Math help chapter 1
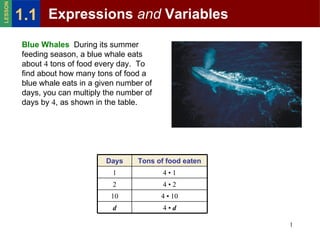
- 1. LESSON 1.1 Expressions and Variables Blue Whales During its summer feeding season, a blue whale eats about 4 tons of food every day. To find about how many tons of food a blue whale eats in a given number of days, you can multiply the number of days by 4, as shown in the table. Days Tons of food eaten 1 4•1 2 4•2 10 4 • 10 d 4•d 1
- 2. LESSON 1.1 Expressions and Variables A numerical expression consists of numbers and operations. In the table, the expression 4 • 10 is a numerical expression. It can also be written as 4 × 10 or 4(10). 2
- 3. LESSON 1.1 Expressions and Variables A numerical expression consists of numbers and operations. In the table, the expression 4 • 10 is a numerical expression. It can also be written as 4 × 10 or 4(10). A variable is a letter used to represent one or more numbers. A variable expression consists of numbers, variables, and operations. 3
- 4. LESSON 1.1 Expressions and Variables A numerical expression consists of numbers and operations. In the table, the expression 4 • 10 is a numerical expression. It can also be written as 4 × 10 or 4(10). A variable is a letter used to represent one or more numbers. A variable expression consists of numbers, variables, and operations. To evaluate a variable expression, substitute a number for each variable and evaluate the resulting numerical expression. 4
- 5. LESSON 1.1 Expressions and Variables EXAMPLE 1 Evaluating a Variable Expression Evaluate the expression 4 • d when d = 120 to find out about how many tons of food a blue whale eats in a feeding season of 120 days. SOLUTION 4 • d = 4 • 120 Substitute 120 for d. = 480 Multiply. ANSWER A blue whale eats about 480 tons of food in 120 days. 5
- 6. LESSON 1.1 Expressions and Variables Study Strategy When you write a variable expression involving multiplication, avoid using the symbol ×. It may be confused with the variable x. 6
- 7. LESSON 1.1 Expressions and Variables EXAMPLE 2 Evaluating Expressions with Two Variables Evaluate the expression when x = 10 and y = 4. x + y = 10 + 4 Substitute 10 for x and 4 for y. = 14 Add. 7
- 8. LESSON 1.1 Expressions and Variables EXAMPLE 2 Evaluating Expressions with Two Variables Evaluate the expression when x = 10 and y = 4. x + y = 10 + 4 Substitute 10 for x and 4 for y. = 14 Add. xy = 10(4) Substitute 10 for x and 4 for y. = 40 Multiply. 8
- 9. LESSON 1.1 Expressions and Variables Writing Variable Expressions You can solve a real-world problem by creating a verbal model and using it to write a variable expression. A verbal model describes a problem using words as labels and using math symbols to relate the words. The table shows common words and phrases that indicate mathematical operations. Common Words and Phrases that Indicate Operations Addition Subtraction Multiplication Division plus minus times divided by the sum of the difference of the product of divided into increased by decreased by multiplied by the quotient of total fewer than of more than less than added to subtracted from 9
- 10. LESSON 1.1 Expressions and Variables EXAMPLE 3 Evaluating a Variable Expression Baseball You plan to divide the 120 players in a baseball league into teams with the same number of players. Use a verbal model to write a variable expression for the number of teams if you know the number of players on each team. SOLUTION Let p represent the number of players on each team. The word divide indicates division. Number of players Number of players Number of teams = in league ÷ on each team = 120 ÷ p 120 ANSWER The number of teams is 120 ÷ p, or p . 10