Embed presentation

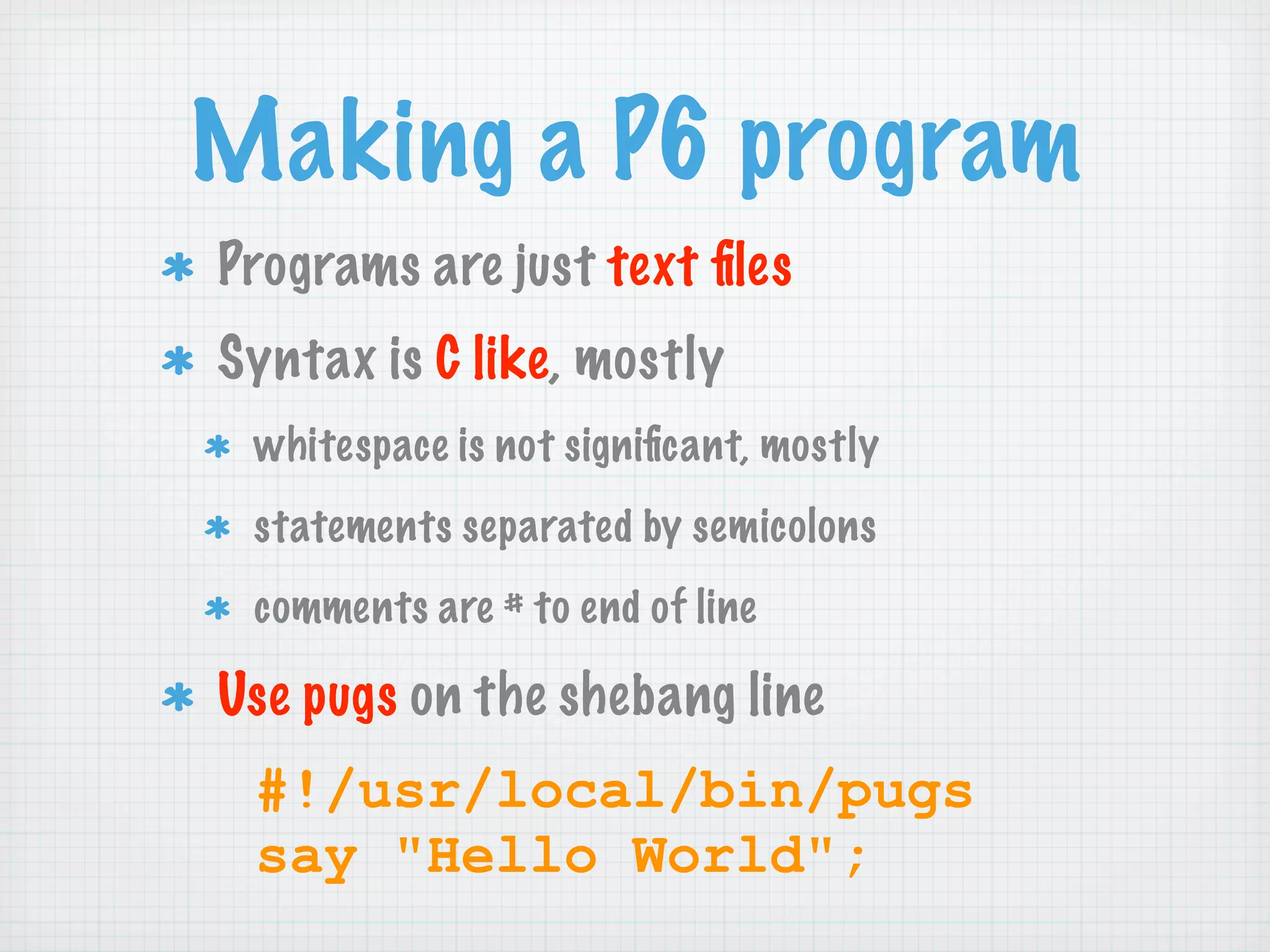
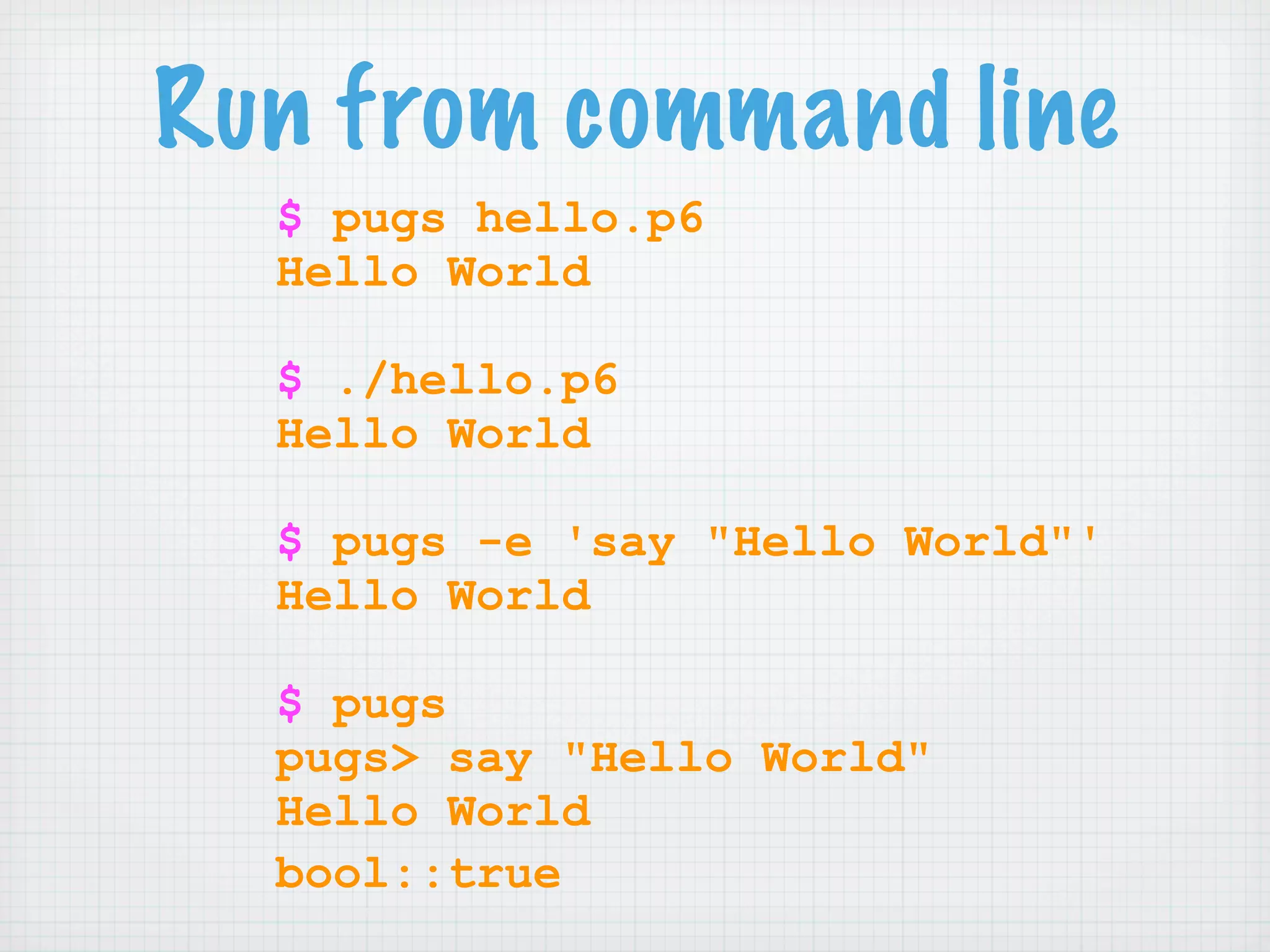
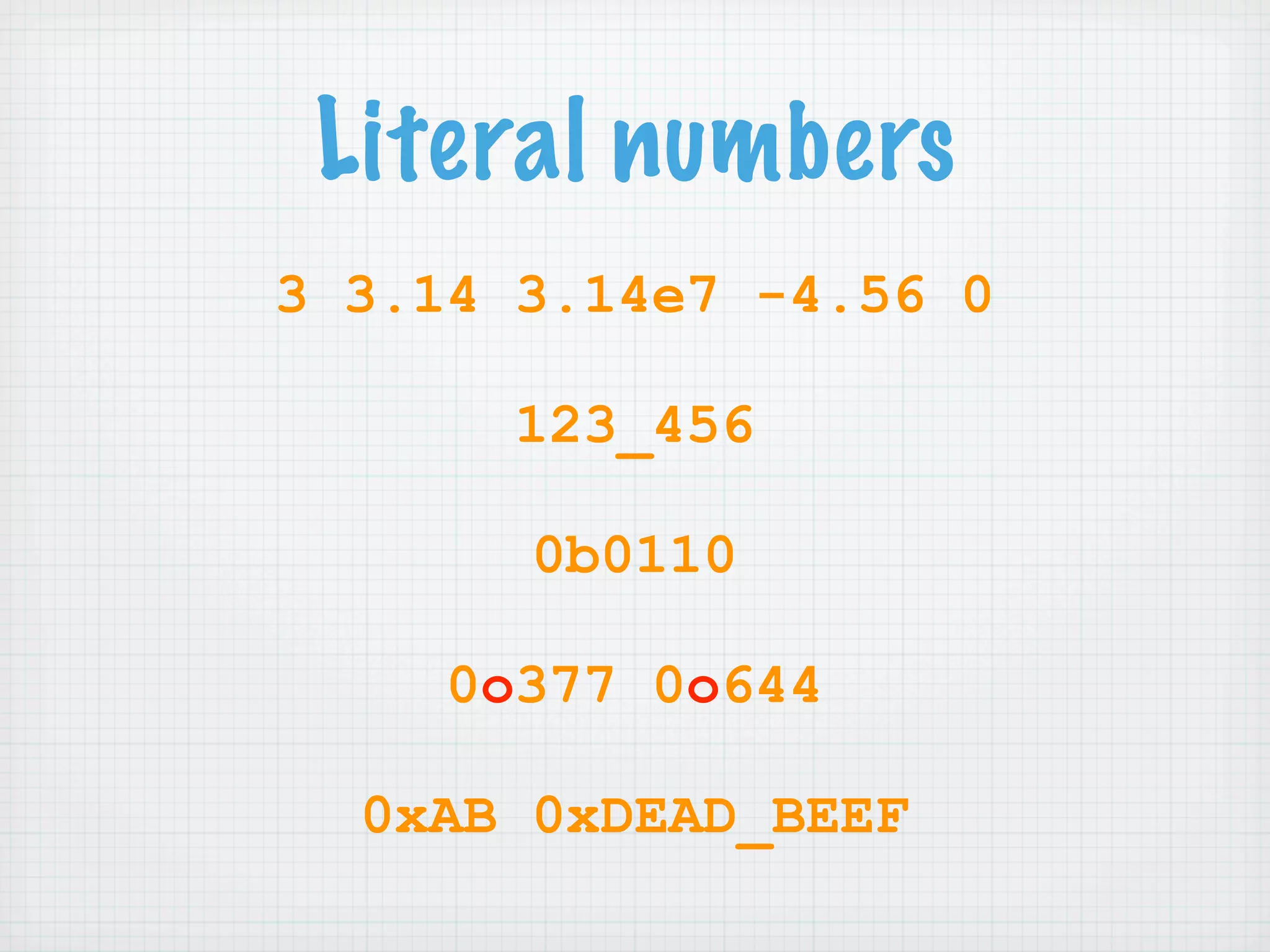
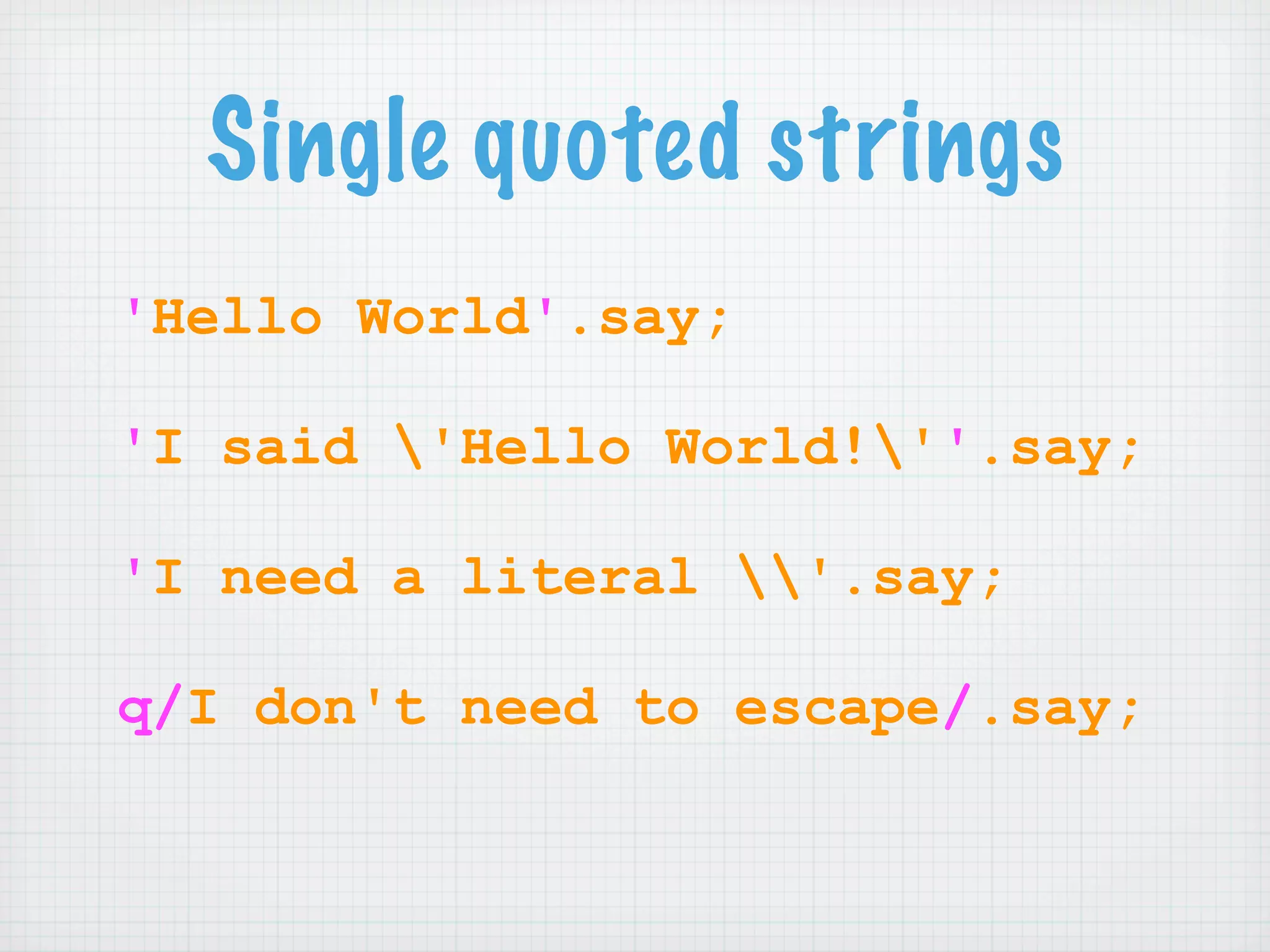
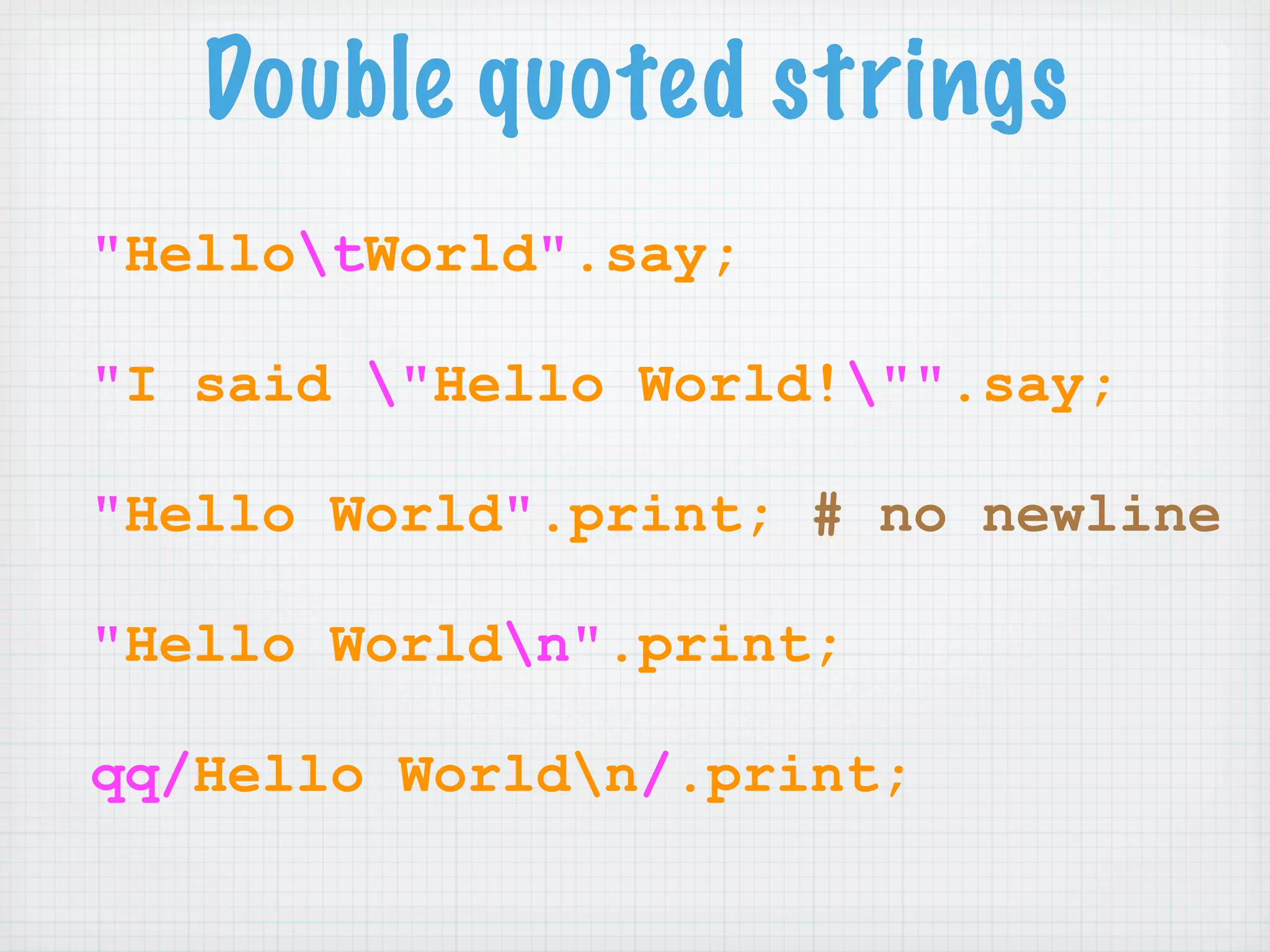
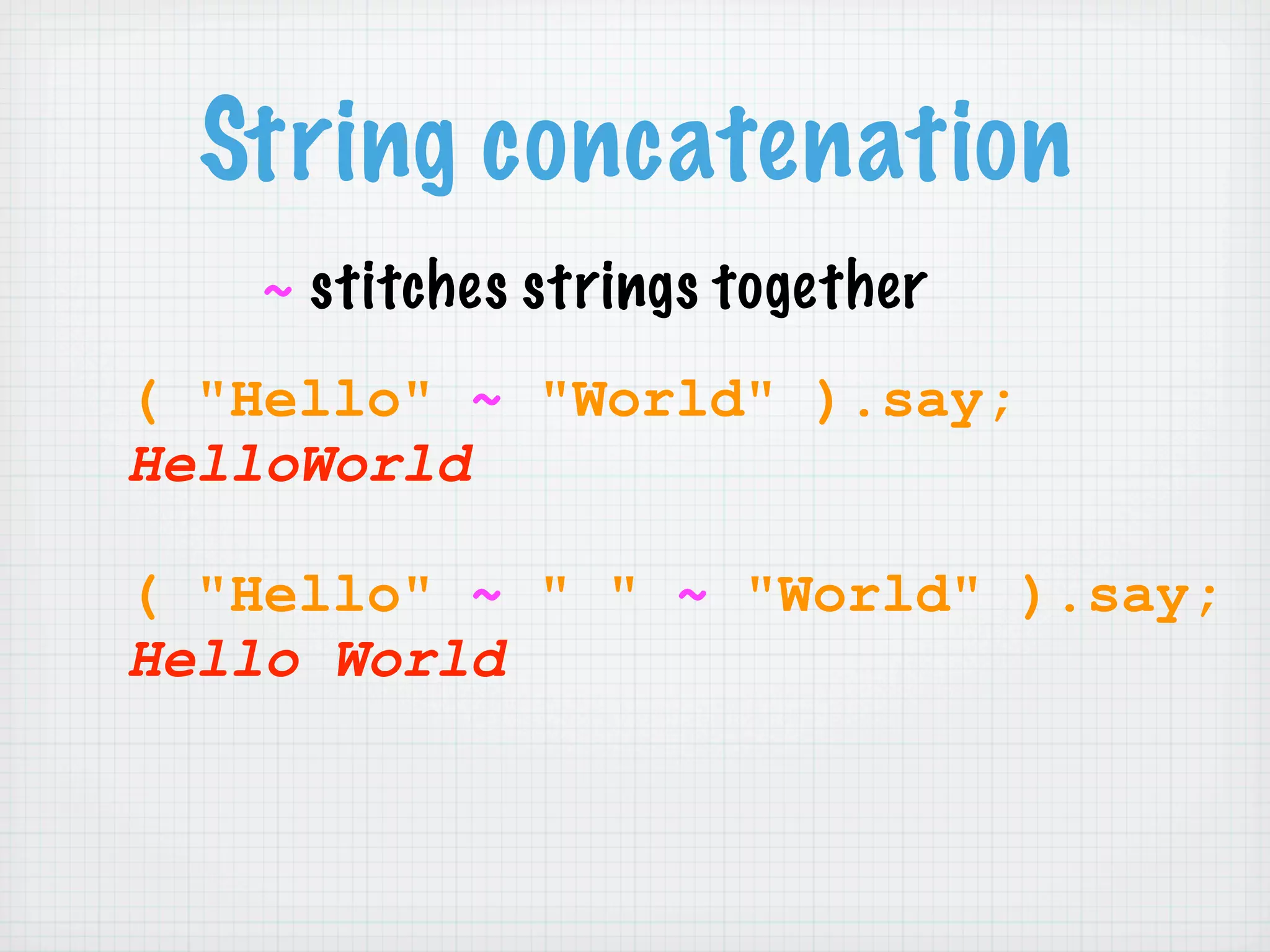
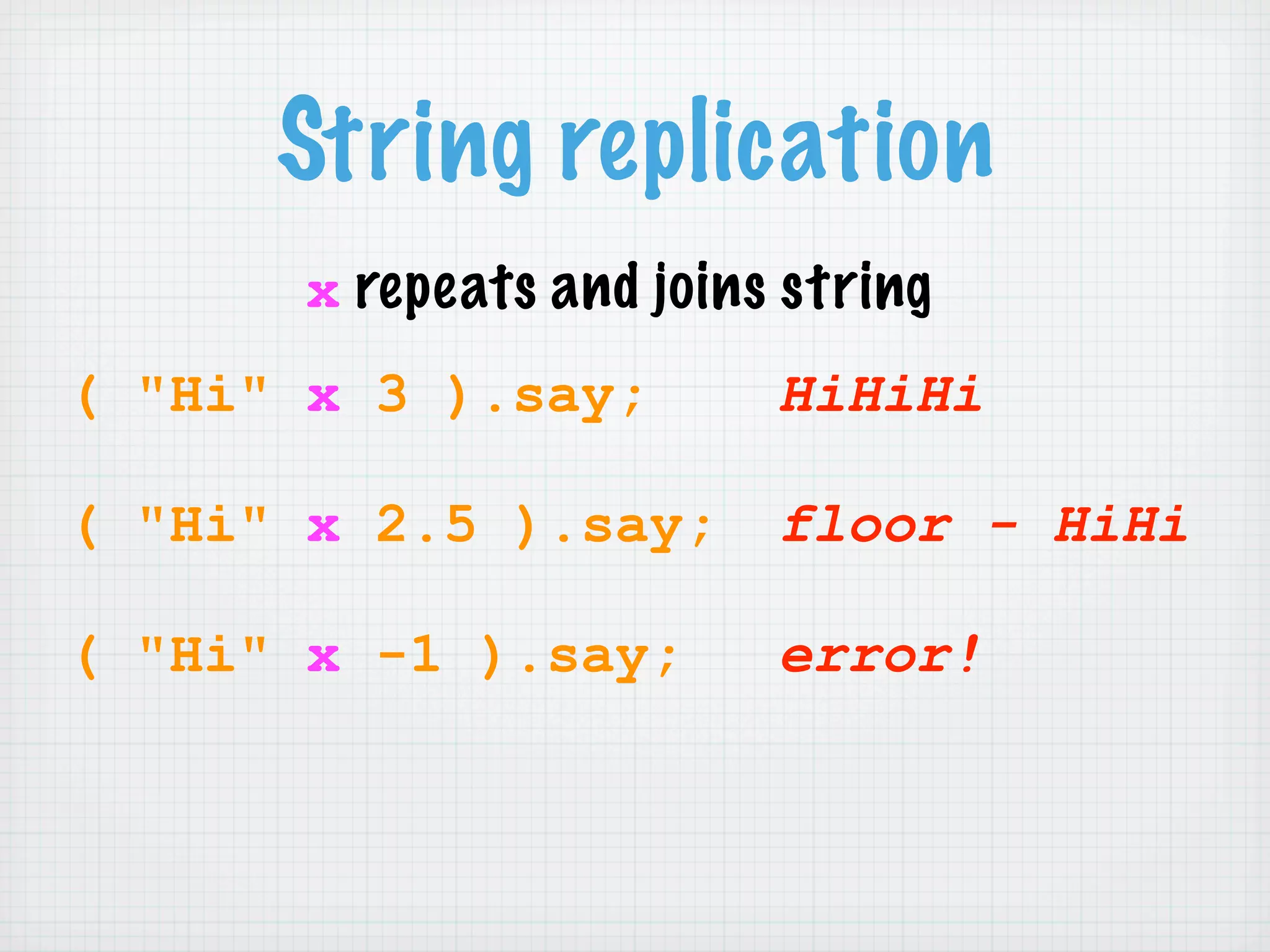
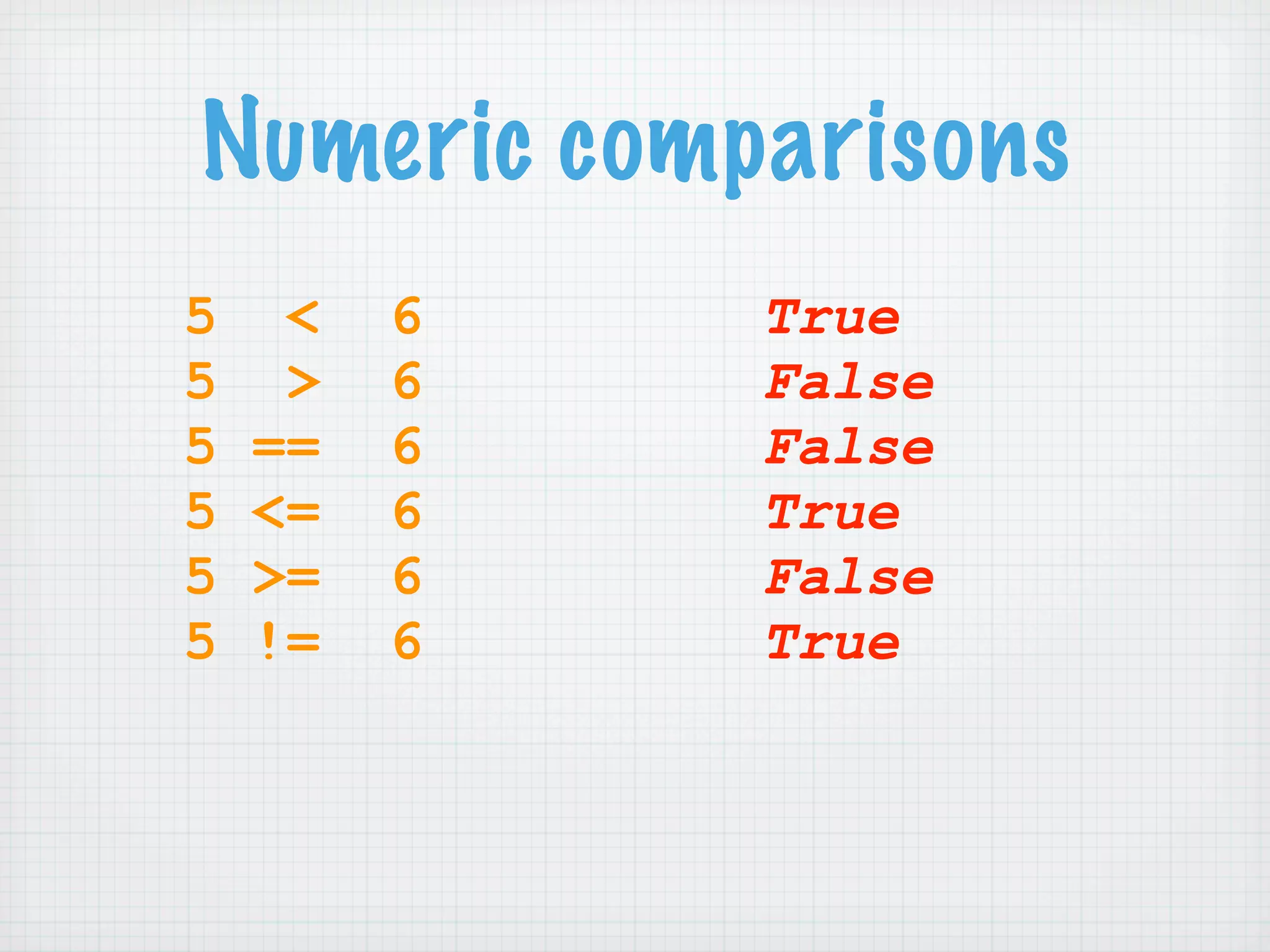
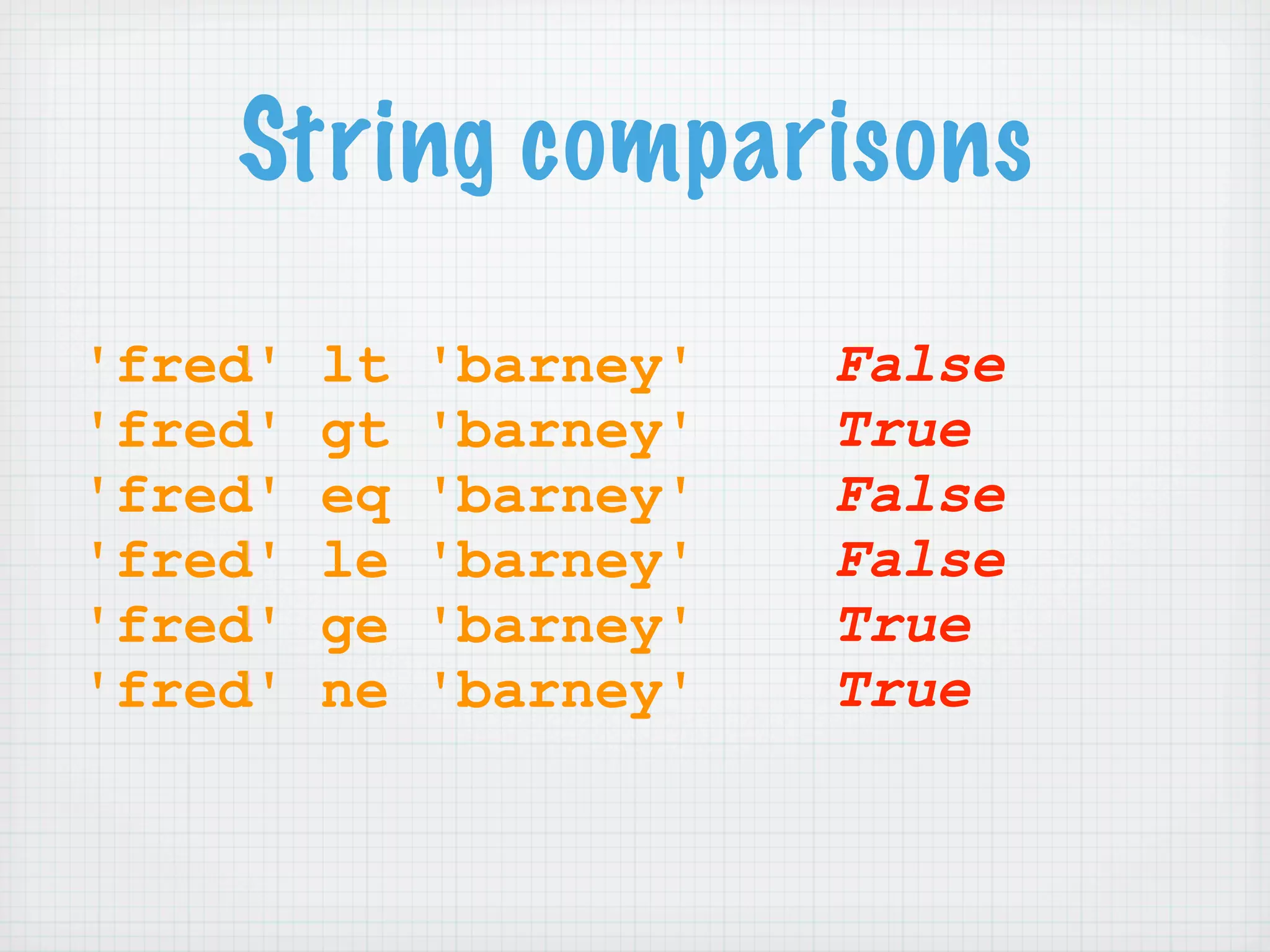
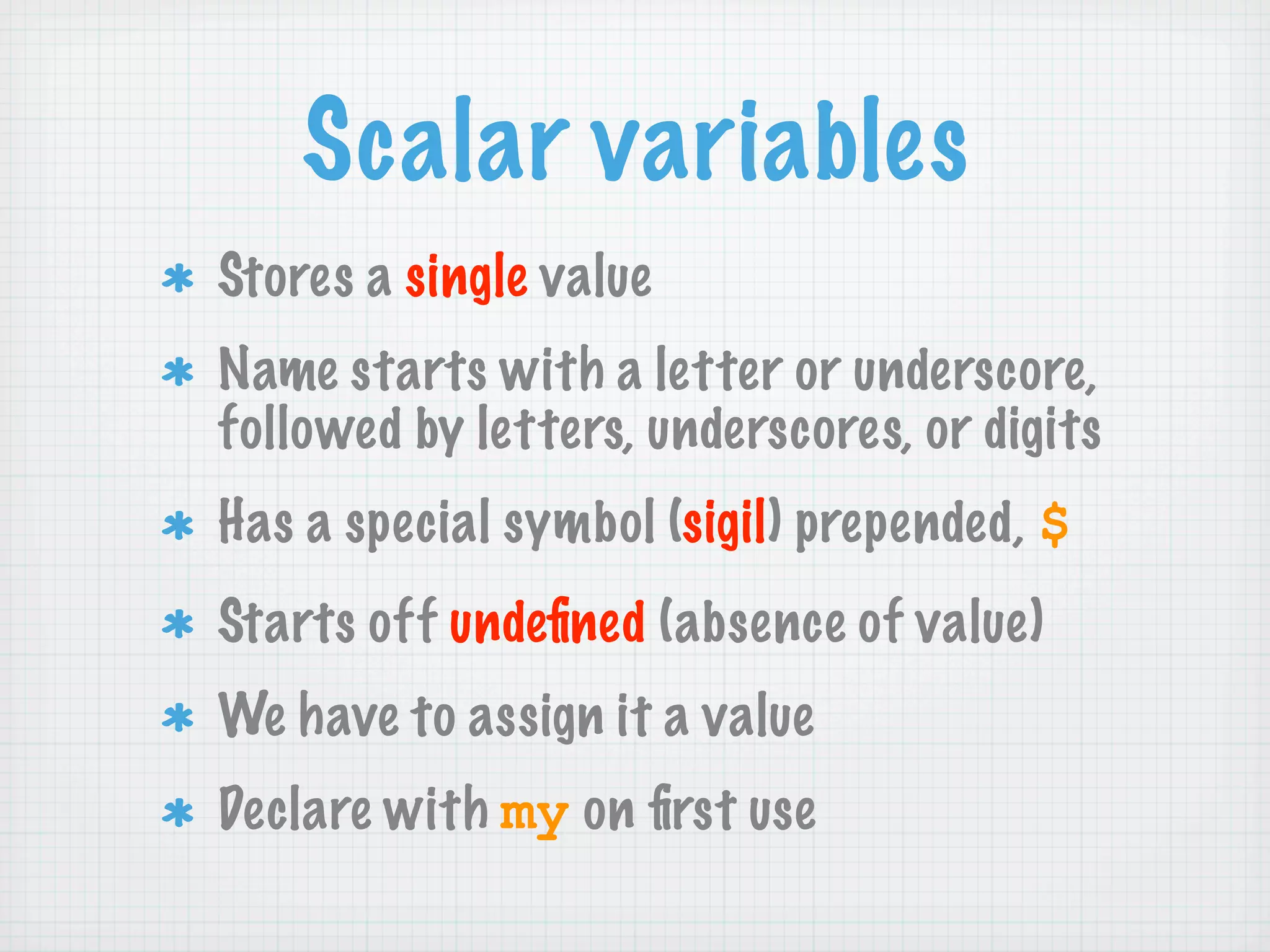
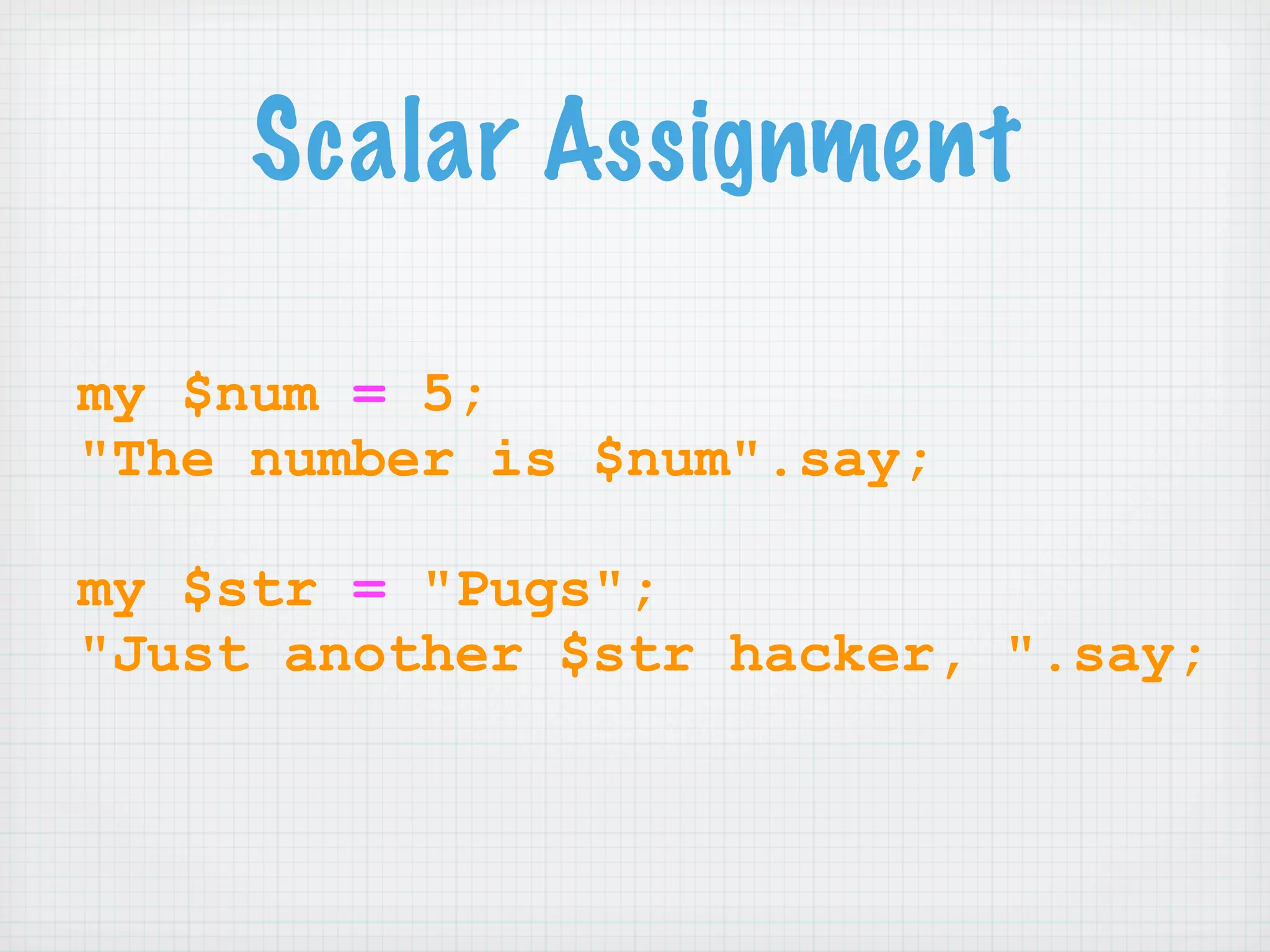
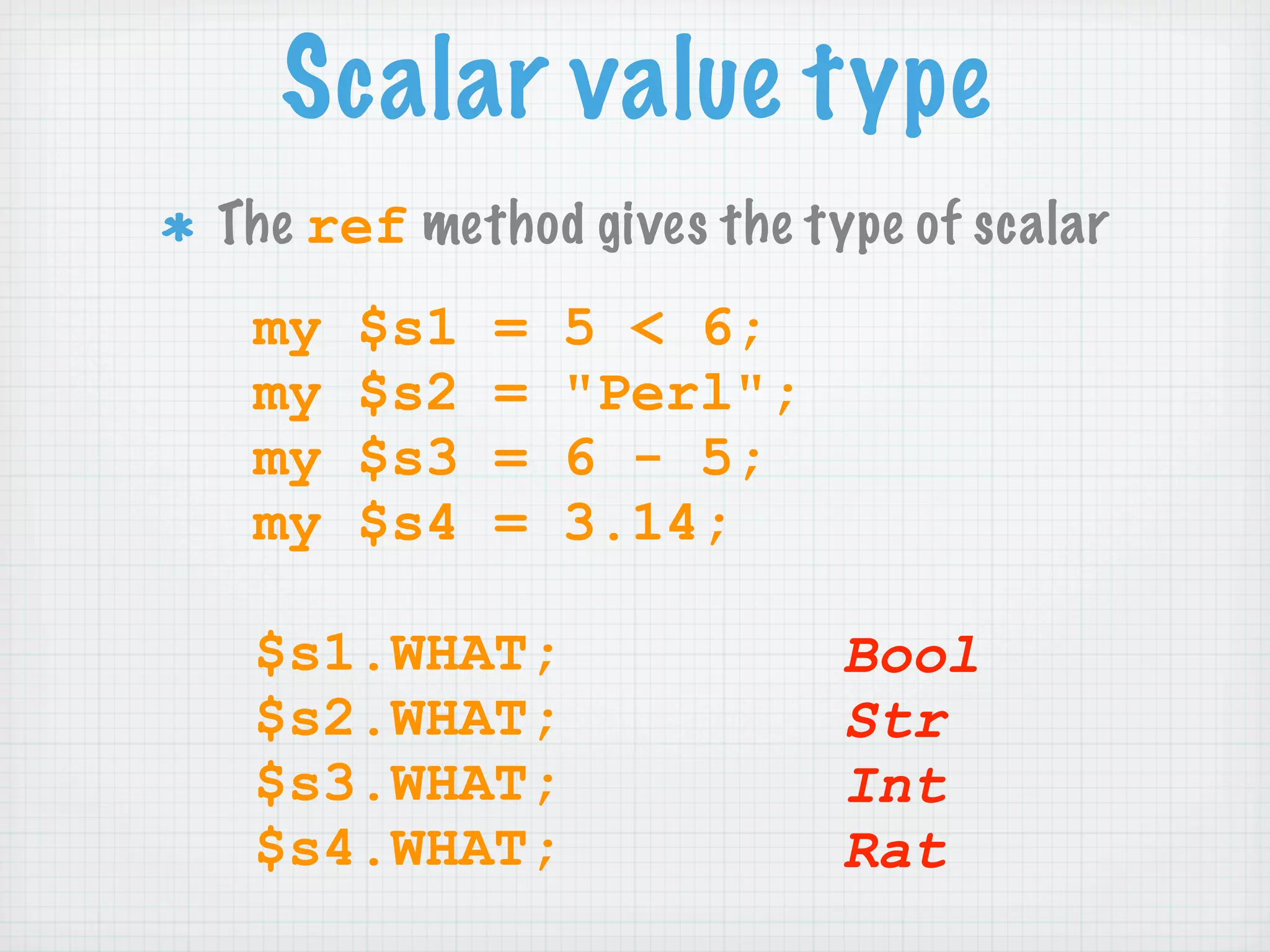
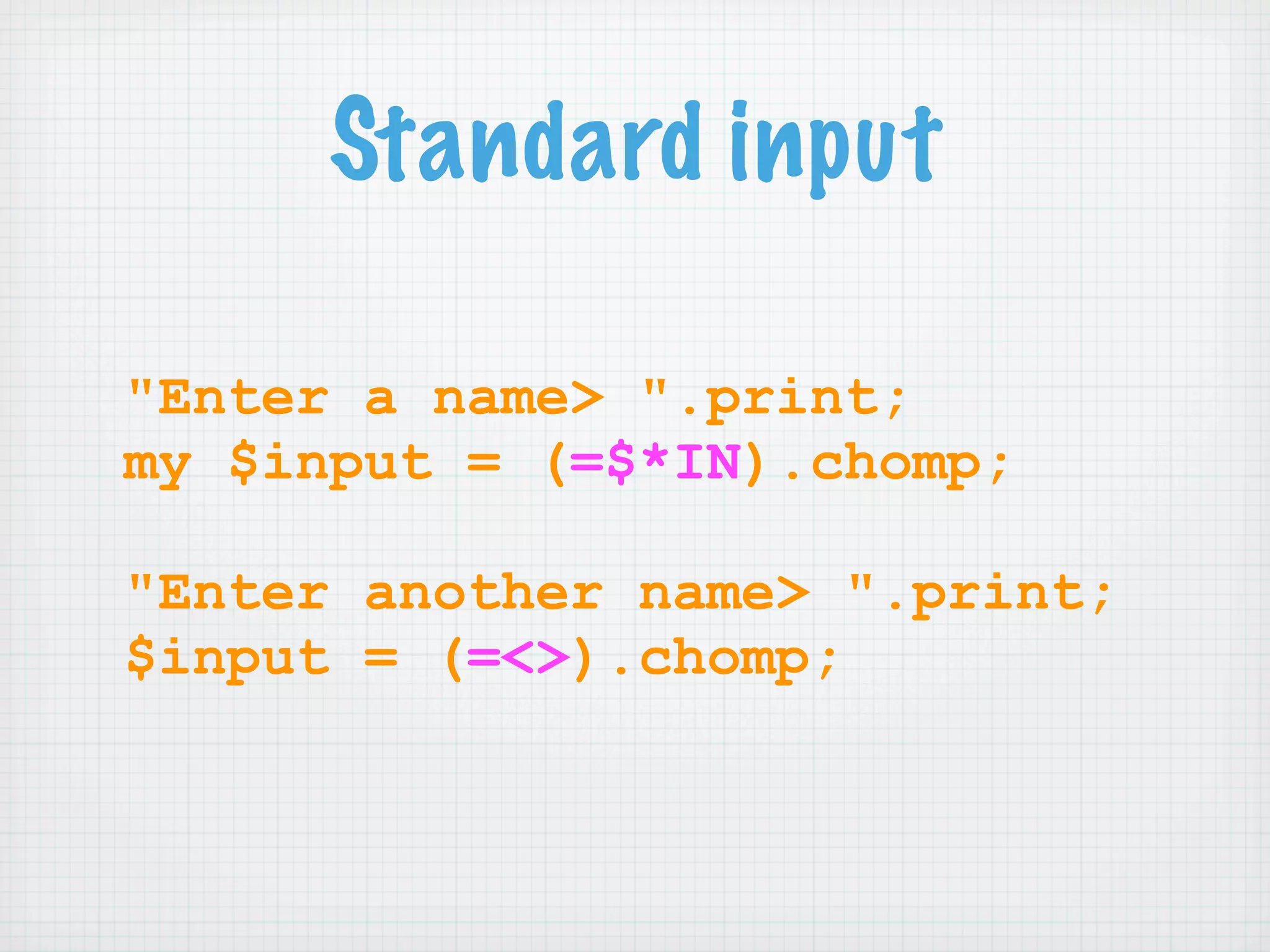
