The document summarizes legal issues related to data privacy and security breaches. It discusses (1) the relevant cost-benefit analysis that courts consider for data security, (2) examples of court orders regarding document productions and computer forensics in litigation, and (3) that parties are responsible for errors made by their vendors. The document then provides an agenda on legal issues in data privacy and security, including anticipating threats, incident response, and applying relevant laws and frameworks.
![2
“the relevant inquiry here is a cost-benefit analysis, that considers a number of relevant
factors, including the probability and expected size of reasonably unavoidable harms to
consumers given a certain level of cybersecurity and the costs to consumers that would arise
from investment in stronger cybersecurity.” FTC v. Wyndham Worldwide Corp., No. 14-3514,
Slip Op. at 39-40 (3rd Cir. 8/24/2015)
Defendant “has made a supplemental production of the approximately 15,000 additional
documents inadvertently omitted from its prior production. However, at least 500 pages have
been inadvertently omitted from that production as well. No later than August 23, 2010,
defendant … will produce the omitted pages. Defense counsel will personally supervise the
preparation of this production and will assure the completeness of the production.” Chubb
Custom Ins. Co. v. Grange Mut. Cas. Co., No. 2:07-cv-1285 (S.D. Ohio 8/19/10).
“The defendants are to provide [one defendant]’s wife[‘s] computer image to the plaintiffs.
Mr. Dibert will communicate with the defendants’ IT personnel for the information”). PPG
Indus. v. Payne, No. 3:10-cv-73 (E.D. Tenn. 5/21/10).
In re Seroquel Products Liab. Lit., No. 06-md-1769, Slip Op. at 26 (M.D. Fla. 8/21/07) (“a
party is responsible for the errors of its vendors”).
Why Are Lawyers Here?!?!?](https://image.slidesharecdn.com/jun14fbt-talkppt-fbt-180618002918/75/Legal-Issues-in-Data-Privacy-and-Security-Response-Readiness-Before-the-Breach-2-2048.jpg)
![12
What Are The Costs?
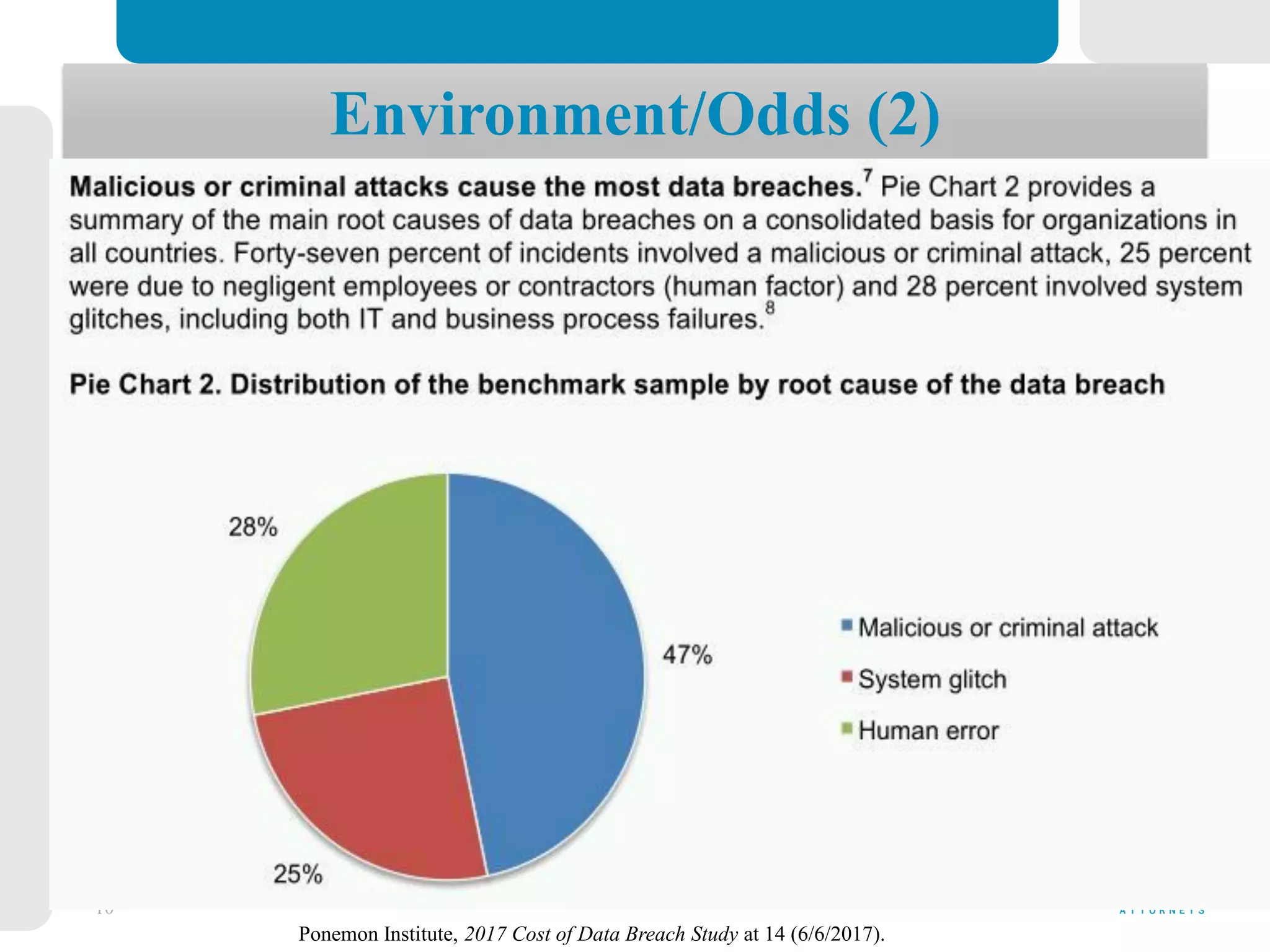
“Almost half of organizations represented in this research (47 percent) identified the root cause of the data
breach as a malicious or criminal attack and the average cost was approximately $156 [per compromised
record]. In contrast system glitches and human error or negligence averaged approximately $128 and $126,
respectively.” Ponemon, supra at 4 (6/6/2017).
