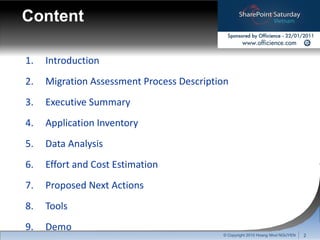
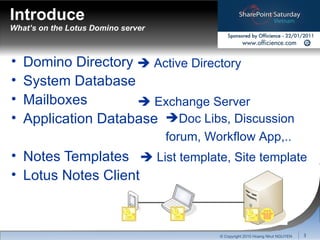
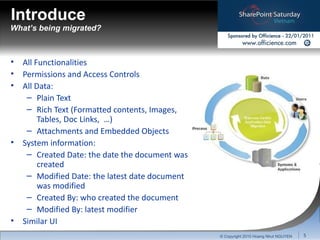
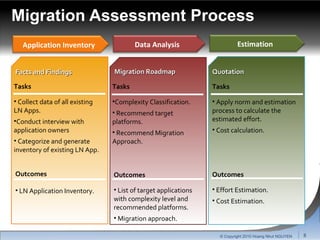
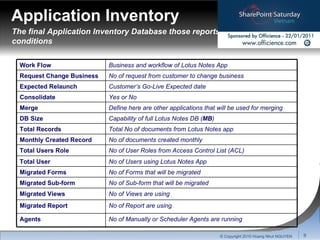
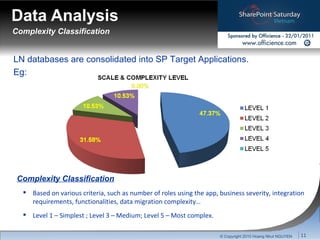
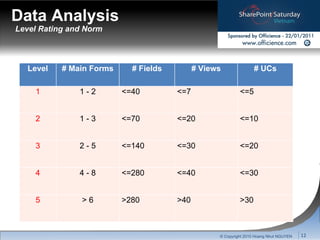
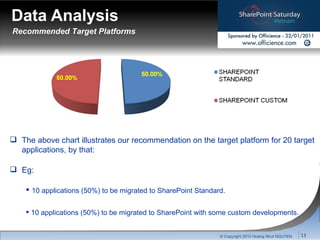
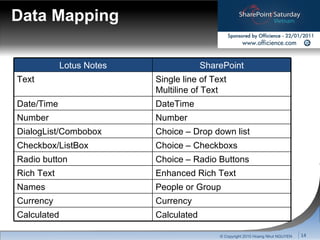
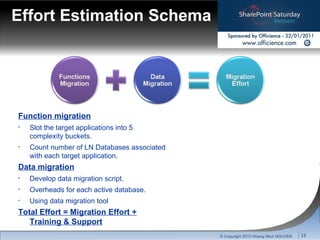
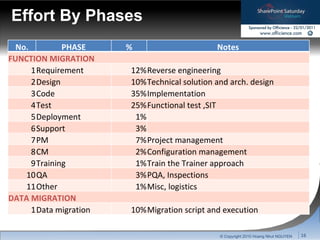
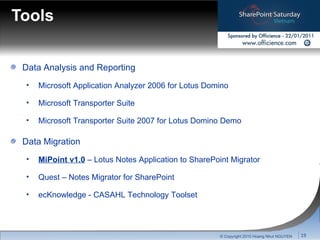
The document outlines the migration process from Lotus Notes to SharePoint, highlighting the necessity and benefits of the transition, including improved collaboration, reduced costs, and efficient workflows. It discusses the assessment and inventory of existing applications, estimating the complexity, efforts, and costs associated with migration. Recommended tools and next actions are also provided to facilitate the transition.