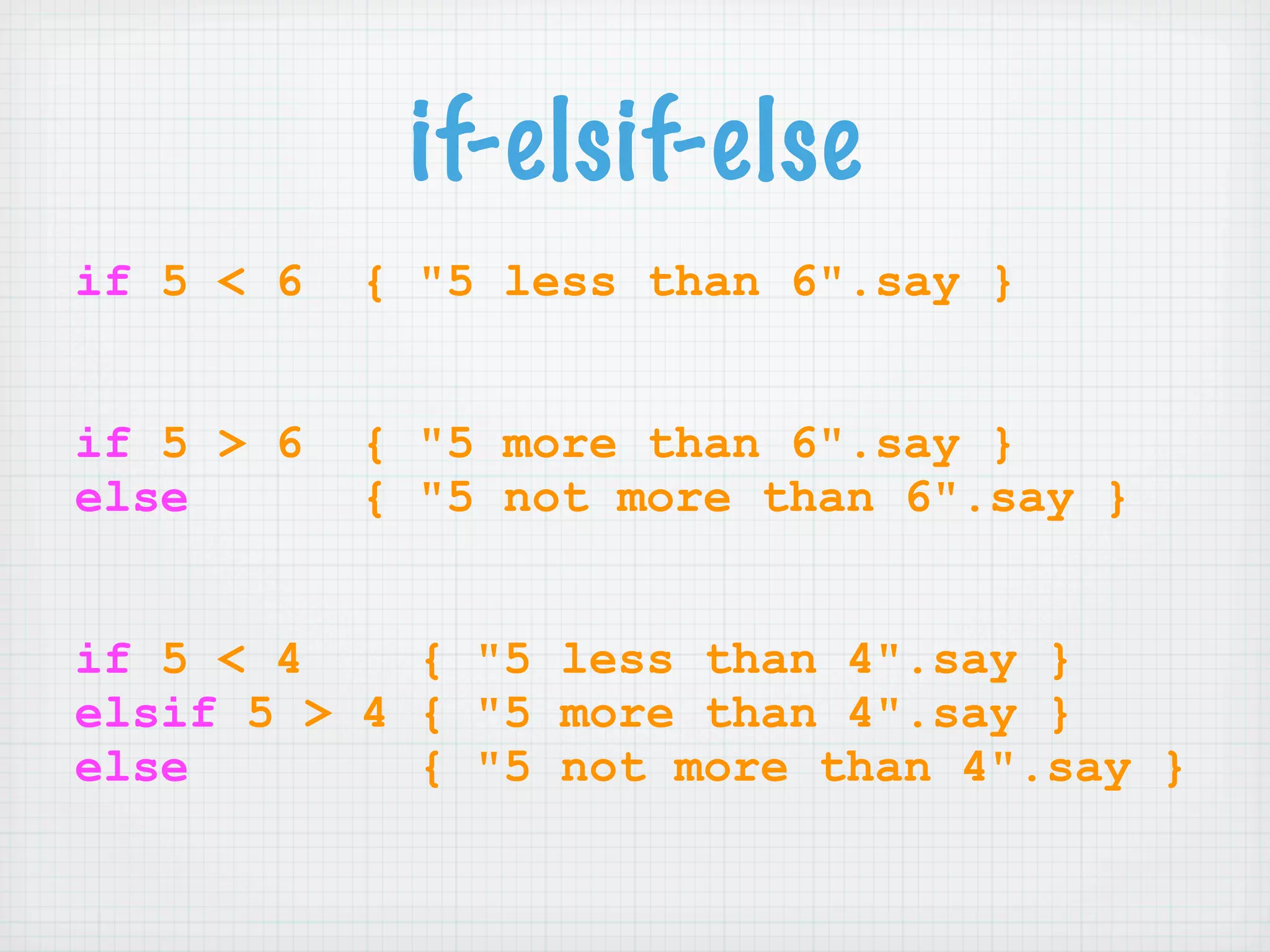
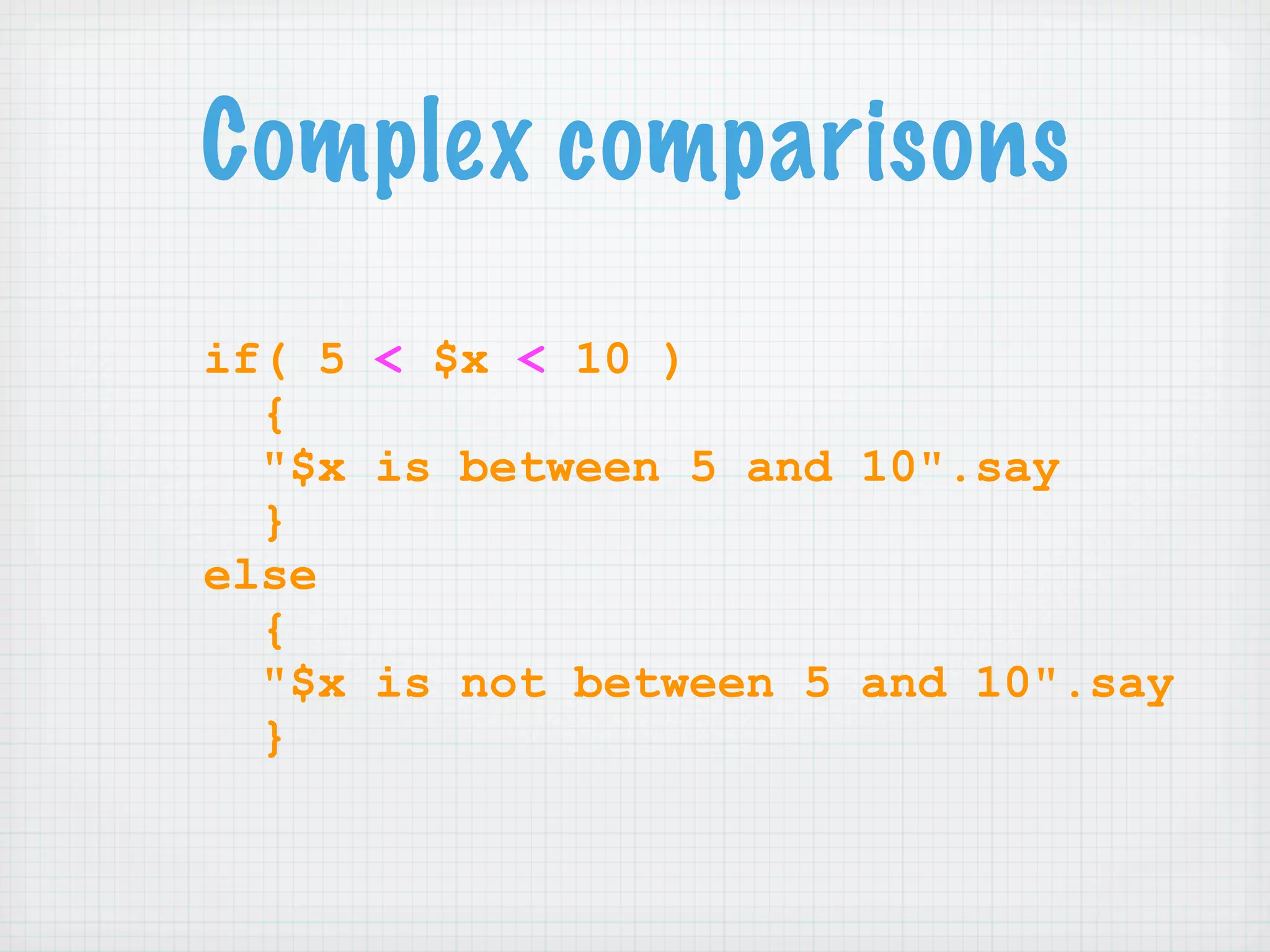
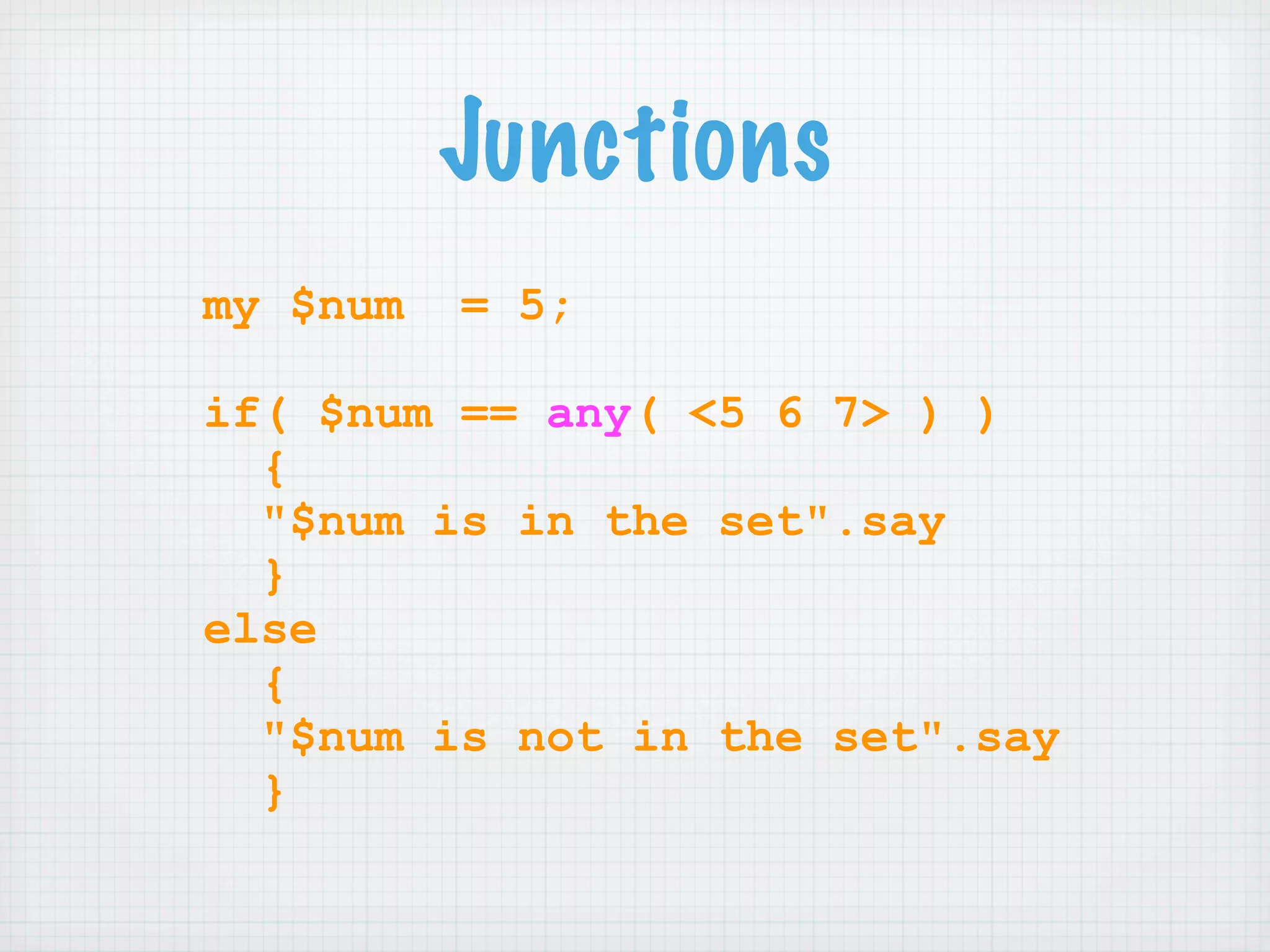
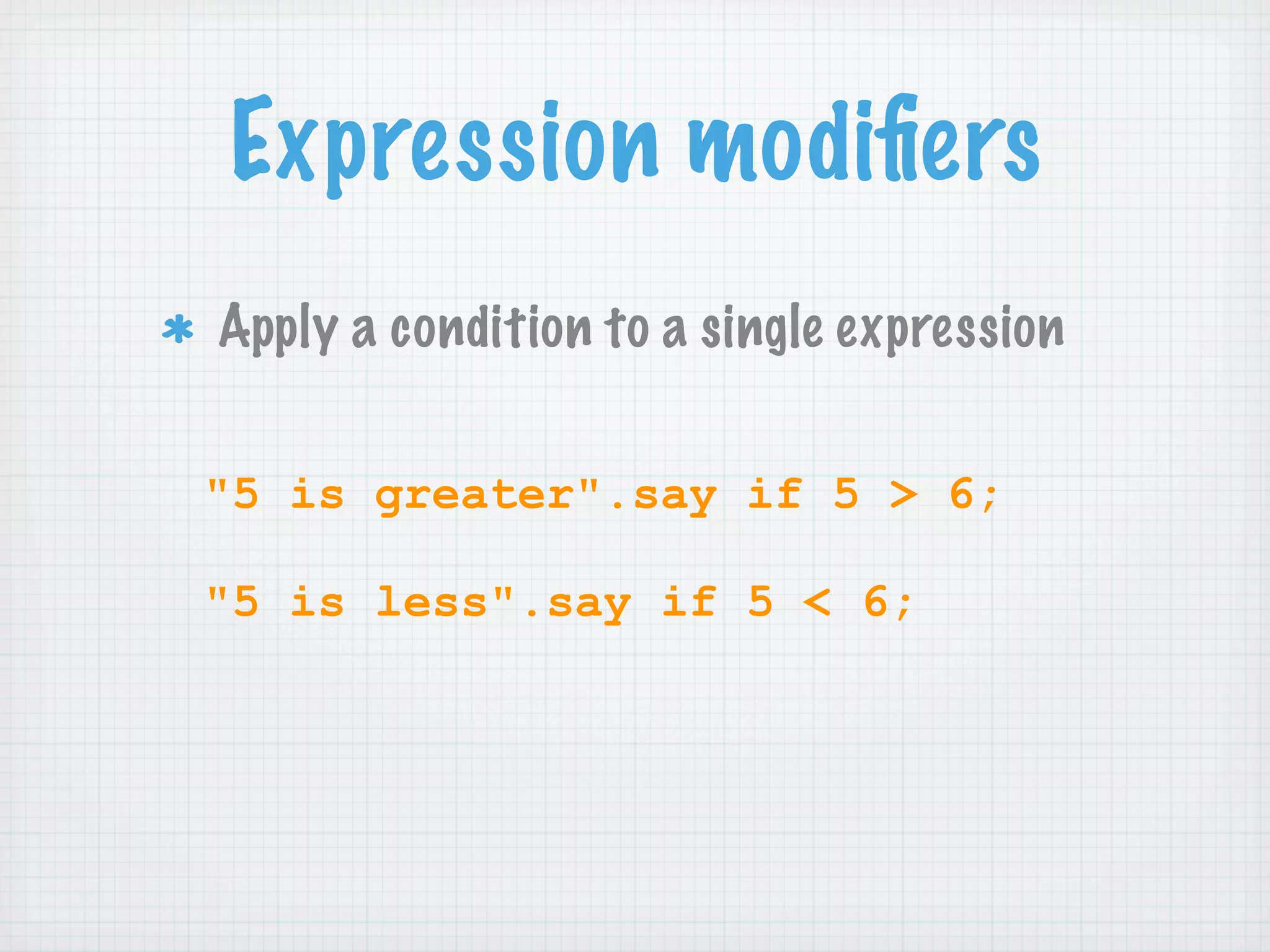
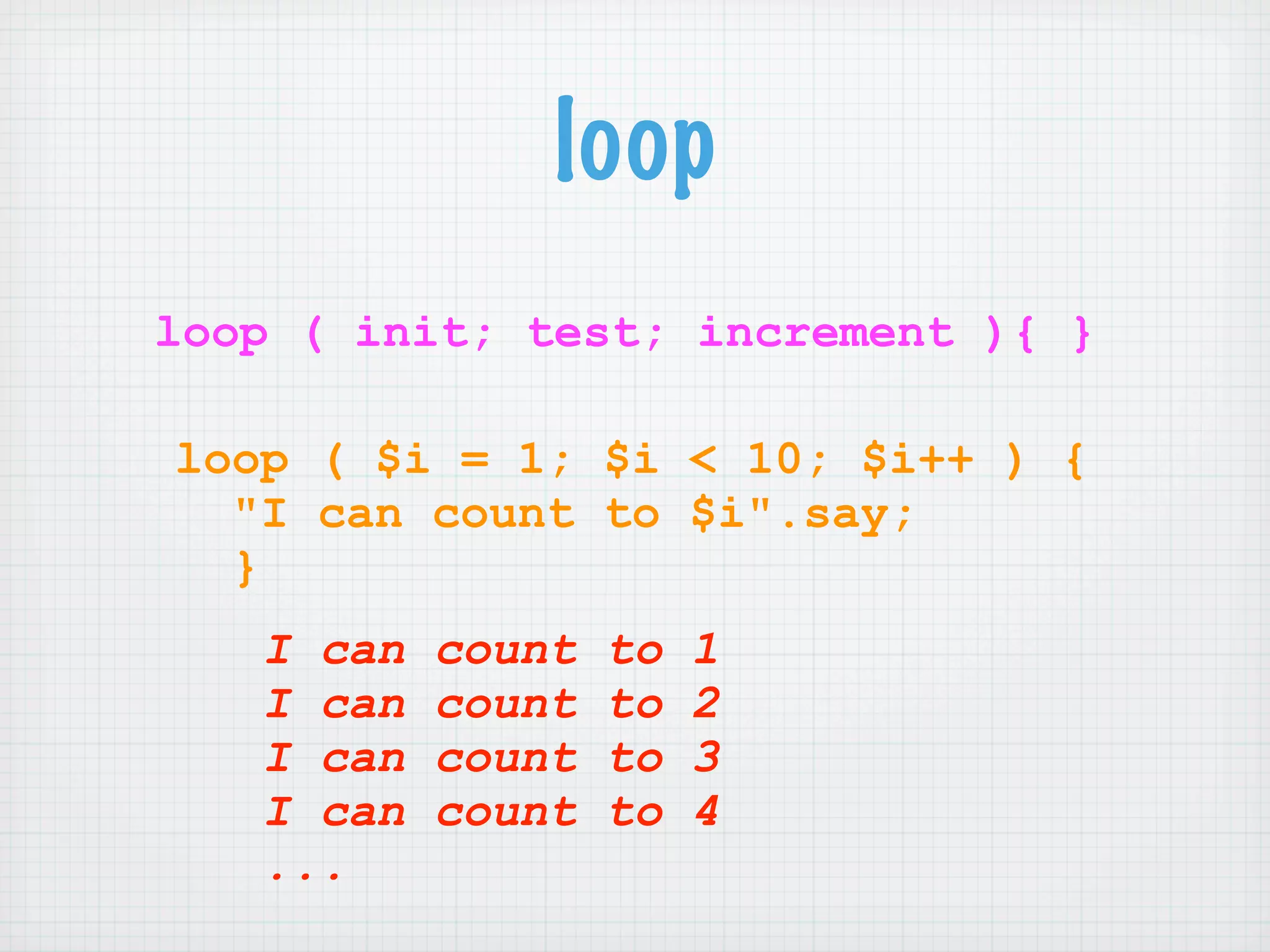
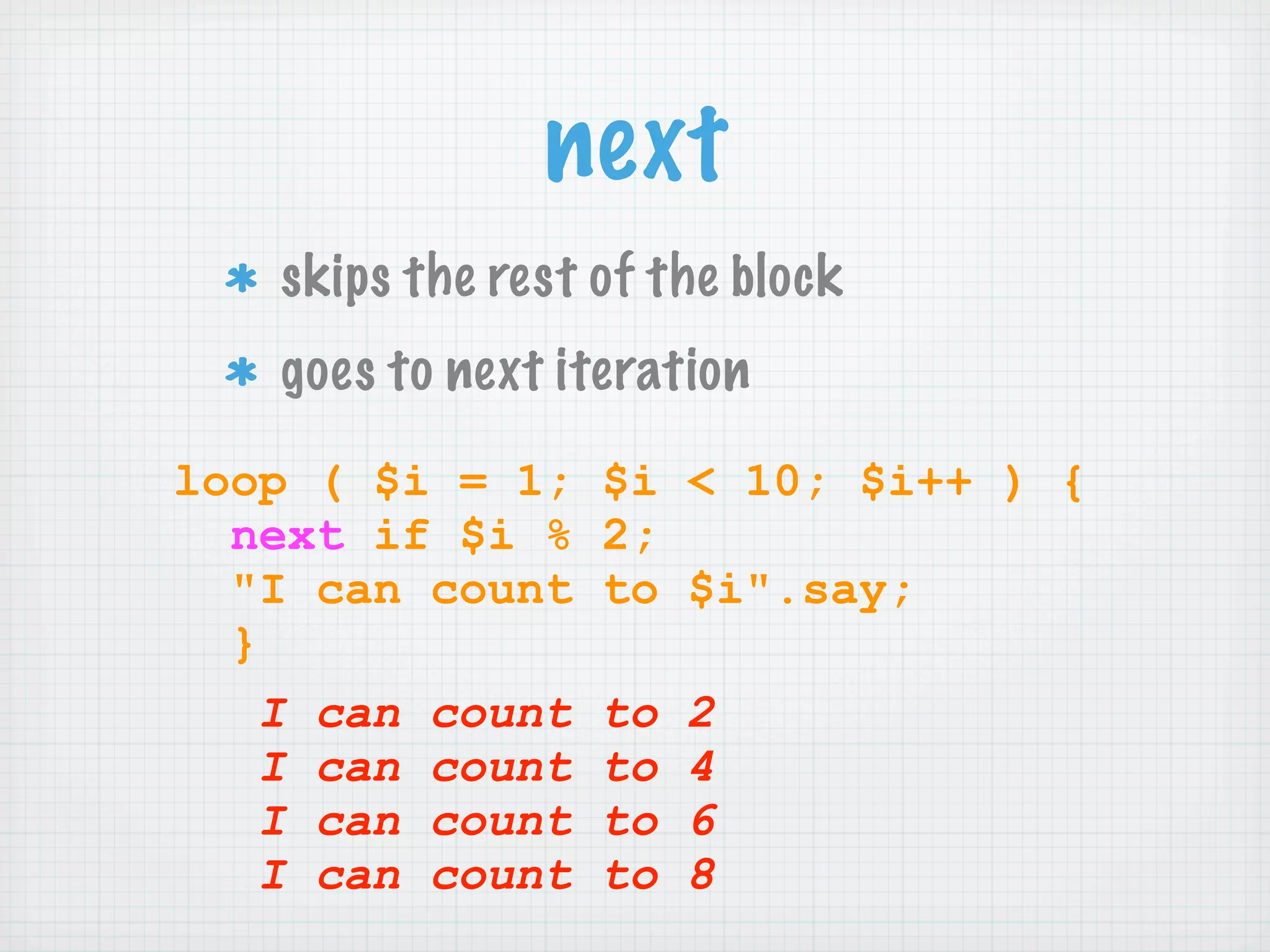
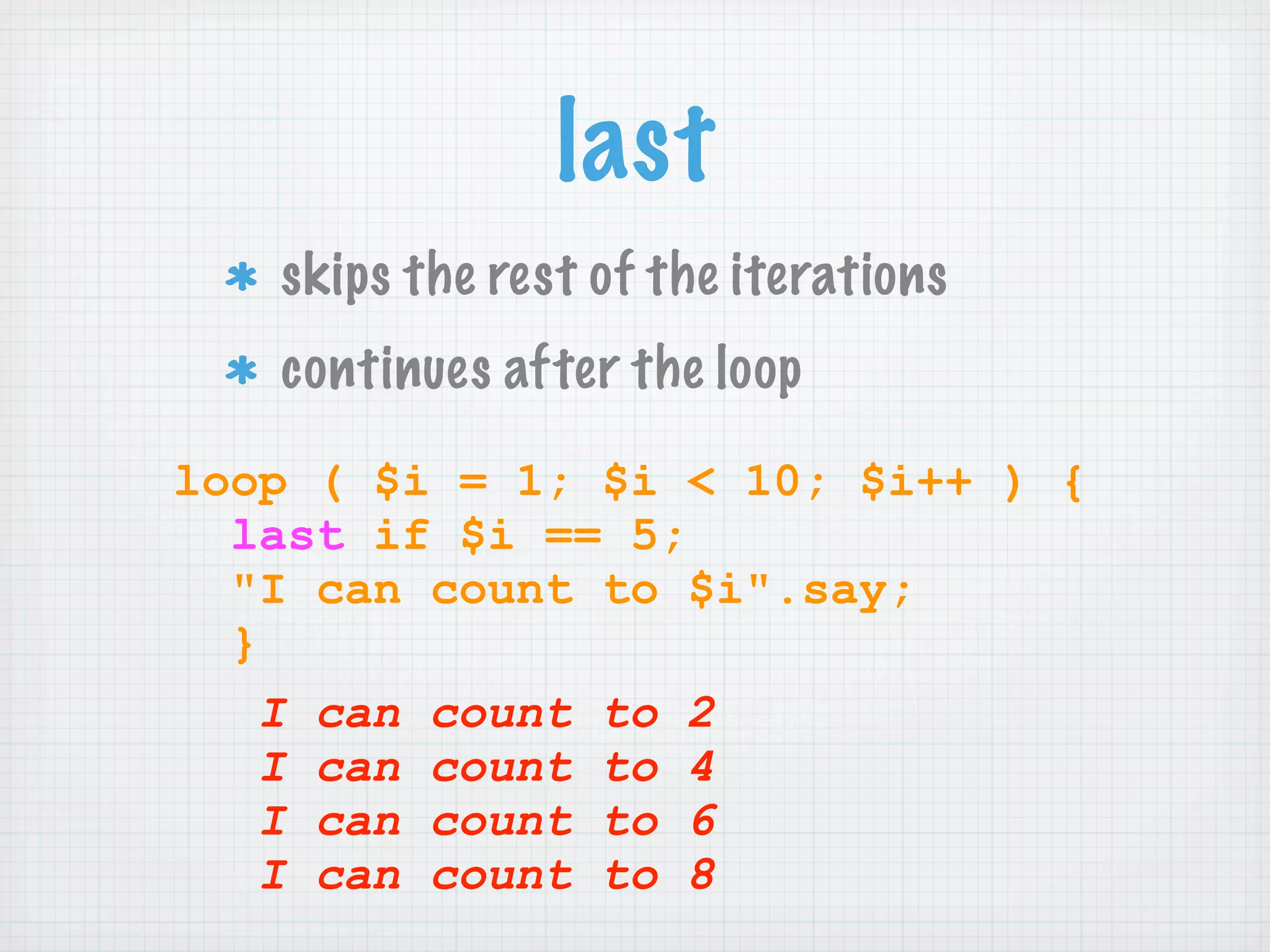
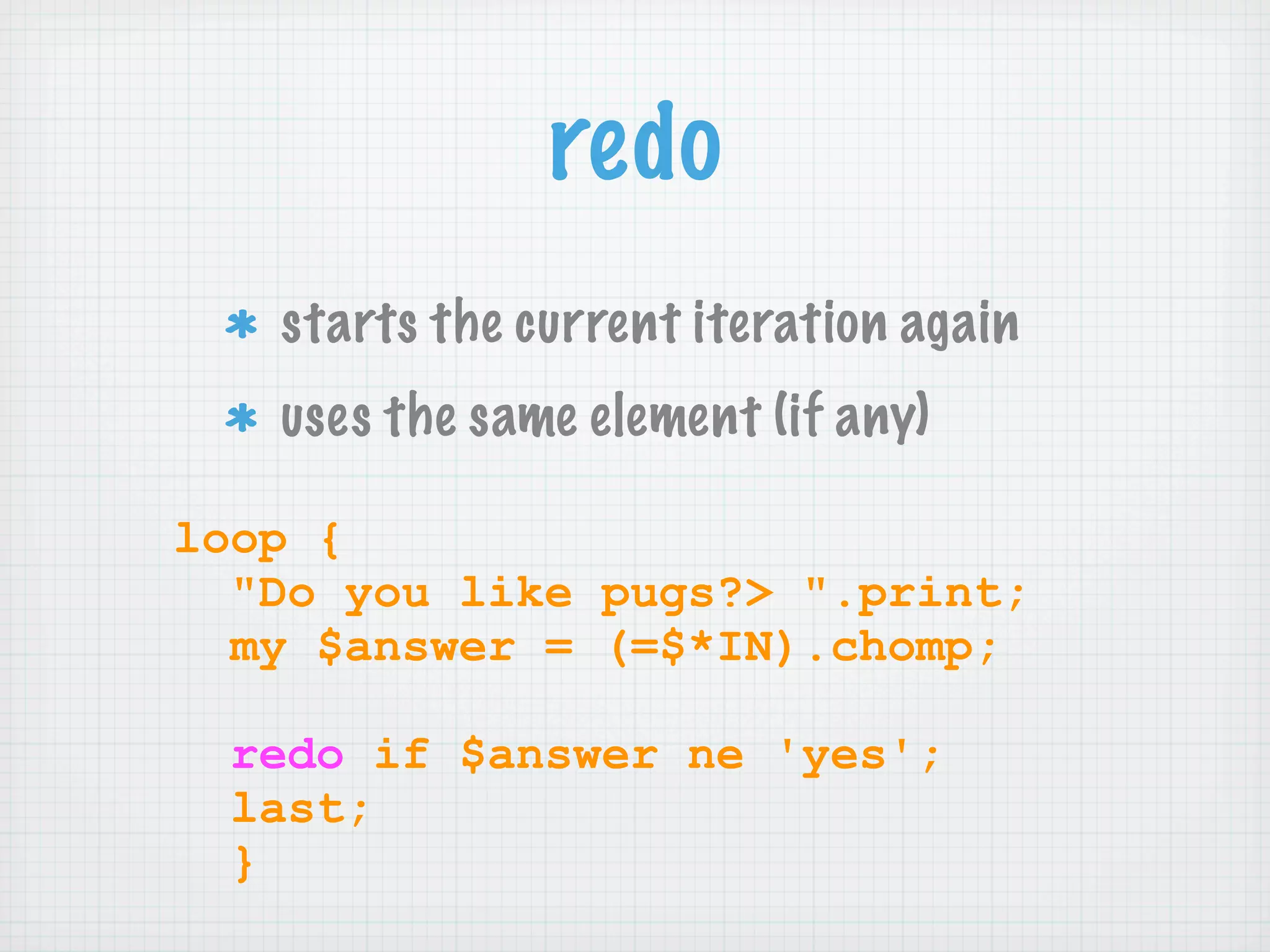
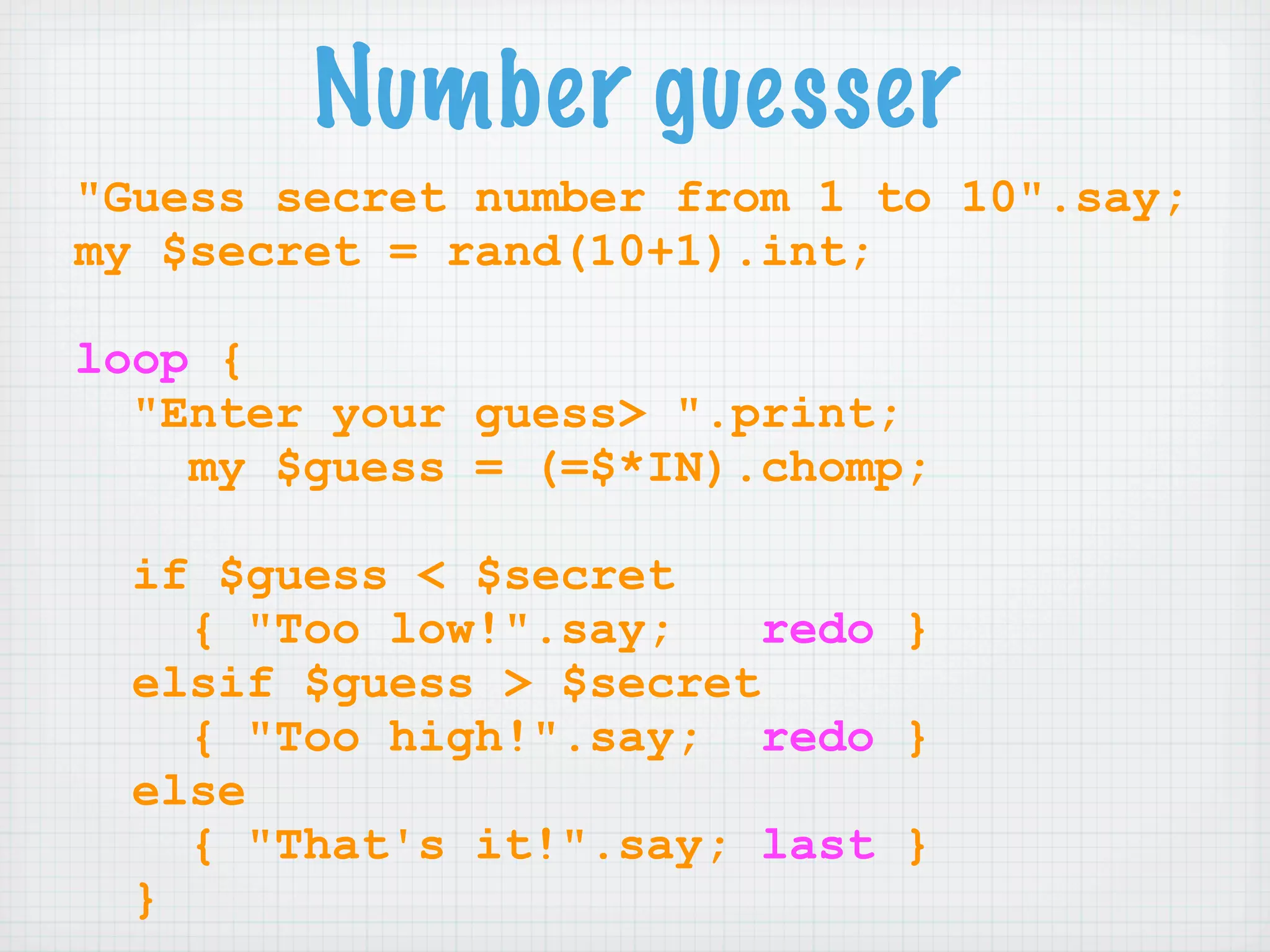

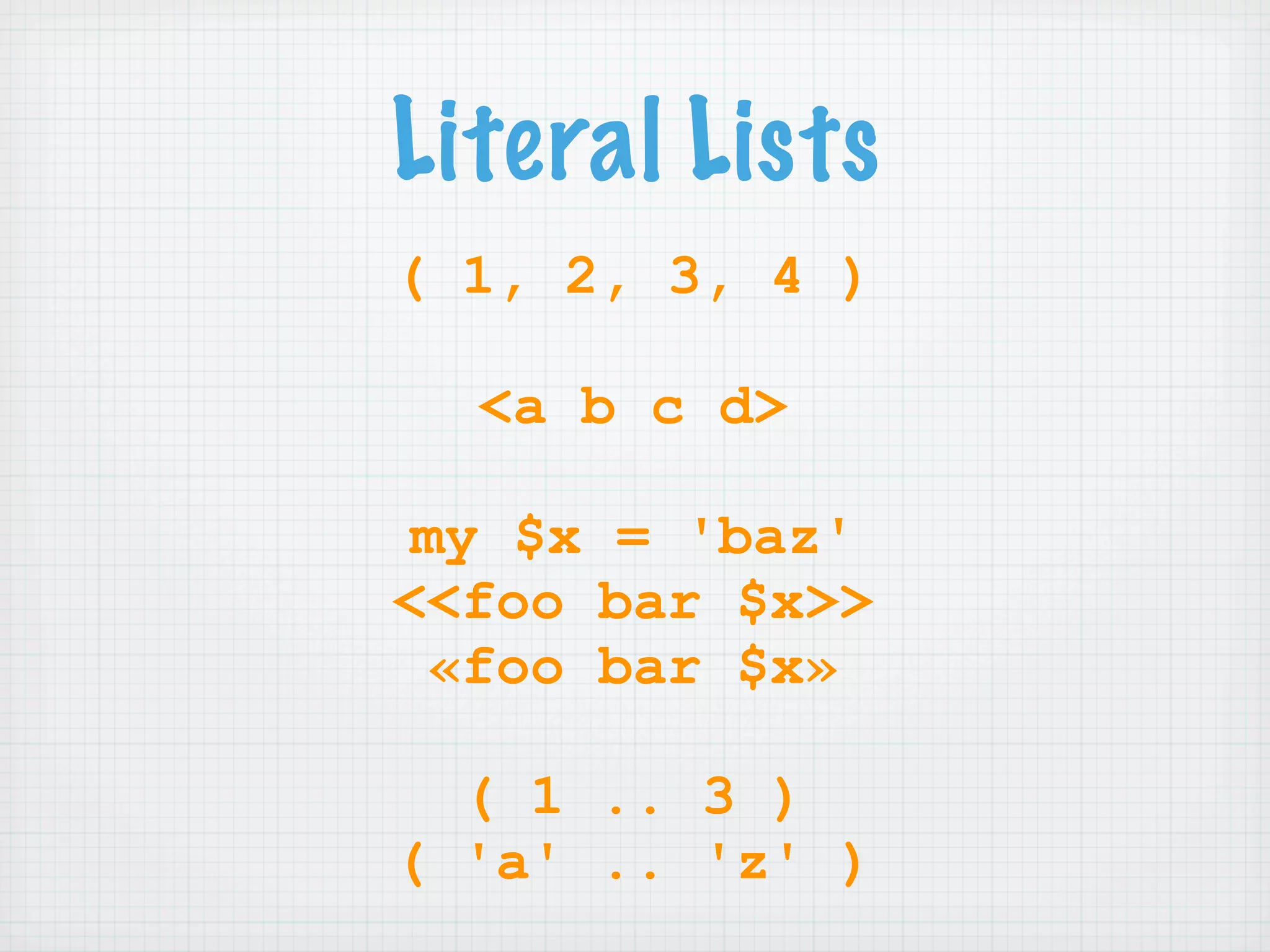
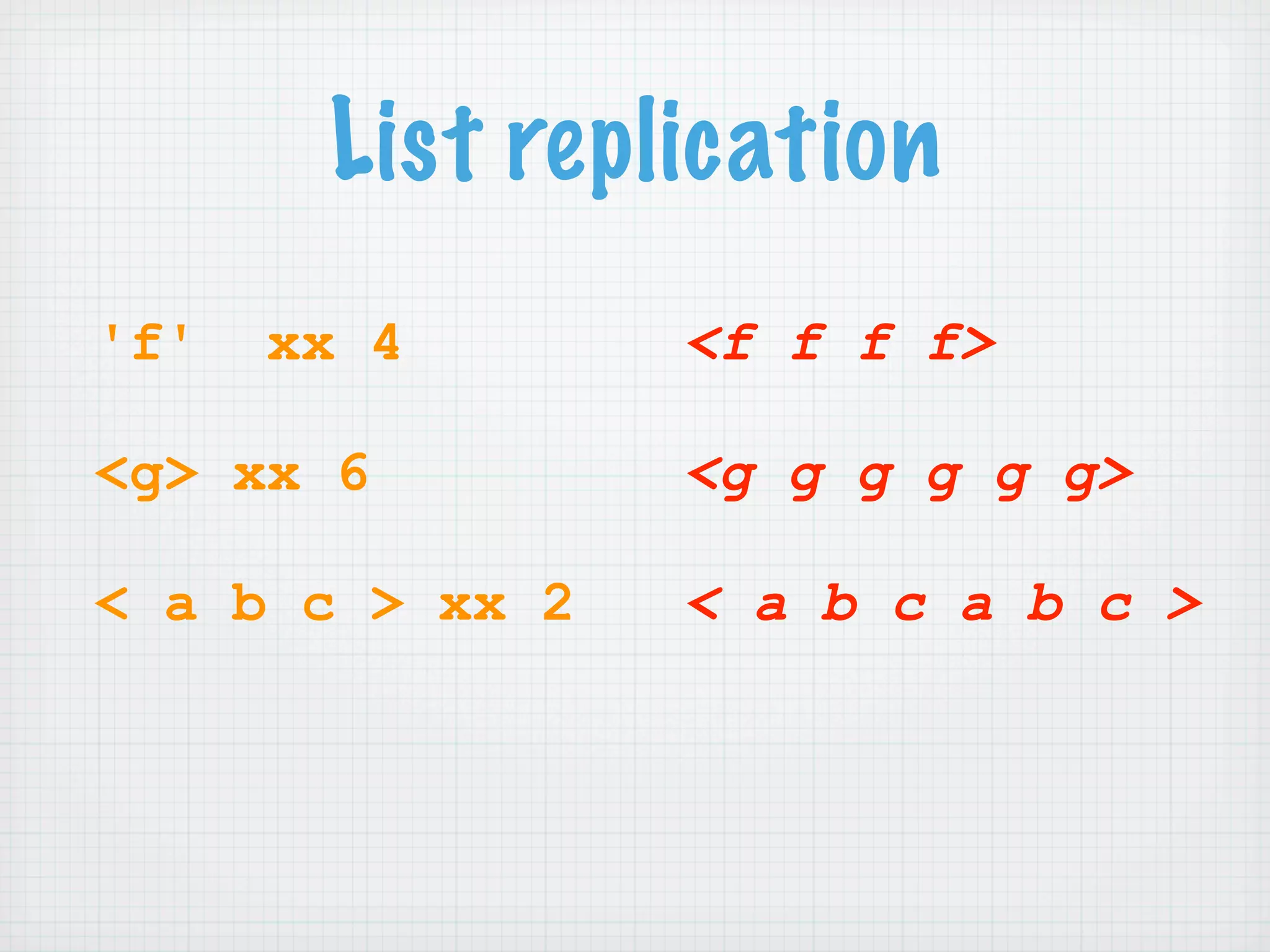
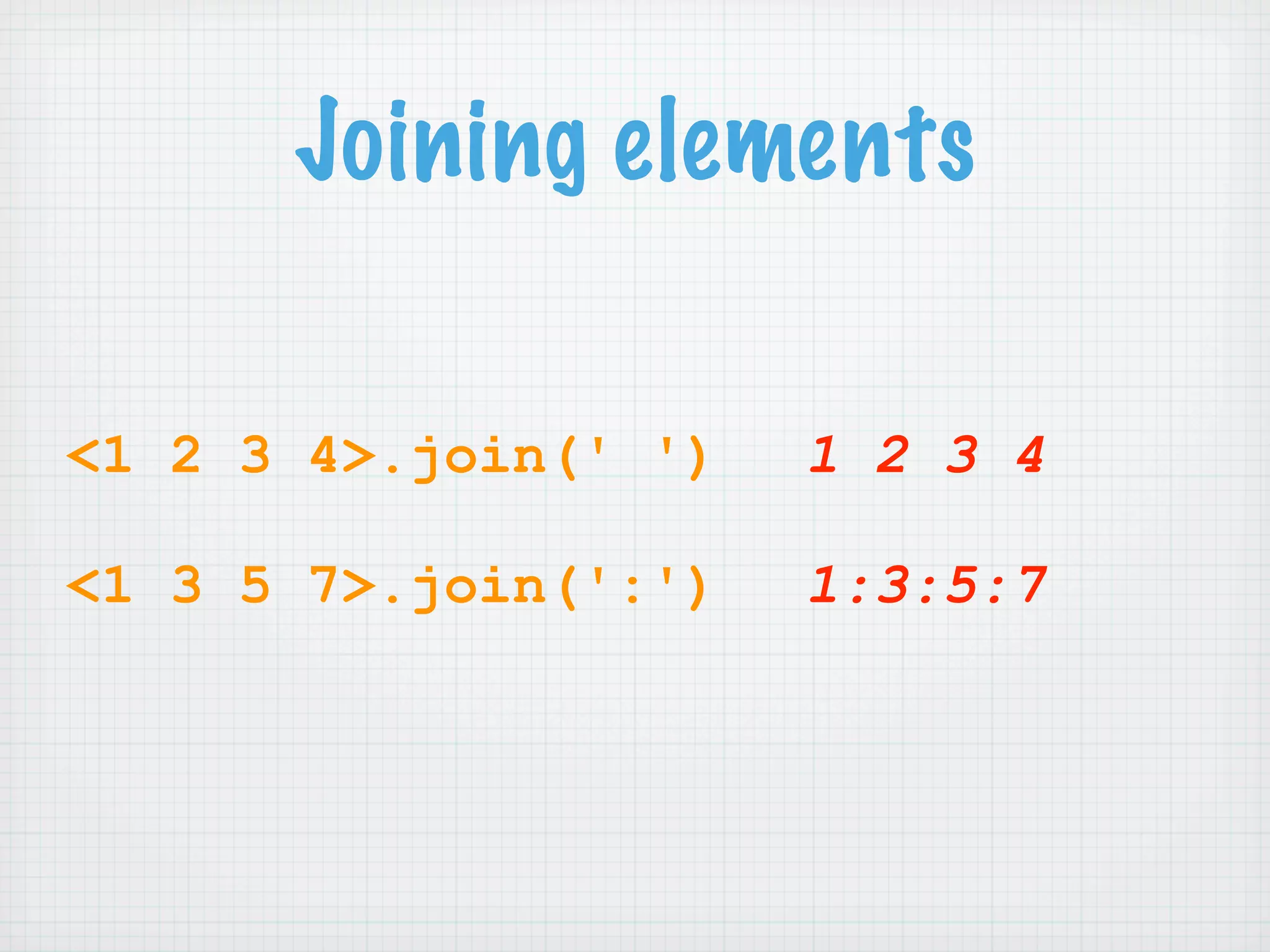
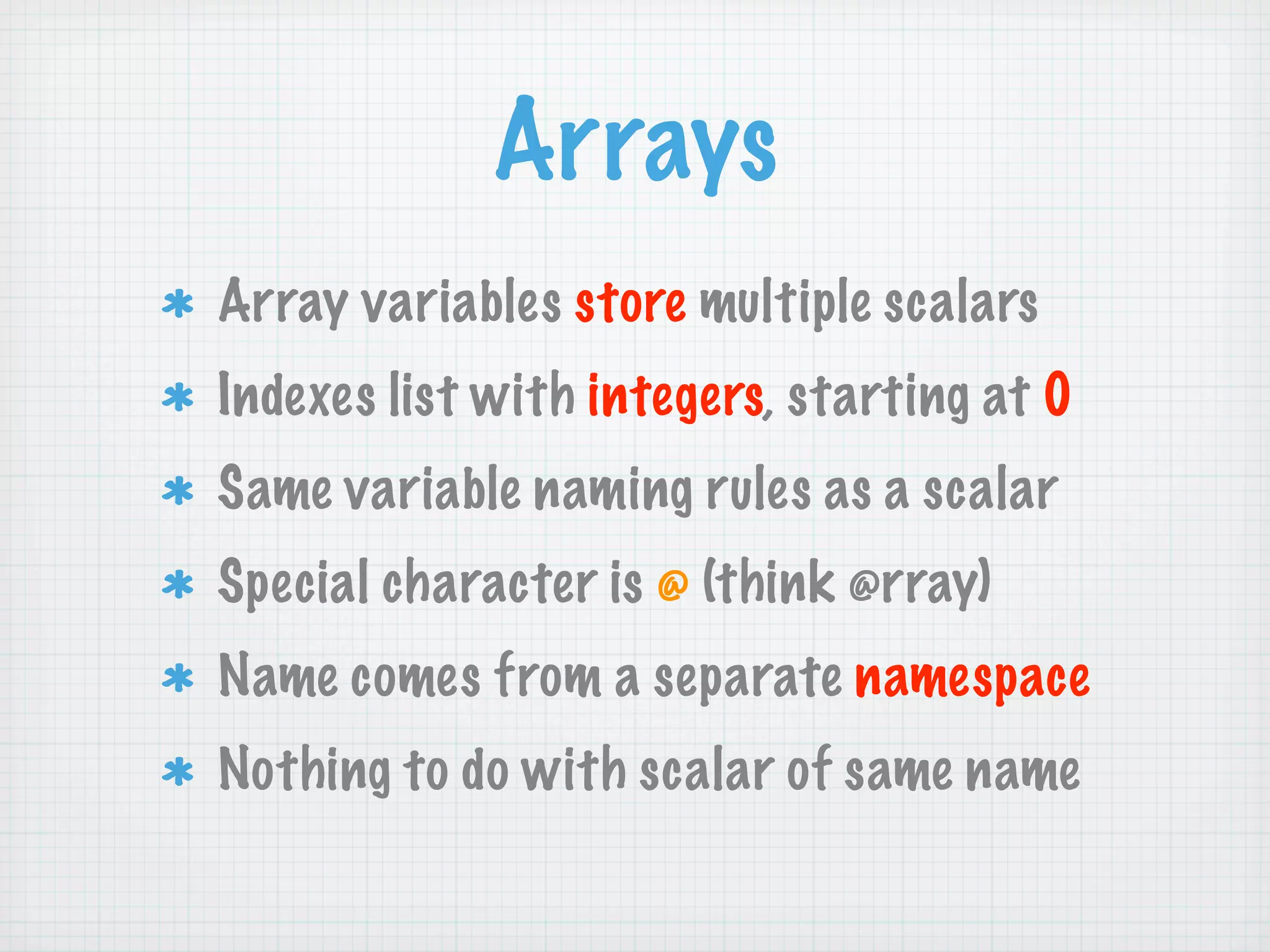
