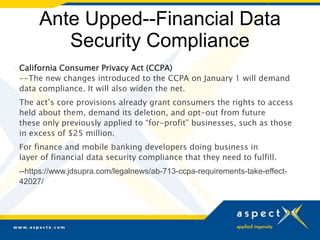
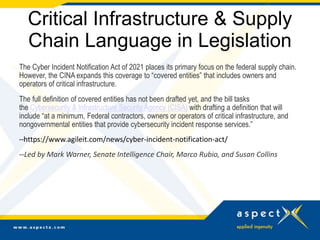
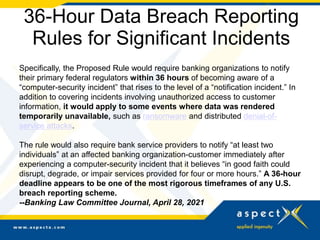
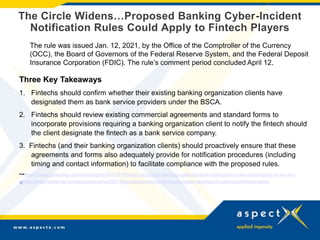
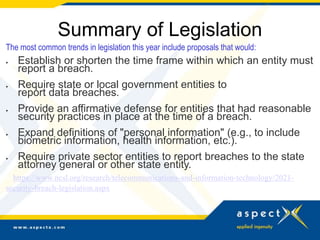
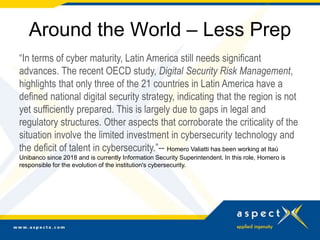
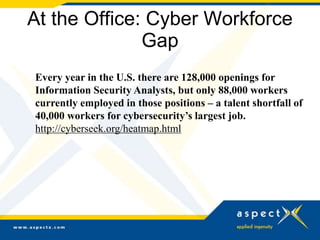
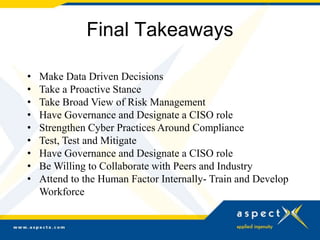
The document outlines evolving cybersecurity policies for financial institutions, highlighting the significant rise in cyber threats and the associated costs faced by the industry. It discusses new legislation aimed at enhancing cybersecurity measures, including rapid data breach notification rules and compliance requirements for fintechs, as well as the growing need for effective vendor management strategies. Key trends include an increasing focus on social engineering threats and the necessity for greater cybersecurity training within institutions to address vulnerabilities in a rapidly changing digital landscape.