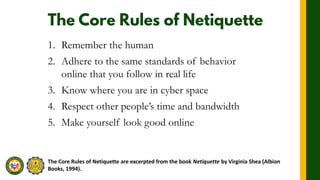
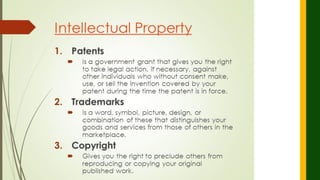
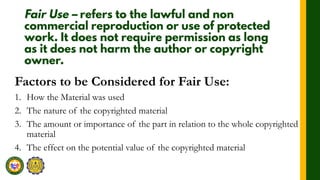
The document discusses proper netiquette and cybercrime laws. It provides 10 core rules of netiquette including remembering the human on the other side, respecting privacy and bandwidth, and avoiding flame wars. It explains that netiquette is based on real-world etiquette and encourages considerate online behavior. The document also defines intellectual property, copyright, trademarks and patents. It discusses factors for fair use and types of cybercrime like piracy and trademark infringement.