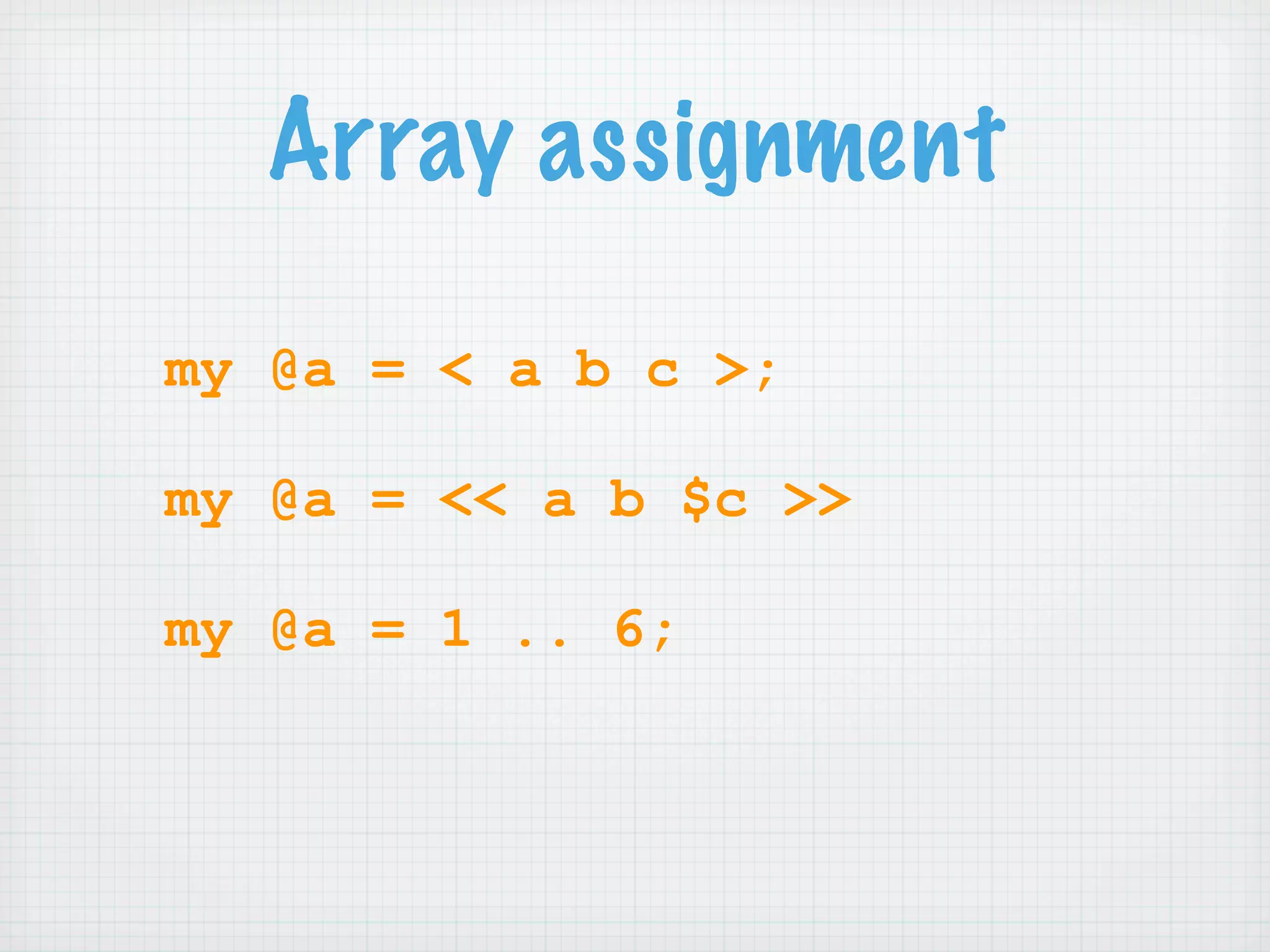
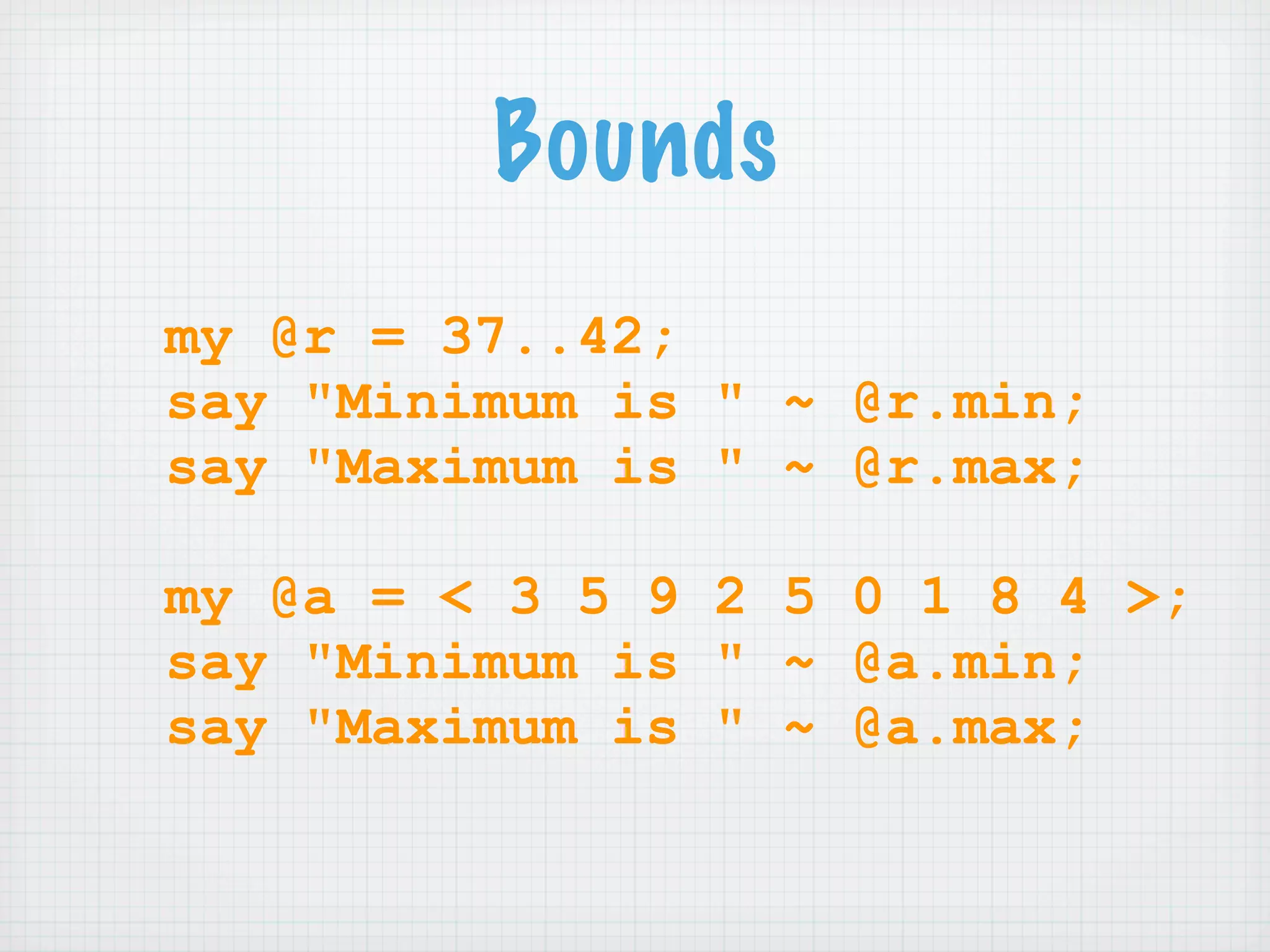
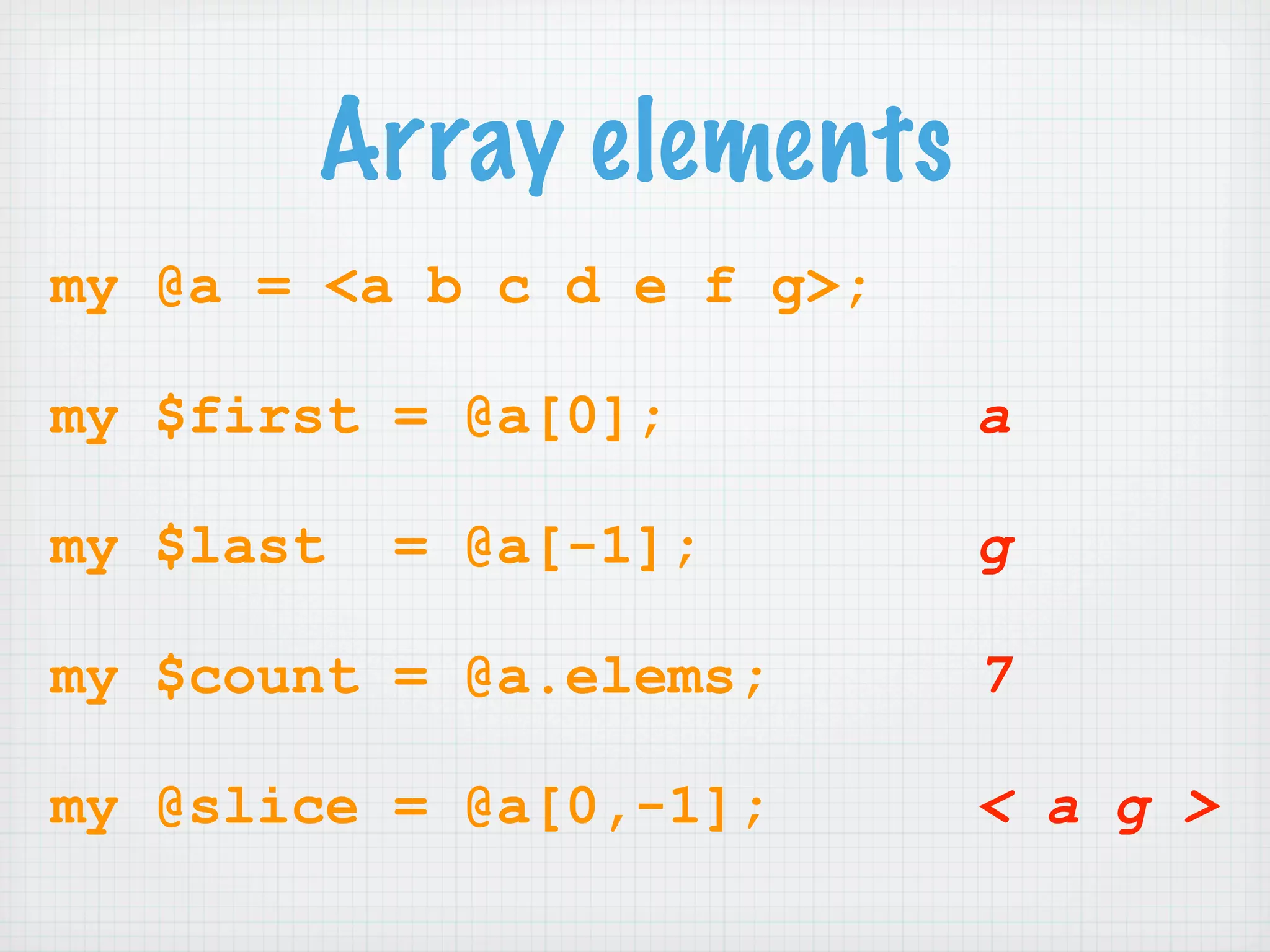
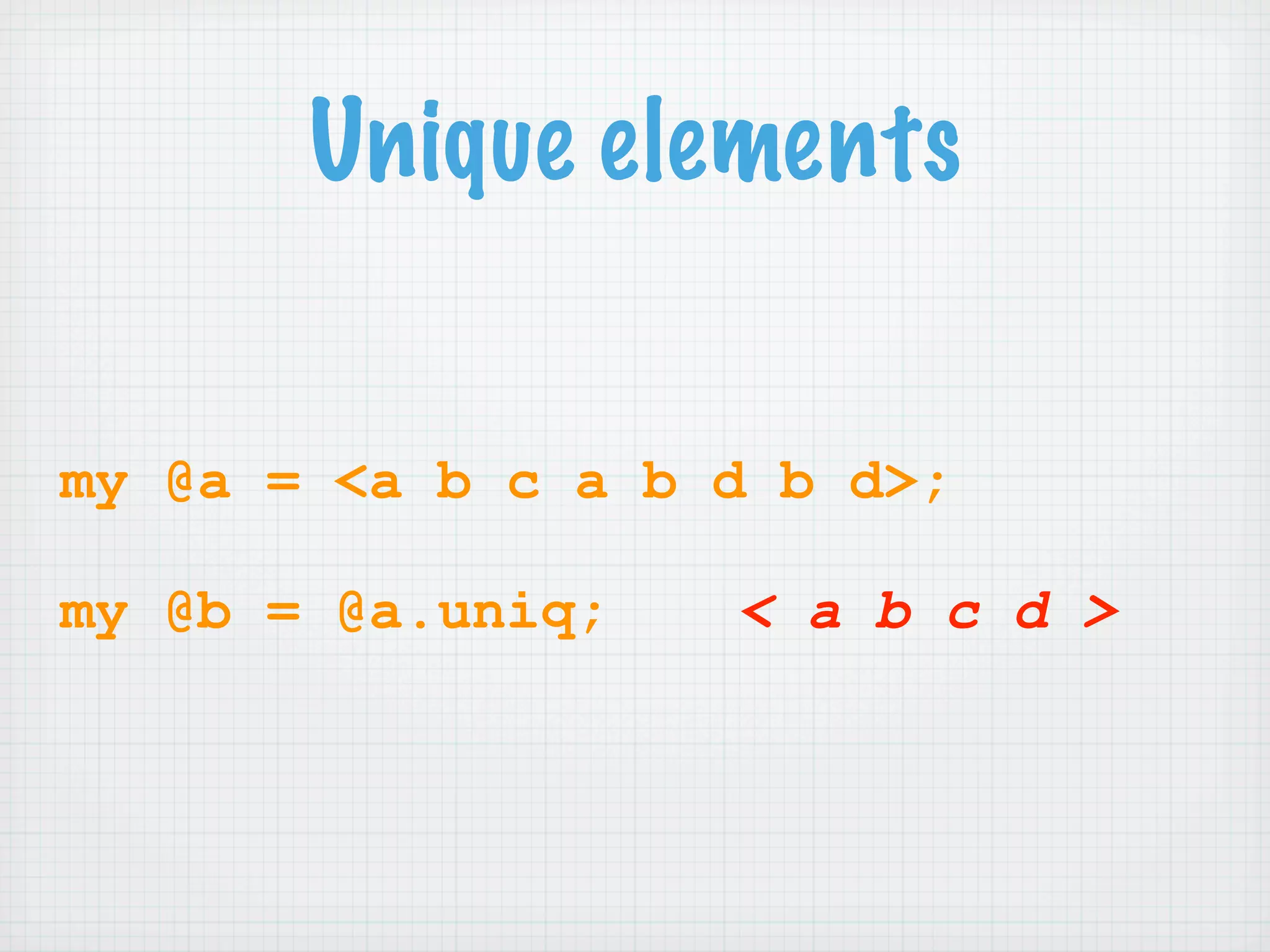
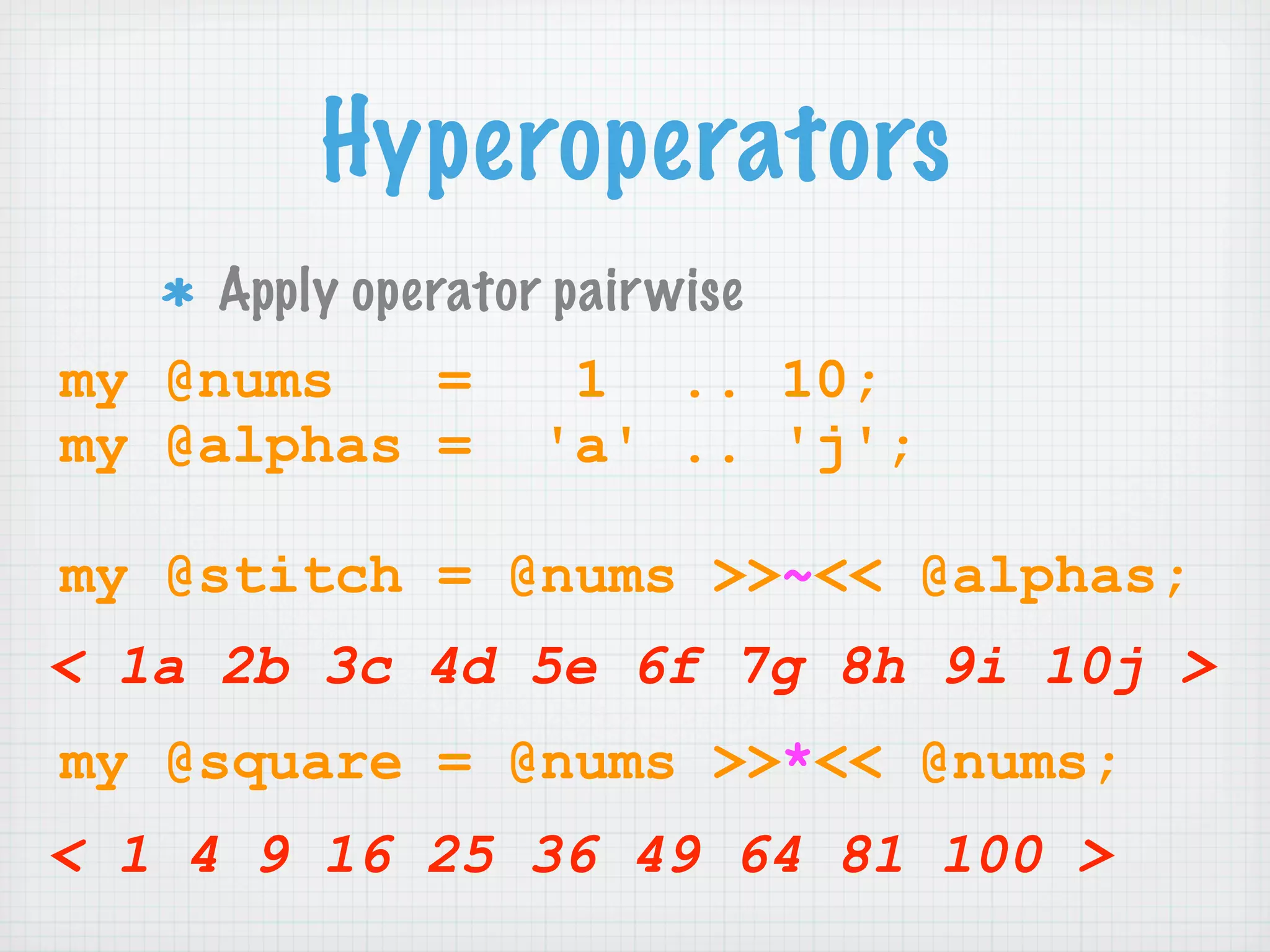
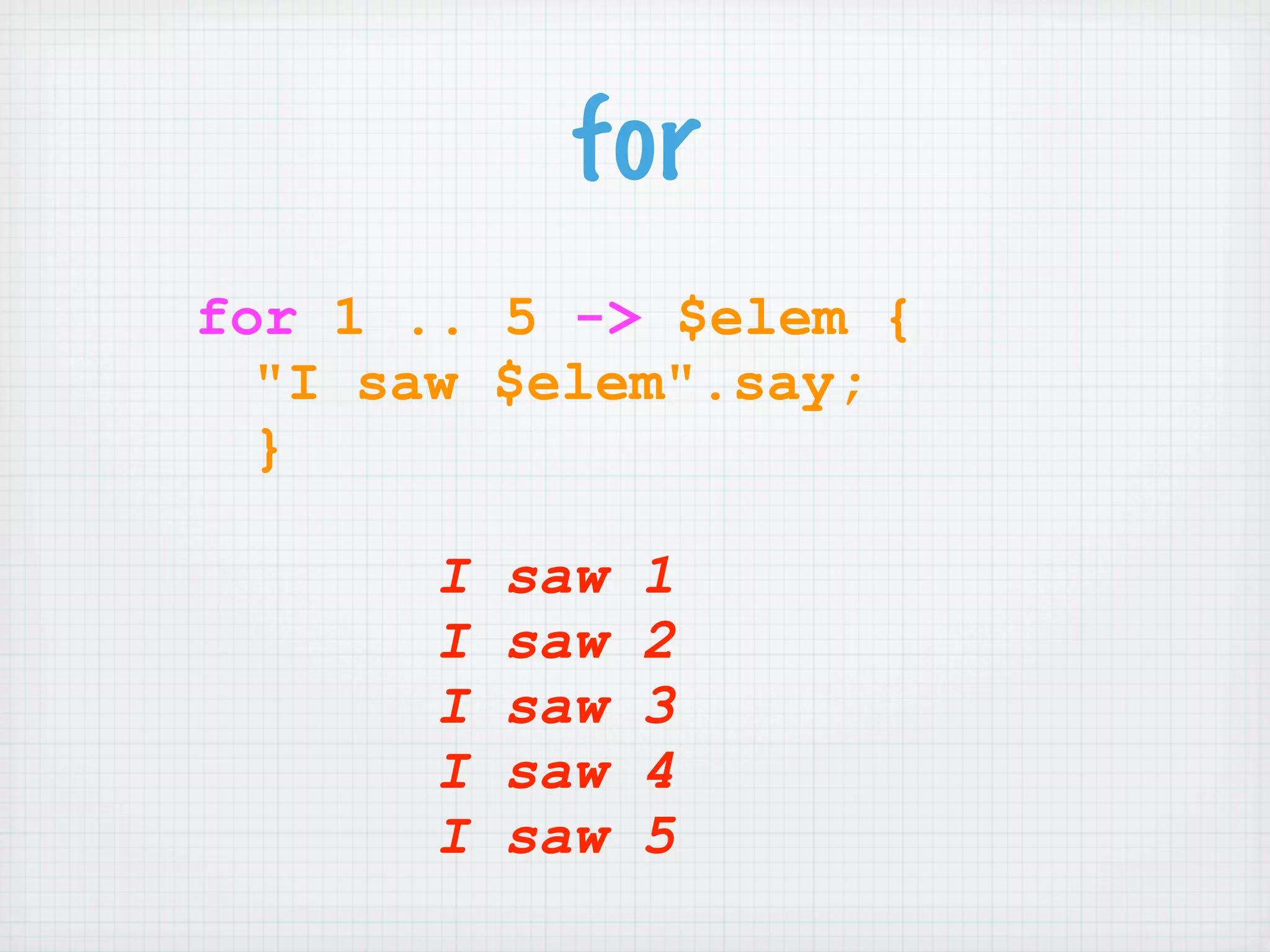
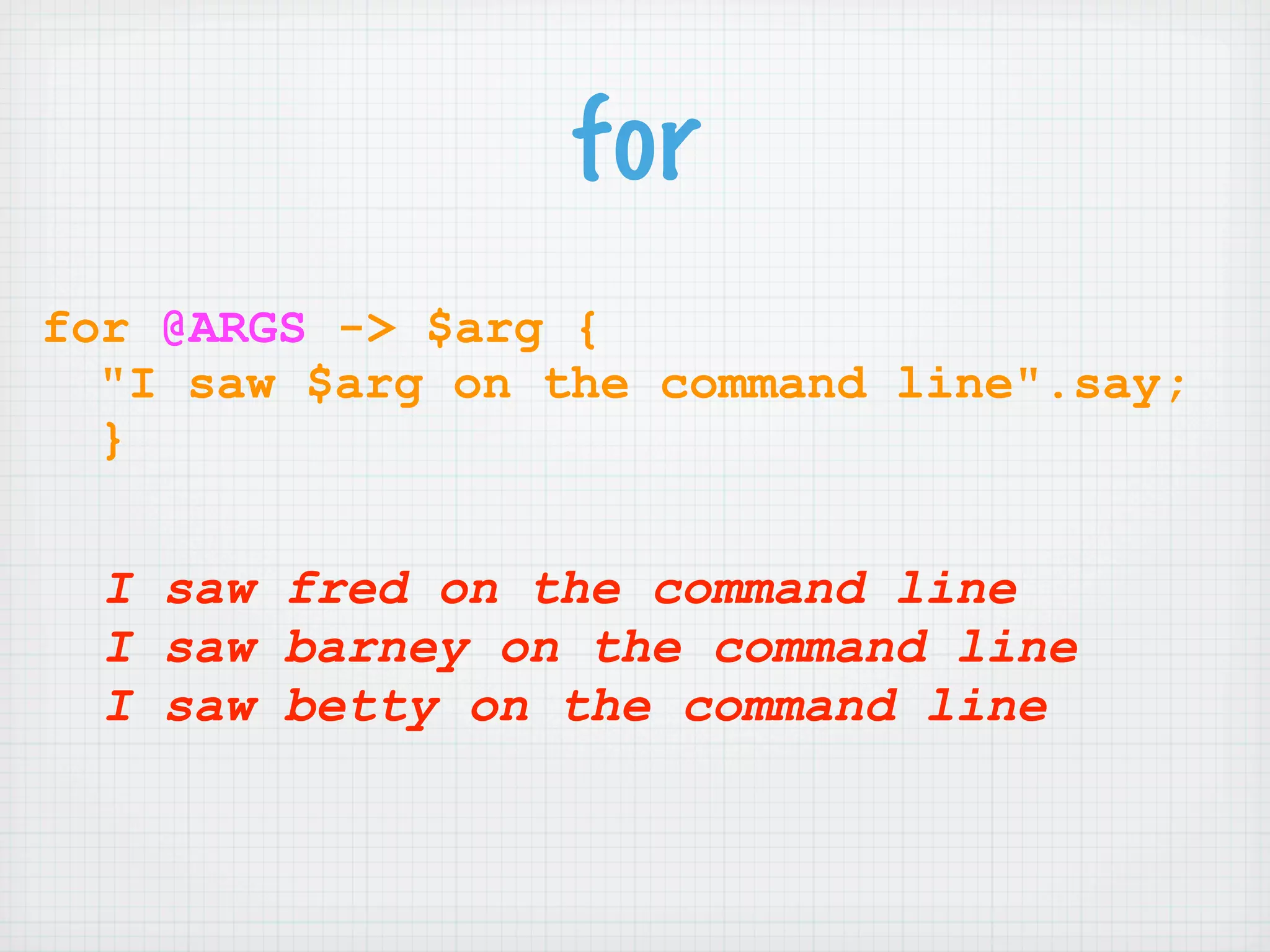

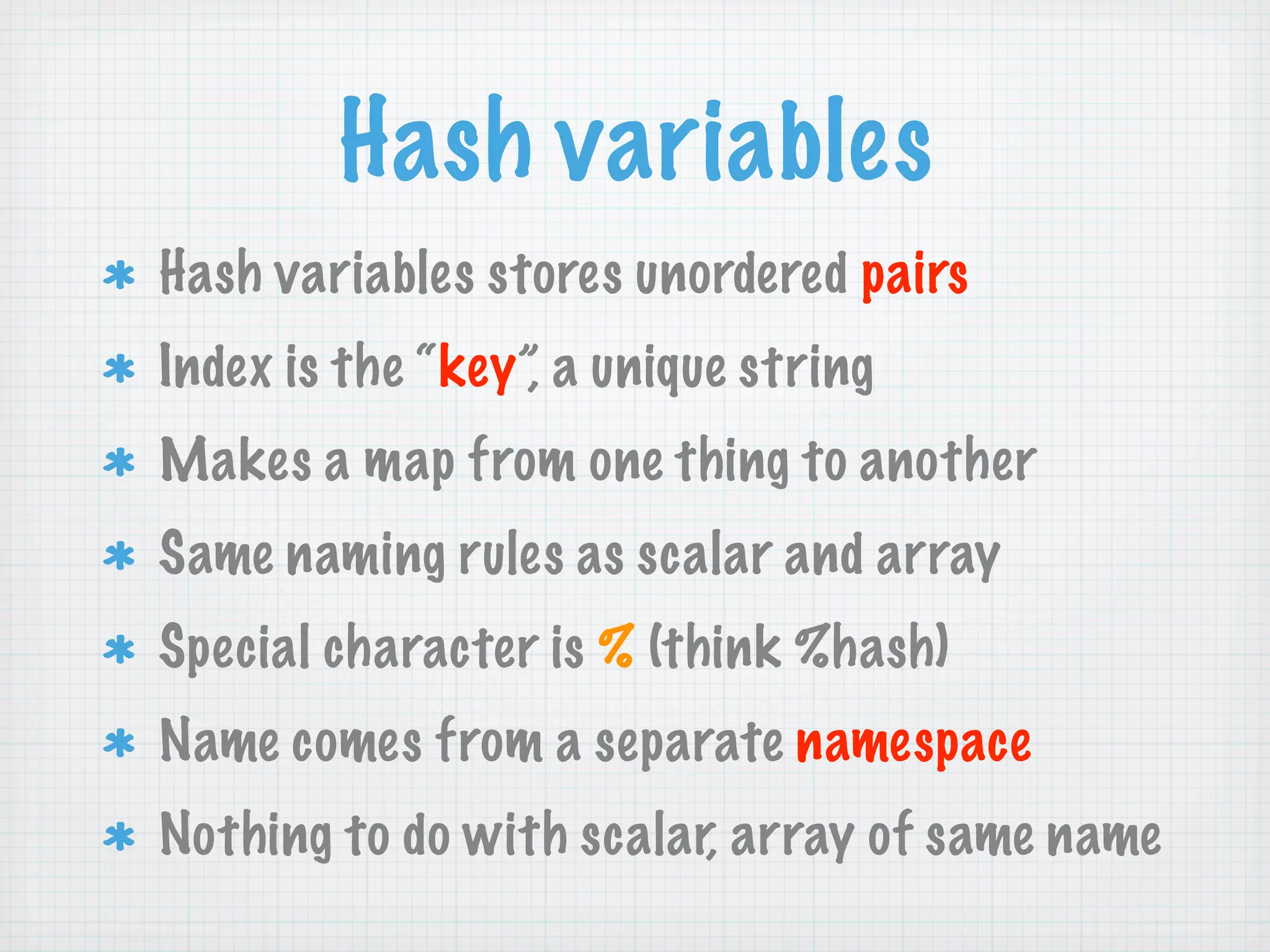
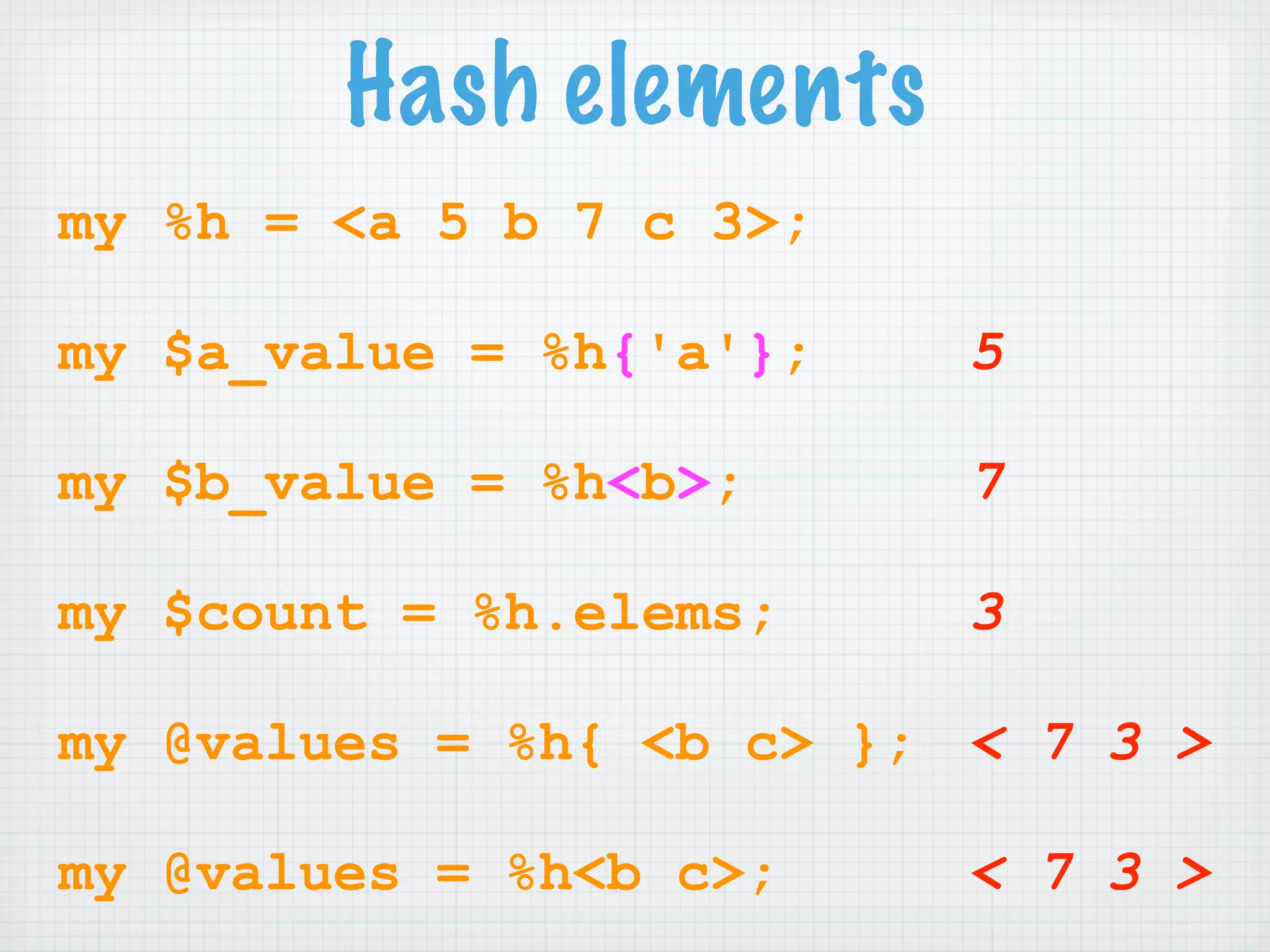
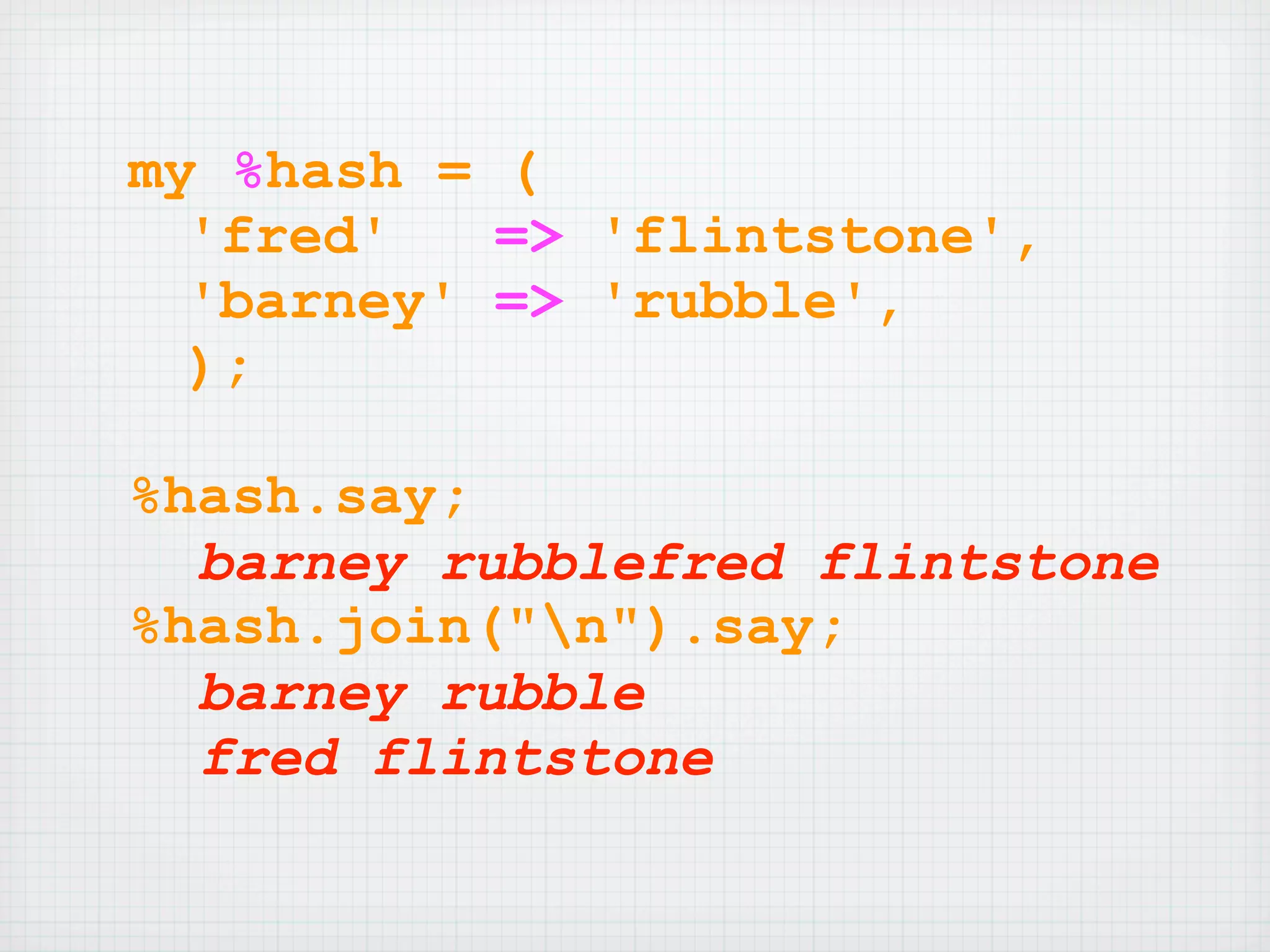

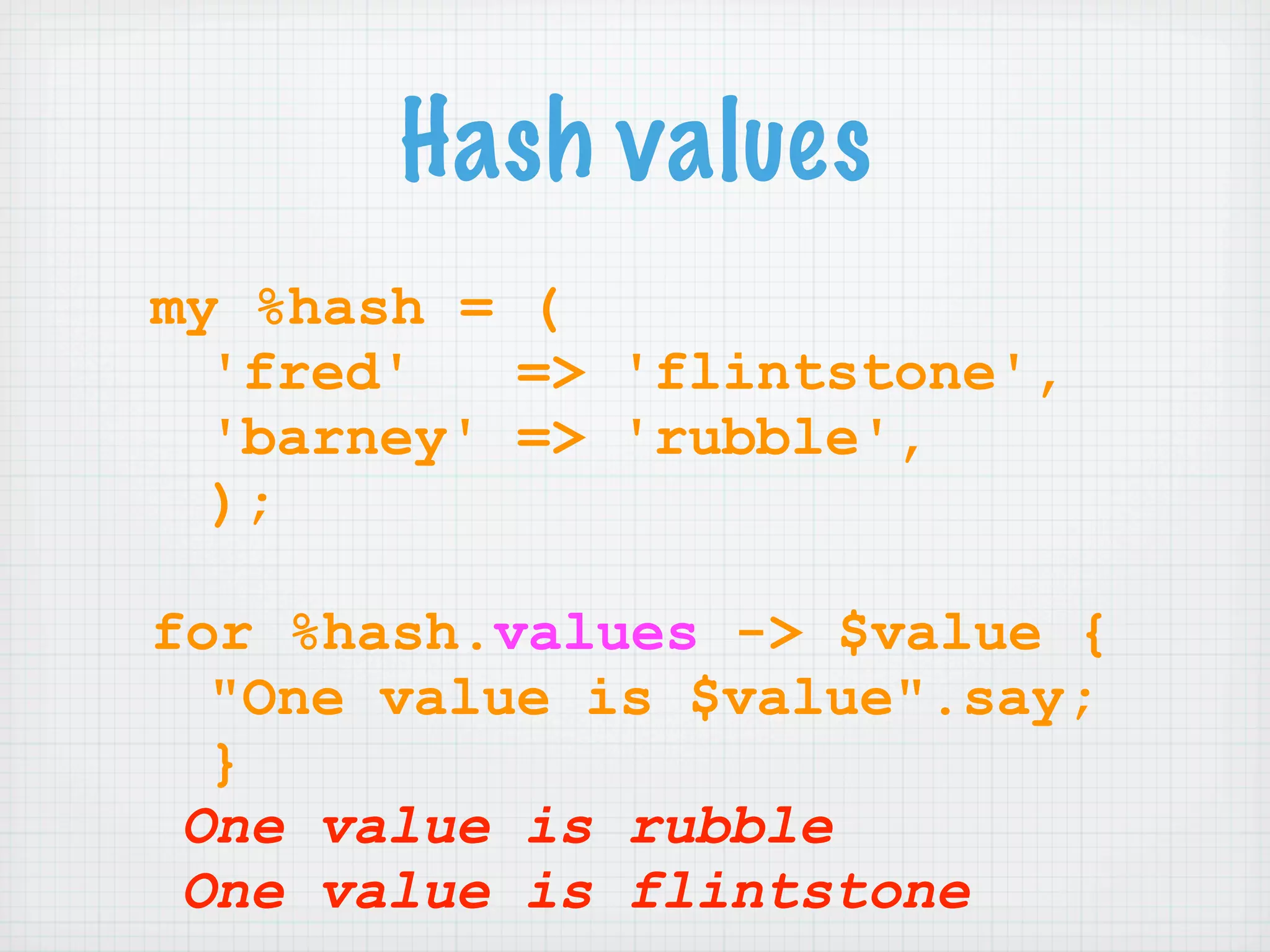
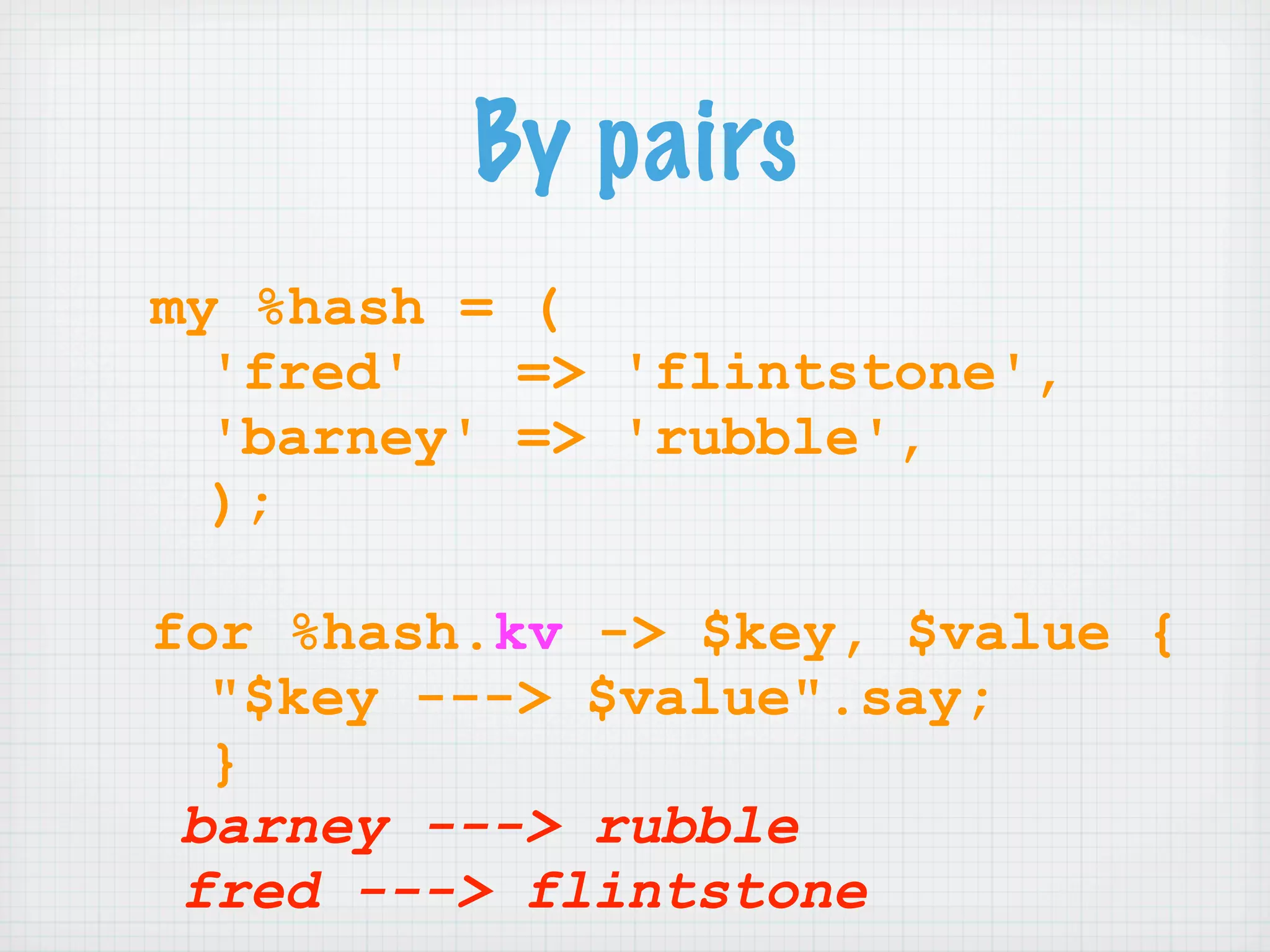
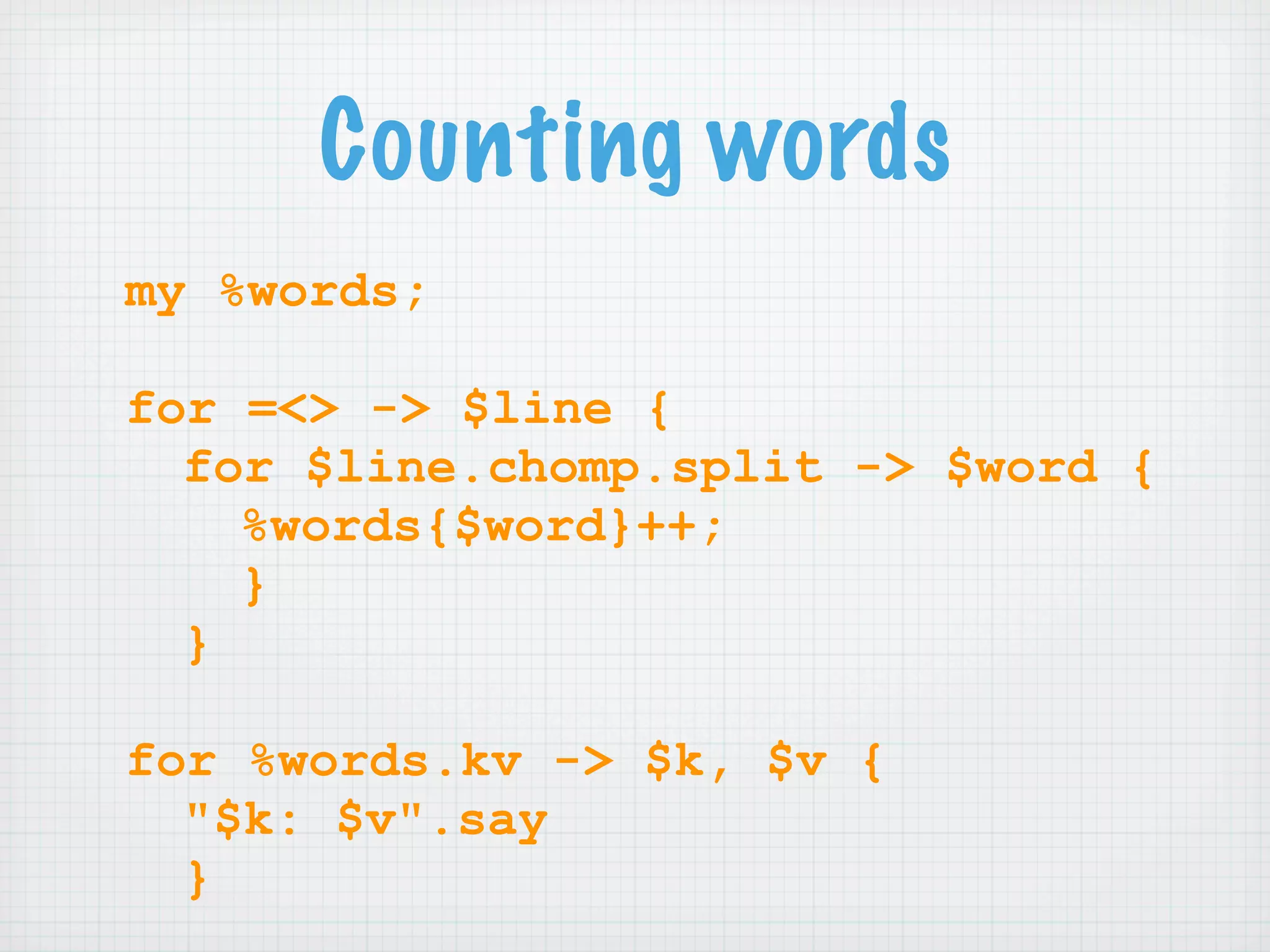


