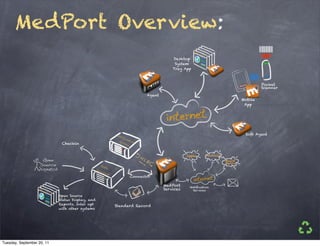
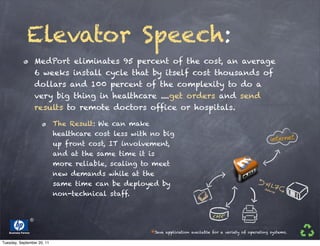
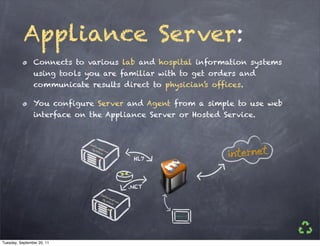
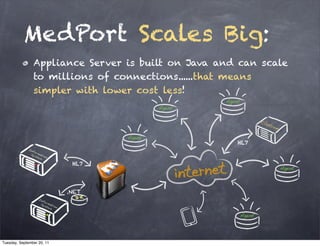
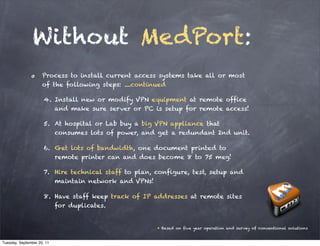
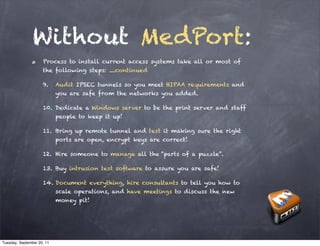
MedPort provides a plug-and-play Agent that automates communication of orders and results between hospitals, labs, and physicians' offices at a fraction of the typical cost and complexity. The Agent eliminates 95% of installation costs and 100% of complexity compared to conventional systems. MedPort scales to support millions of connections through its Java-based Appliance Server.