This document provides an overview of resources for researching EU law at Sheppard Library, including:
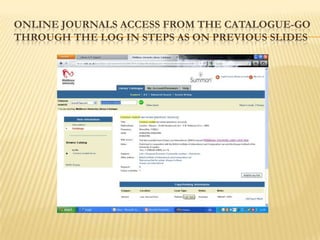
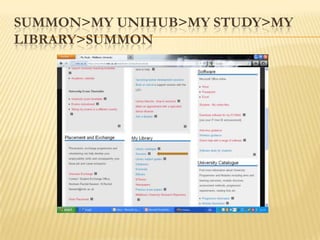
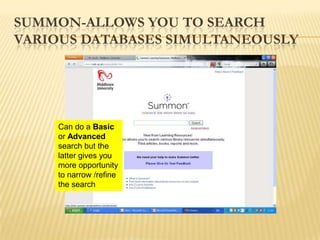
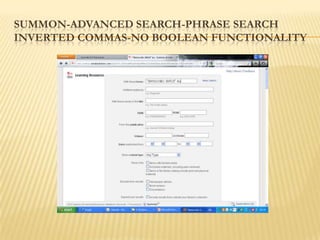
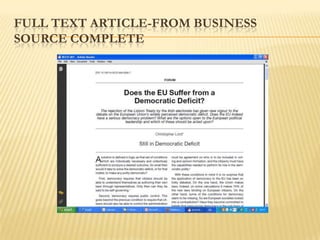
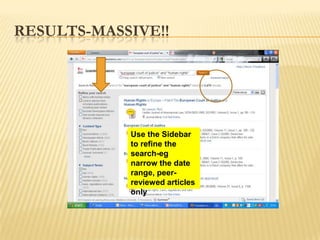
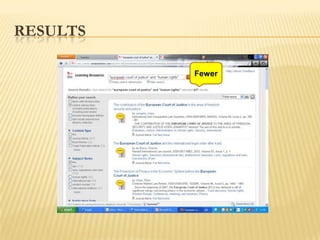
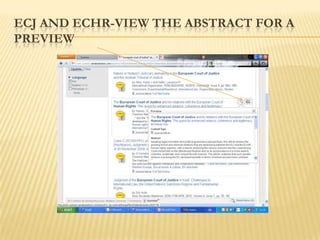
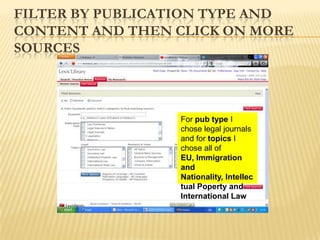
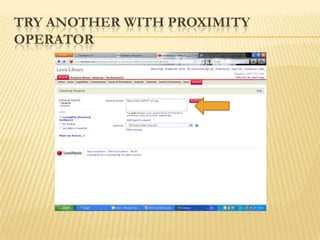
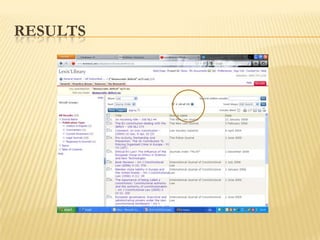
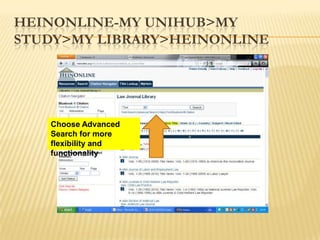
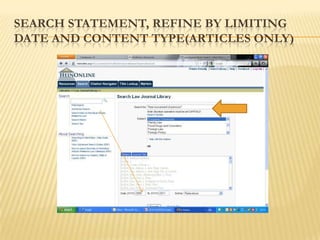
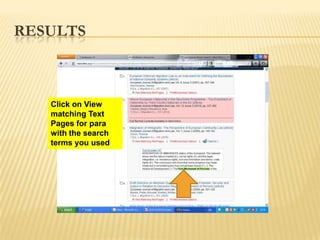
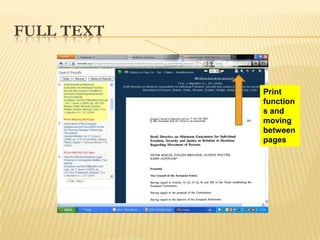
1) Databases like Westlaw International, Lexis Library and HeinOnline for searching journal articles and legal texts. Summon allows simultaneous searching across multiple databases.
2) Websites for current awareness on EU issues, news and information like Europa and the European Information Association.
