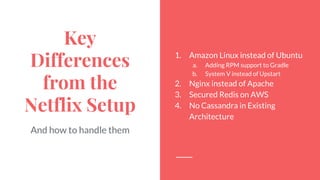
The document outlines the process of setting up Spinnaker at Stitch Fix, detailing the infrastructure and deployment methods utilized in an AWS environment. It covers the installation steps, challenges faced, particularly related to authentication, and differences in configuration compared to other setups, emphasizing the importance of SSL, OAuth2.0, and client certificates. The author shares insights gained from the experience and expresses anticipation for Spinnaker's production use.




![Adding RPM Support to
Gradle
Create the buildRpm block:
● add our rpm repo in /etc/yum.repos.d
on bake machine
● add dependency rpms inside the block
● make sure to build all the other spinnaker
rpms and push to your rpm repo
./gradlew buildRpm
// Ubuntu
buildDeb {
requires('redis-server', '3.0.5', GREATER | EQUAL)
requires('spinnaker-clouddriver')
requires('spinnaker-deck')
requires('spinnaker-echo')
requires('spinnaker-front50')
requires('spinnaker-gate')
requires('spinnaker-igor')
requires('spinnaker-orca')
requires('spinnaker-rosco')
requires('spinnaker-rush')
requires('apache2')
}
// Centos
buildRpm {
requires('sf-nginx')
requires('sf-base')
requires('spinnaker-clouddriver')
requires('spinnaker-deck')
requires('spinnaker-echo')
requires('spinnaker-front50')
requires('spinnaker-gate')
requires('spinnaker-igor')
requires('spinnaker-orca')
requires('spinnaker-rosco')
requires('spinnaker-rush')
os = LINUX # ⇐ YOU NEED THIS MAGIC LINE!
}
[spinnaker] build.gradle](https://image.slidesharecdn.com/makingspinnakergostitchfix-161013010637/85/Making-Spinnaker-Go-Stitch-Fix-15-320.jpg)
![Upstart on
Amazon Linux
Different startup systems:
● We use System V (ancient)
○ service nginx start
○ startup scripts in /etc/init.d
○ chkconfig for starting on bootup
● Spinnaker uses upstart
○ initctl start spinnaker
○ conf files in /etc/init
Another Issue:
● 0.6.5 version of upstart on Amazon Linux which
is way older than 1.4 on Ubuntu
description "rosco"
start on filesystem or runlevel [2345]
# not supported in old version
# so for amazon linux we remove these lines:
setuid spinnaker
setgid spinnaker
expect fork
stop on stopping spinnaker
env HOME=/home/spinnaker exec /opt/rosco/bin/rosco 2>&1
> /var/log/spinnaker/rosco/rosco.log &
[rosco] /etc/init/rosco.conf](https://image.slidesharecdn.com/makingspinnakergostitchfix-161013010637/85/Making-Spinnaker-Go-Stitch-Fix-16-320.jpg)
![Namespace Gate and
Rosco in Nginx
● include /etc/nginx/sites-enabled in main nginx conf
● on deploy, symlink
/etc/nginx/sites-available/spinnaker.conf =>
/etc/nginx/sites-enabled/spinnaker.conf
[spinnaker]
/etc/nginx/sites-available/spinnaker.conf
# all services on the same machine
server {
listen 80;
location / {
root /opt/deck/html;
}
# namespacing gate
location ~* ^/gate/ {
rewrite ^/gate/(.*) /$1 break;
proxy_pass http://localhost:8084;
}
# namespacing rosco
location ~* ^/rosco/ {
rewrite ^/rosco/(.*) /$1 break;
proxy_pass http://localhost:8087;
}
}
ELB
HTTP 80 ⇒ HTTP 80
nginx 80
/ => /opt/deck/html
/gate/health => localhost:8084/health
/rosco/health => localhost:8087/health
EC2
spinnaker.<internal-domain>.com](https://image.slidesharecdn.com/makingspinnakergostitchfix-161013010637/85/Making-Spinnaker-Go-Stitch-Fix-18-320.jpg)
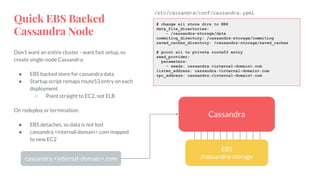
![AWS Elasticache is
Special
AWS Redis won’t let you issue CONFIG
commands!
● Redis version has to be >= 2.8.0
● On AWS elasticache console, add
notify-keyspace-events=Egx
to a new parameter group
○ this enables redis keyspace
events for generic commands
and expired events
● In gate.yml, add
redis.configuration.secure=true
server:
port: ${services.gate.port:8084}
address: ${services.gate.host:localhost}
...
redis:
connection: ${services.redis.connection}
# add the following two lines if using aws redis
configuration:
secure: true
[spinnaker] /config/gate.yml
AWS
Redis 2.8.0
spinnaker
parameter
group
notify-keyspace-events=Egx](https://image.slidesharecdn.com/makingspinnakergostitchfix-161013010637/85/Making-Spinnaker-Go-Stitch-Fix-20-320.jpg)


![Nginx to Terminate
SSL for Deck, Rosco
● Configure nginx with cert and key and turn ssl on
● Nginx now cannot start on bootup - needs
password?
○ Add password to a file, add to nginx
● Now our healthcheck is messed up
○ Add 5000 port for easy ELB healthcheck
● Optional 80 => 443 redirect
● Notice how gate rewrite is gone…
○ has to do with oauth redirects
server {
listen 5000;
location / {
add_header Content-Type text/plain;
return 200 'POOOOOOOOP';
}
}
# optional redirect here
server {
listen 80;
return 301 https://$host$request_uri;
}
server {
listen 443 ssl;
ssl_password_file /etc/keys/spinnaker.pass;
ssl_certificate /opt/spinnaker/ssl/server.crt;
ssl_certificate_key /opt/spinnaker/ssl/server.key;
location / {
root /opt/deck/html;
}
location ~* ^/rosco/ {
rewrite ^/rosco/(.*) /$1 break;
proxy_pass http://localhost:8087;
}
}
[spinnaker]
/etc/nginx/sites-available/spinnaker.conf](https://image.slidesharecdn.com/makingspinnakergostitchfix-161013010637/85/Making-Spinnaker-Go-Stitch-Fix-27-320.jpg)