“Third party involvement in a breach and extensive cloud migration at the time of the breach increases the
cost.” Id., at 6.
Small to medium-sized businesses may face cyber incident losses ranging in the tens of thousands of
dollars per incident. See The Hiscox Cyber Readiness Report 2017, at 5 (Forrester Research survey found an
average cost per incident of $35,967 for businesses with fewer than 99 employees).
Example cyber insurance annual premiums may range from hundreds (for $1-2 million coverage on a
small business) to more than $40,000 (for $5-10 million coverage on a medium-sized business)
The average cyber insurance claim may average $250,000.
“Expenses/fines related to breach of customer/personal information is the primary driver for purchasing a
cyber insurance policy. Conversely, just 10 percent of respondents identified business interruption as the
primary reason for purchasing the cover.” Information Security And Cyber Risk Management Survey 4
(Advisen/Zurich North America Oct. 2017)](https://image.slidesharecdn.com/jun14fbt-talkppt-fbt-180618002918/75/Legal-Issues-in-Data-Privacy-and-Security-Response-Readiness-Before-the-Breach-12-2048.jpg)
![14
General Legal Duties: Beyond Sectors
Common law fiduciary duties to protect non-public information: Attorney-client; employer-employee … see also,
Savidge v Pharm-Save, Inc., 2017 WL 5986972 (W.D. Ky. 12/1/2017) (“the Court can draw the reasonable inference
that, because [the employee] Plaintiffs' information was released to unauthorized individuals, Defendants breached their
duties to safeguard that information ... Defendants' motion to dismiss will be denied with respect to Plaintiffs'
negligence claim.”); id. (“these facts [of employees providing ‘personal information for tax purposes and to receive
employment and benefits’] are sufficient for the Court to draw the reasonable inference that Defendants impliedly
assented to protect Plaintiffs' information ... Plaintiffs have adequately pled the existence of an implied contract”).
General statutory duty to protect confidentiality of non-public citizen data: “At least 13 states now have general
information security laws that require reasonable measures to protect defined categories of personal information
(including Arkansas, California, Connecticut, Illinois, Maryland, Massachusetts, Nevada, New Jersey, New York,
Oregon, Rhode Island, Texas, and Utah). ... ‘personal information’is usually defined to include general or specific facts
about an identifiable individual.” I. Hemmans & D. Ries, Cybersecurity: Ethically Protecting Your Confidential Data in
a Breach-A-Day World, at 25 (ABA Law Prac. Div. 4/27/2016).
Mandatory, secure disposal of records containing “personal information” when their legal or business retention
has expired. KRS 365.725.
Duty to notify individuals of a data security breach: “All 50 states, the District of Columbia, Guam, Puerto
Rico and the Virgin Islands have enacted legislation requiring private or governmental entities to notify individuals of
security breaches of information involving personally identifiable information.” Nat’l Conf. of State Legislatures
(NCSL), Security Breach Notification Laws, http://www.ncsl.org/research/telecommunications-and-information-
technology/security-breach-notification-laws.aspx (3/29/2018) (last visited 4/17/2018).](https://image.slidesharecdn.com/jun14fbt-talkppt-fbt-180618002918/75/Legal-Issues-in-Data-Privacy-and-Security-Response-Readiness-Before-the-Breach-14-2048.jpg)


![43
(Choice of) Laws & Frameworks
Whose Law Controls?
