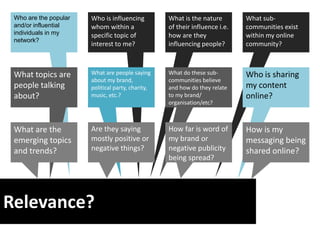
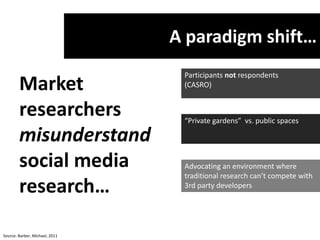
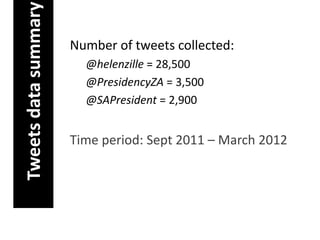
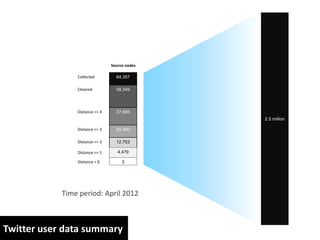
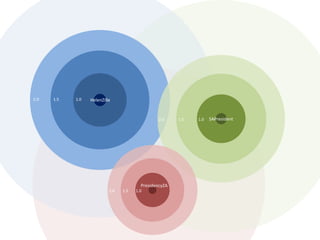
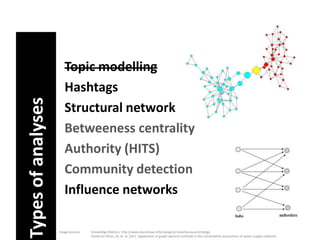
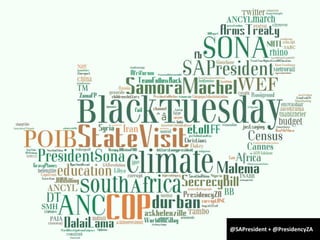
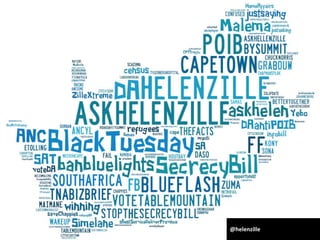
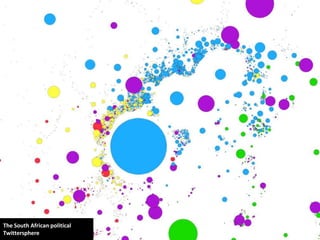
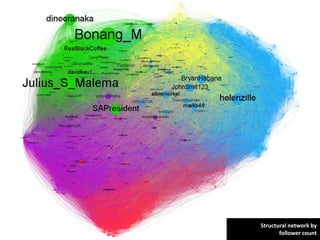
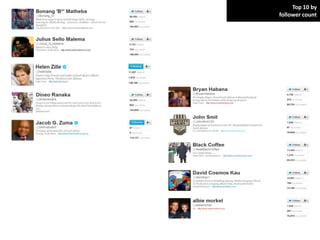
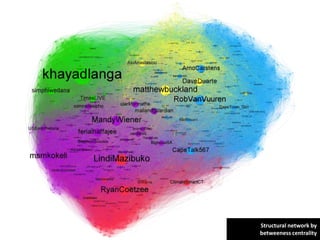
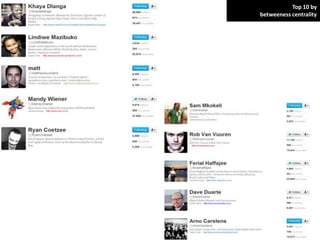
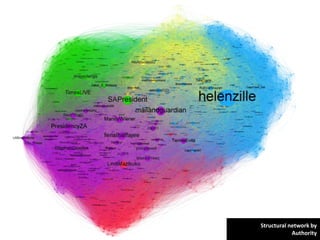
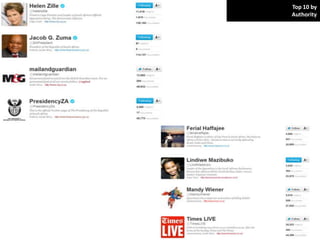
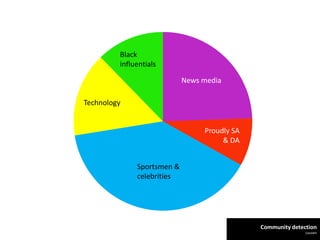
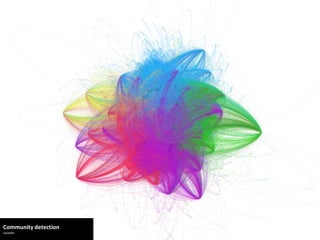
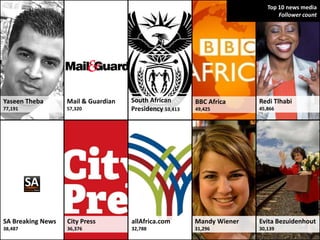
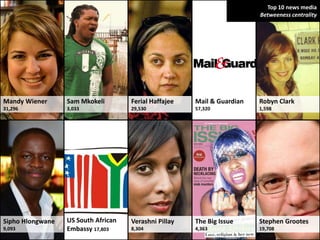
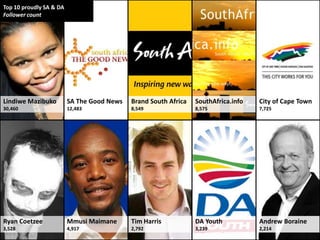
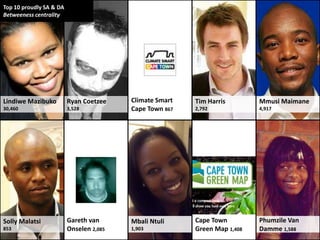
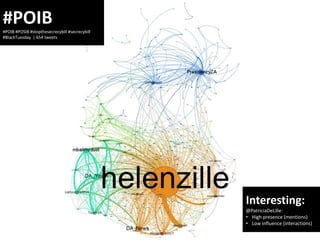
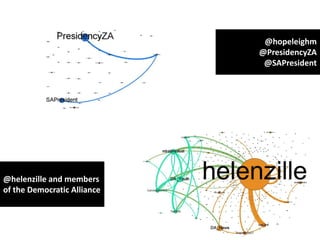
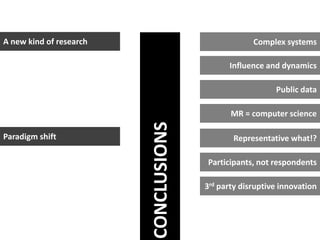
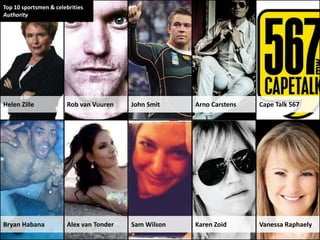
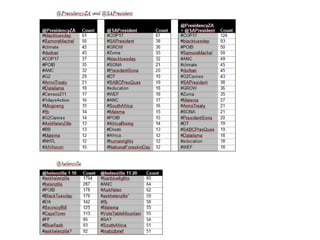
The document analyzes the South African political Twittersphere, examining influential individuals and communities within this online network from September 2011 to March 2012. It provides data on tweet frequency and influence, identifying key figures in politics, sports, technology, and media, while discussing the relevance and impact of these influences on public perception of brands and messaging. The findings highlight a paradigm shift in research methodologies, emphasizing the value of participant-driven data over traditional respondent surveys.