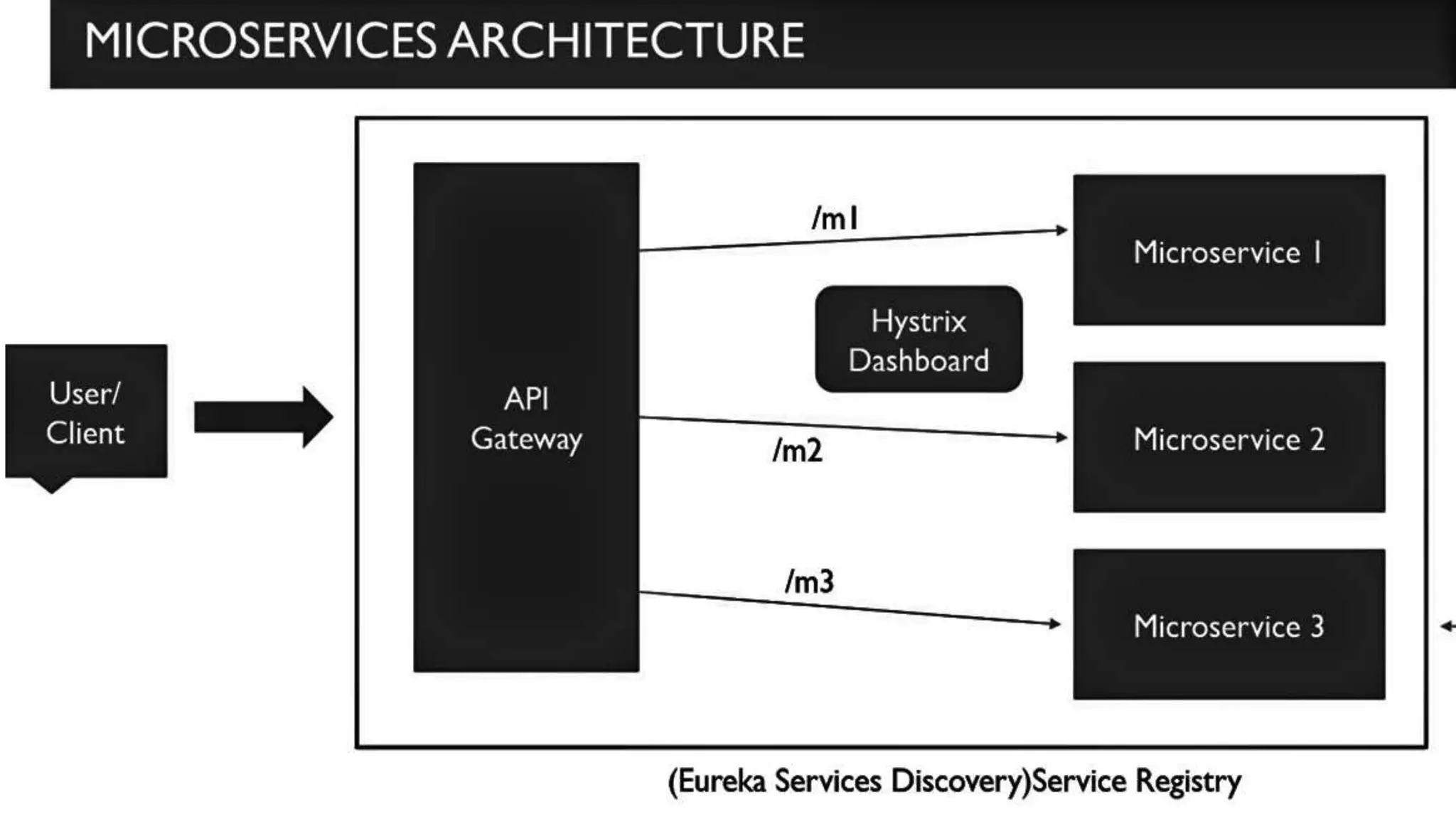
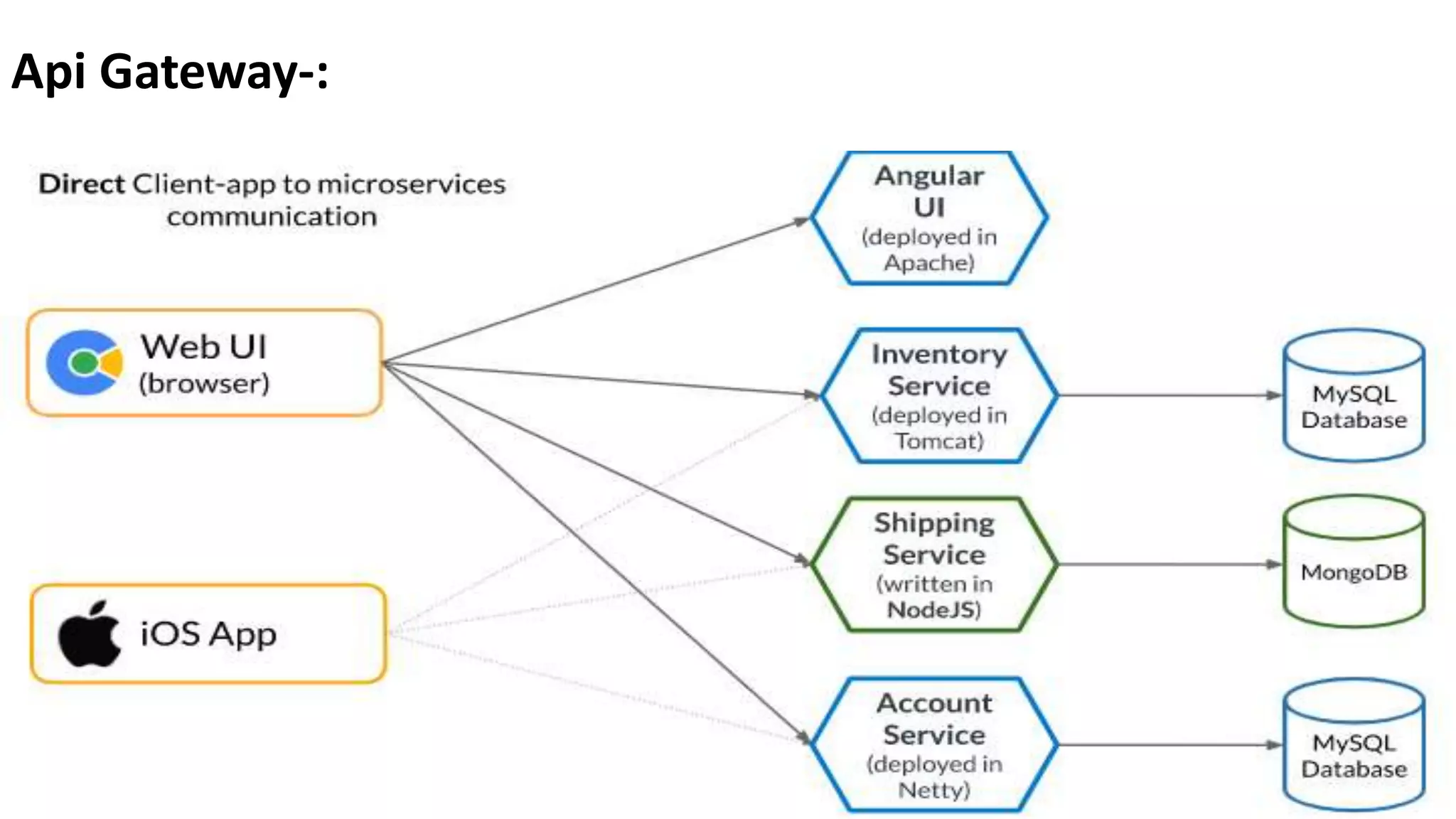
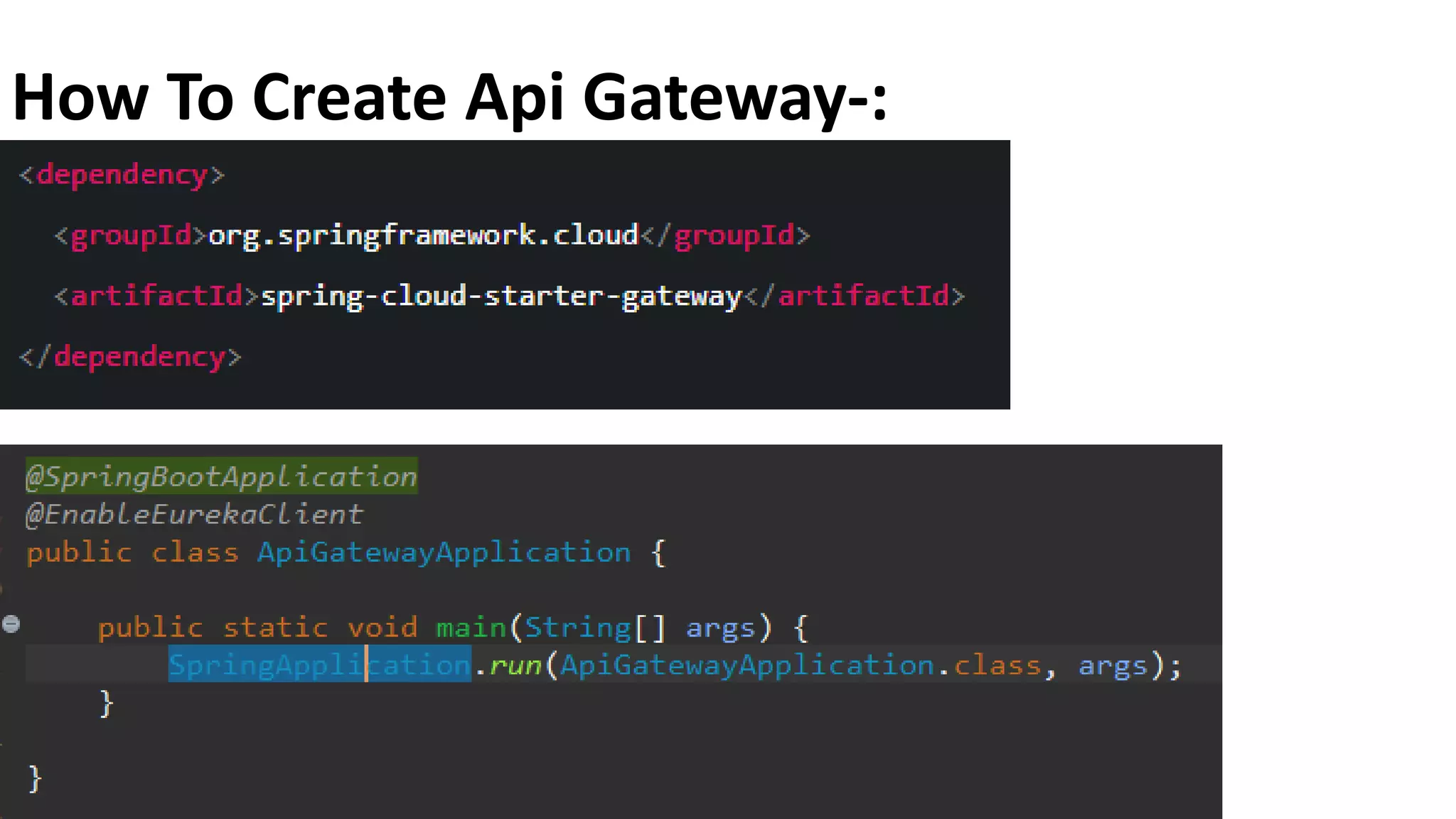