“Kentucky has adopted the ‘most significant relationship’test to resolve choice of law issues relating to contract
disputes. … ‘[t]he rights and duties of the parties with respect to an issue in contract are determined by the local
law of the state which, with respect to that issue, has the most significant relationship to the transaction and the
parties …’ Kentucky will override the outcome of the ‘most significant relationship’test and apply its own laws
if ‘a clear and certain statement of strong public policy in controlling laws or judicial precedent’would be
violated in applying another state's laws.“ Henry v. Travelers Personal Security Insurance Co., 2016-CA-
001939-MR (Ky. App. 2/2/2018) (unpublished) (citations omitted).
“Some third countries adopt laws, regulations and other legal acts which purport to directly regulate the
processing activities of natural and legal persons under the jurisdiction of the Member States. … extraterritorial
application of those laws, regulations and other legal acts may be in breach of international law and may impede
the attainment of the protection of natural persons ensured in the Union by this Regulation.” GDPR, at Recital
(115).
∑ Is There a Race to an Agency or Courthouse?
What are the Facts Supporting One Choice Over Another?
Does the Framework Provide Early Answers?](https://image.slidesharecdn.com/jun14fbt-talkppt-fbt-180618002918/75/Legal-Issues-in-Data-Privacy-and-Security-Response-Readiness-Before-the-Breach-43-2048.jpg)
![45
Courts expect parties to have document & data retention practices in order: See Rules 16(b)(2);
26(f)(1) (requiring pre-discovery conference & scheduling order within 90-120 days of the beginning of
an action); In re Direct Southwest, Inc. FLSA Litigation, 2009 U.S. Dist. LEXIS 69142 (E.D. La.)
(requiring execution of supplemental search terms, production of documents & production of privilege log
within 10 days).
[Defendant] “was ordered to “provide a data-map of the ESI involved in this litigation for in-camera
review ... If no data-map exists, then …[defendant] [was to] to explain why no ESI data-map exist[ed] and
how Counsel ... educated themselves about [defendant’s] information and record keeping systems.” Small
v. Univ. Med. Center of Southern Nevada, 2:13-cv-00298 (D. Nev. 8/18/2014). Id., at n. 15 (Court-
appointed Special Master “was forced to create his own data map ... from scratch, by synthesizing
testimony from IT personnel and other employees”).
“[T]he parties have fifteen (15) business days from the date of this order to exchange information
regarding the location and existence of electronic data sources that may contain discoverable ESI (the
"Data Map"), including information regarding the parties' policies and/or procedures regarding data
retention; their computer servers and back-up and archival sources that store ESI; all computers, phones,
tablets, and other storage devices issued to the Custodians or used by the Custodians for business
purposes; all email accounts and cloud-storage/file-sharing service accounts used by the Custodians for
business purposes; and any data source that the party identifies as not reasonably accessible pursuant to
Fed. R. Civ. P. 26(b)(2).” Hydrochem LLC v. Duplessis, Civil No. 14-264 (M.D. La. 5/28/2015).
Courts Accelerate Compliance](https://image.slidesharecdn.com/jun14fbt-talkppt-fbt-180618002918/75/Legal-Issues-in-Data-Privacy-and-Security-Response-Readiness-Before-the-Breach-45-2048.jpg)
![46
Examples Of Cyber Evidence
Logs of internet URL/domain access. Microsoft Corp. v. John Does 1-5, No. 15-cv-6565
(E.D.N.Y. 11/23/2015)
Server login records. Tyan v Garcia, No. 15-cv-05443 (C.D. Cal. 5/2/2017)
“more than 42, 000 files on appellant’s computer were intentionally overwritten on February
6, 2011, using [XXXXXX], a program designed to permanently delete and overwrite files.
[Defendants’ expert] was unable to restore or retrieve the content of the overwritten files. In
addition, certain files one would expect to find (such as “Recent Folder Activity, Link Files,
Recycle Bin Info Files, Temp Folders, and Internet Cache Folders”) were missing and could not
be restored or retrieved. [The expert] found remnants of other files …” Braun v. Toyota Motor
Sales, U.S.A., Inc., No. B234212 (Cal. App. 2d Dist. 2/13/2013) (unpublished)
“Defendants have … failed to ascertain that third-party service providers implemented
reasonable security measures to protect personal information.” FTC v Ruby Corp., No. 1:16-cv-
02438, Dkt. 1 at 9, ¶31 (D.D.C. 12/14/2016) (“Ashley Madison”). Cf. Board of Trustees of Ibew
Local 43 Electrical Contractors Health v. D'Arcangelo & Co., LLP, 1 N.Y.S. 3d 659, 124 A.D.3d
1358 (4th Dept. 1/2/2015) (motion to dismiss denied where negligence claim was based on alleged
failure to obtain an audit report)](https://image.slidesharecdn.com/jun14fbt-talkppt-fbt-180618002918/75/Legal-Issues-in-Data-Privacy-and-Security-Response-Readiness-Before-the-Breach-46-2048.jpg)