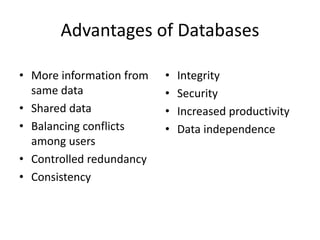
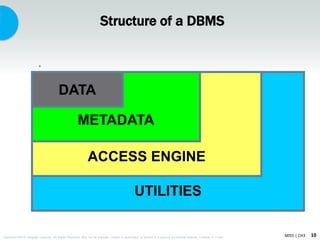
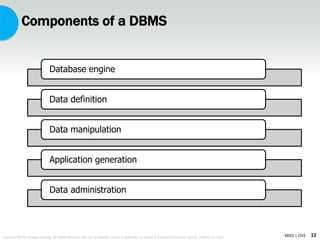
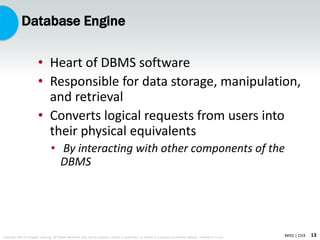
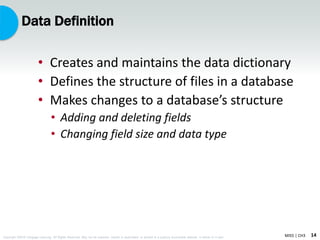
This document discusses database systems and database management systems (DBMS). It defines a database as a collection of related data stored centrally or across multiple locations. A DBMS is software that creates, organizes, and maintains databases to make them more efficient. The key components of a DBMS are the database engine, data definition, data manipulation, application generation, and data administration functions. Logical database design involves how data appears to users and is organized, while physical design refers to how it is stored. The relational model using tables is now dominant. Recent trends include distributed databases, data-driven websites, and object-oriented databases.