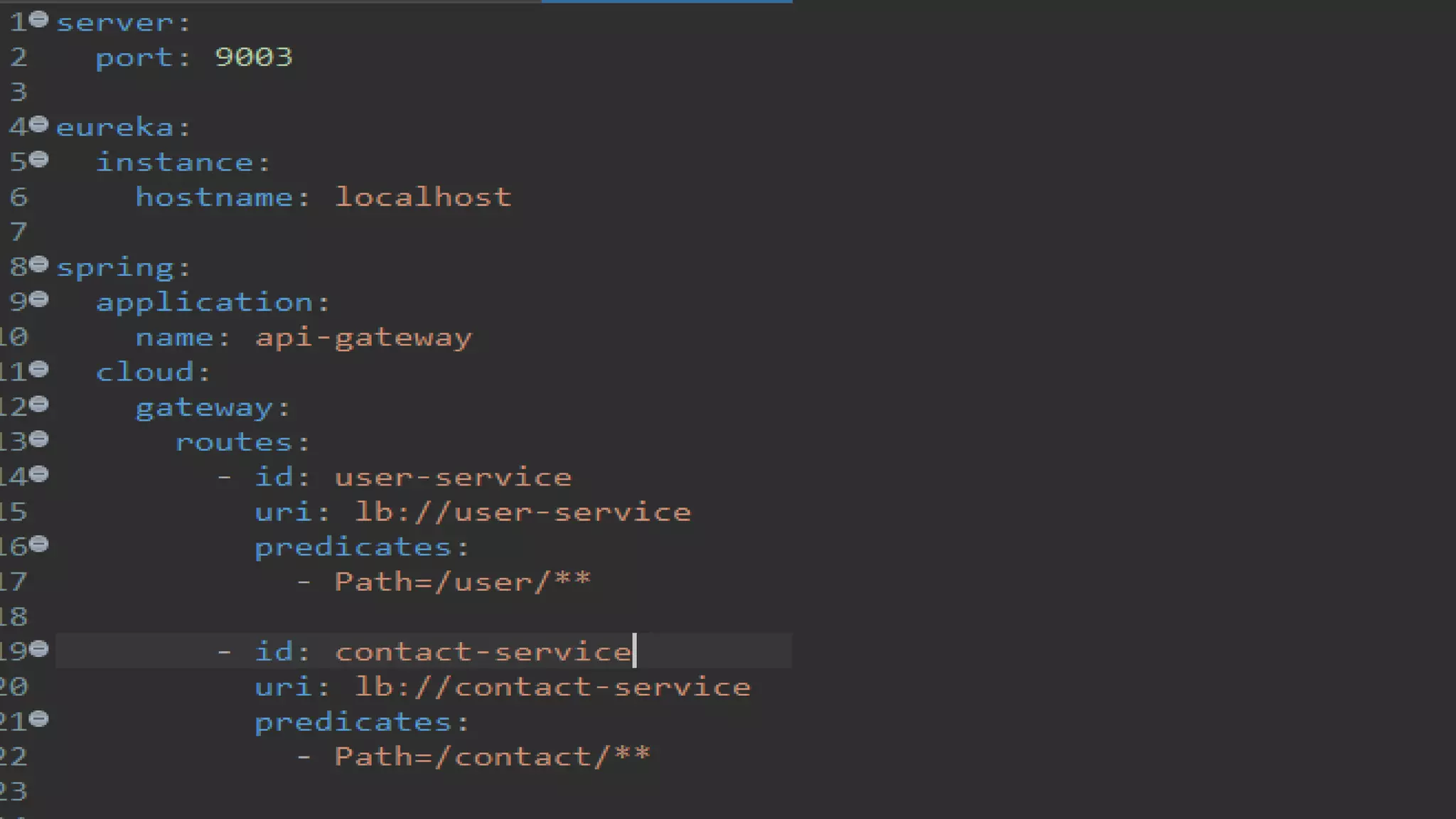
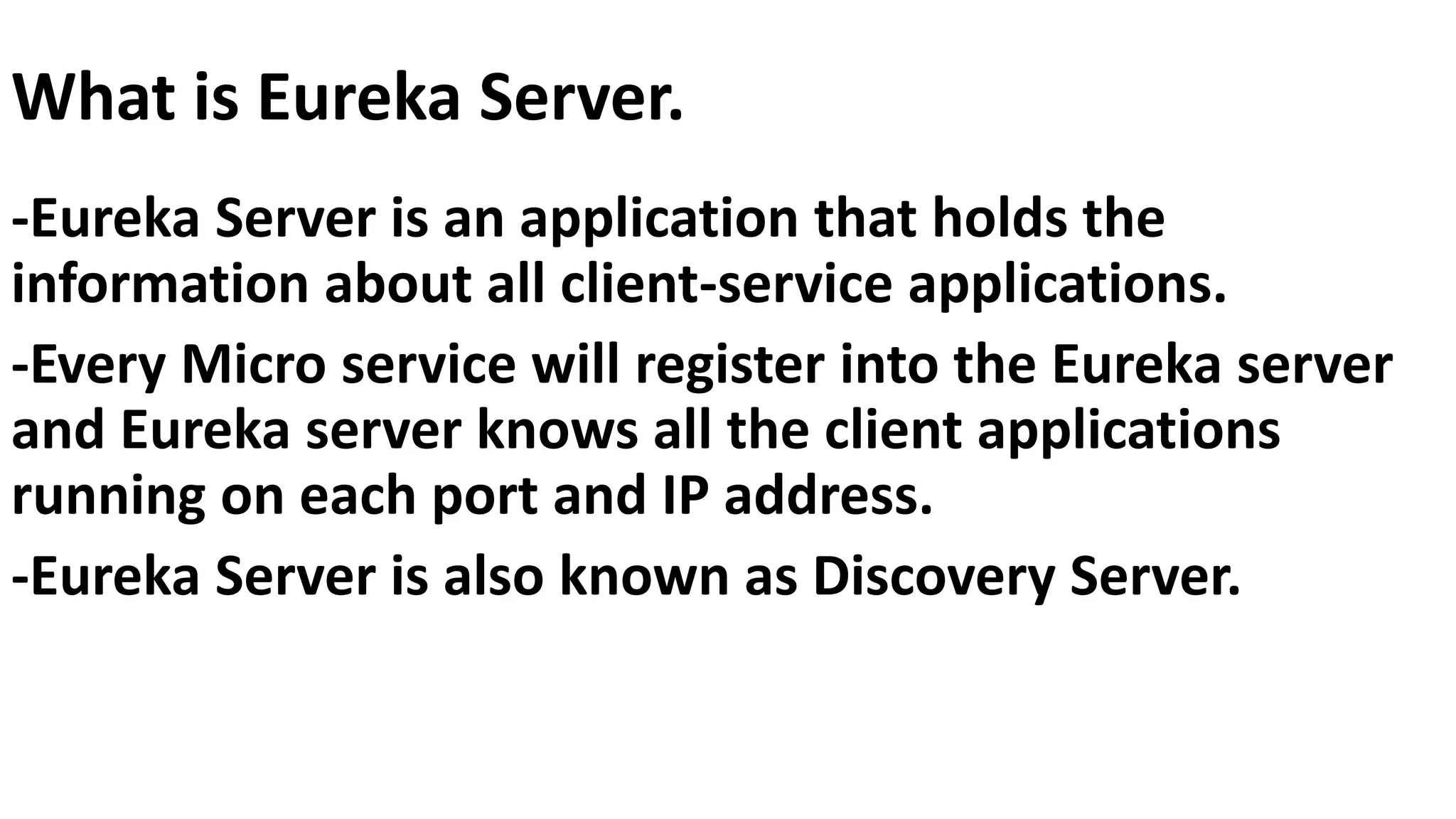
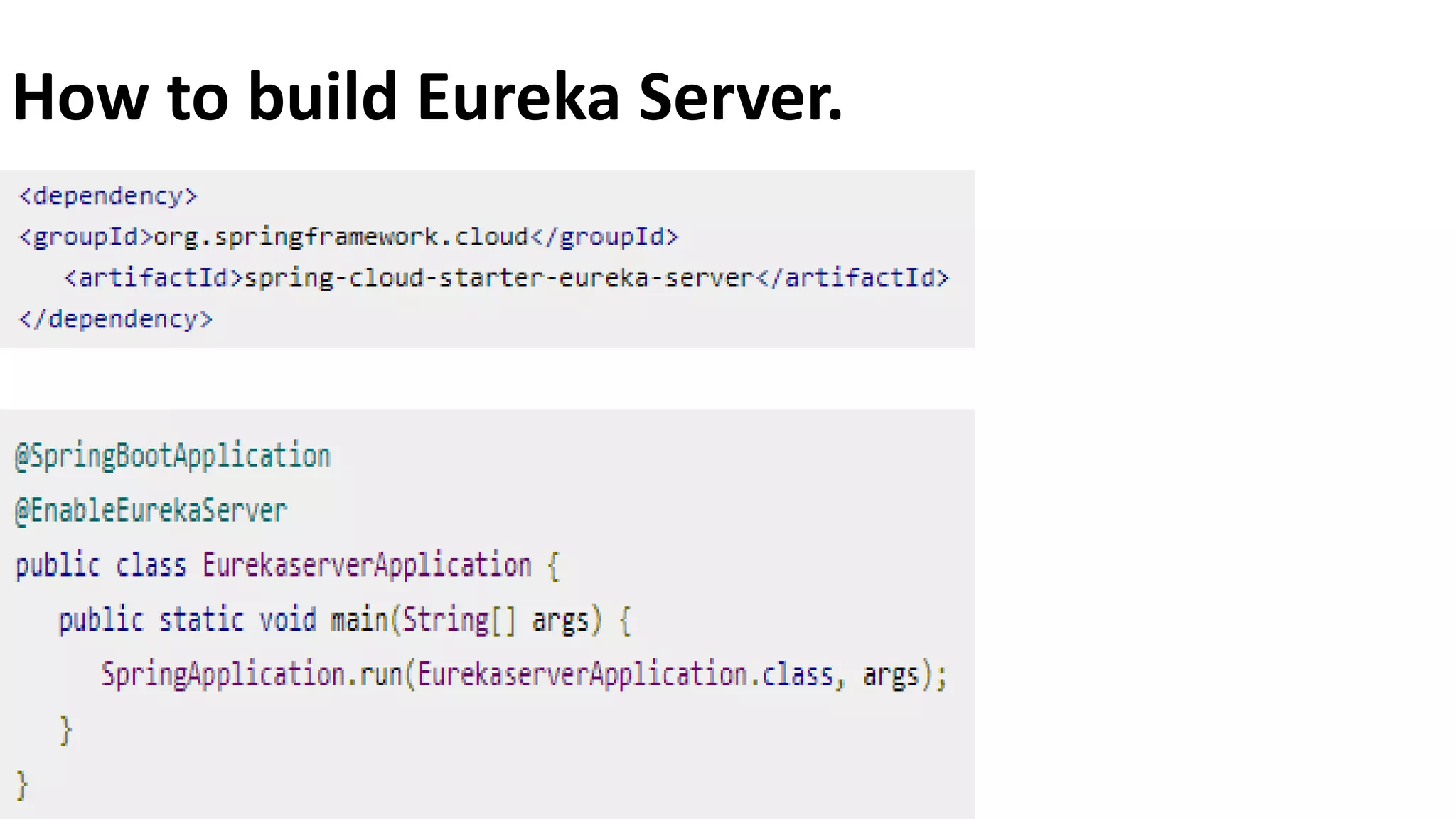