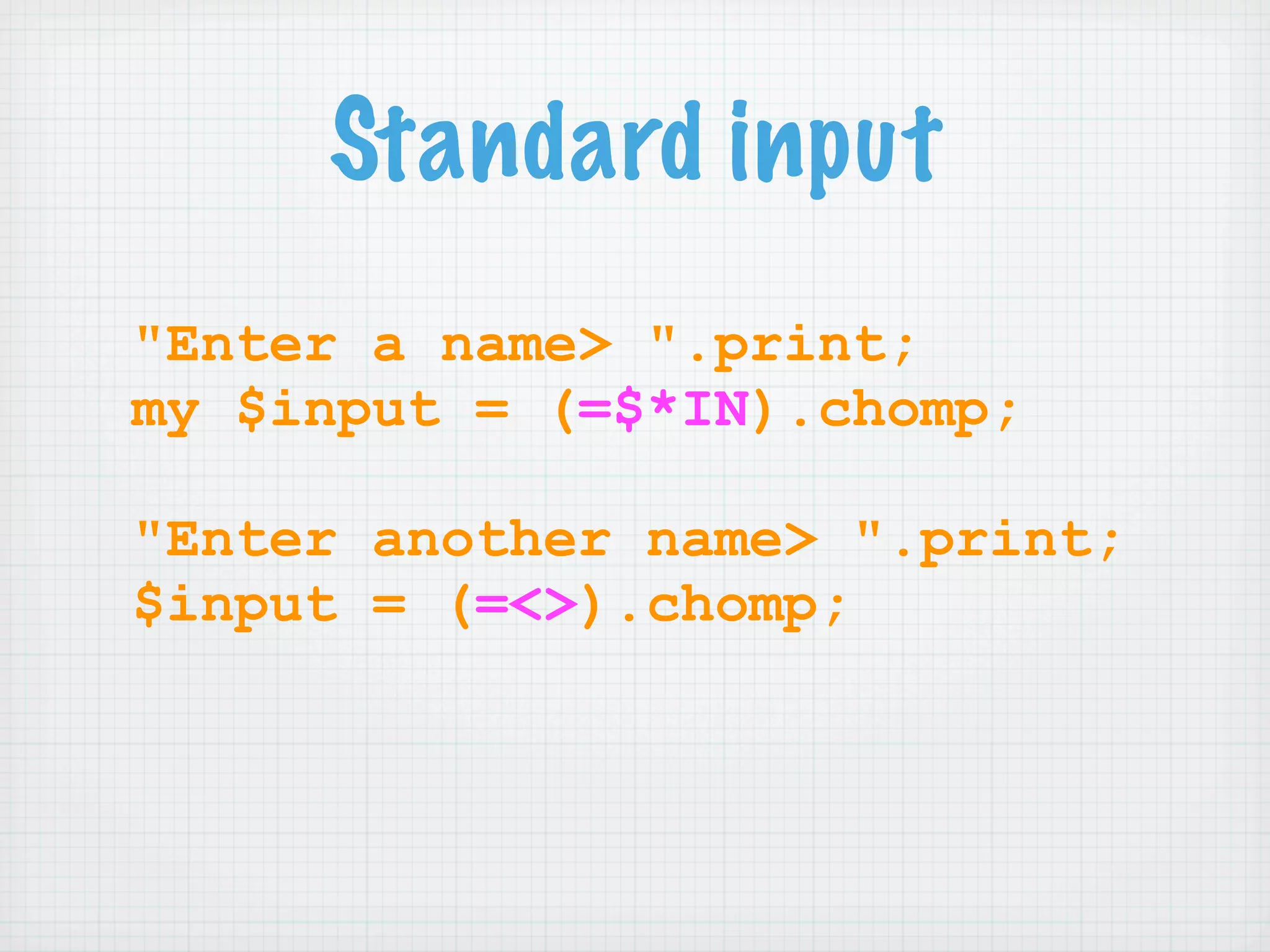
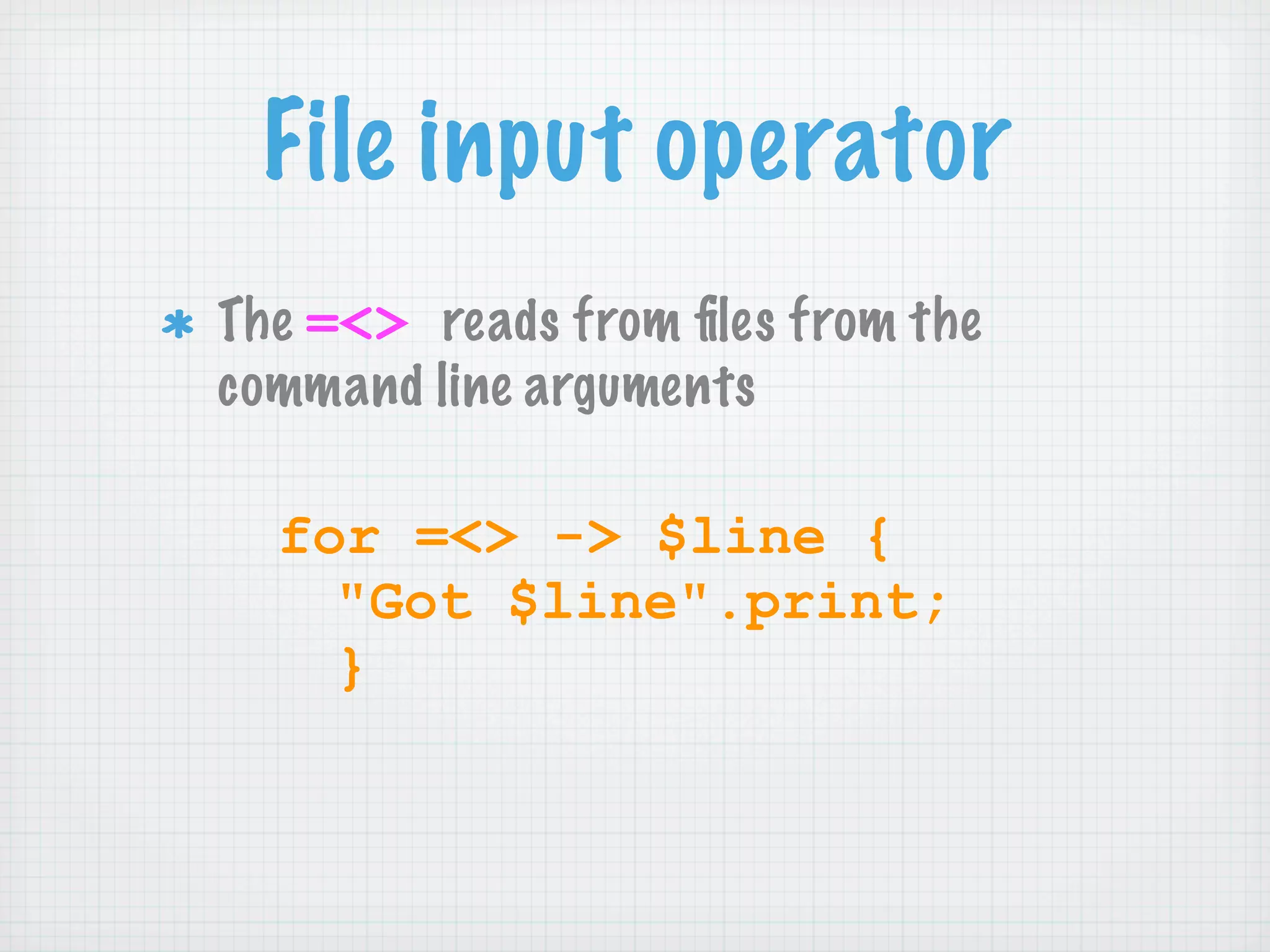
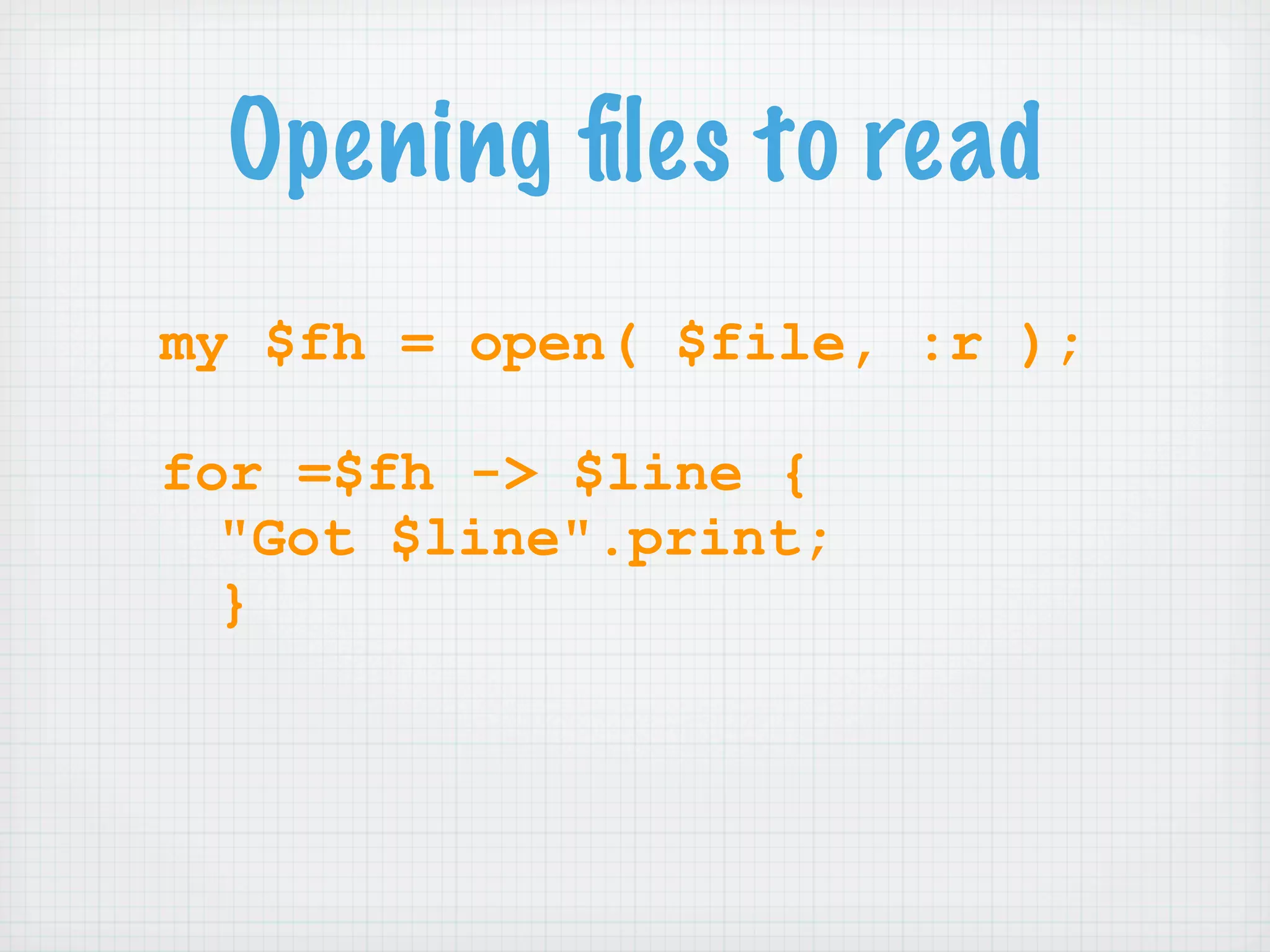
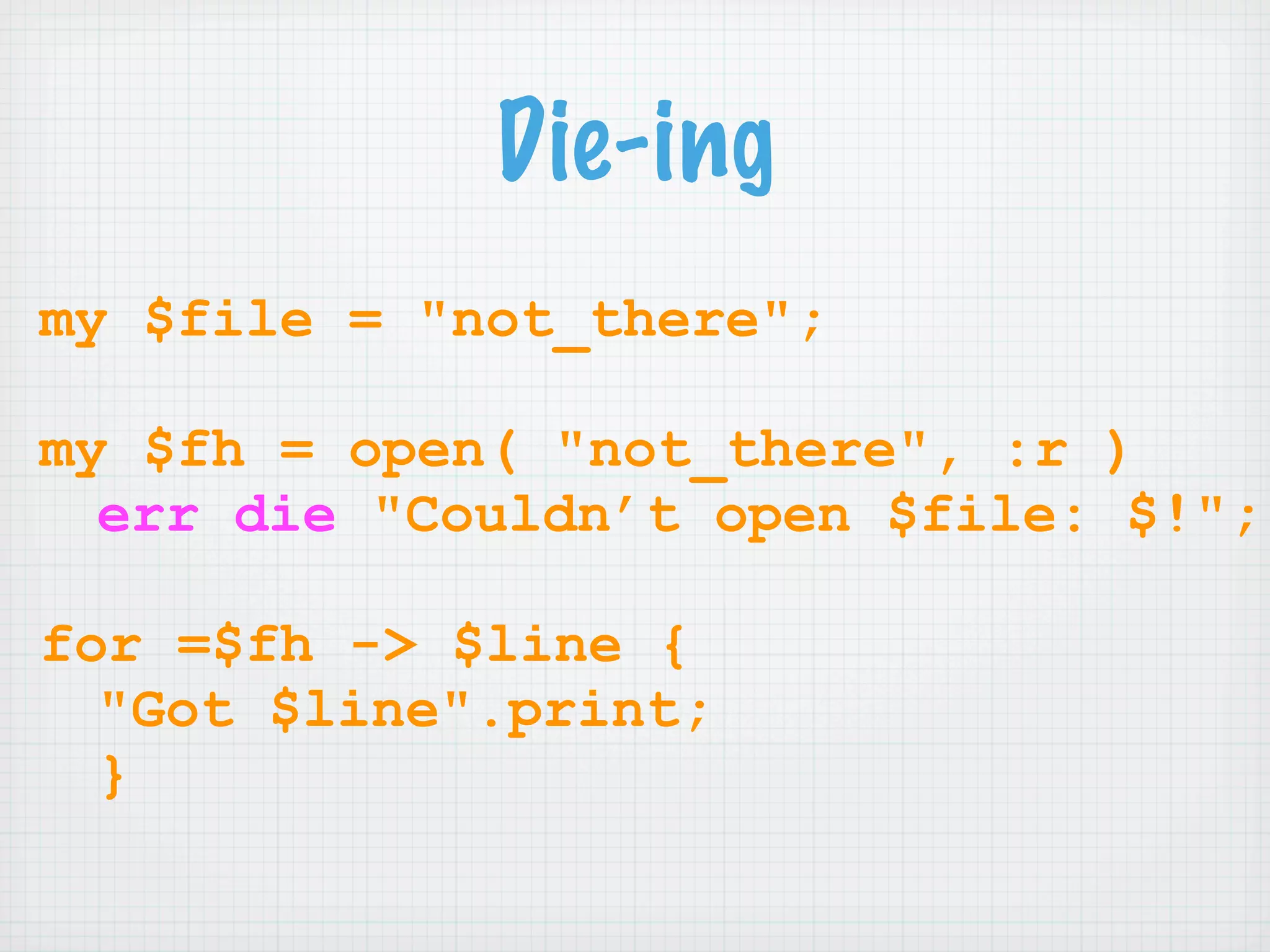
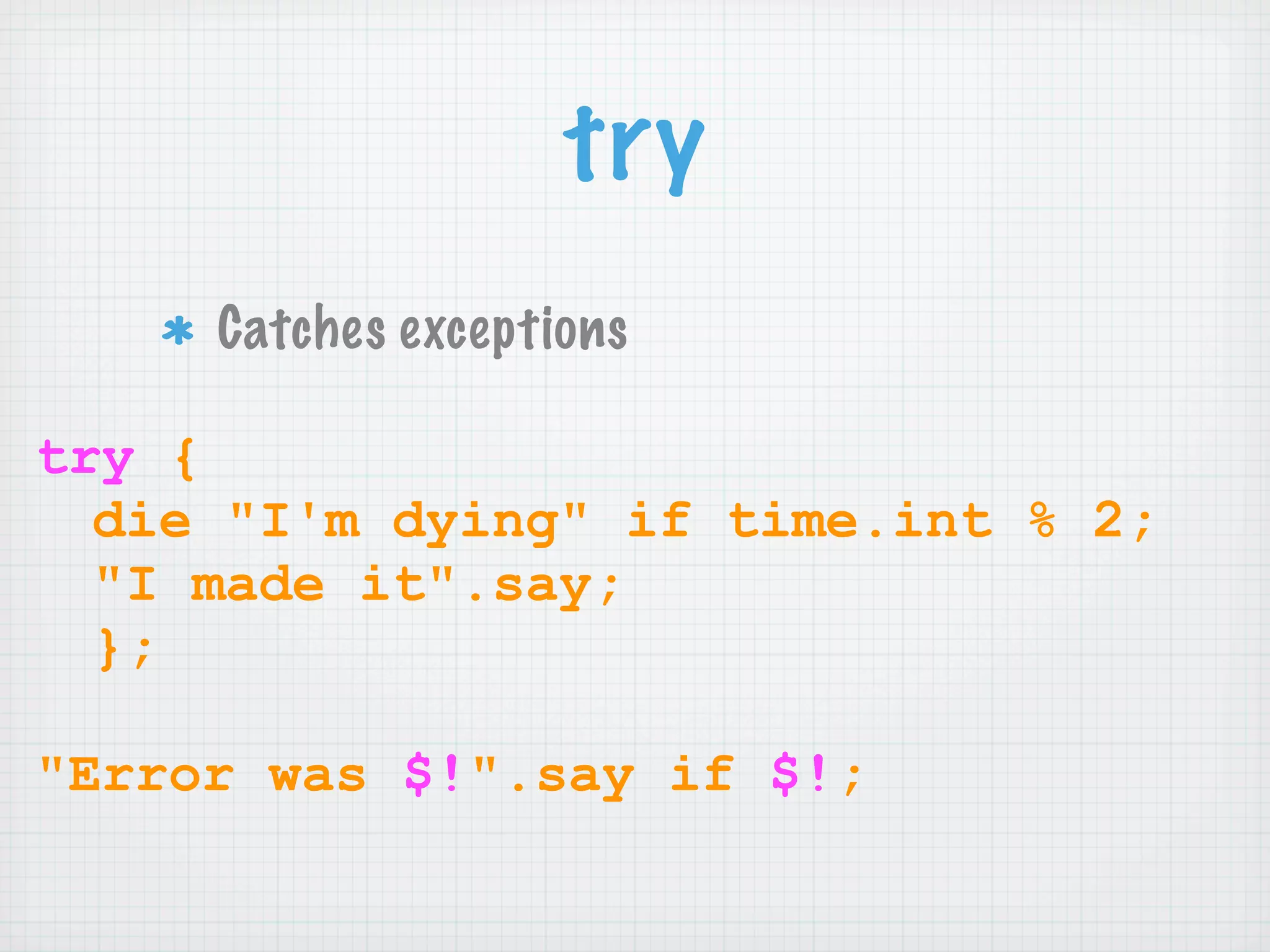
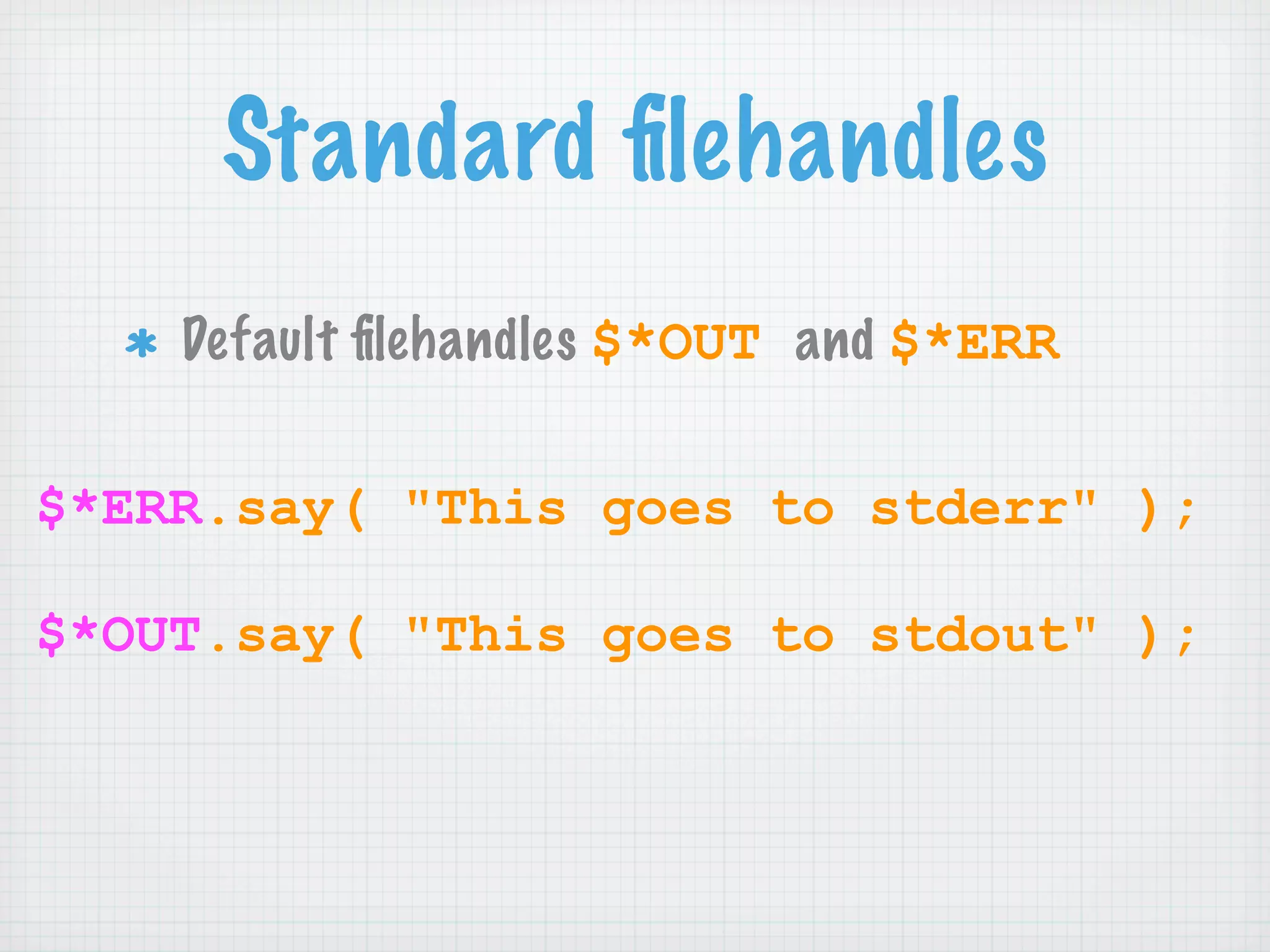
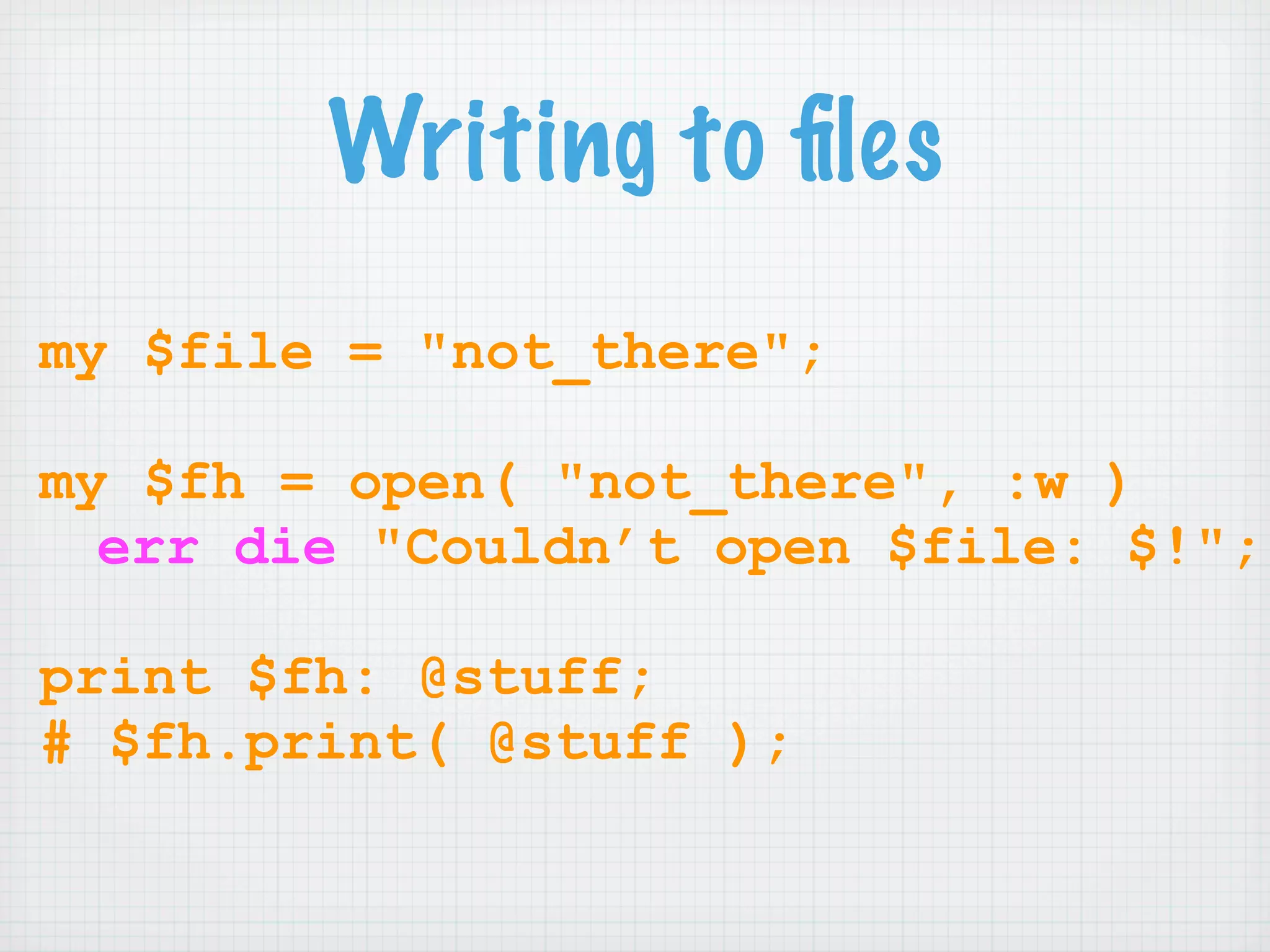
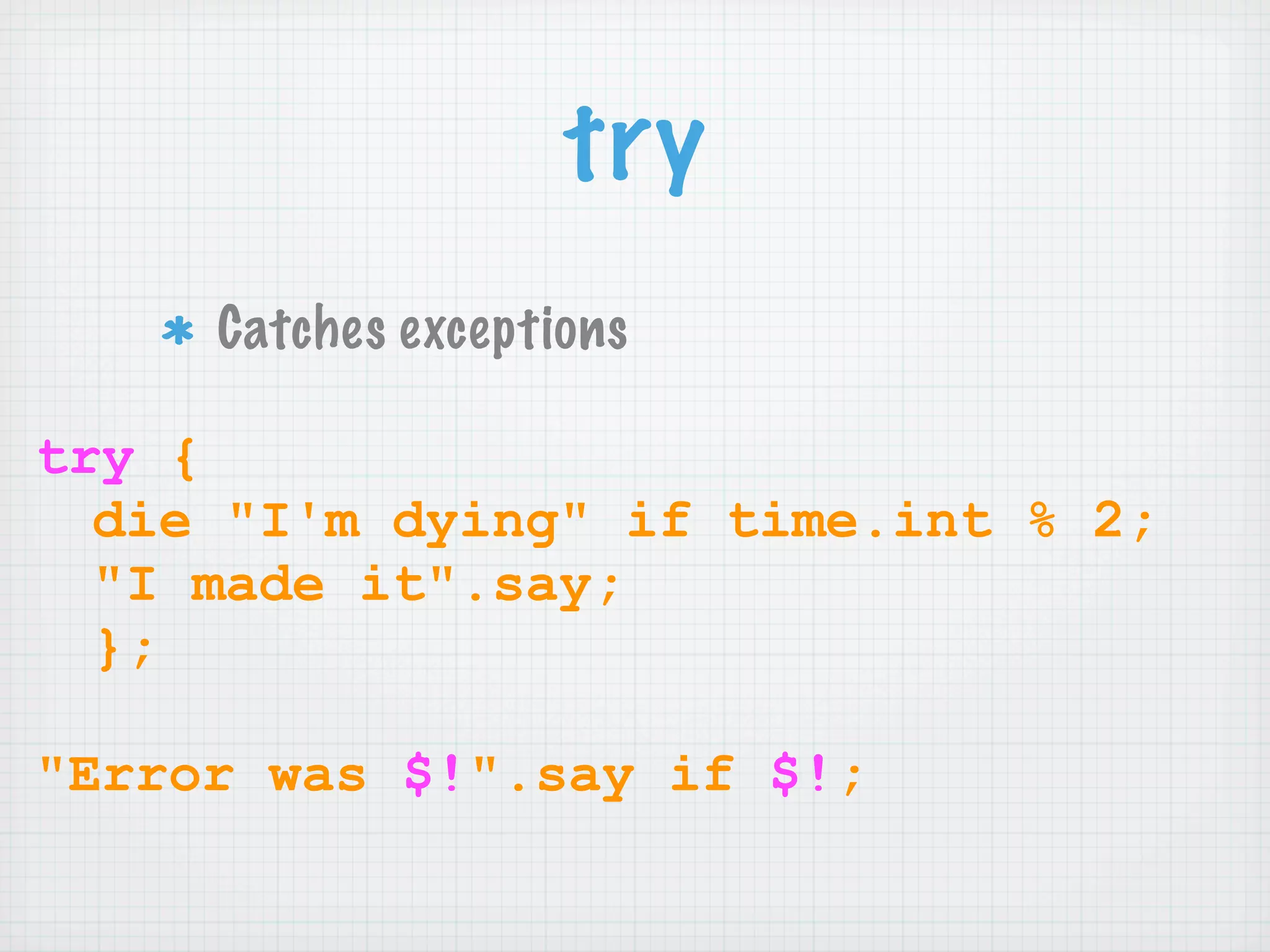

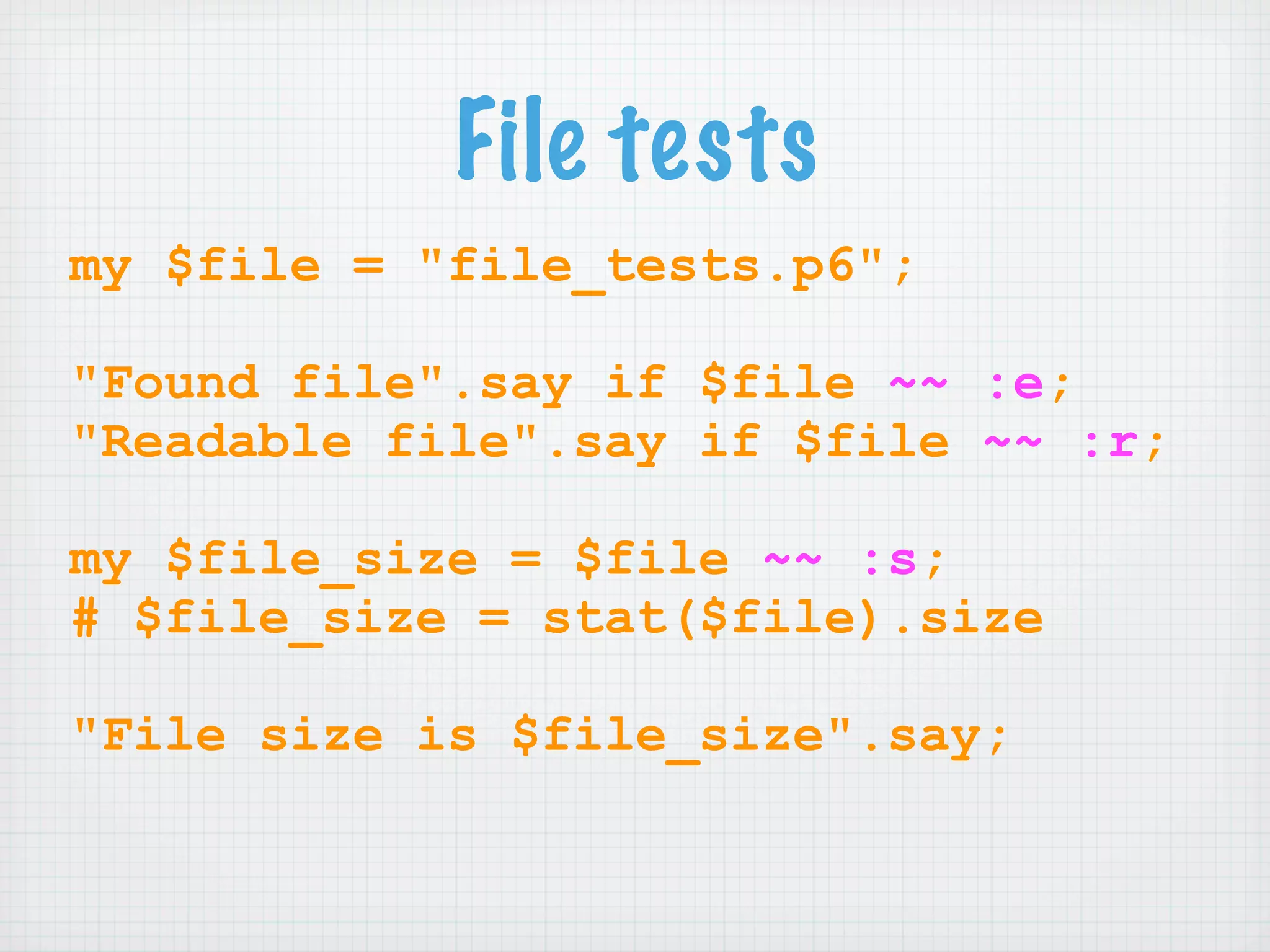
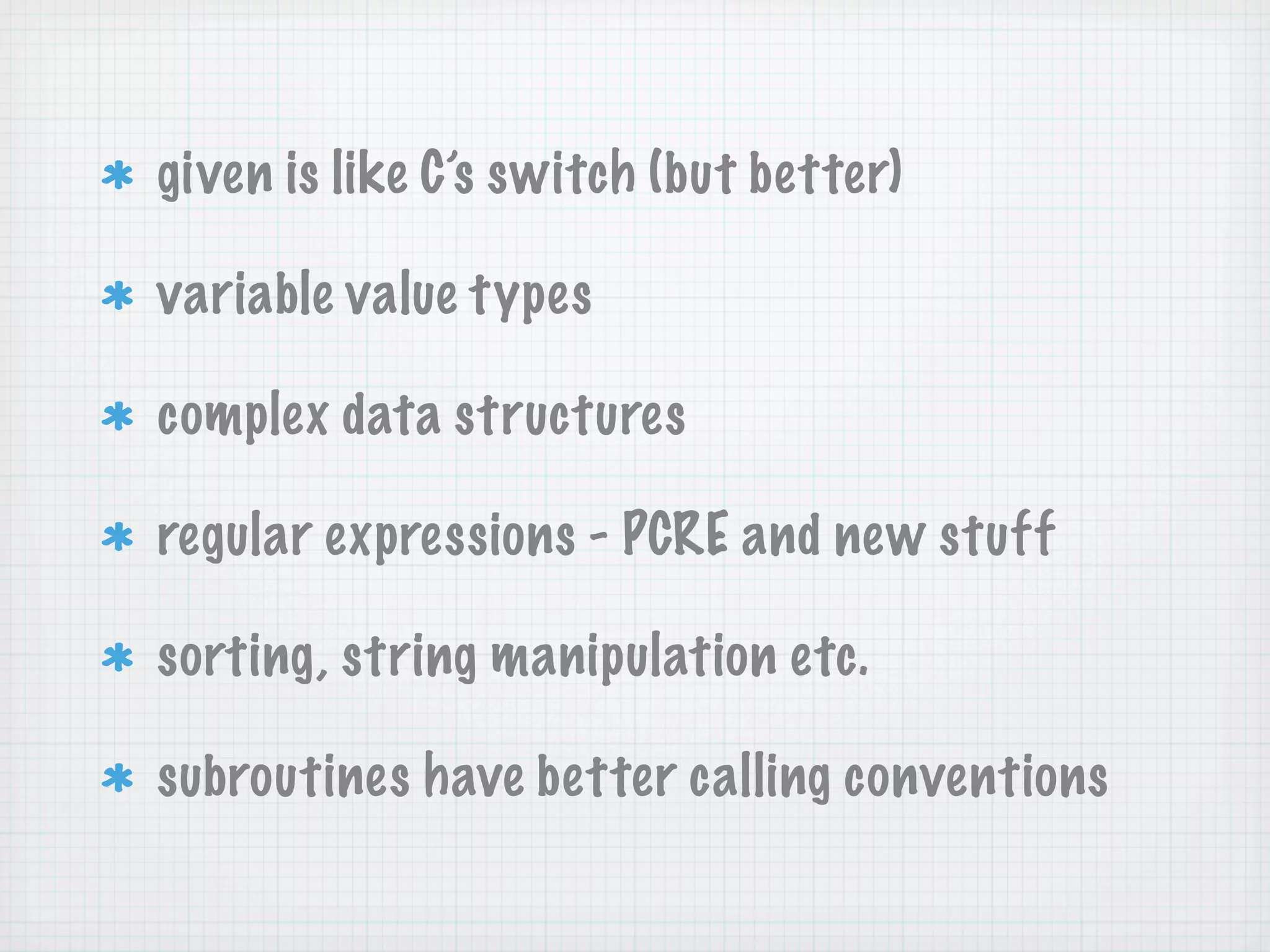

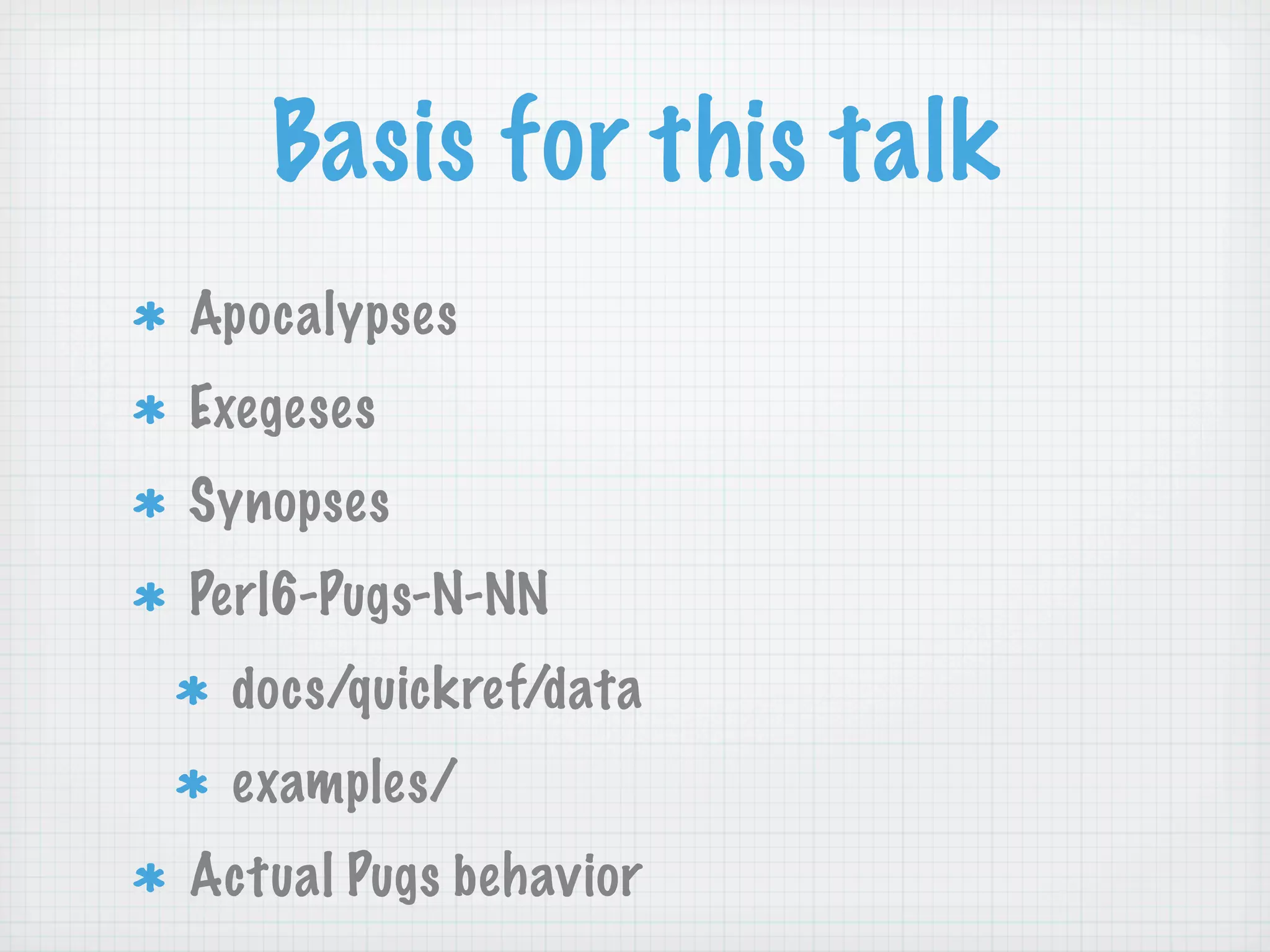
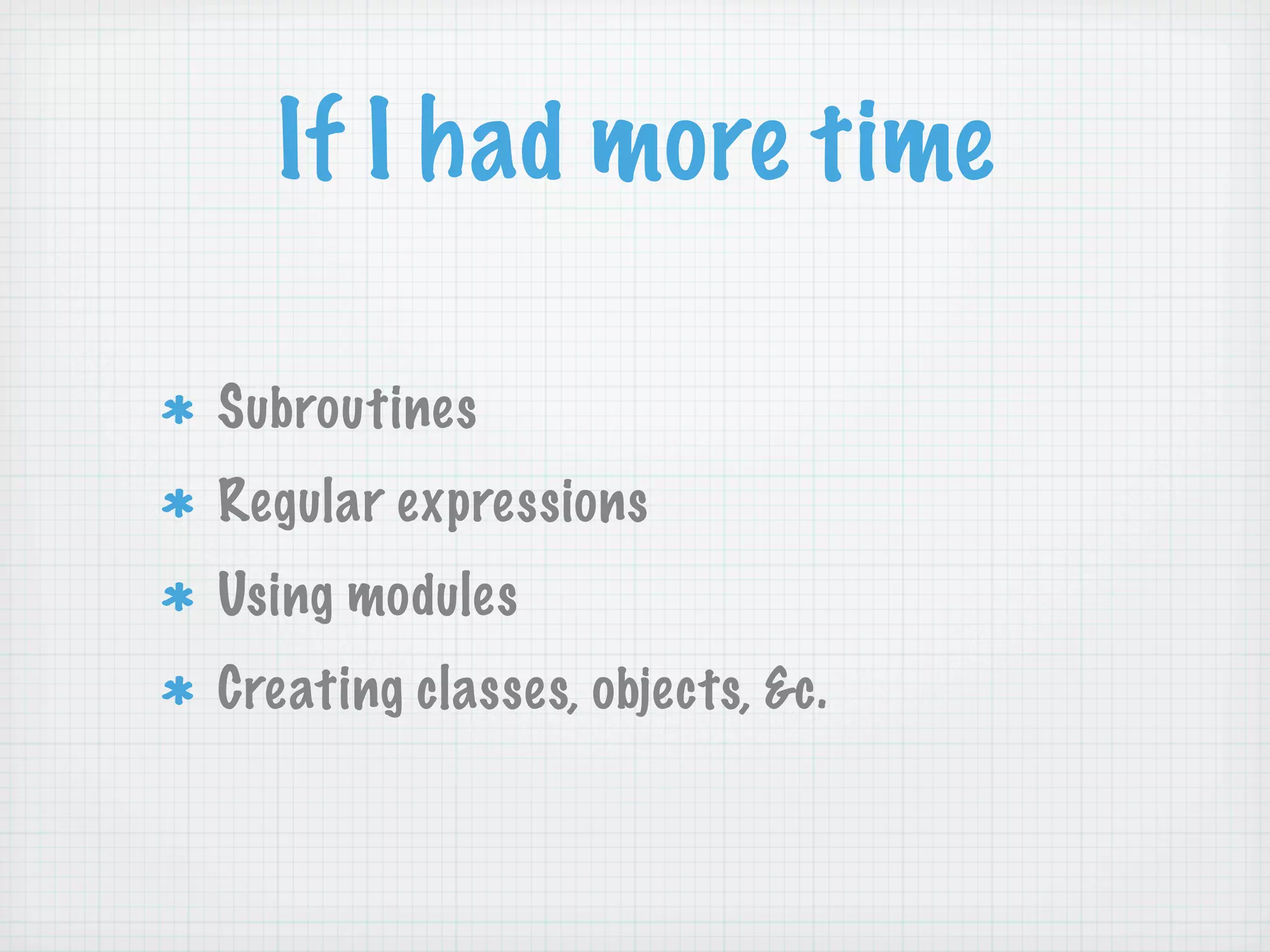
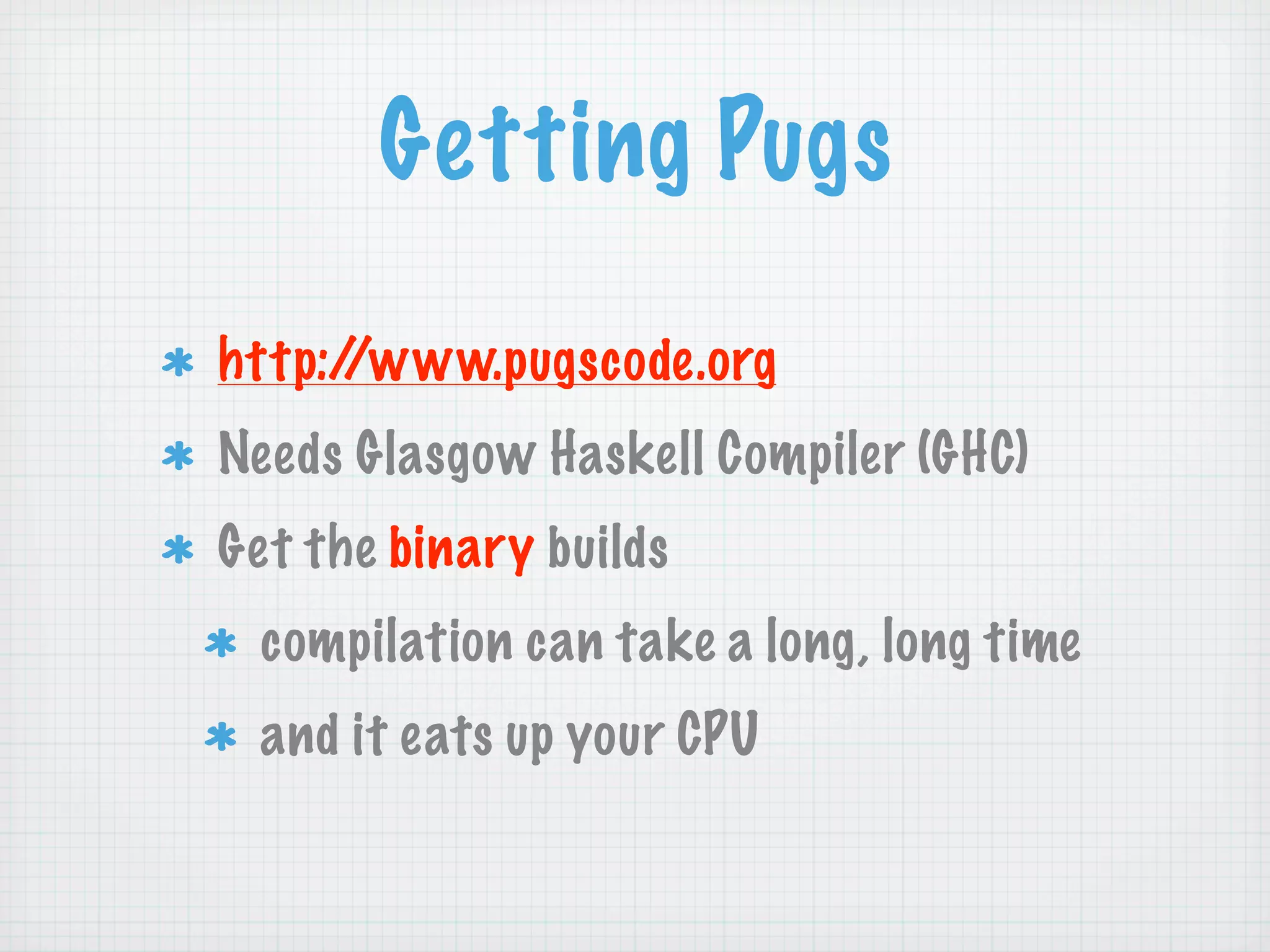
