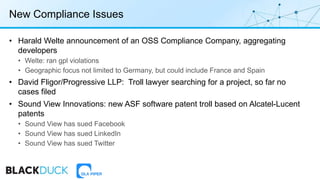
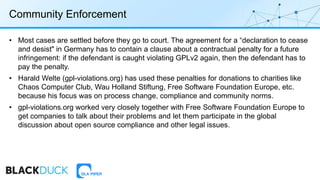
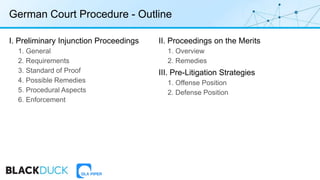
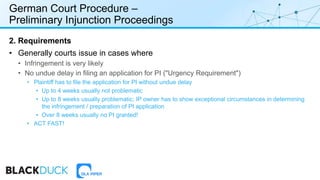
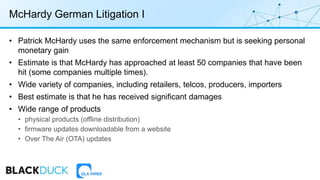
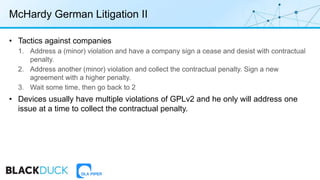
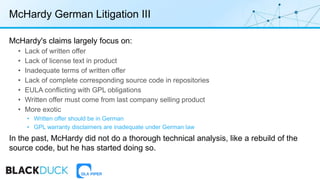
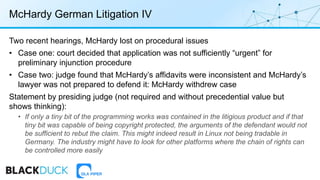
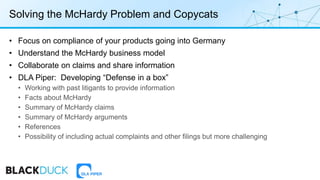
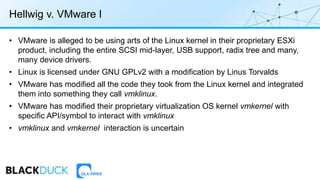
The document discusses the complexities of litigation and compliance within the open source software ecosystem, highlighting risks such as licensing, security, and operational issues that arise from the use of open source code. Key case studies include ongoing legal challenges involving Patrick McHardy, a figure accused of aggressive GPL enforcement tactics, and the VMware litigation regarding alleged GPL violations. It emphasizes the importance of compliance strategies for software distributors, particularly in jurisdictions like Germany, where enforcement actions are more likely.


![Netfilter Project Suspends McHardy
The netfilter project regrets to have to suspend its core team member Patrick McHardy from the core team. This
is a grave step, definitely the first in the projects history, and it is not one we take lightly. Over many months,
severe allegations have been brought forward against the style of his license enforcement activities on parts of
the netfilter software he wrote. With respect to privacy, we will not publicly disclose the content of those
allegations.
Despite many attempts by us to reach him, Patrick has been unable or unwilling to comment on those
allegations or defend against the allegations. The netfilter project does not have first-hand evidence. But given
the consistent allegations from various trusted sources, and in the absence of any response from Patrick, we
feel it is necessary to suspend him until further notice.
We'd like to stress that we do not take any sides, and did not "convict" Patrick of anything. He continues to be
welcome in the project as soon as he is be able to address the allegations and/or co-sign the "principles" [1] in
terms of any future enforcement activities.](https://image.slidesharecdn.com/oct12webinar-updated-161012173612/85/Litigation-and-Compliance-in-the-Open-Source-Ecosystem-7-320.jpg)
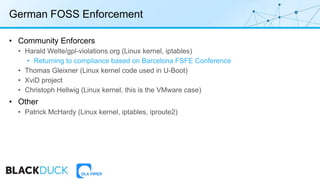


![Linux at 25: Disputes on Compliance
Greg Kroah-Hartman
• "I do [want companies to comply], but I don't ever think that suing them is the right way to do it, given
that we have been _very_ successful so far without having to do that”
• “You value the GPL over Linux, and I value Linux over the GPL. You are willing to risk Linux in order to
try to validate the GPL in some manner. I am not willing to risk Linux for anything as foolish as that.”
Linus Torvalds
• “Lawsuits destroy community. They destroy trust. They would destroy all the goodwill we've built up
over the years by being nice.”
Bradley Kuhn (SFC)
• “You said that you "care more about Linux than the GPL". I would probably agree with that. But, I do
care about software freedom generally much more than I care about Linux *or* the GPL. I care about
Linux because it's the only kernel in the world that brings software freedom to lots of users.”](https://image.slidesharecdn.com/oct12webinar-updated-161012173612/85/Litigation-and-Compliance-in-the-Open-Source-Ecosystem-24-320.jpg)