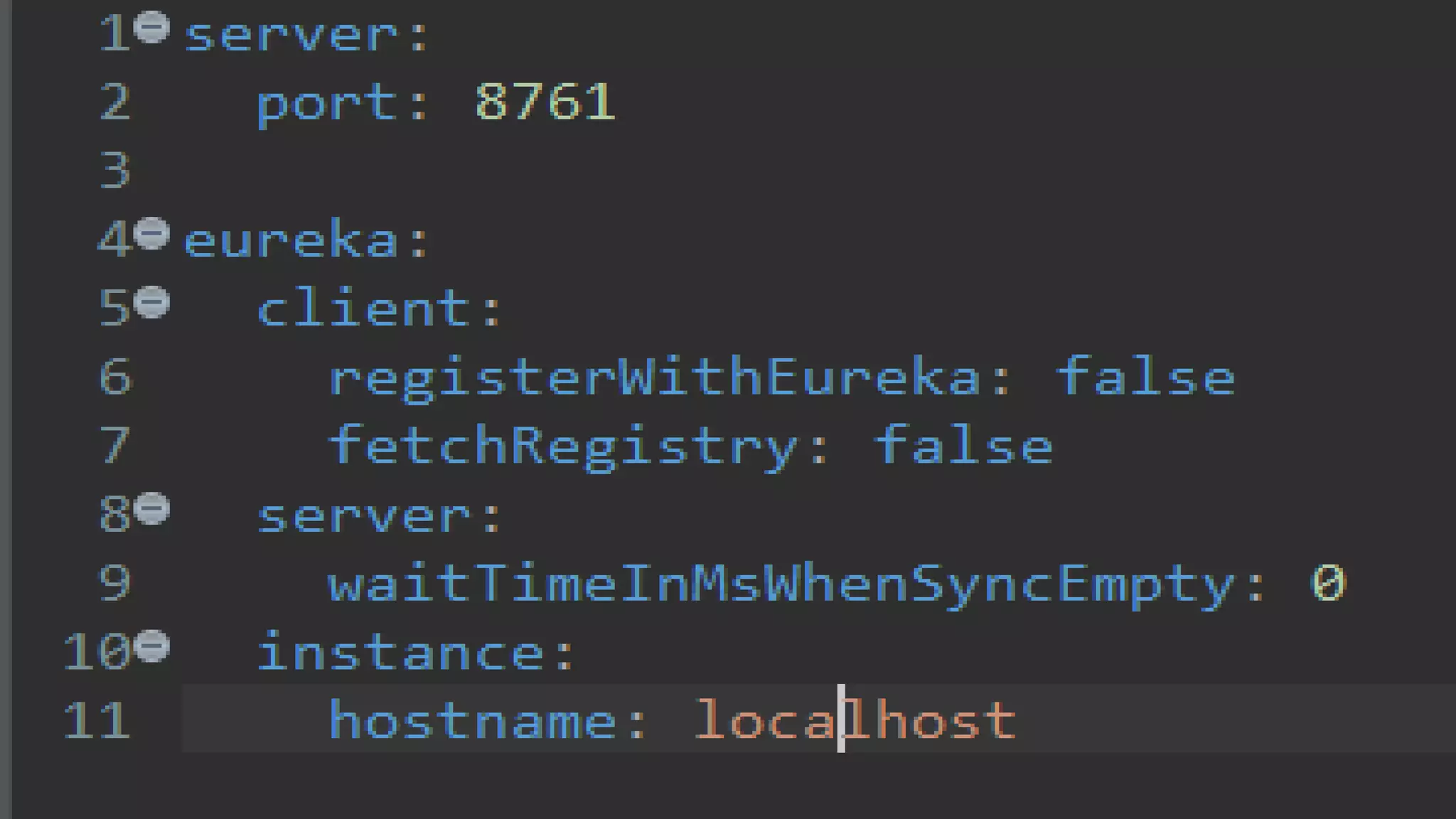
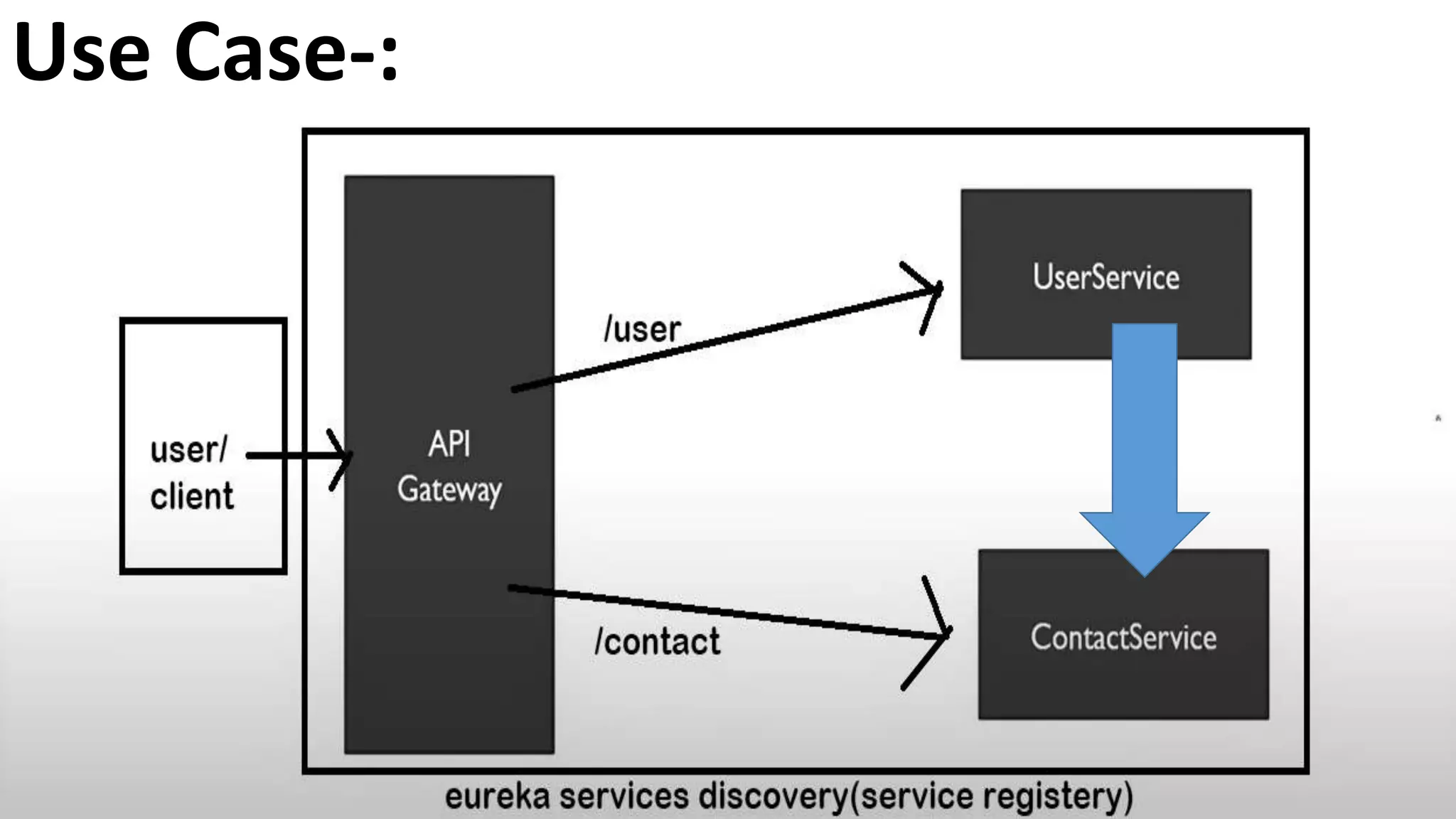
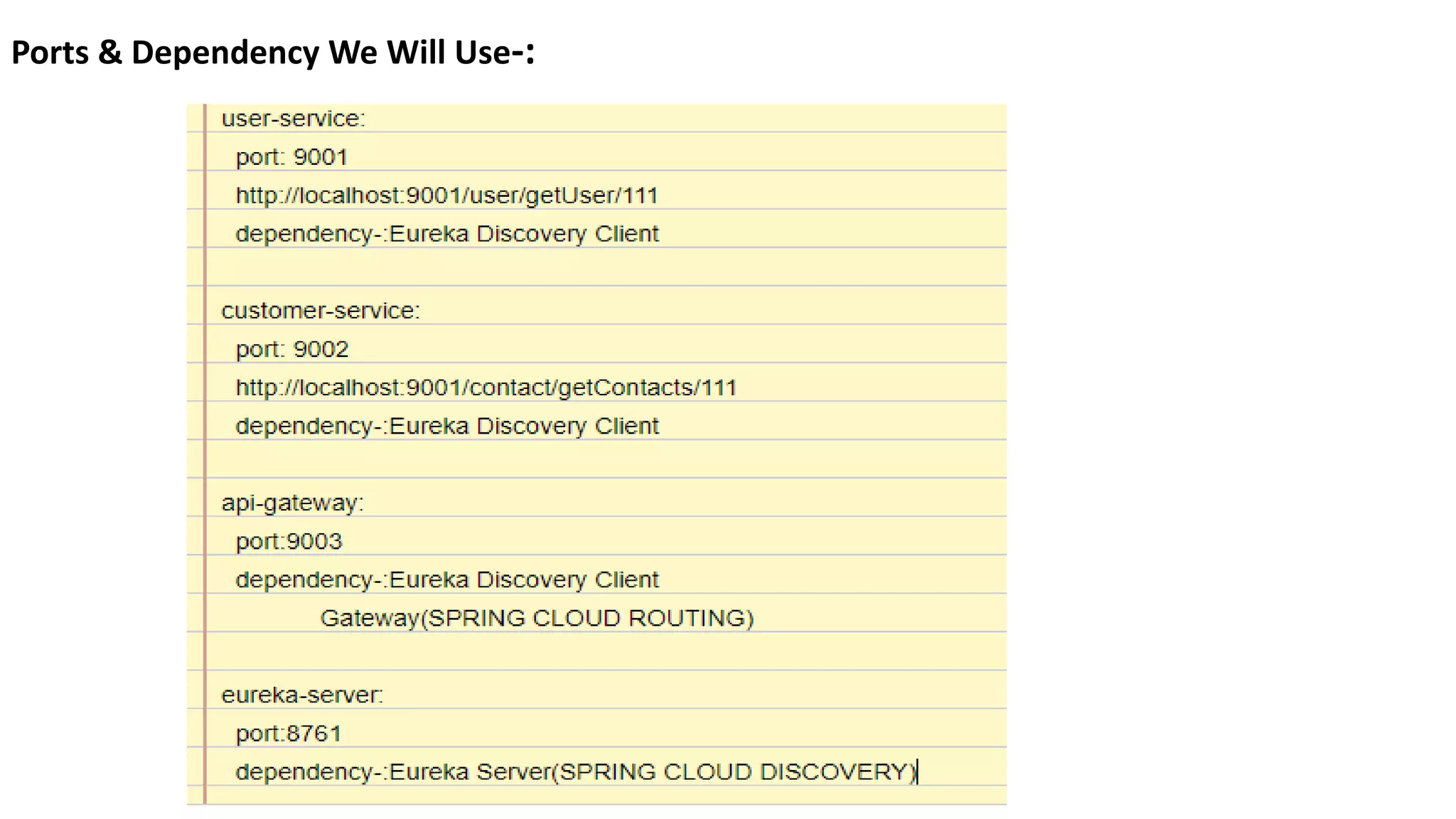
The document discusses various software architecture concepts, primarily contrasting monolithic architecture with microservices architecture. Monolithic applications have a single code base, making deployment simple but challenging for scaling and upgrades, while microservices consist of smaller, independently deployable services that communicate via HTTP, offering improved scalability and less dependency. Additionally, it introduces the API gateway and the Eureka server, which functions as a discovery server, keeping track of client-service applications.