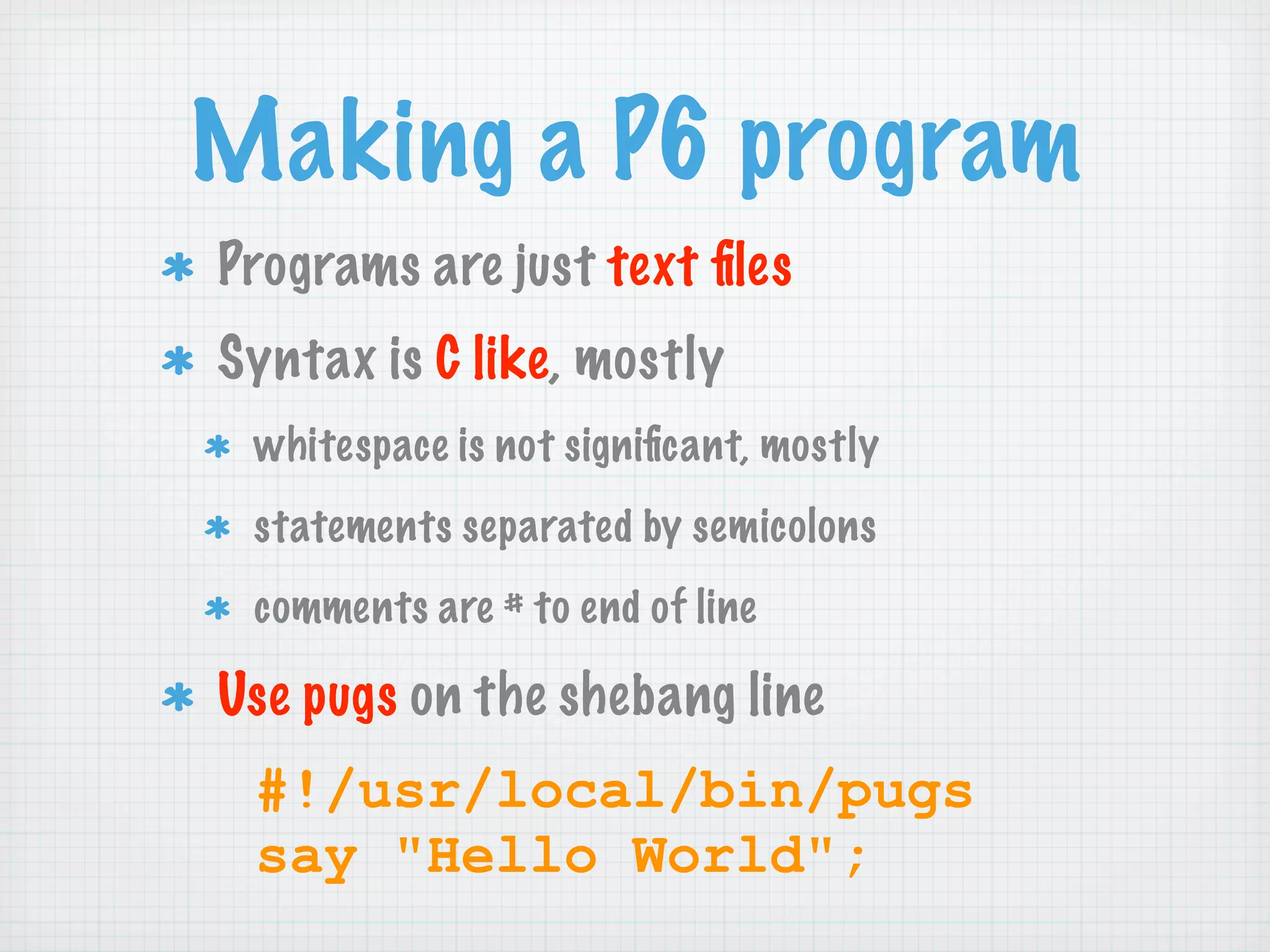
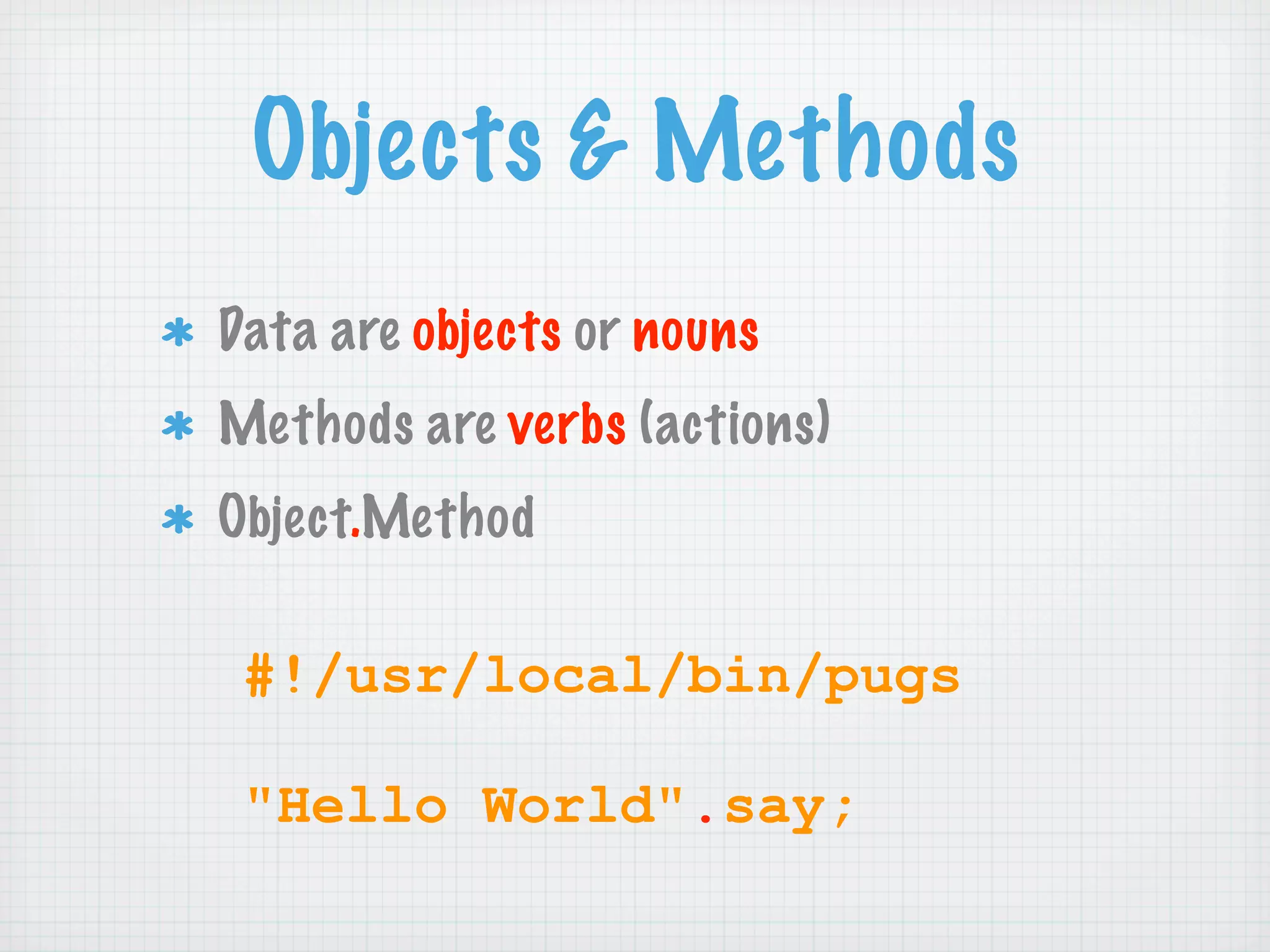
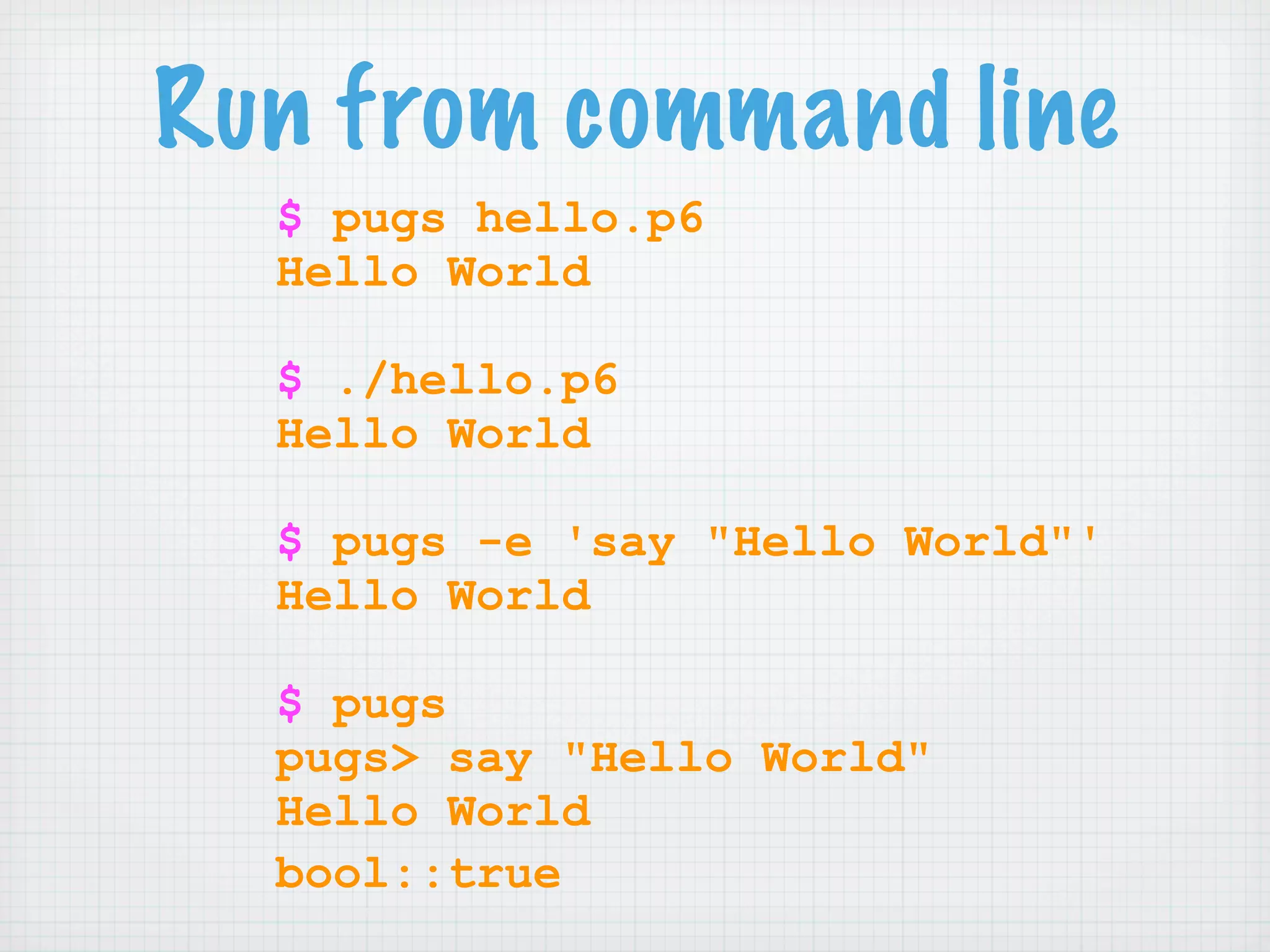
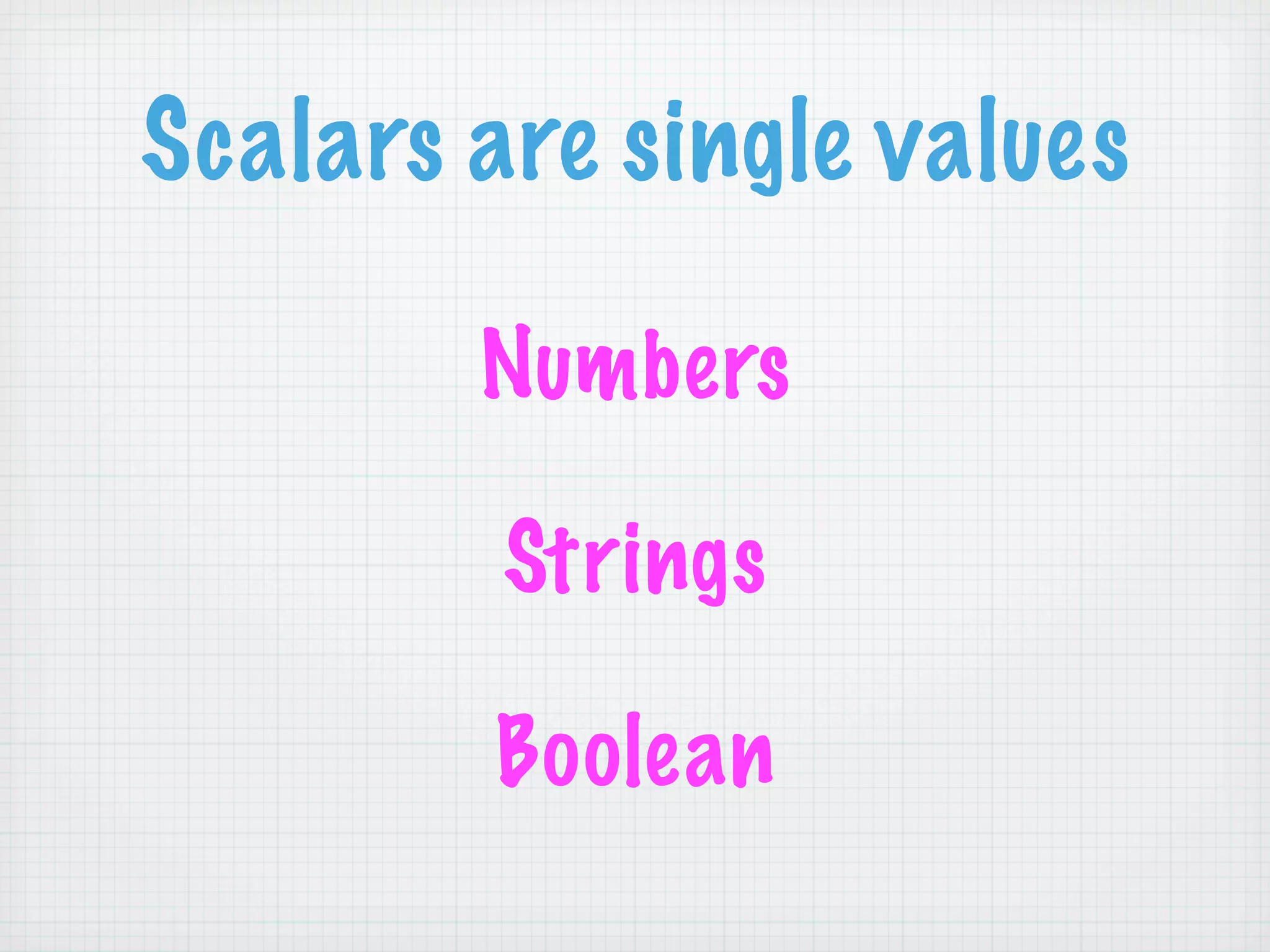
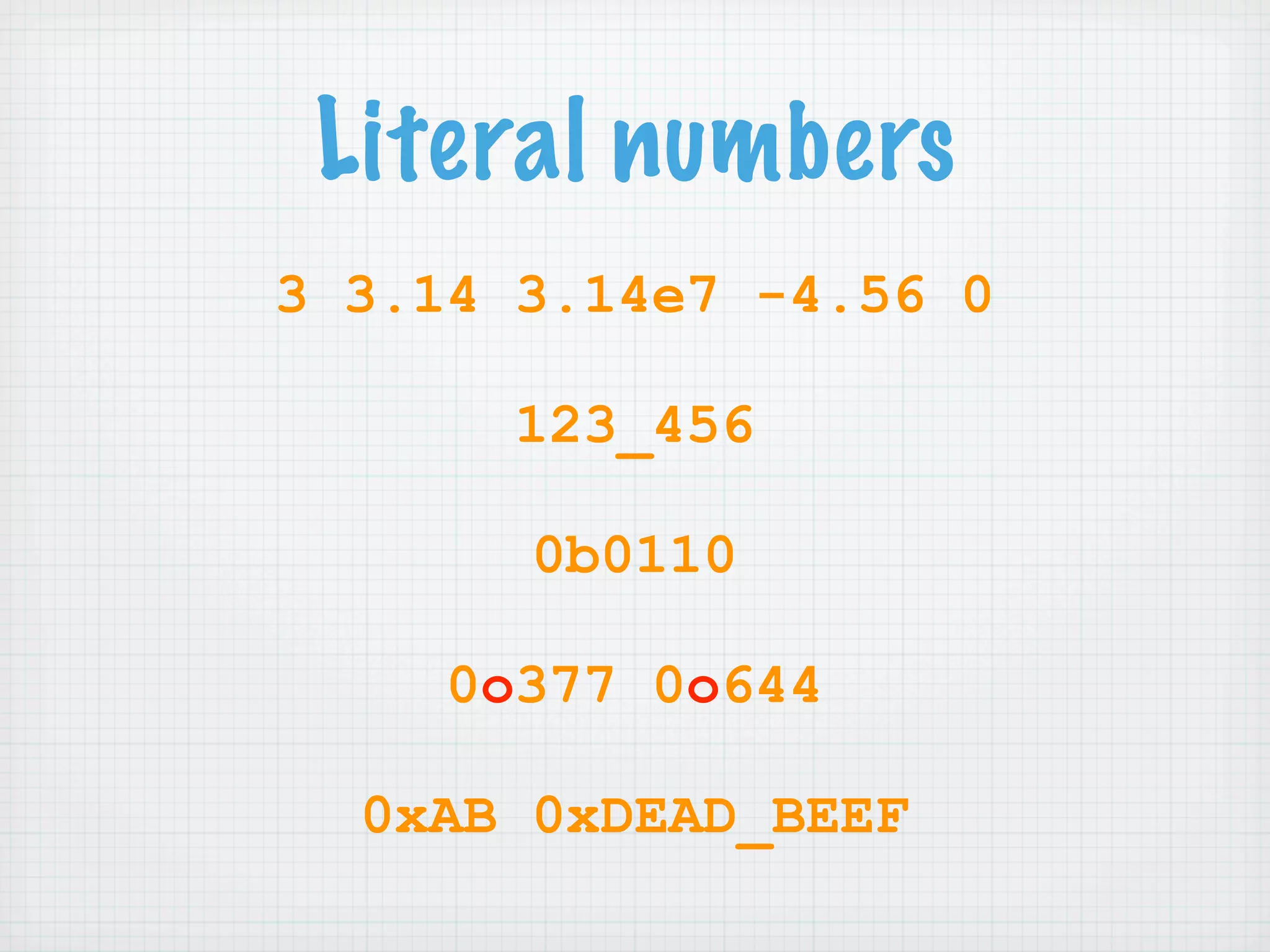
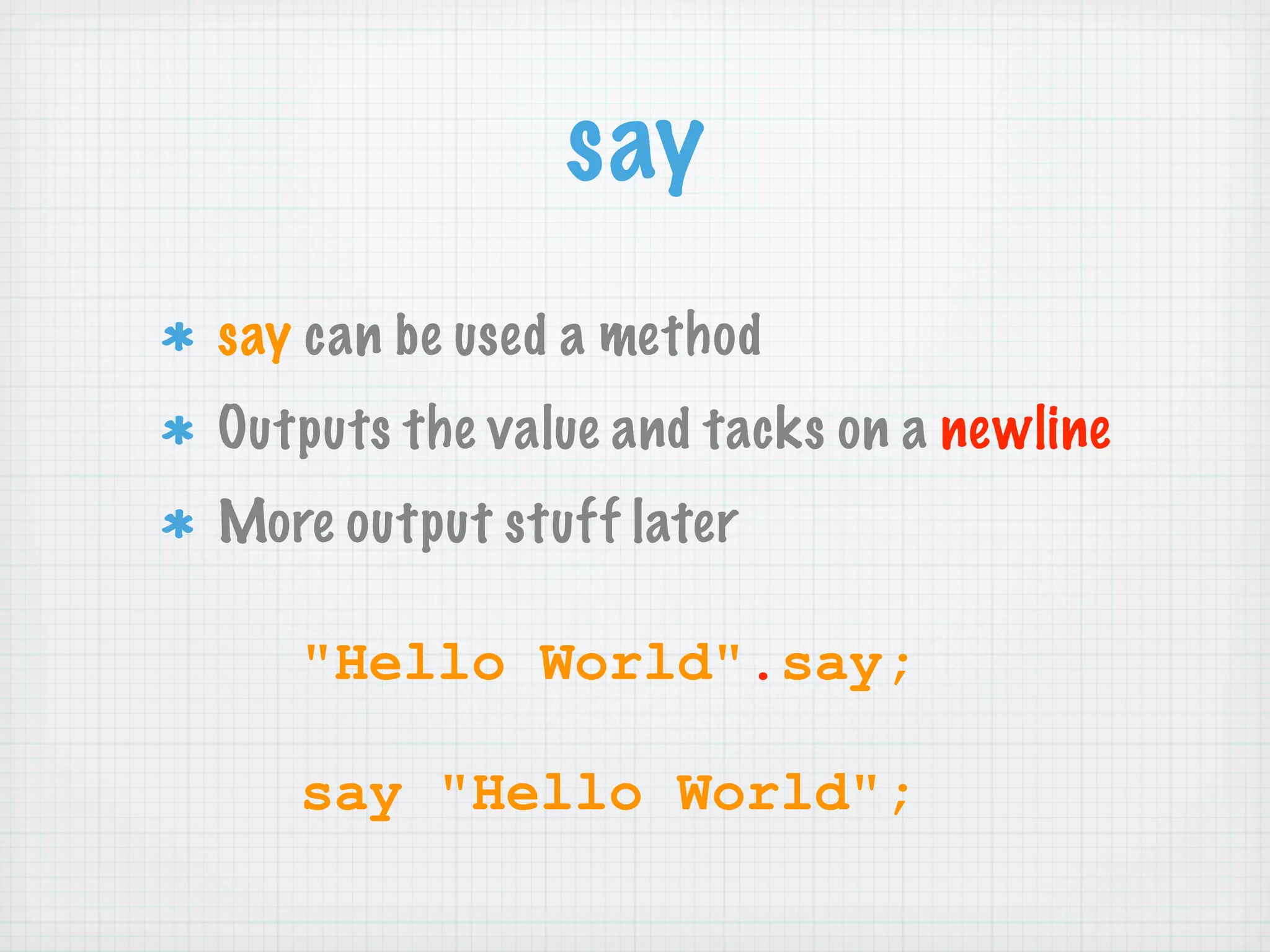
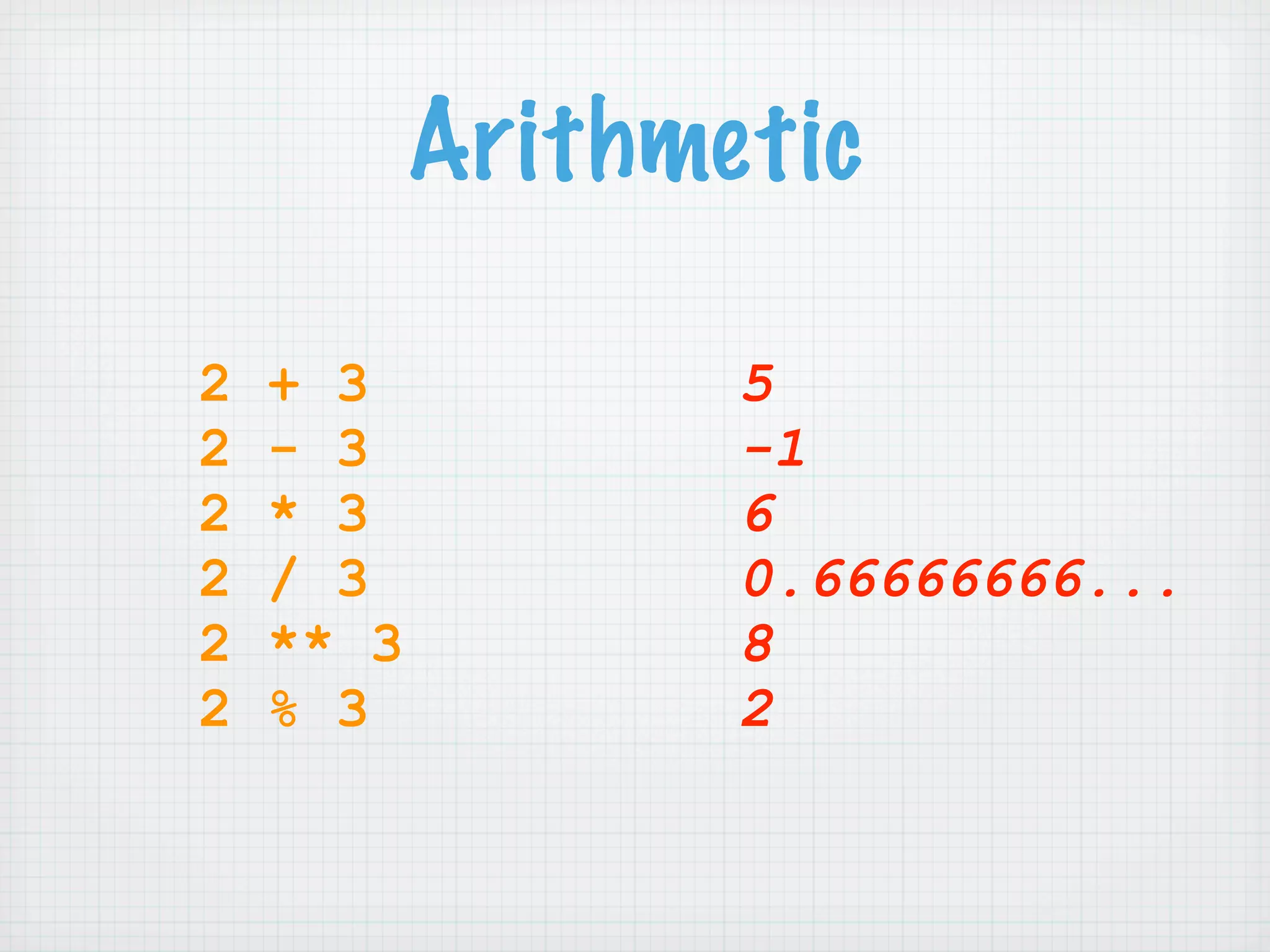
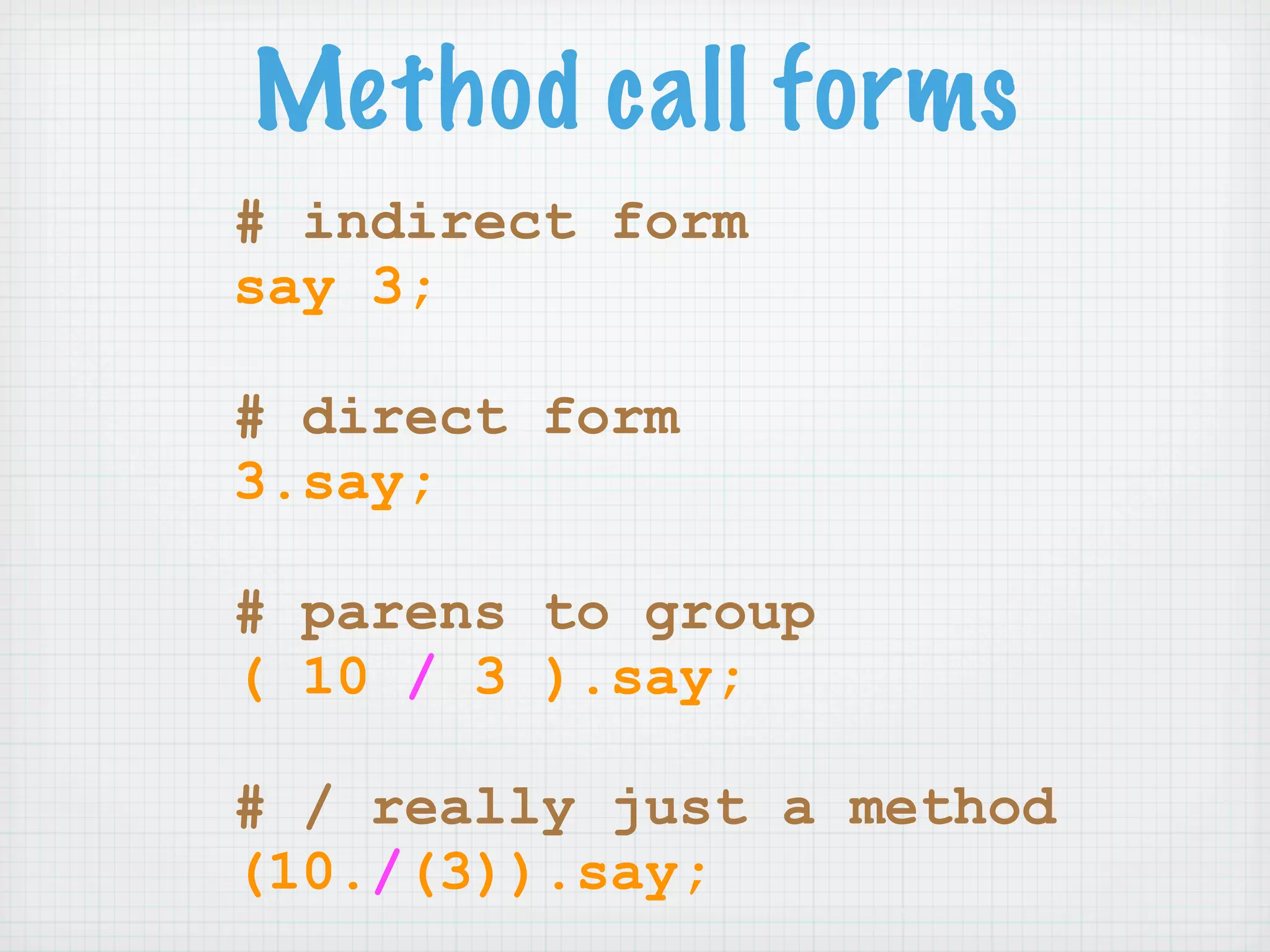
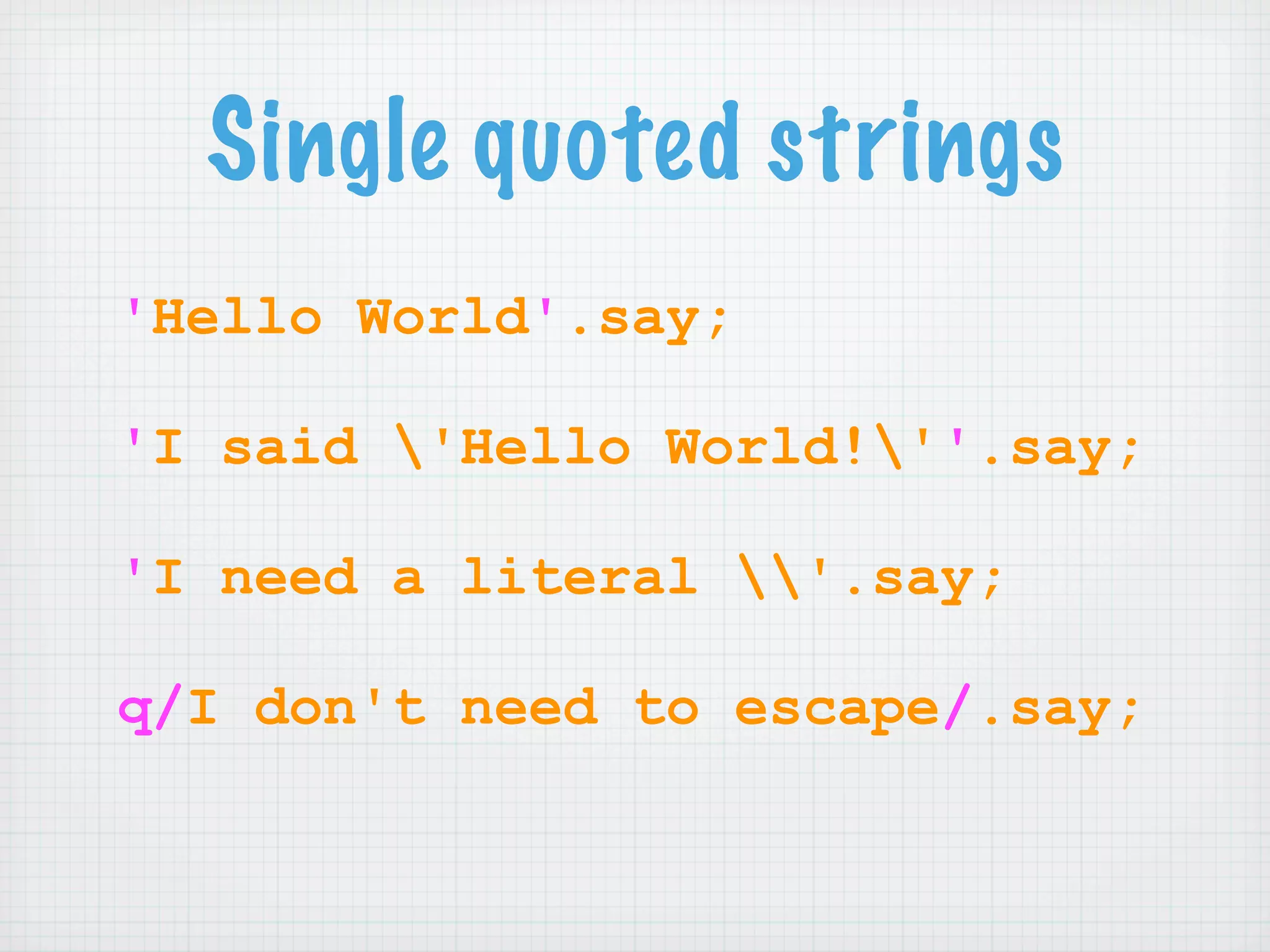
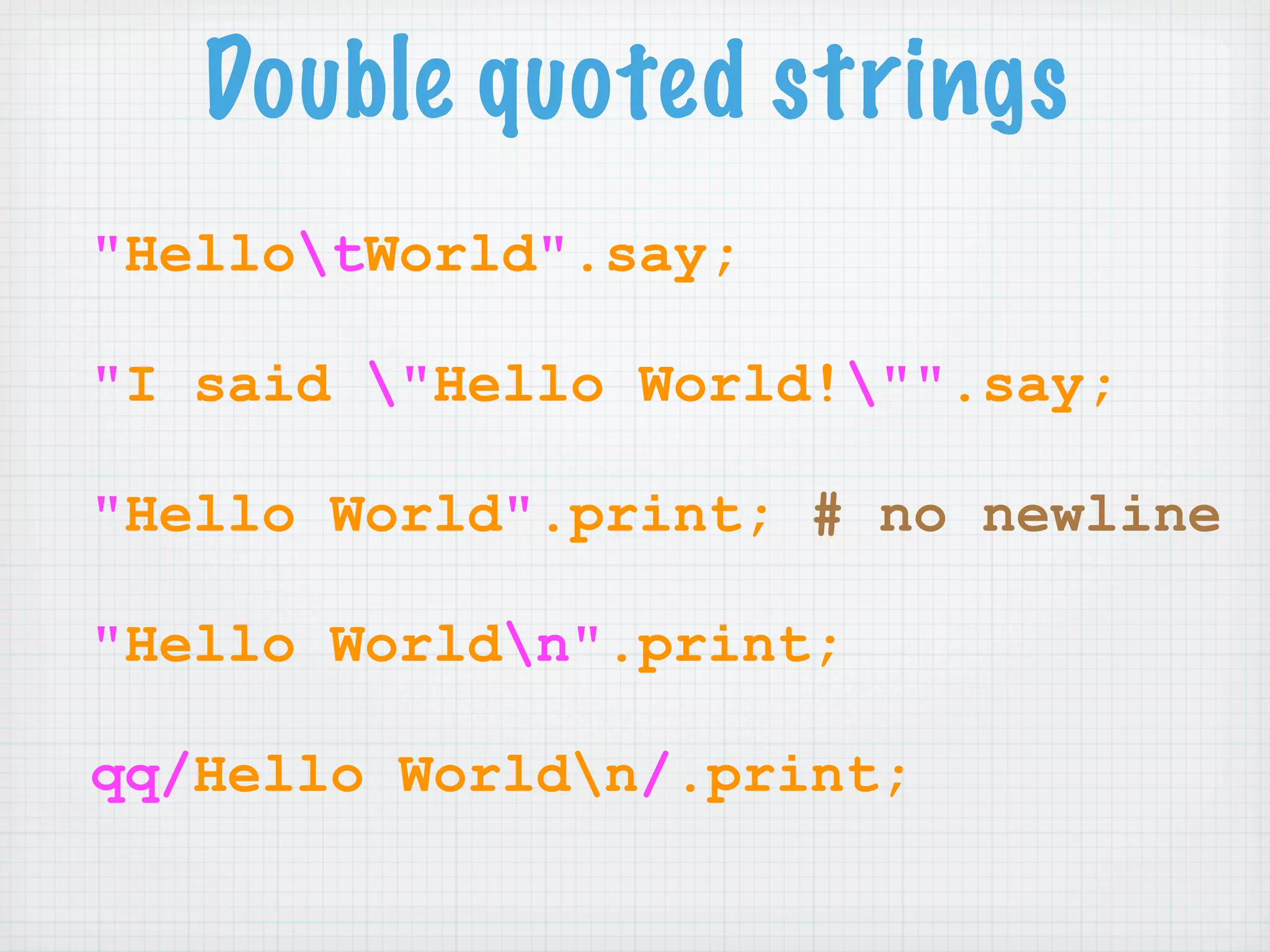
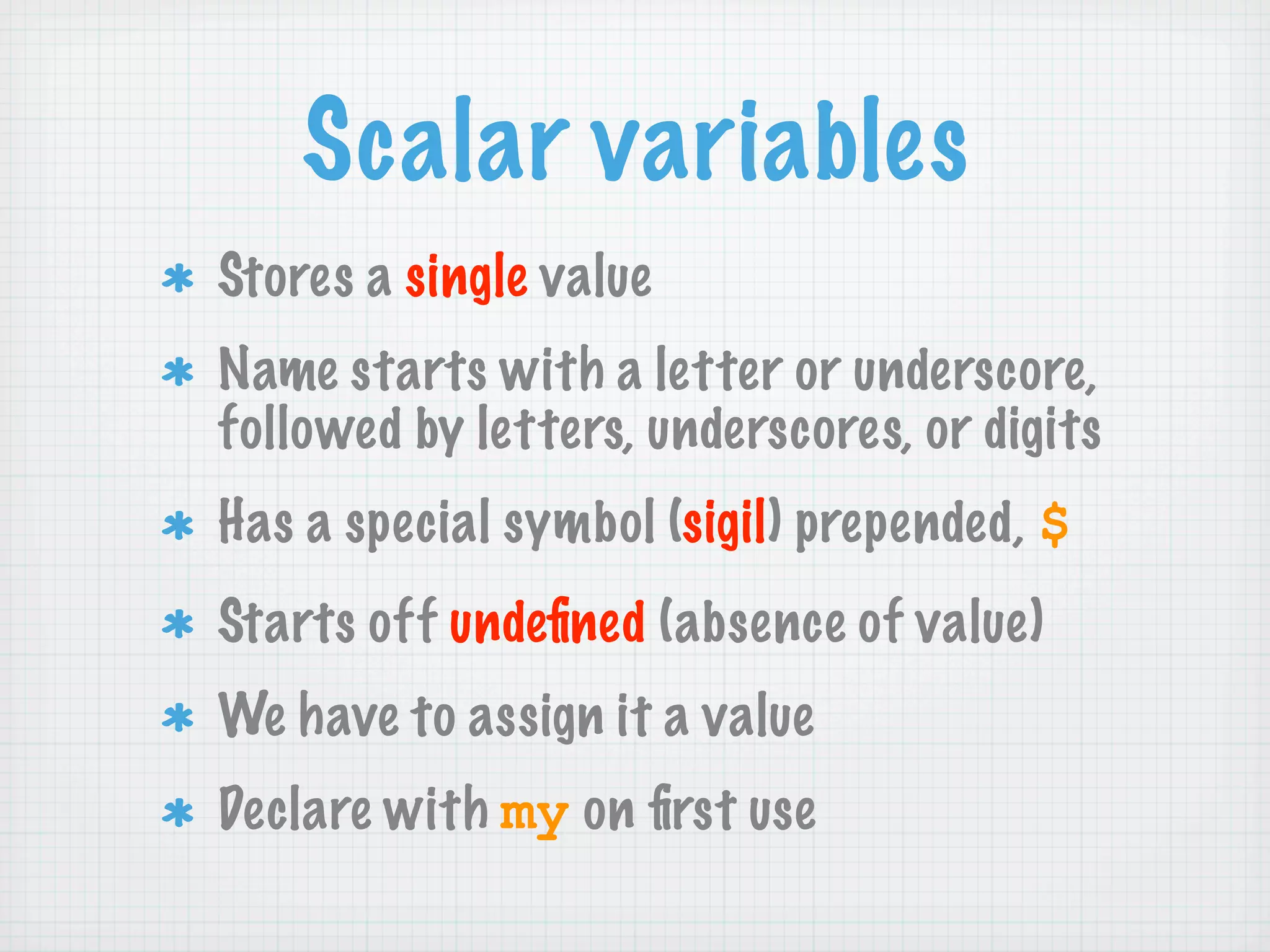
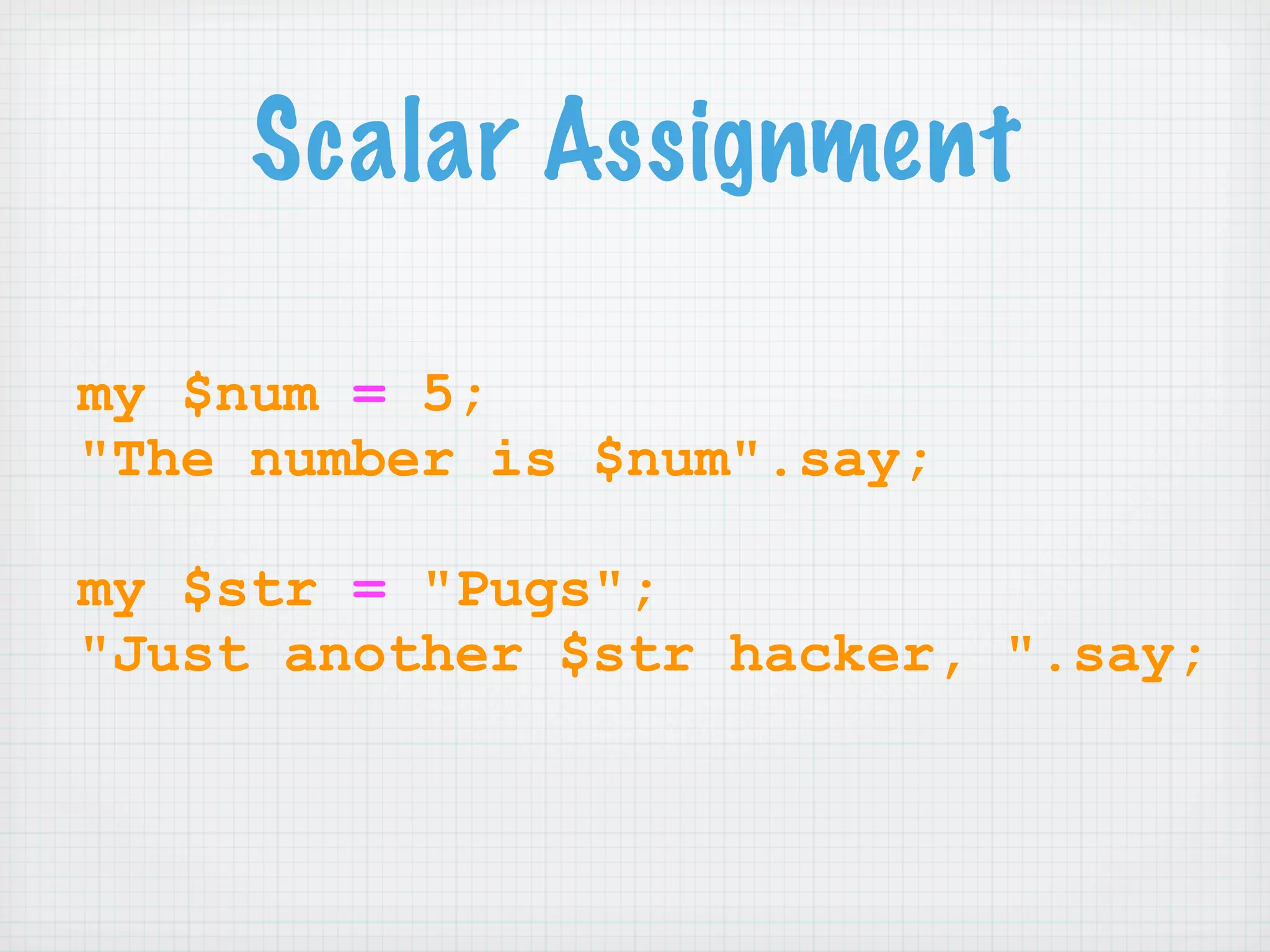
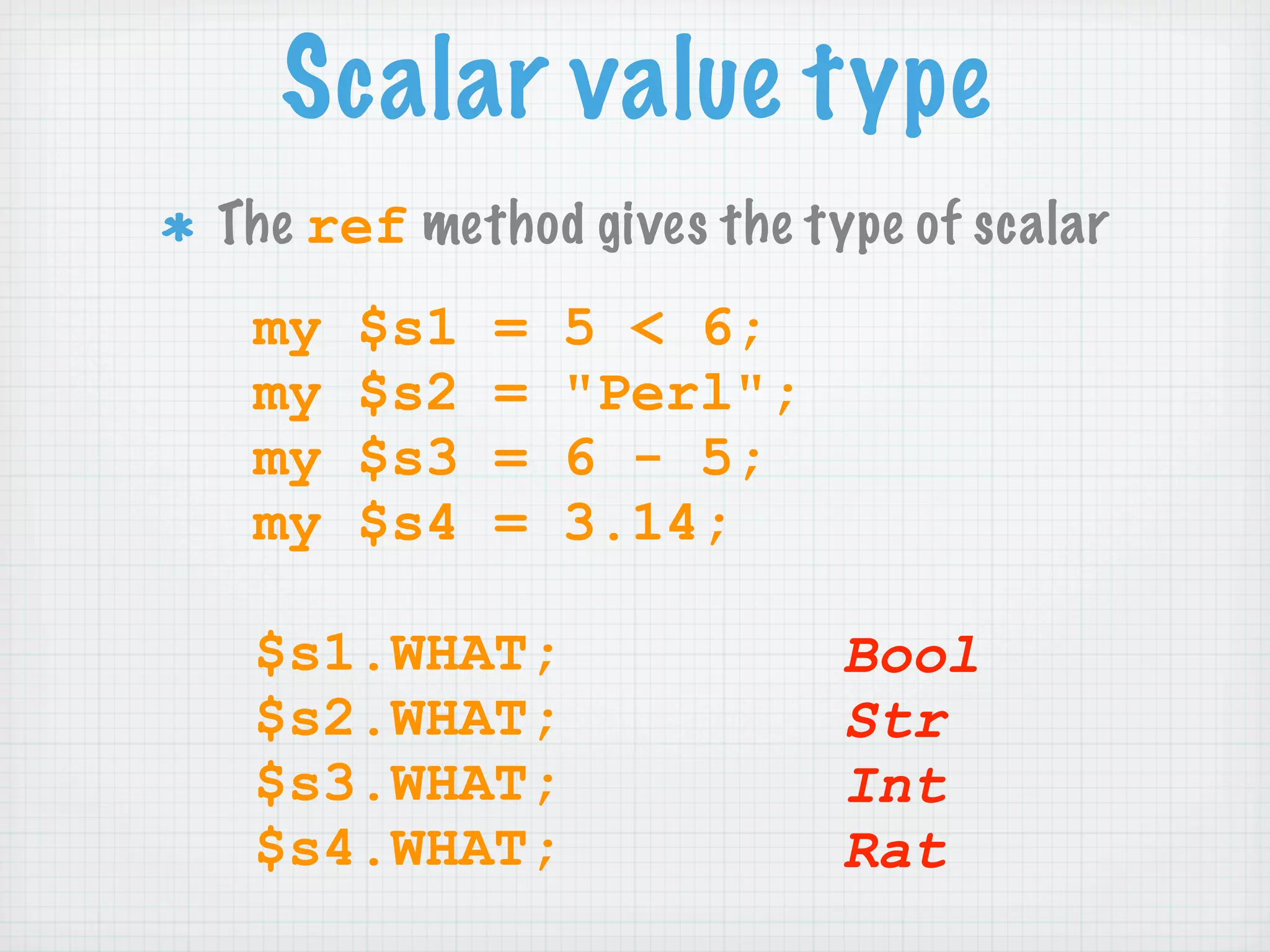