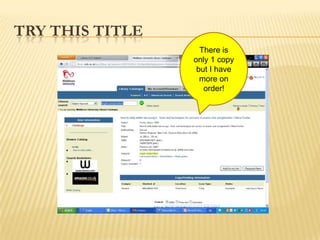
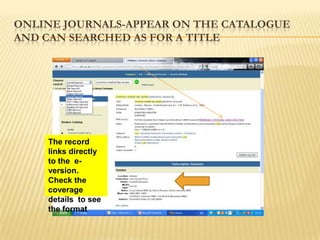
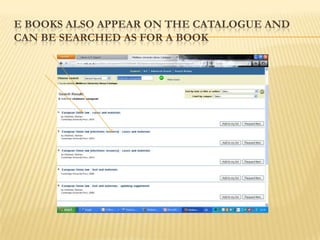
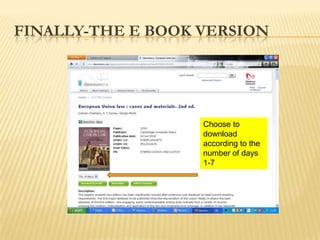
3) Guides on the library catalogue and subject guide for finding relevant e-books, journals and annotated reading lists.
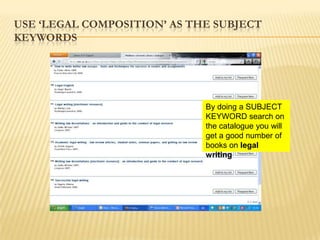
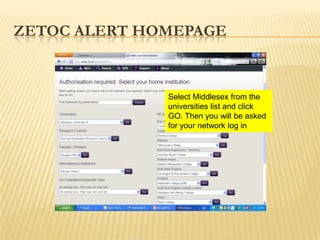
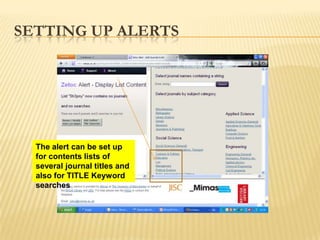
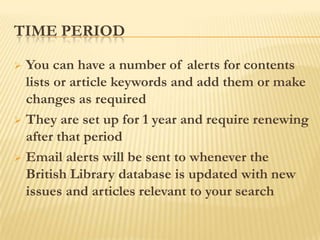
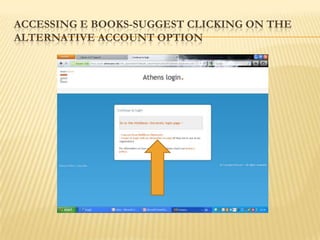
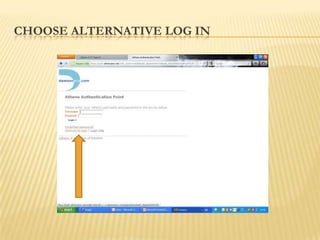
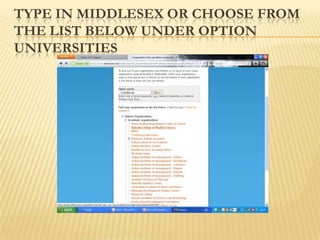
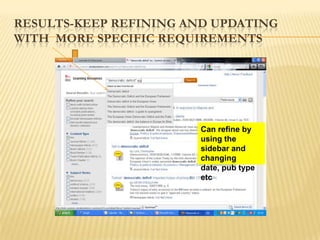
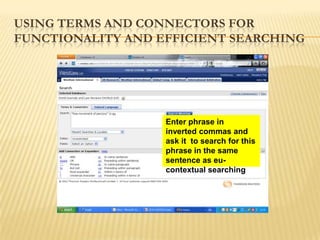
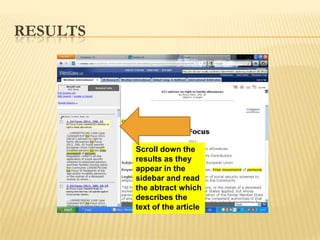
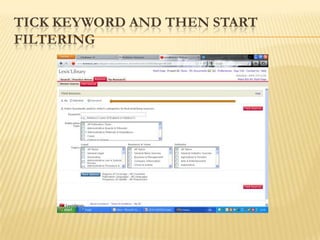
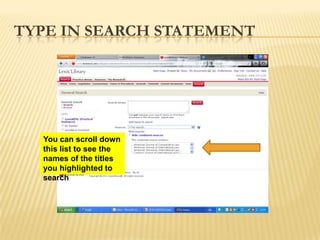
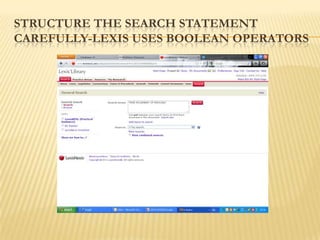
4) Tips on effective literature searching, using subject keywords, setting up article alerts and accessing e-resources through the library login.