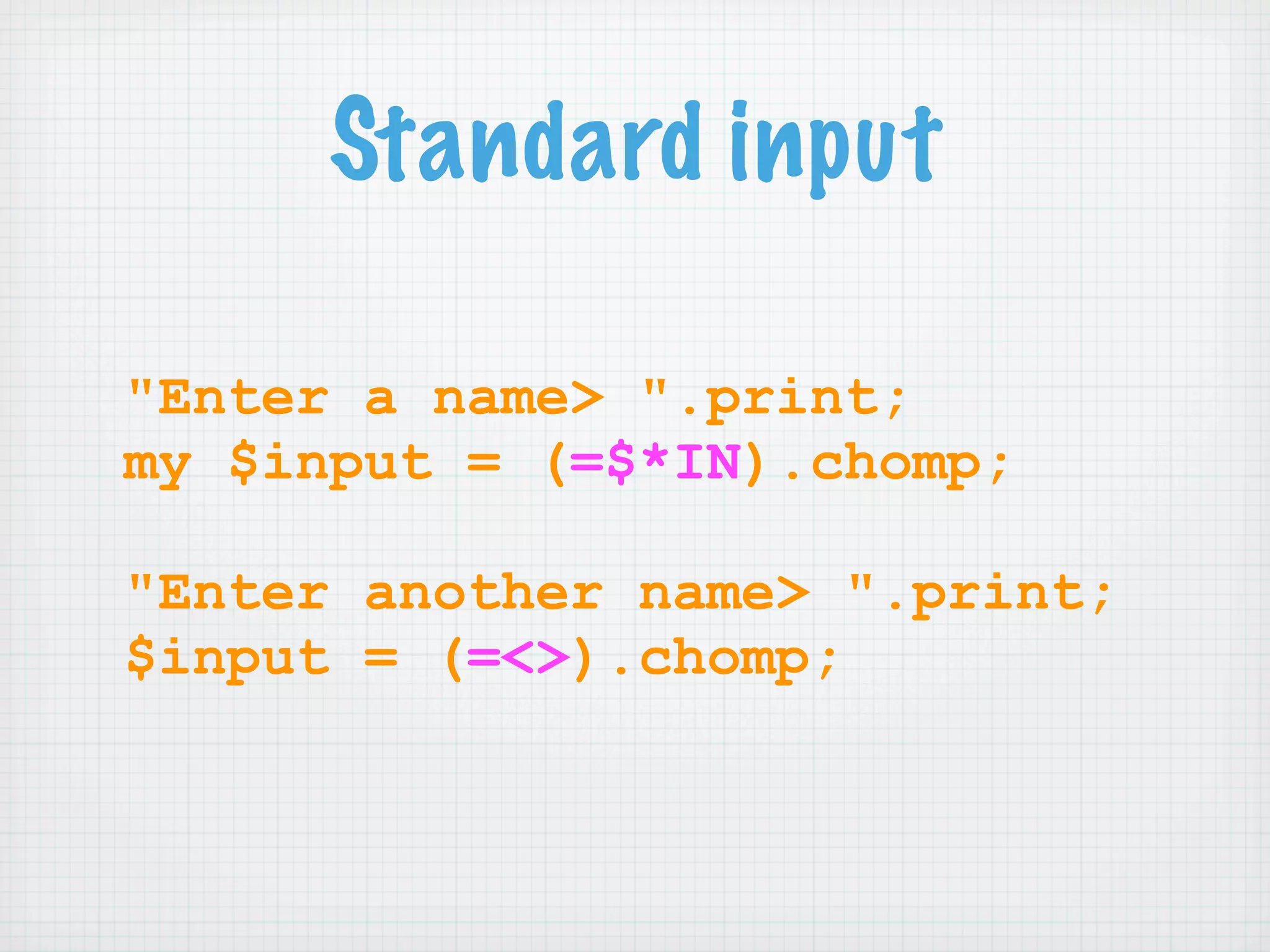
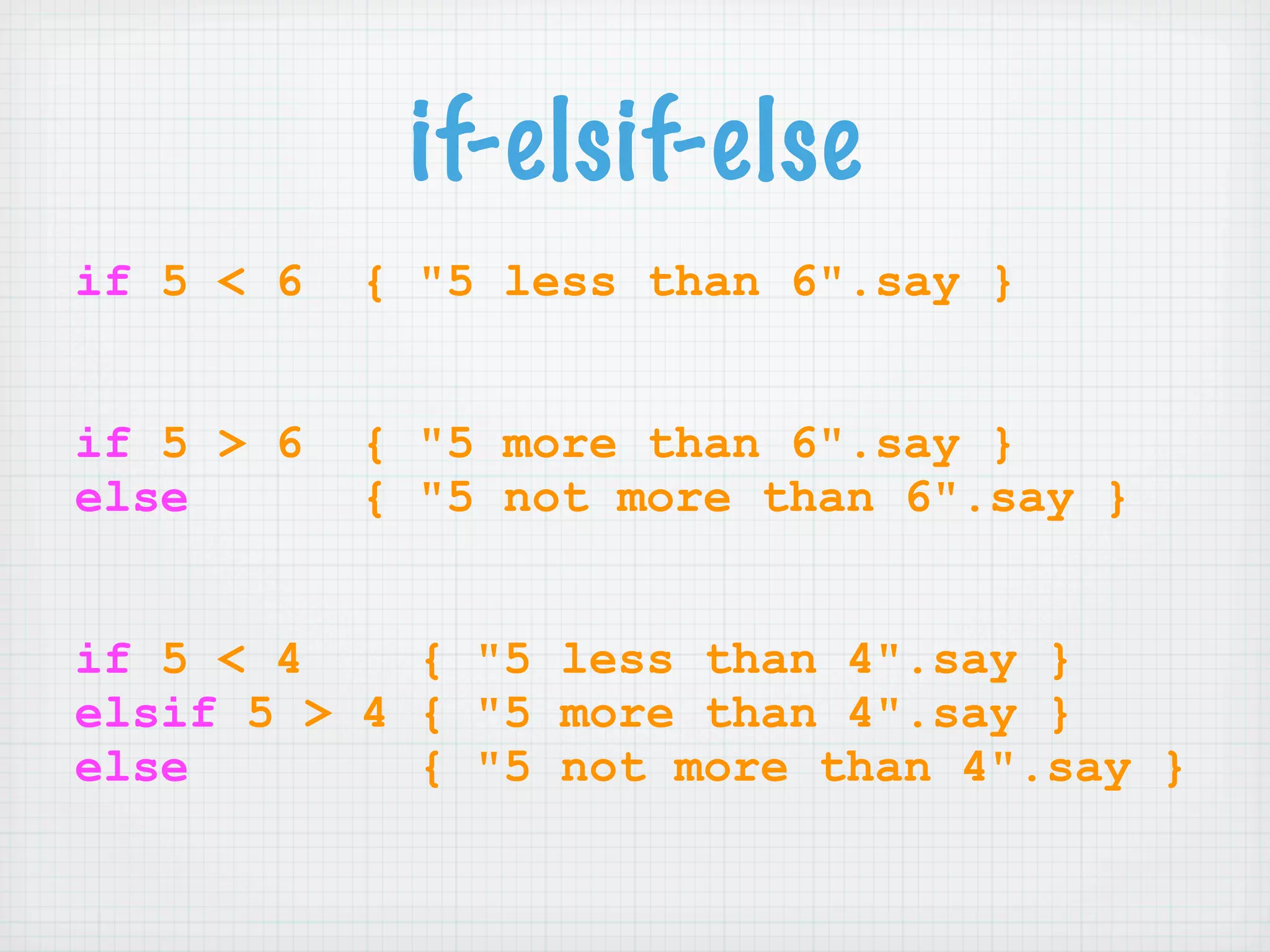
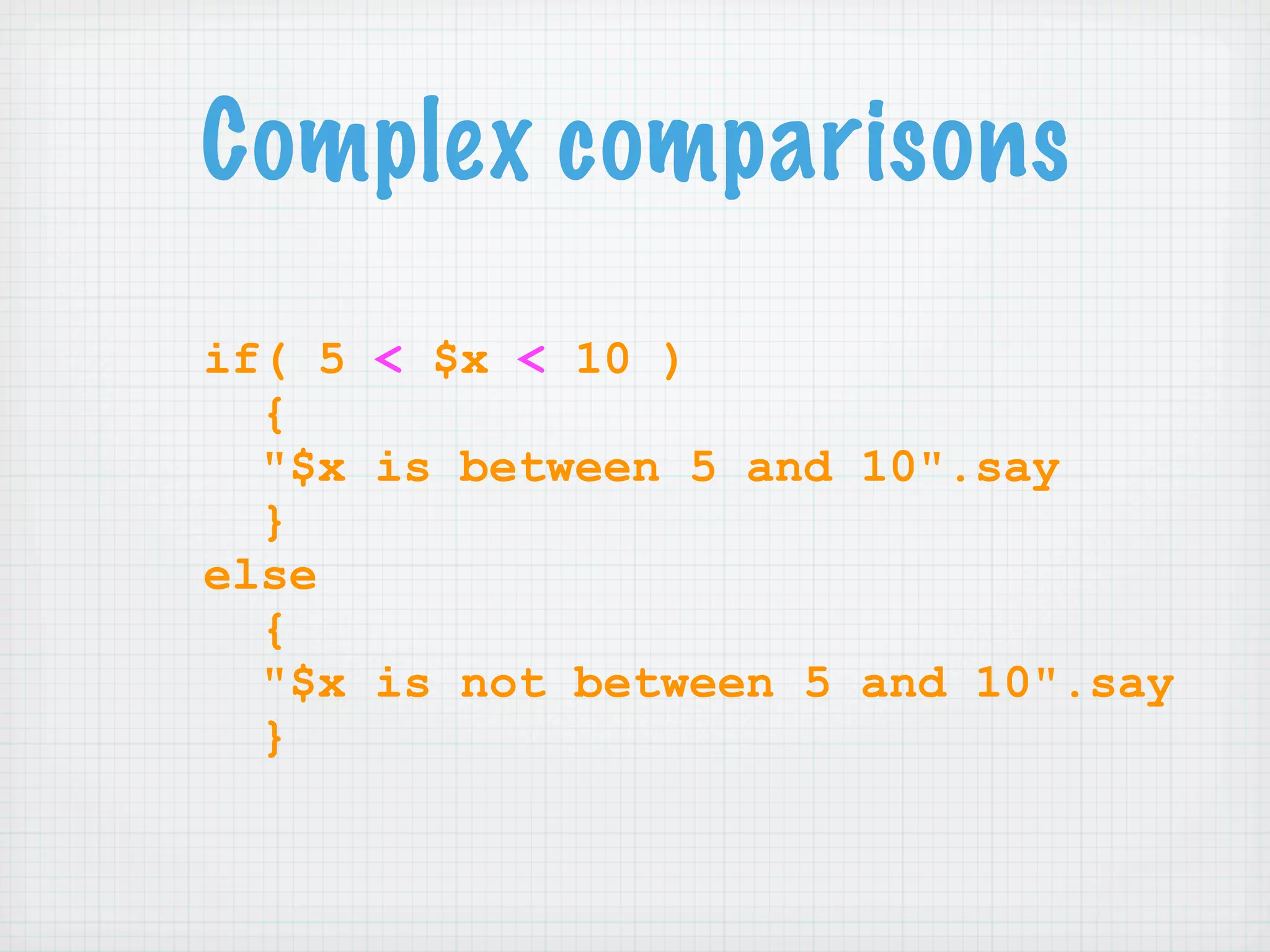
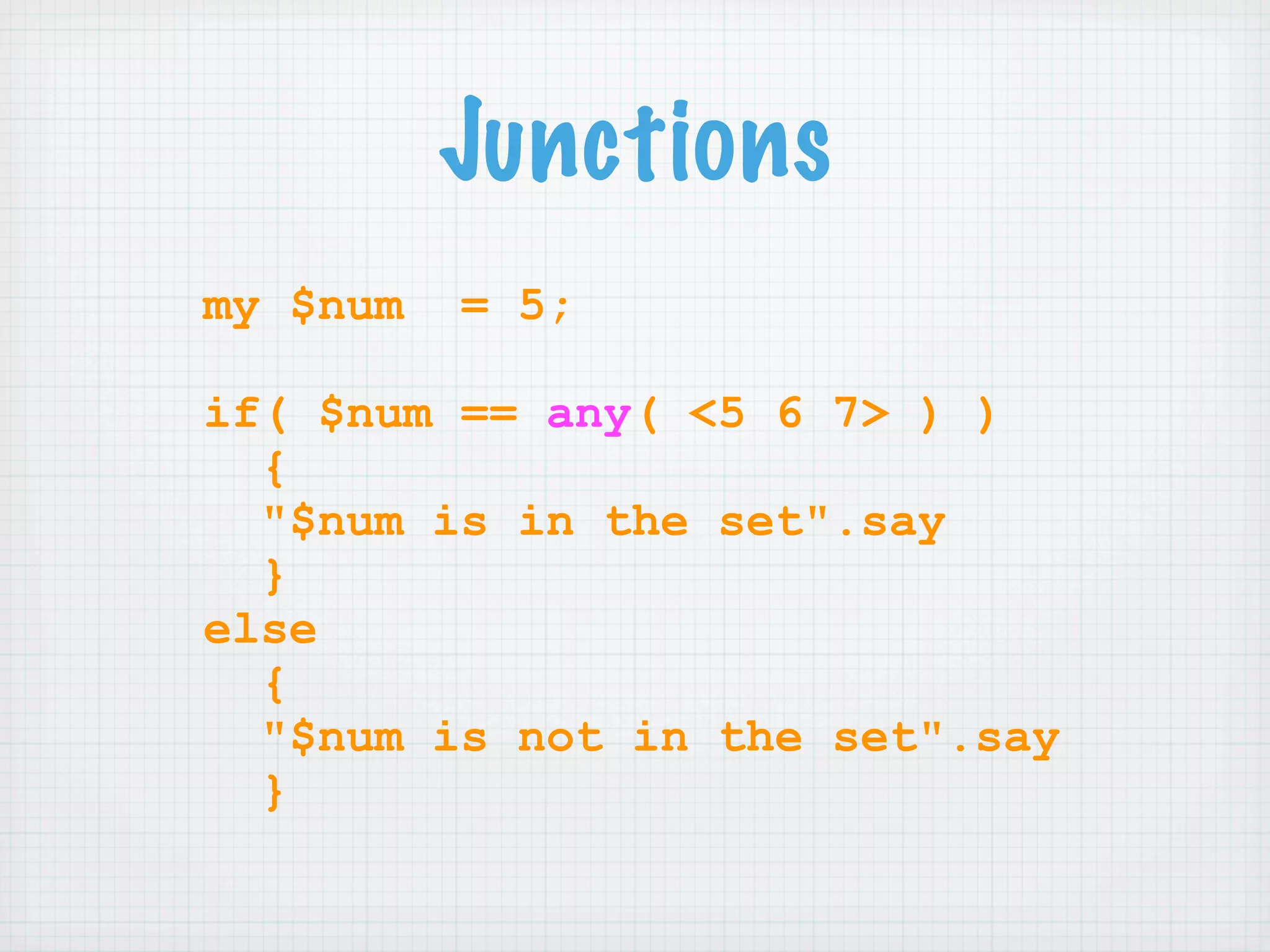
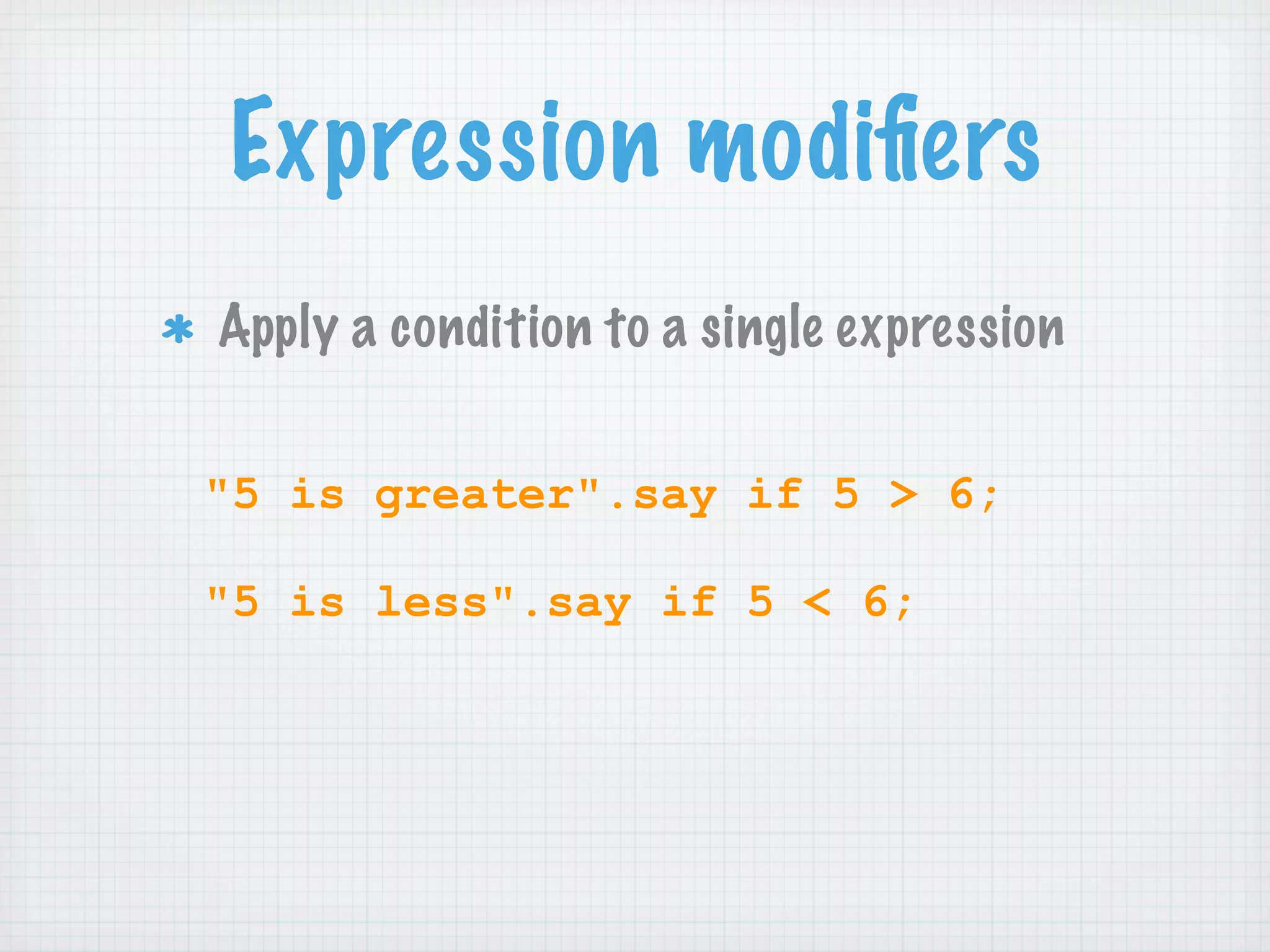
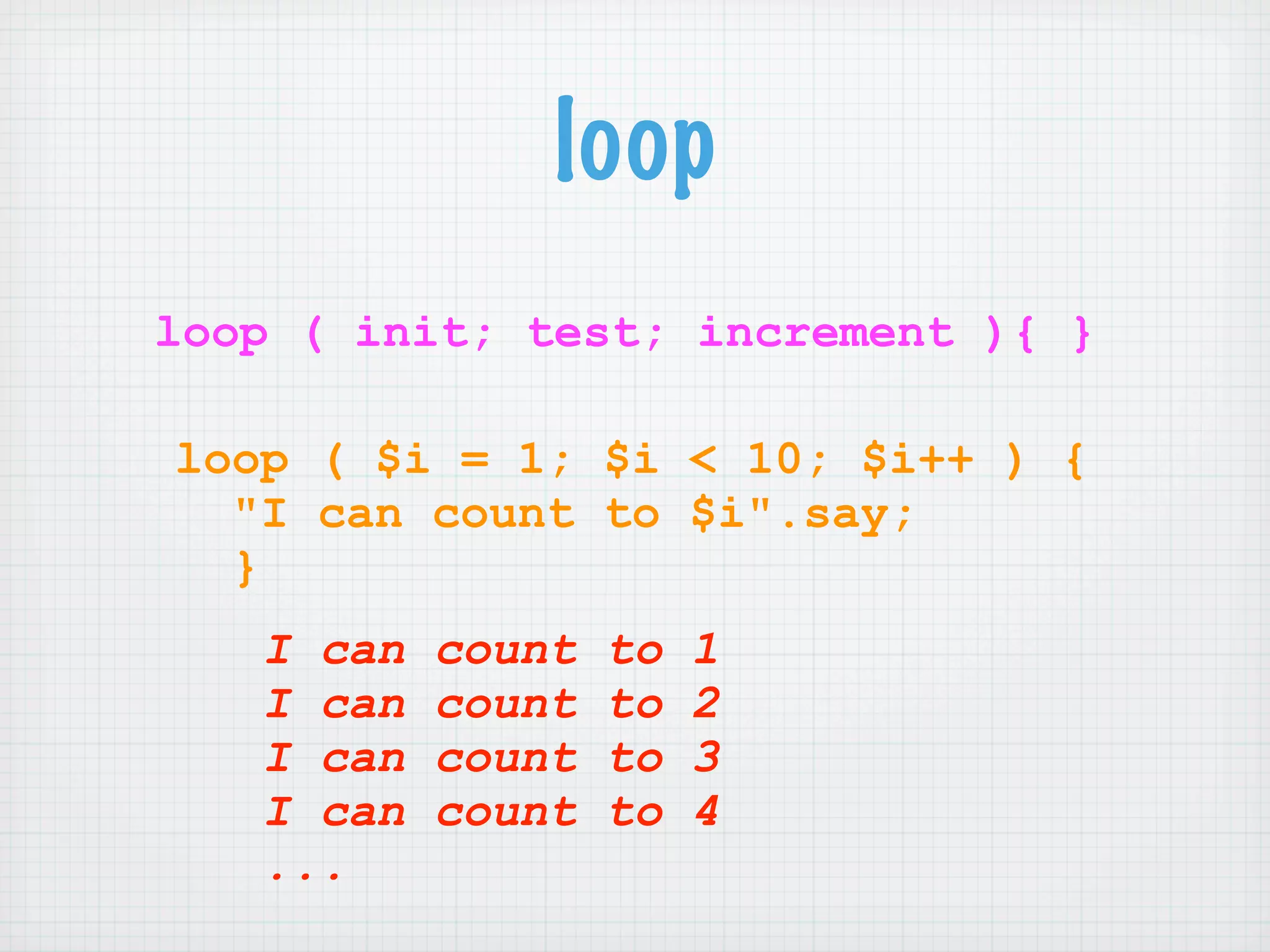
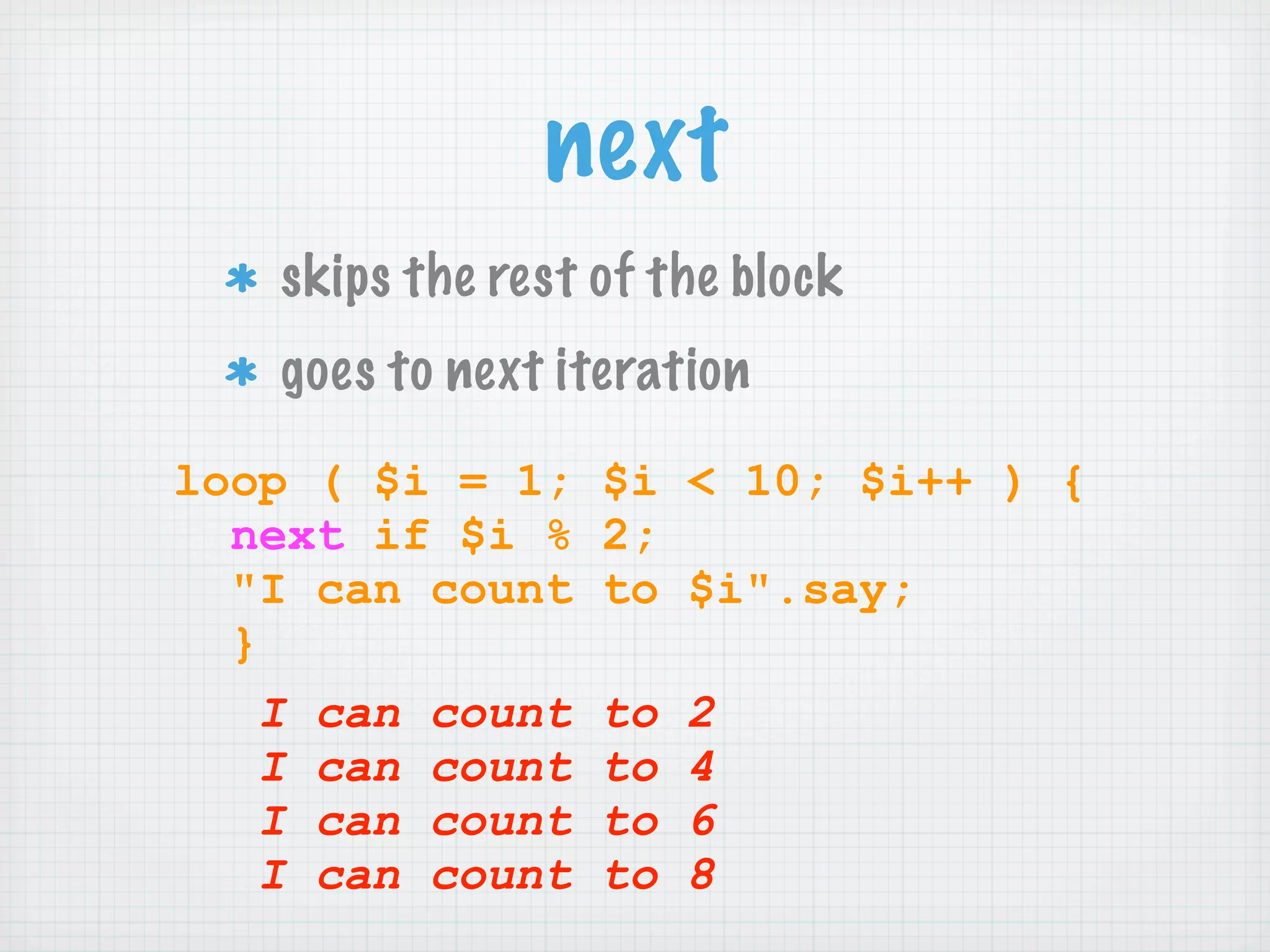
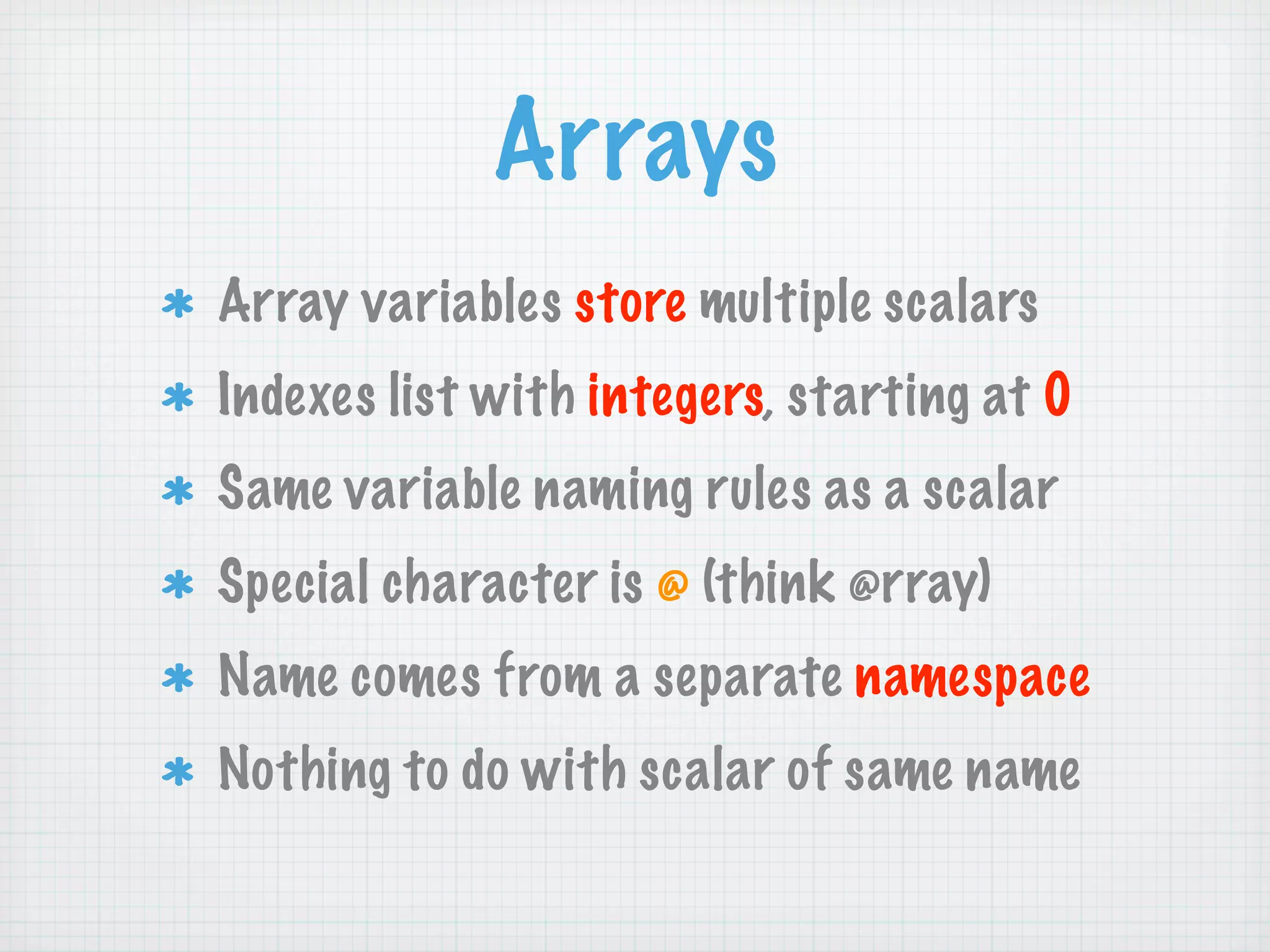
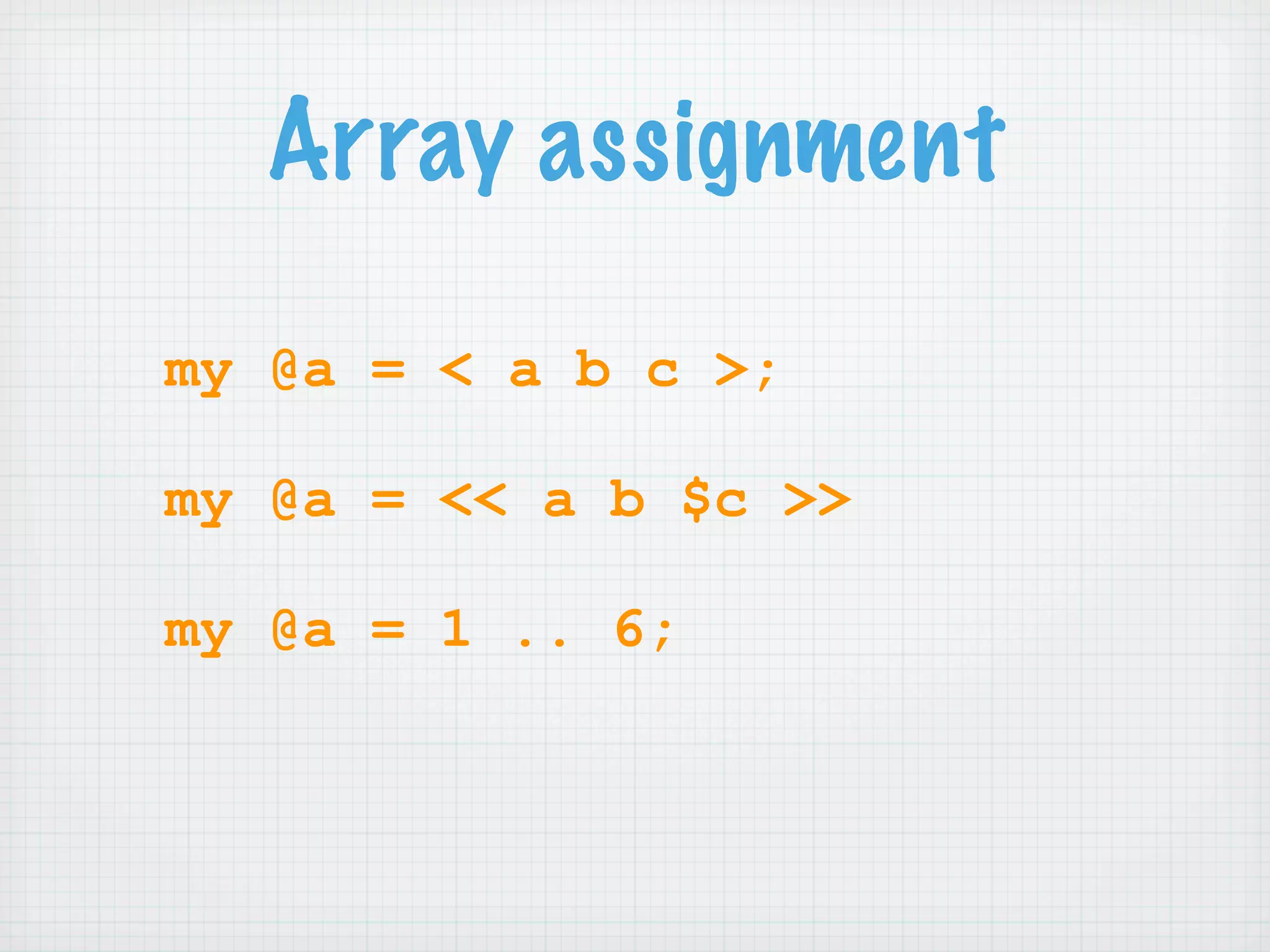
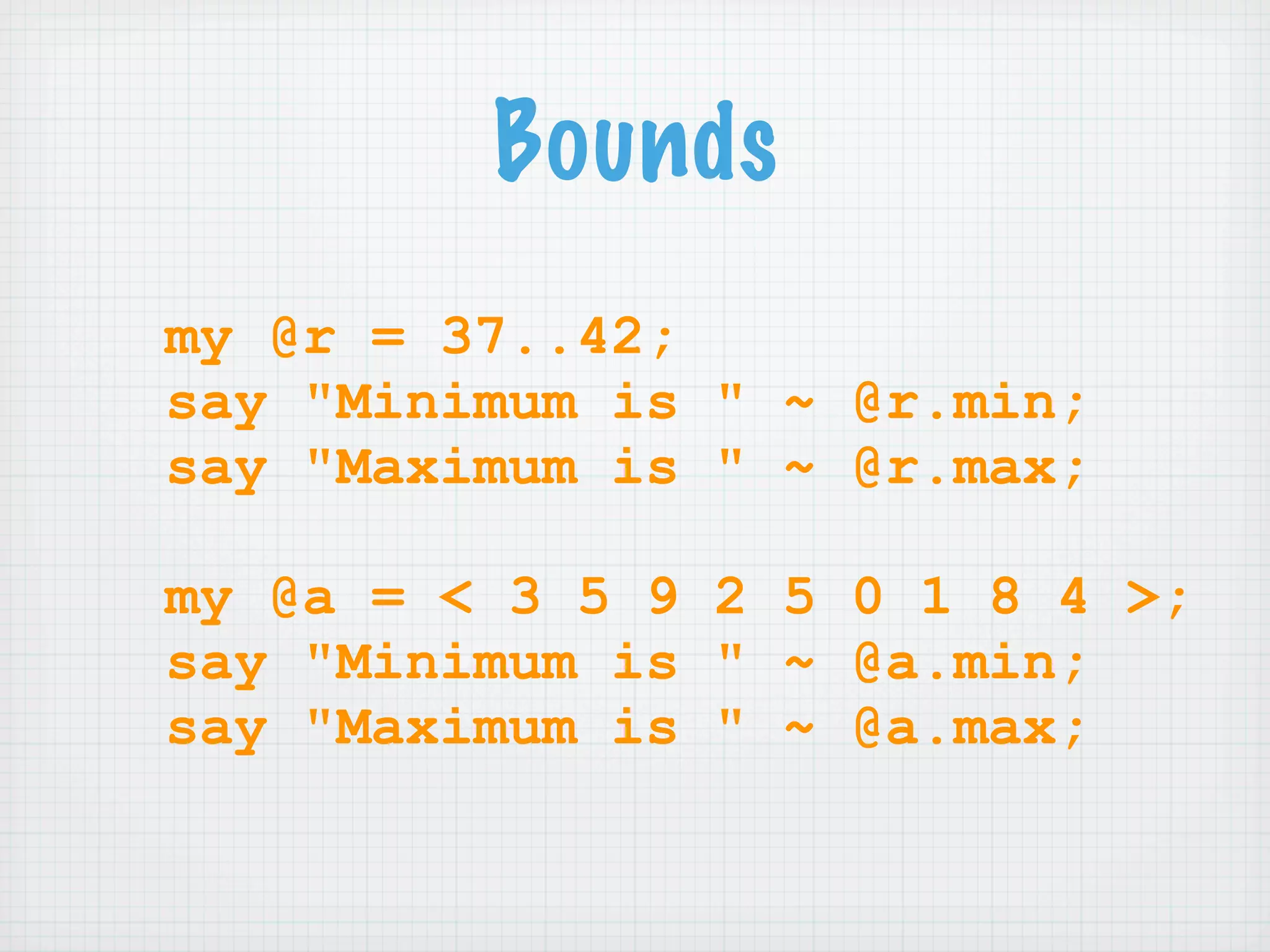
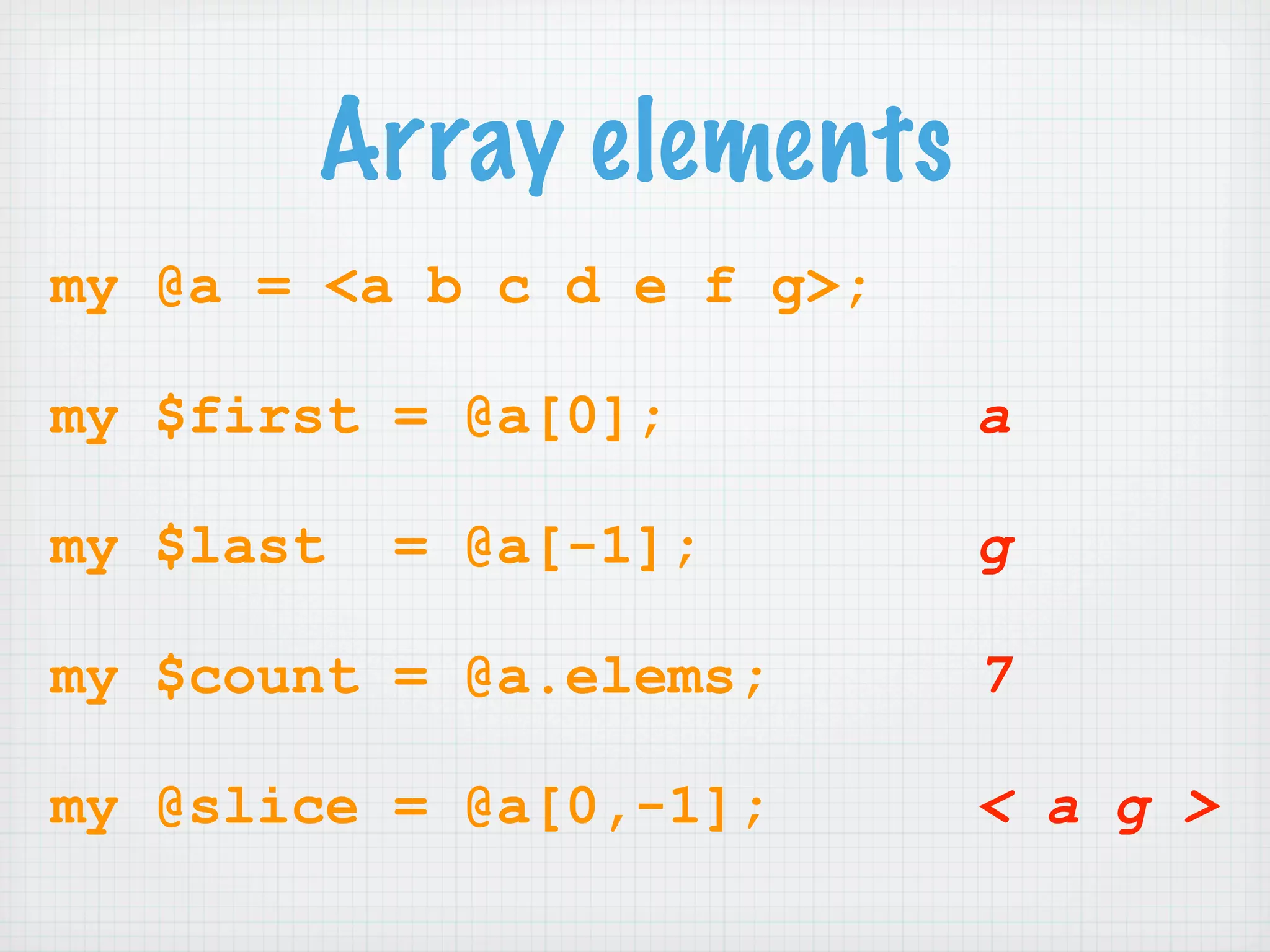
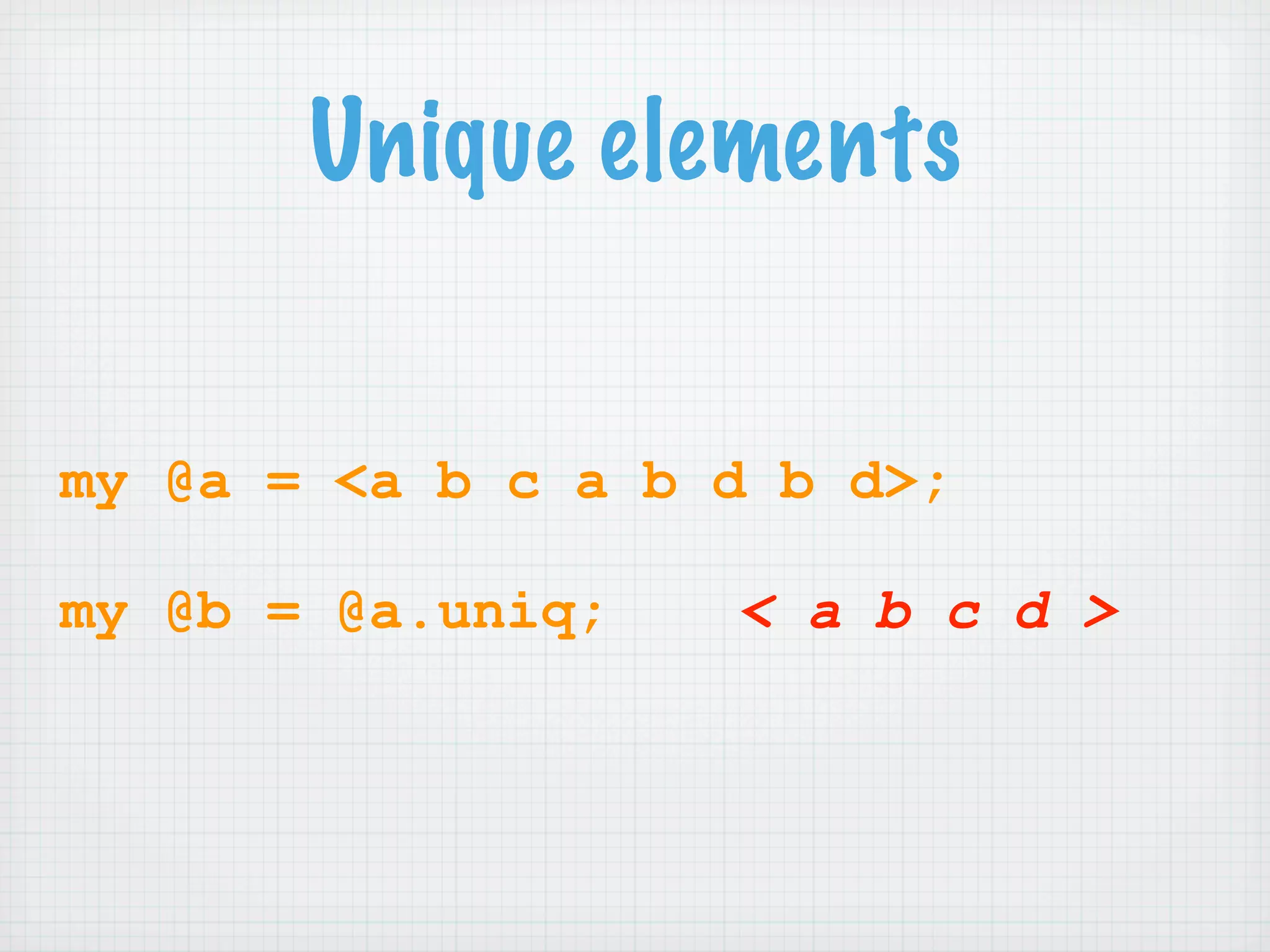
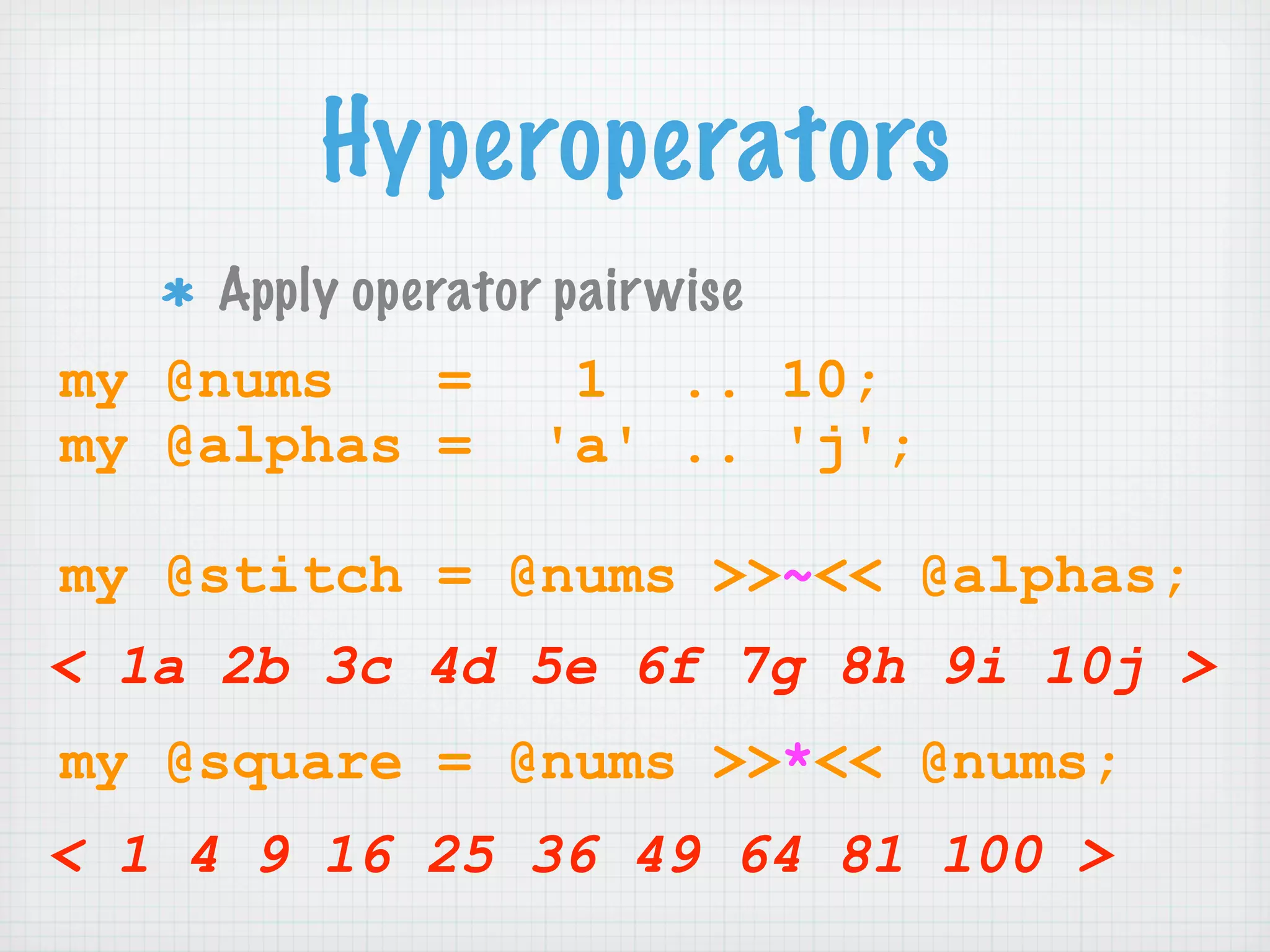
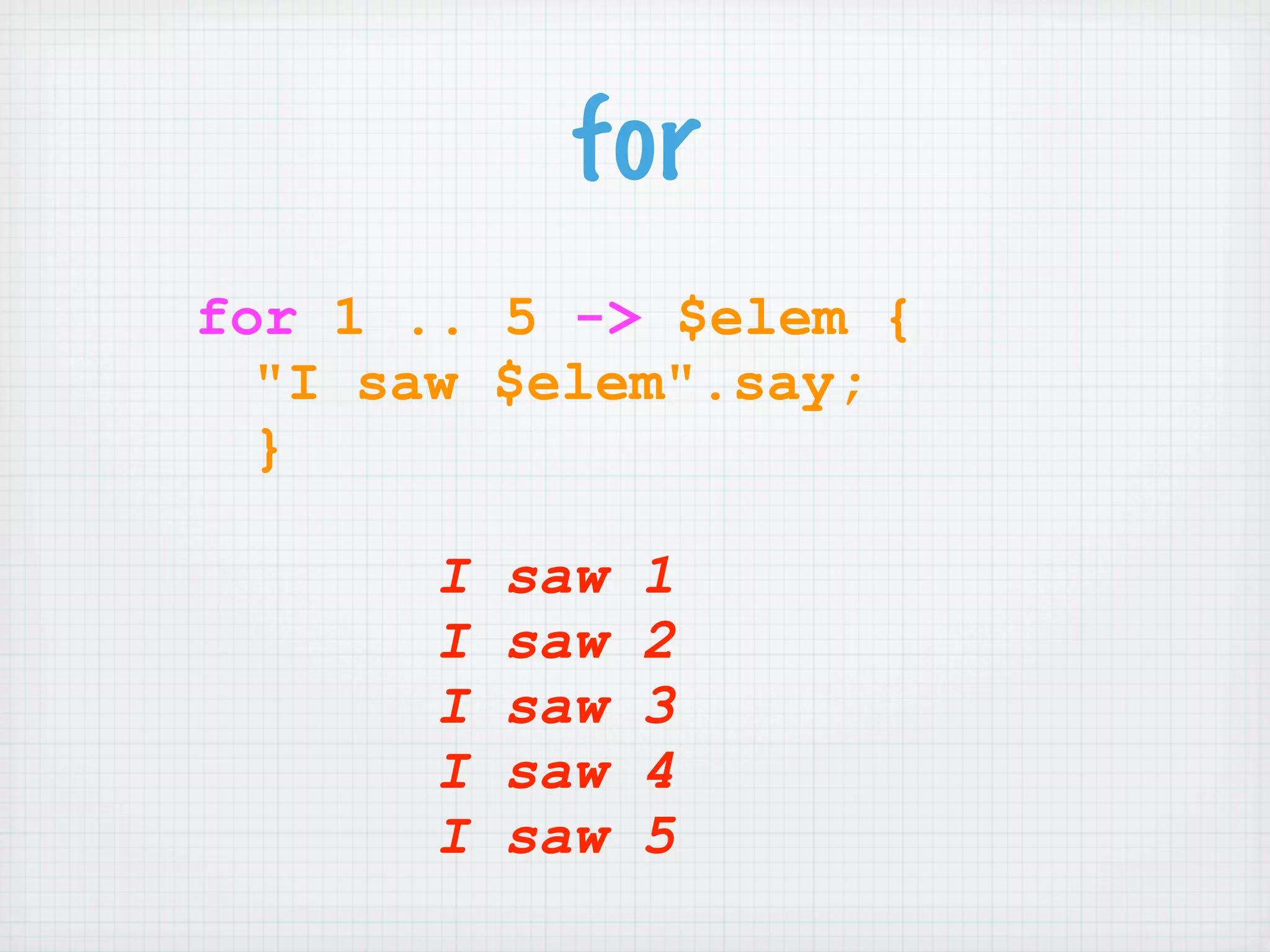
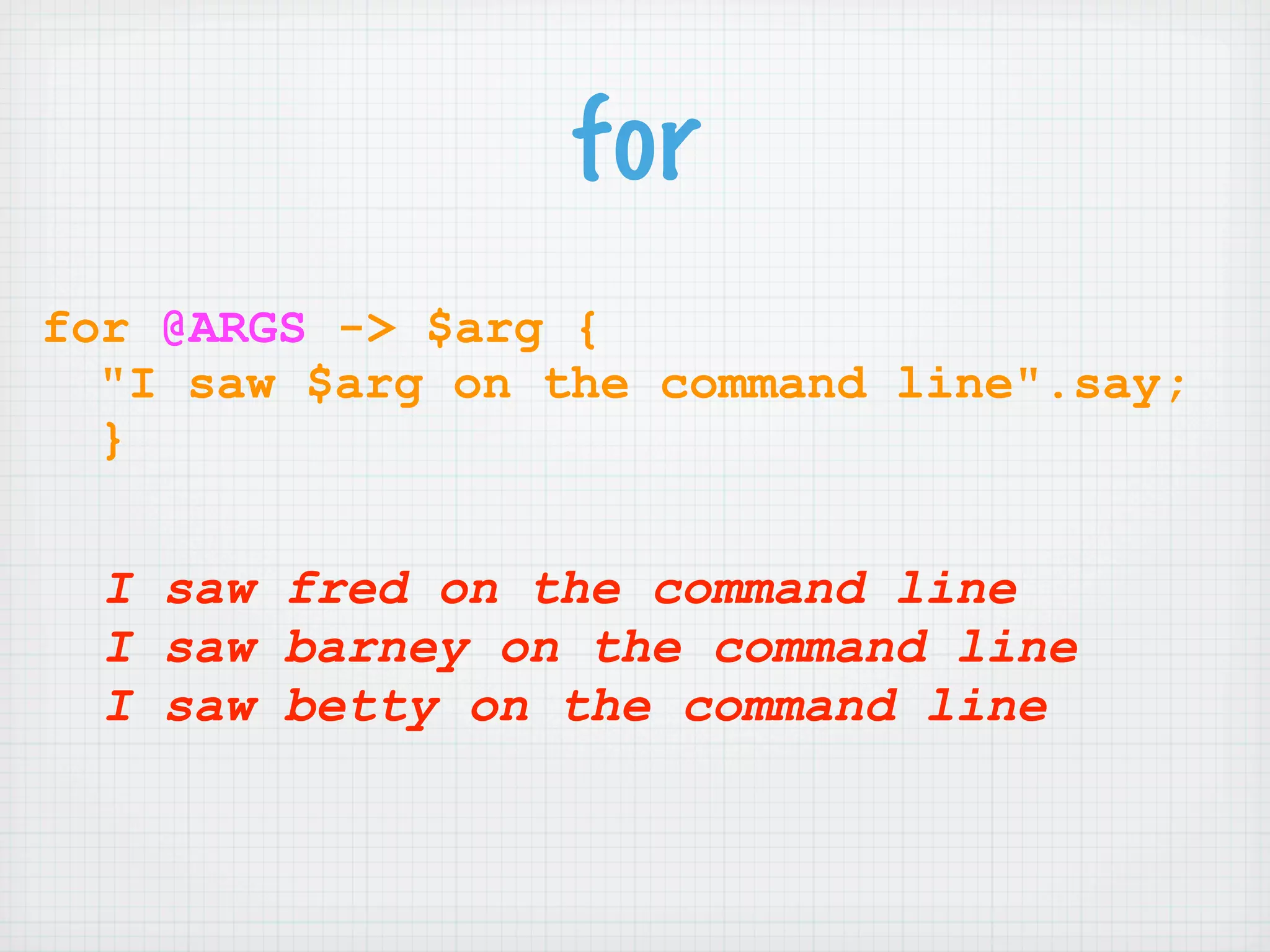
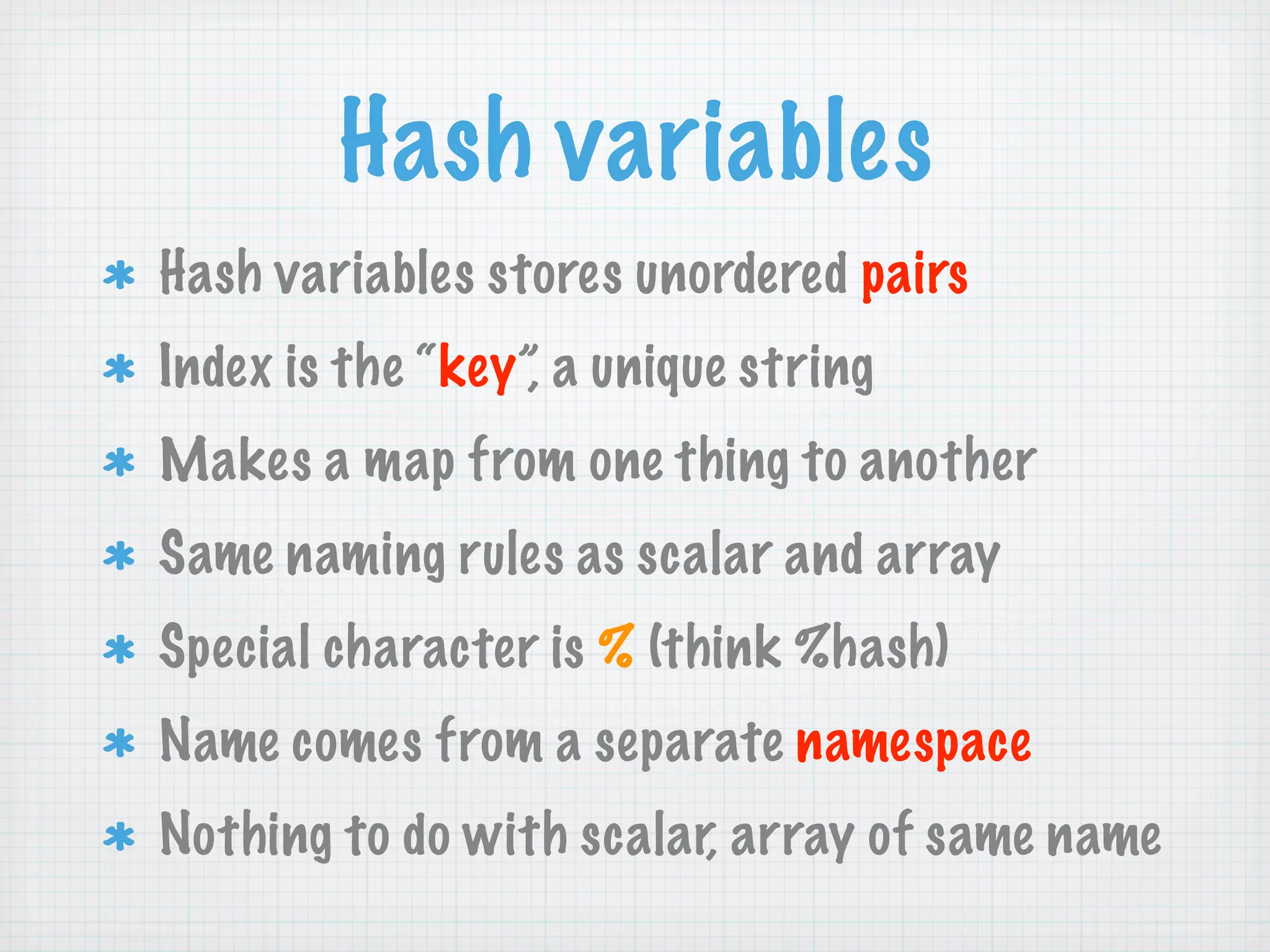
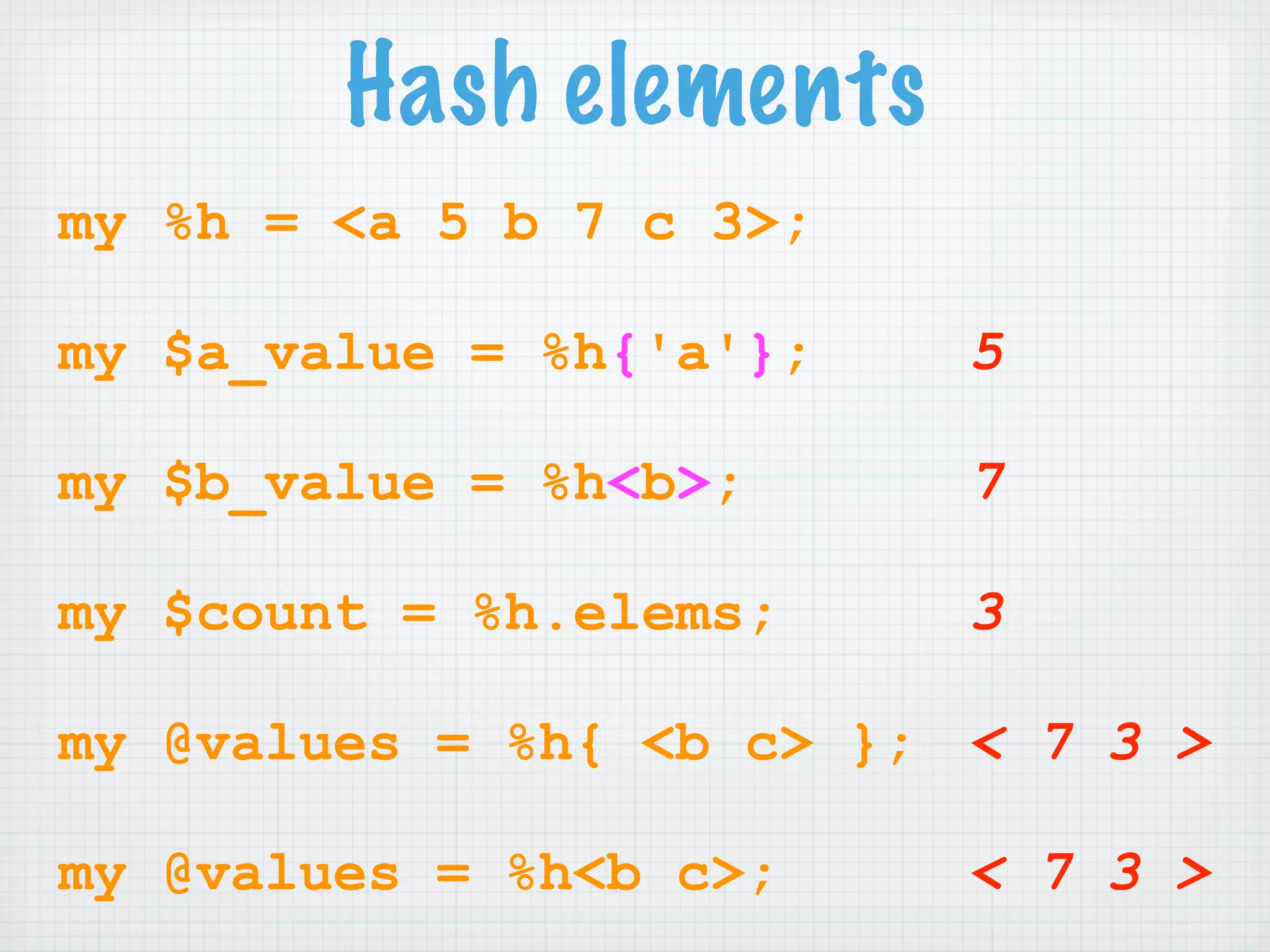
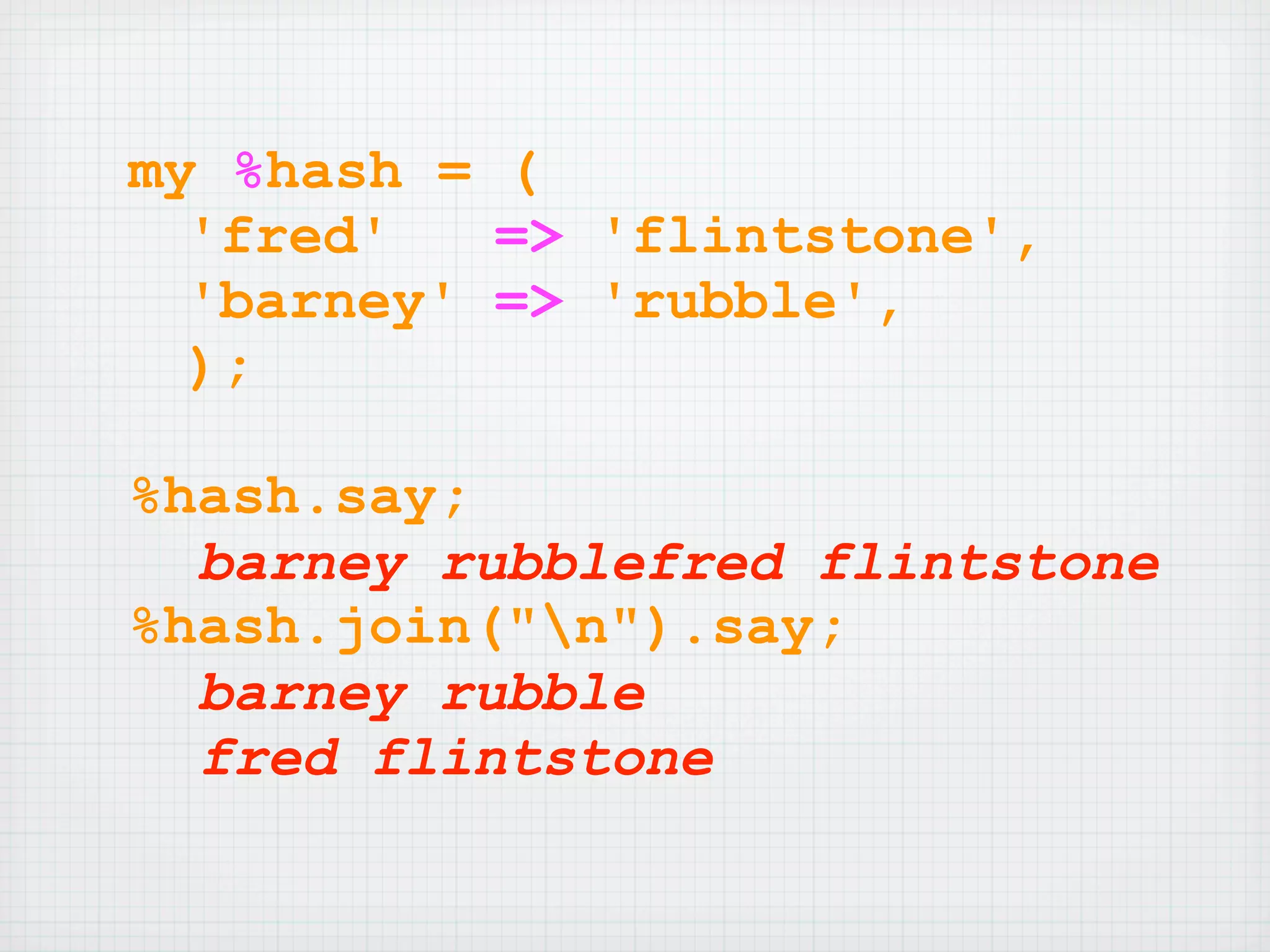
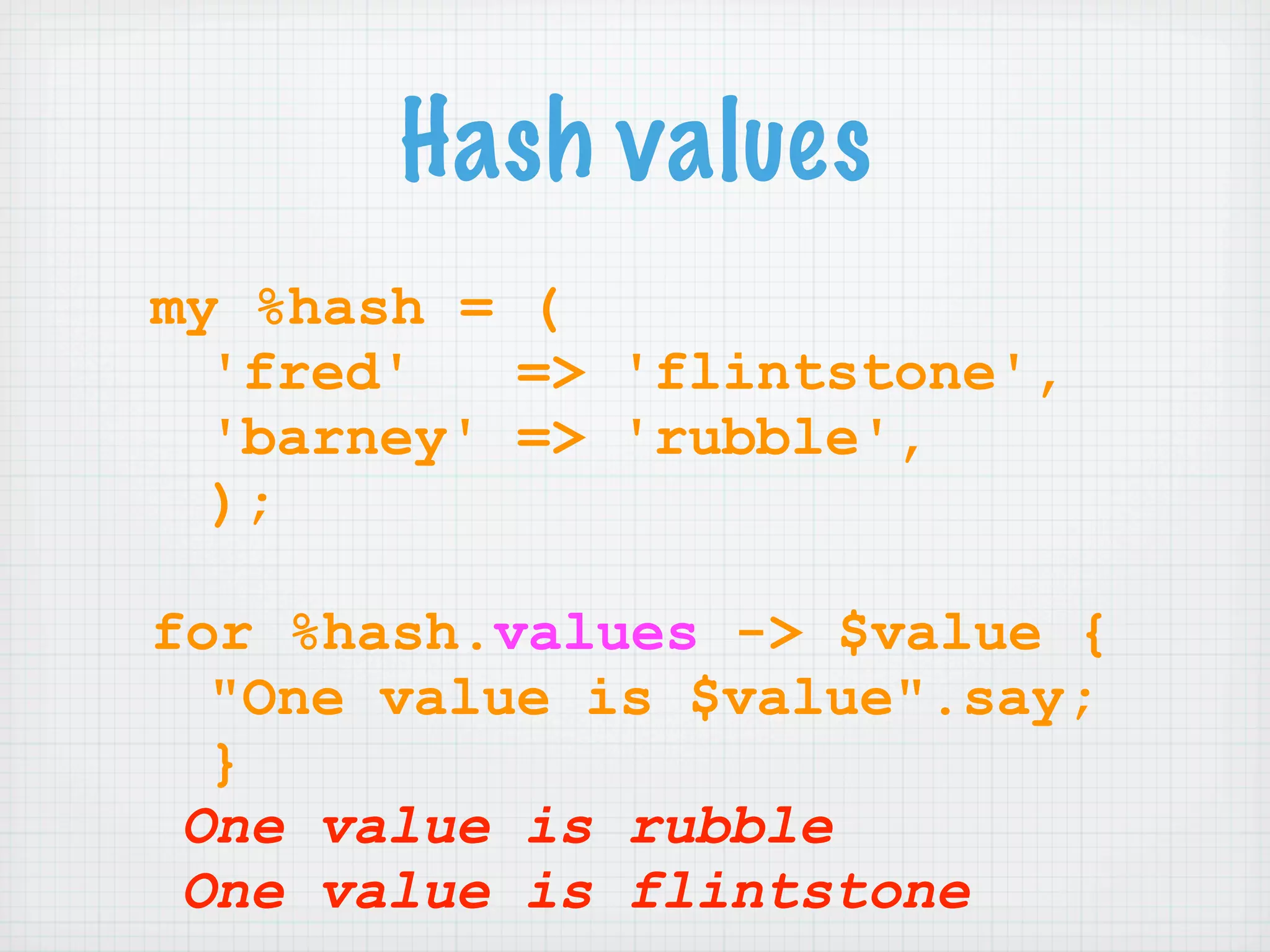
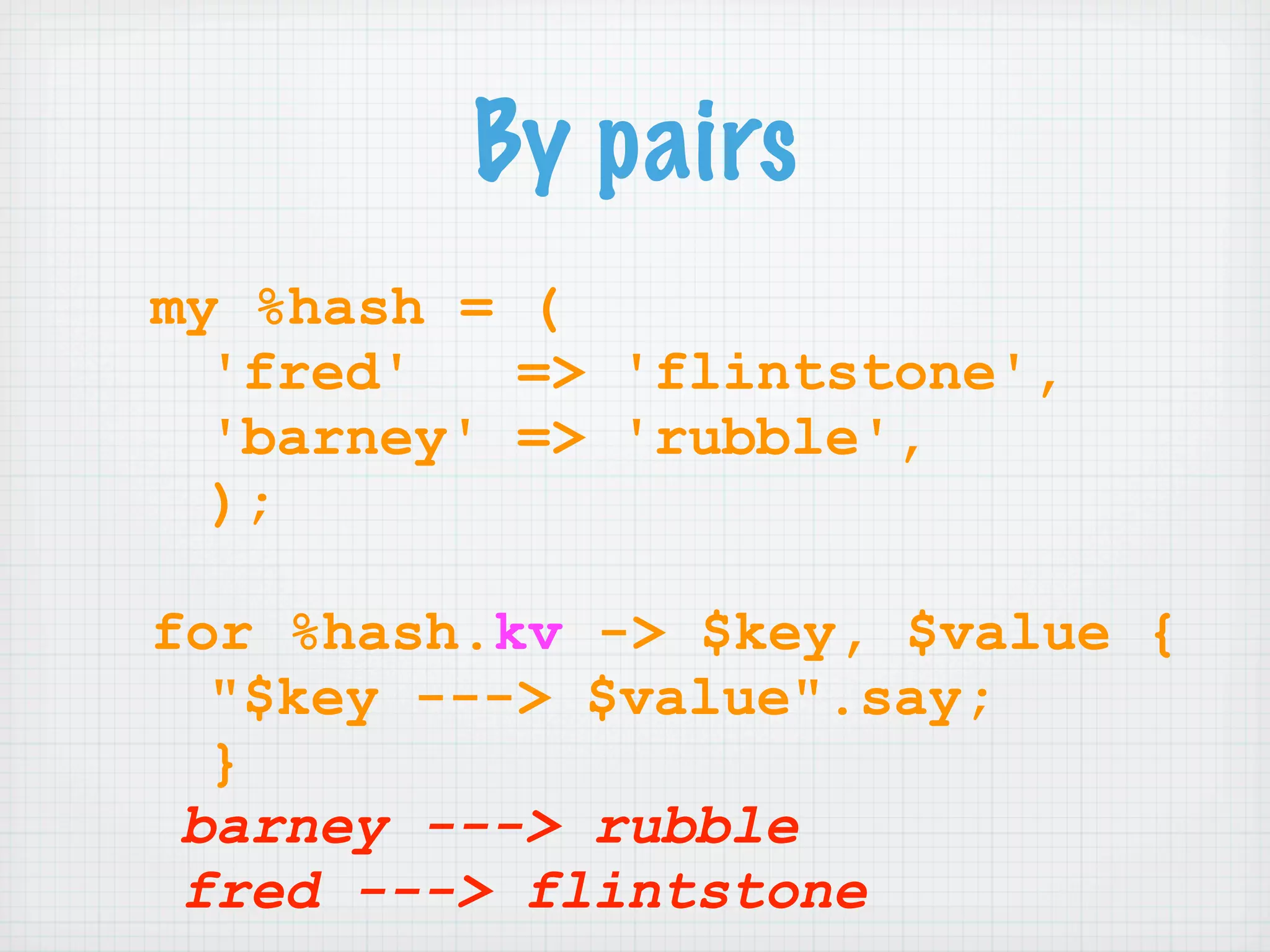
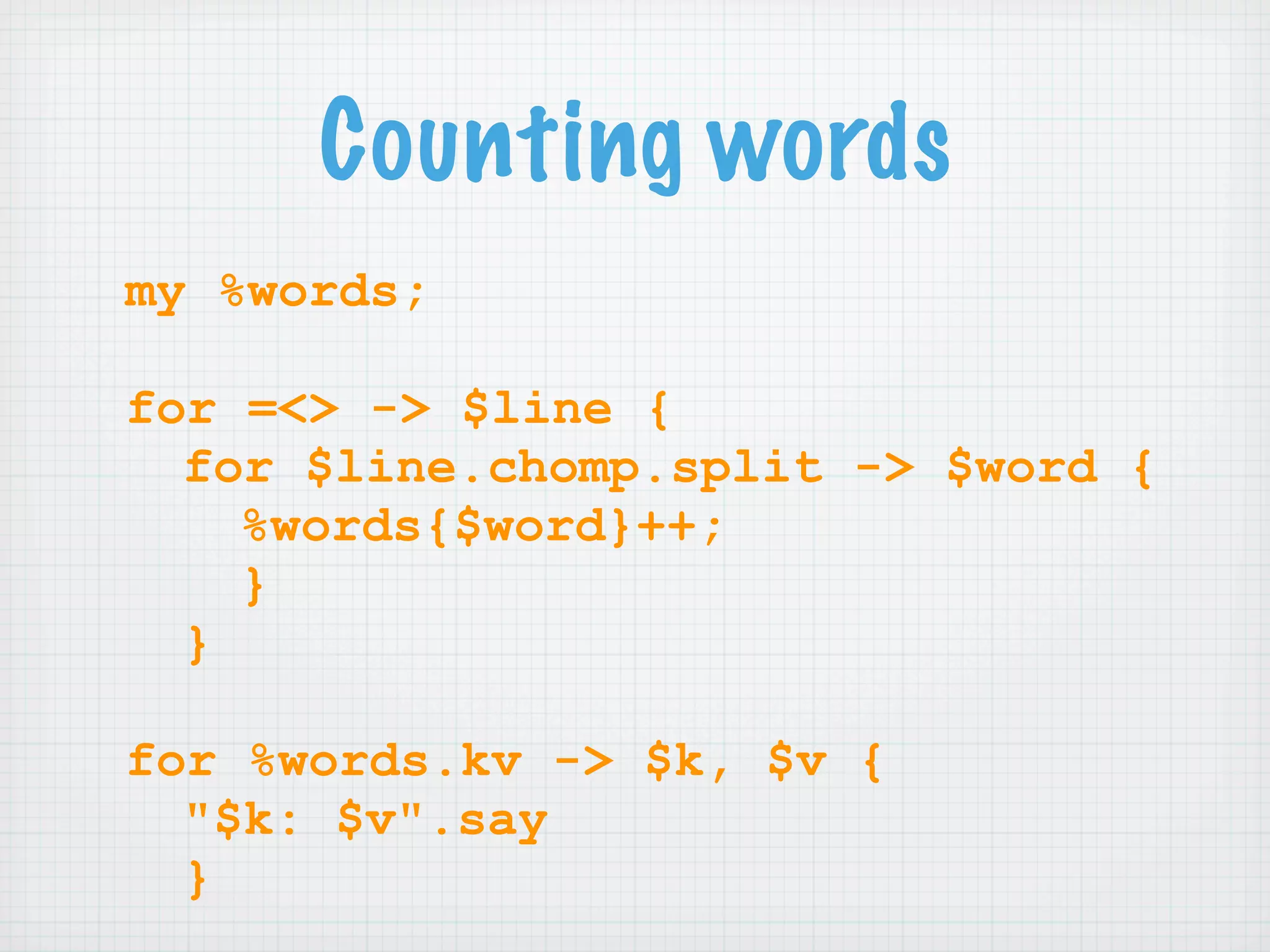
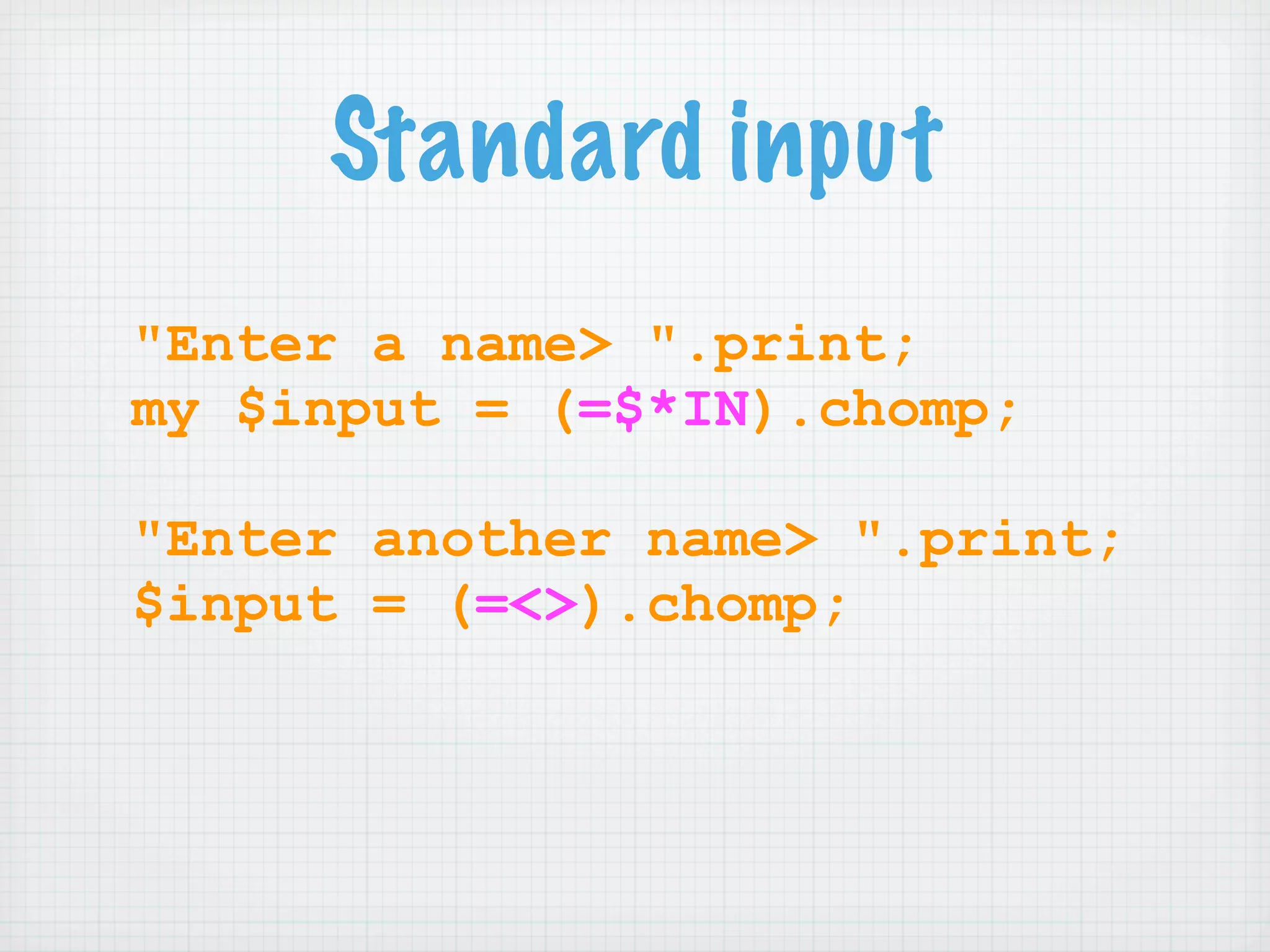
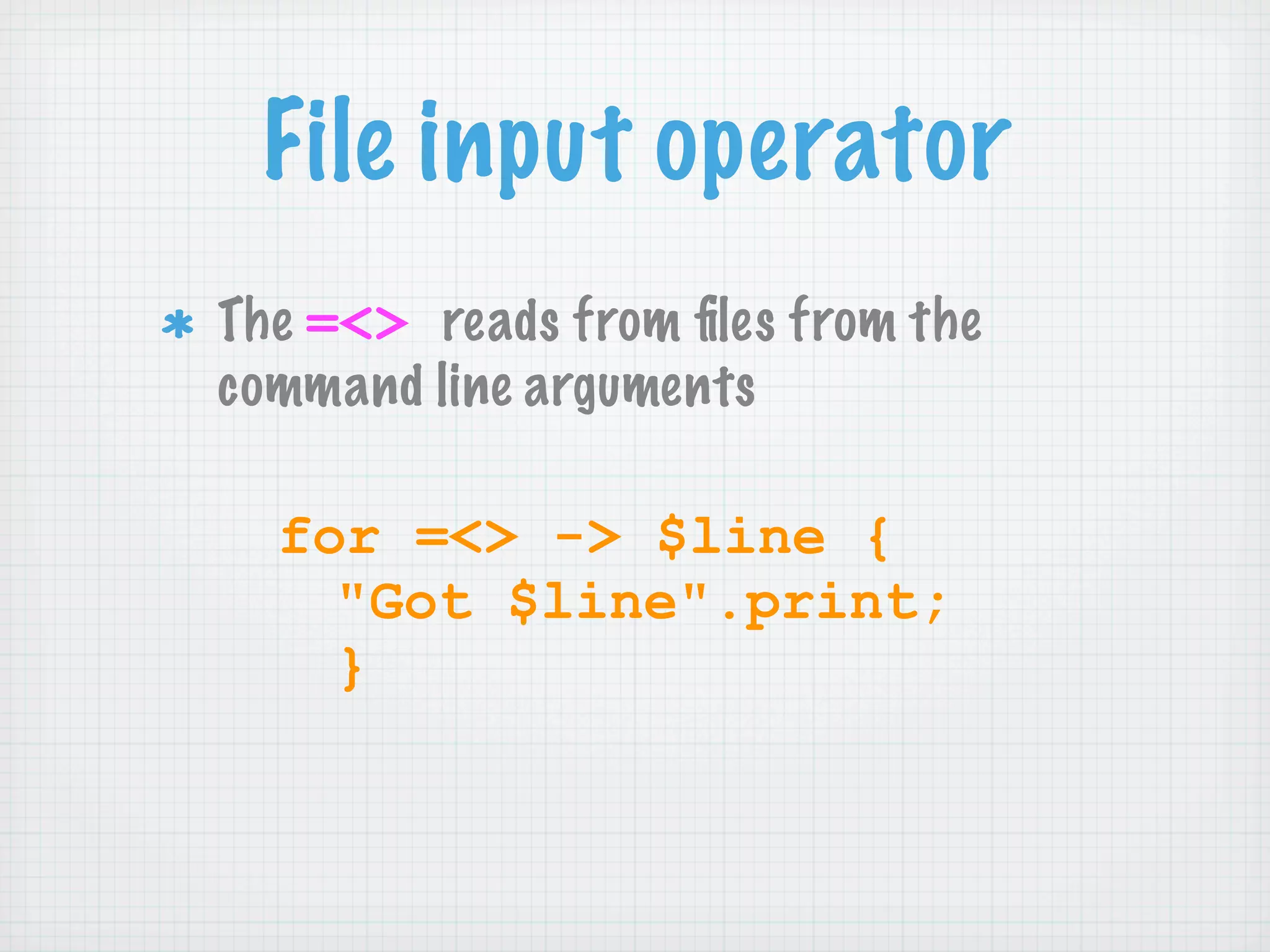
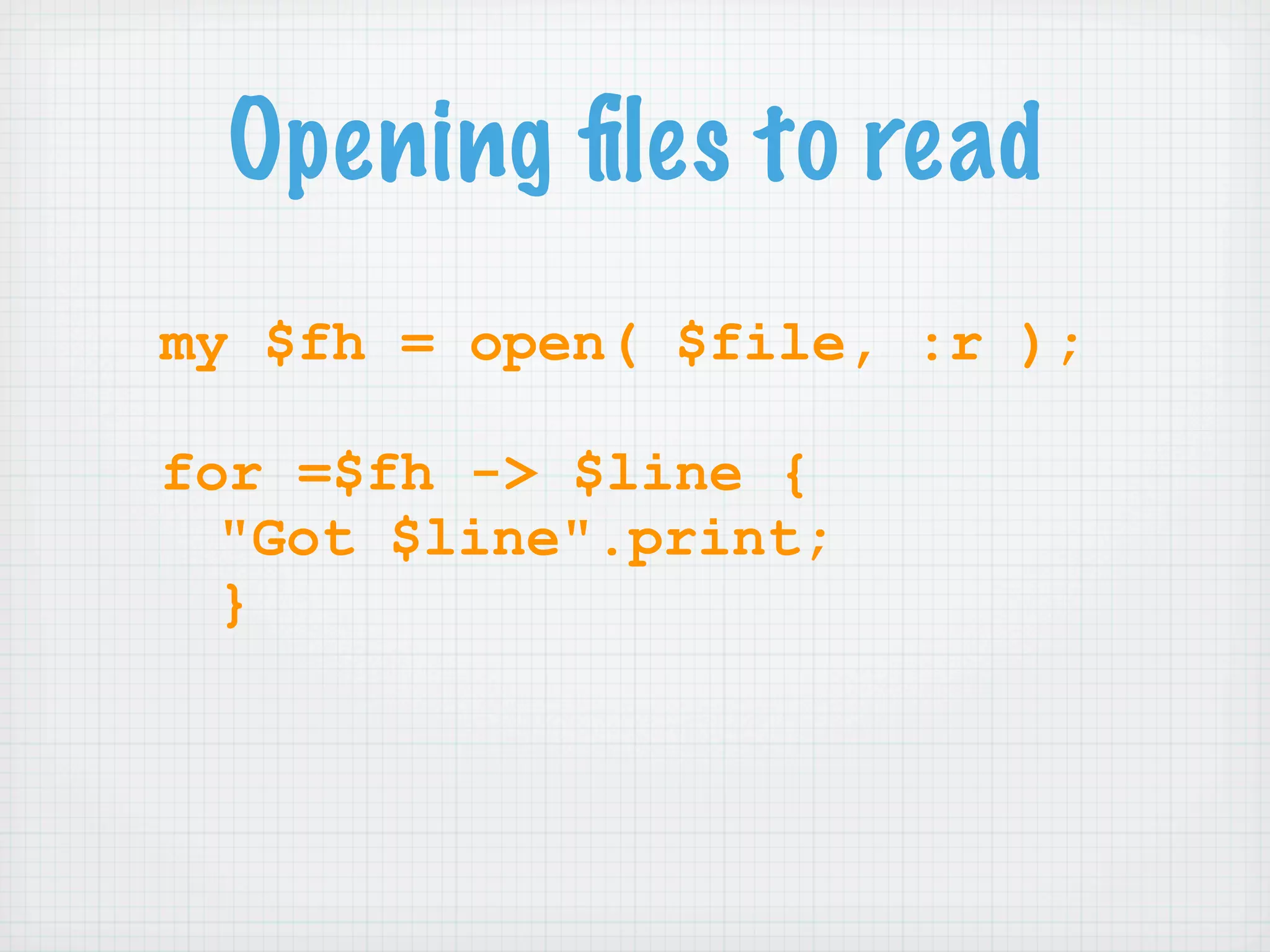
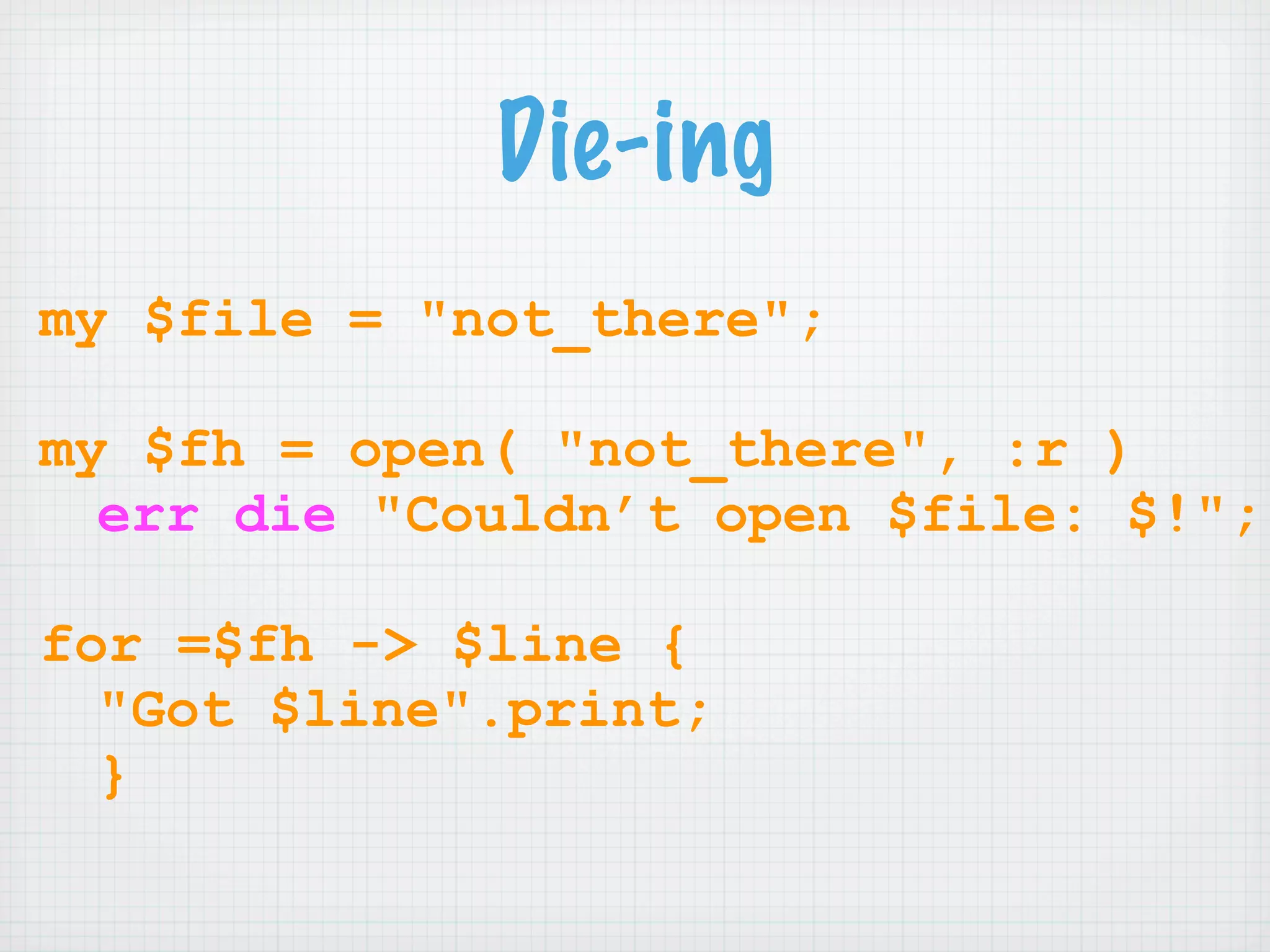
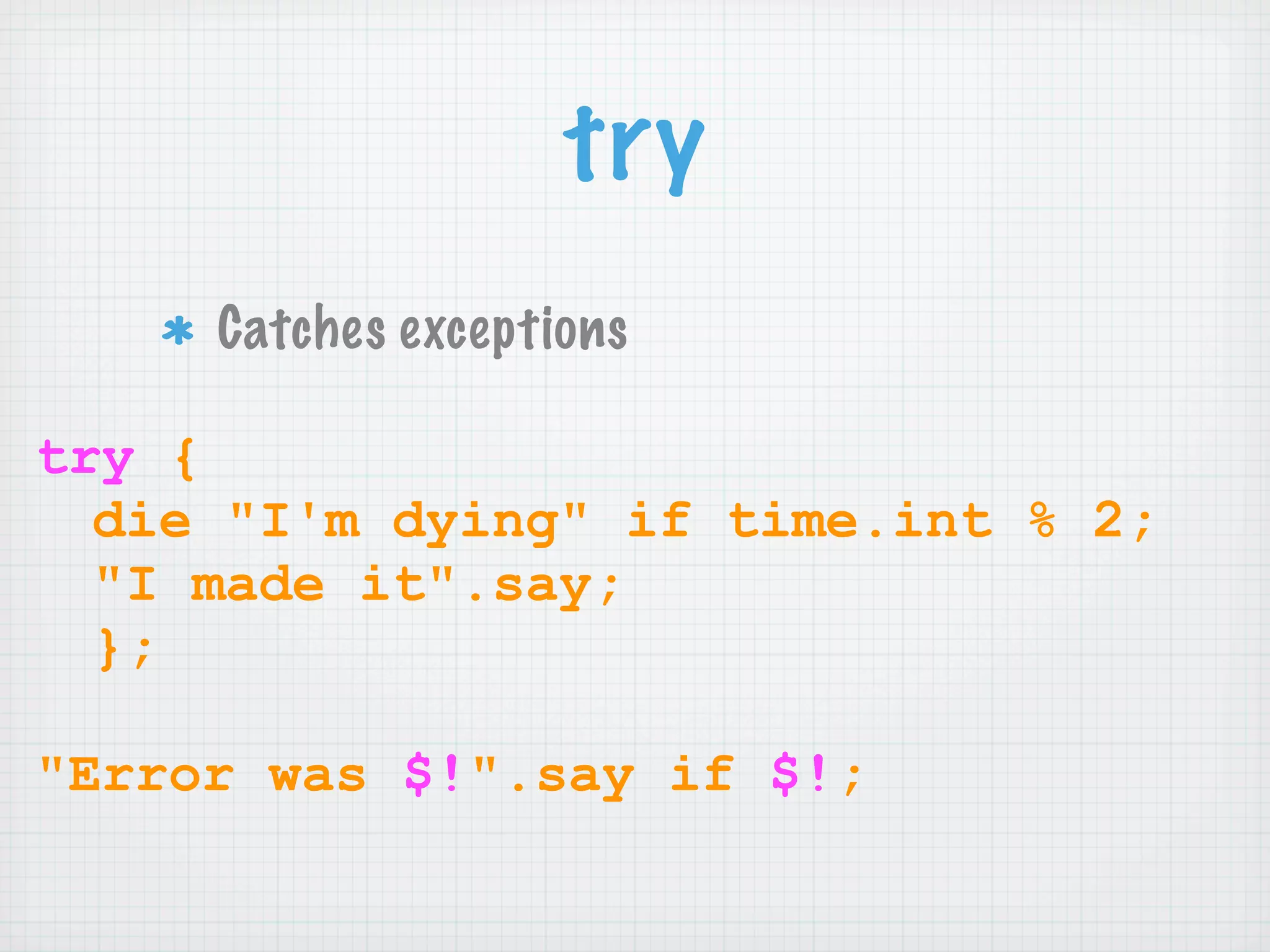
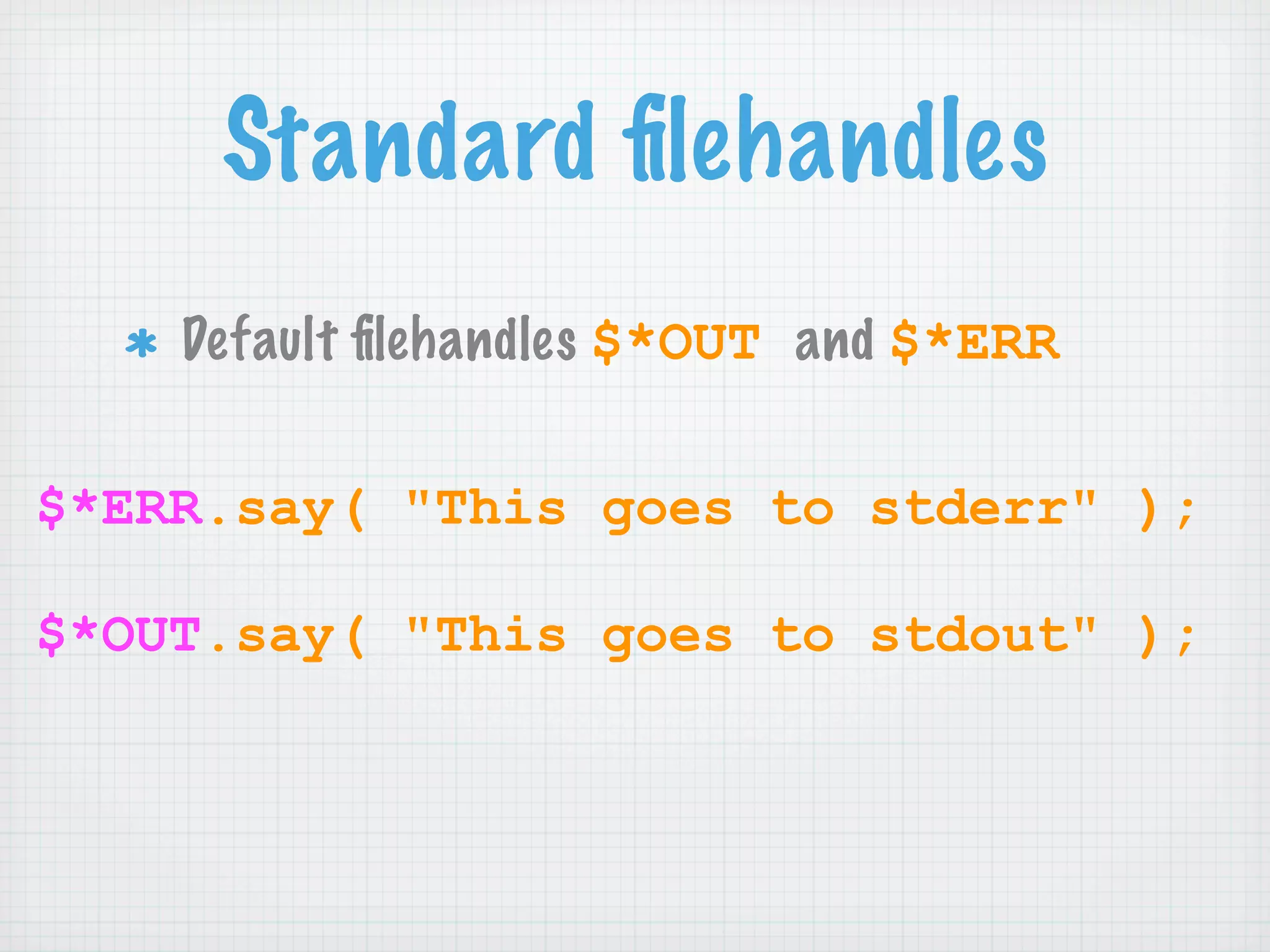
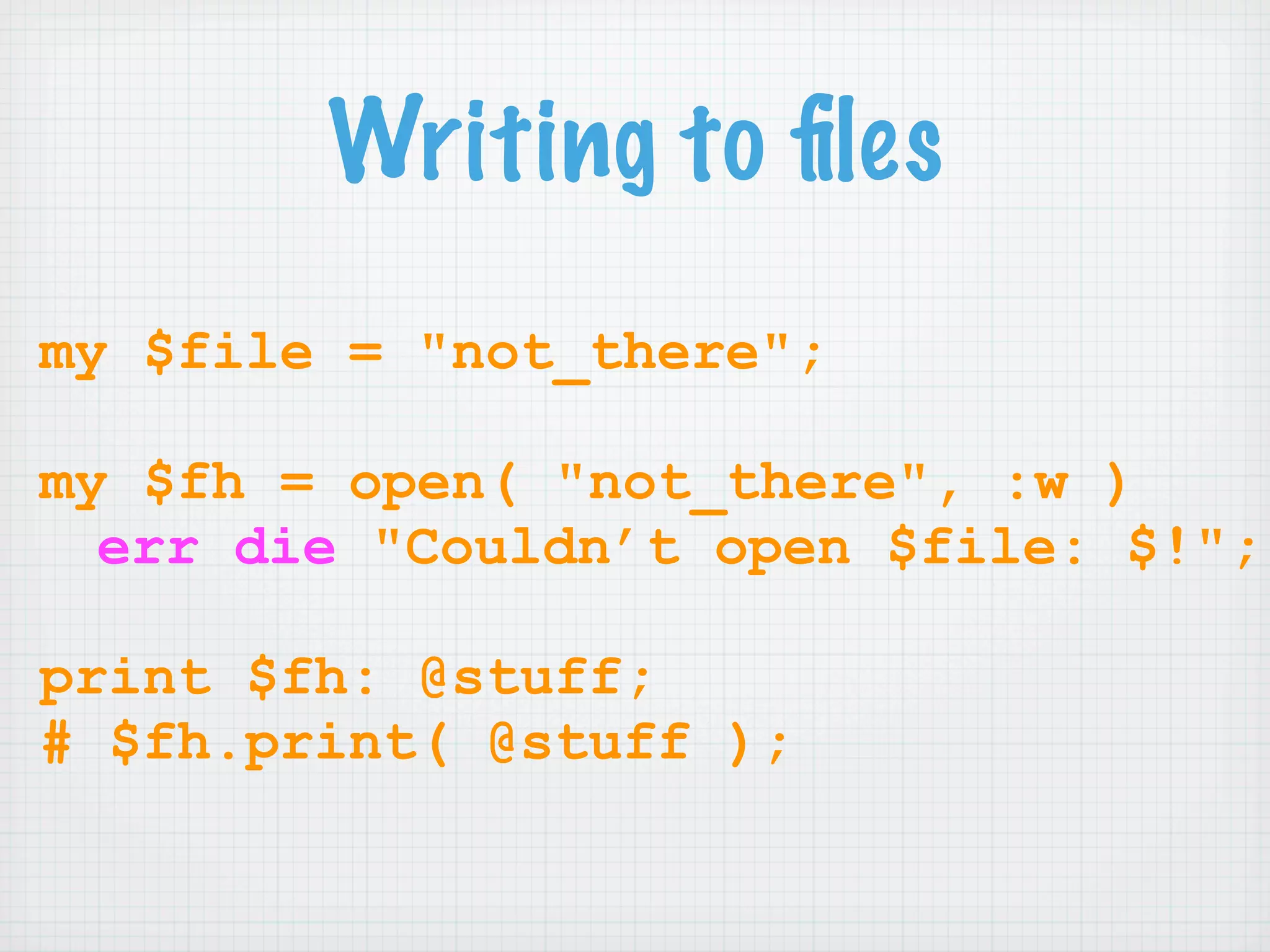
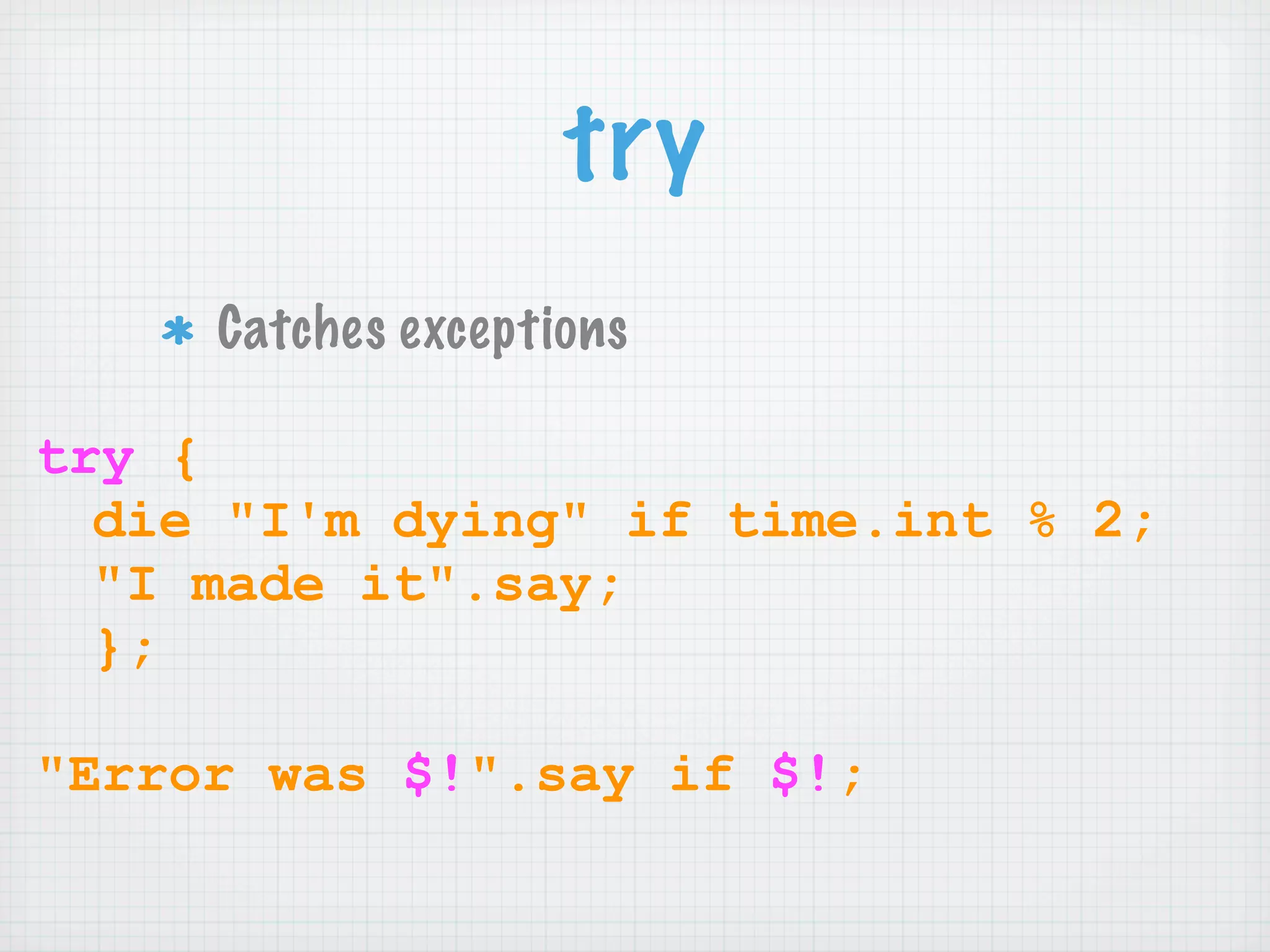
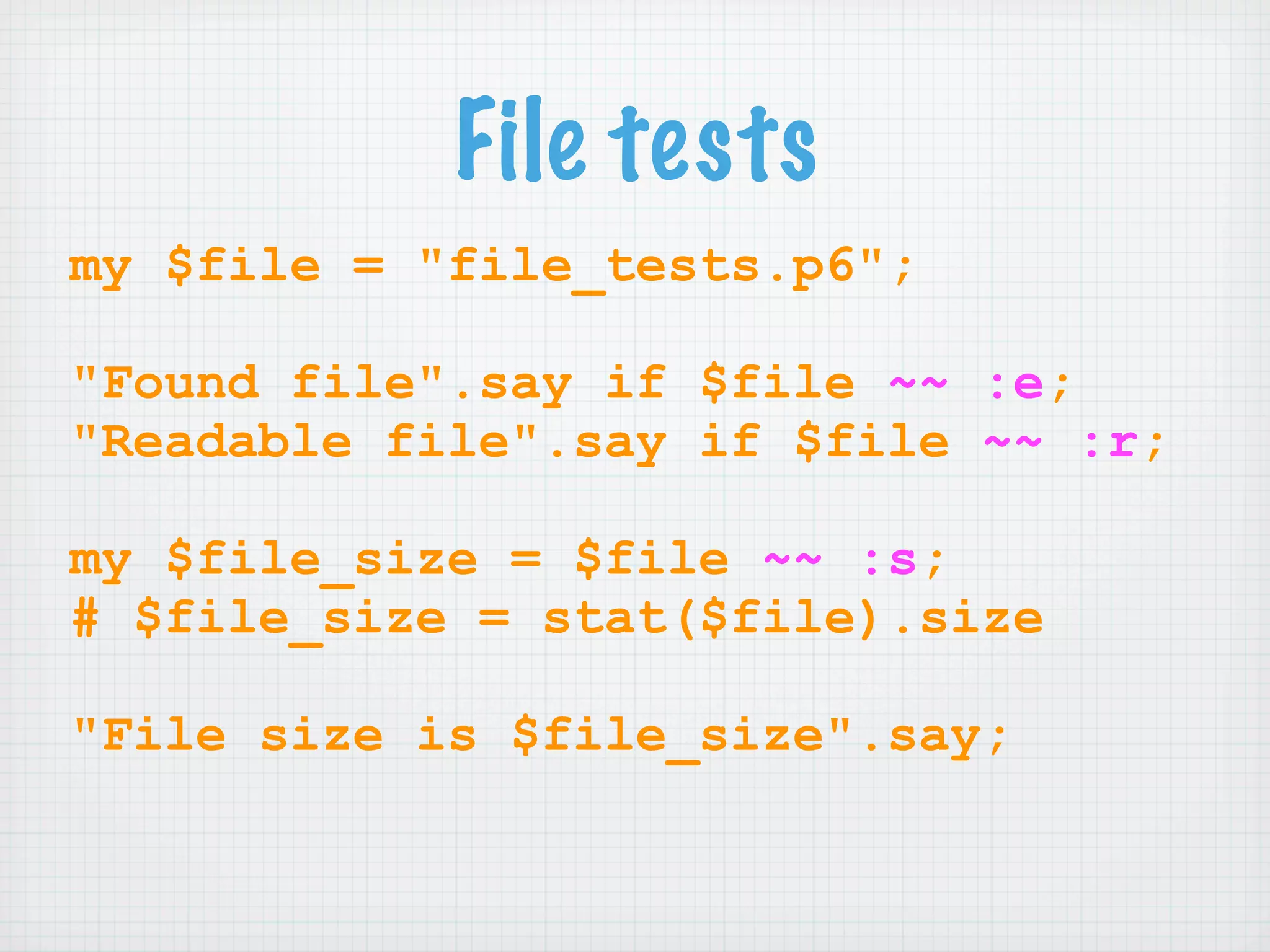
This document provides an introduction and overview of the Perl 6 programming language. It covers topics such as getting started with Perl 6 using Pugs, basic program structure, scalars, variables, control structures, arrays, hashes, input/output, and more. The summary is designed to give a high-level understanding of the key topics covered in the document in 3 sentences or less.