Embed presentation
Download as PDF, PPTX
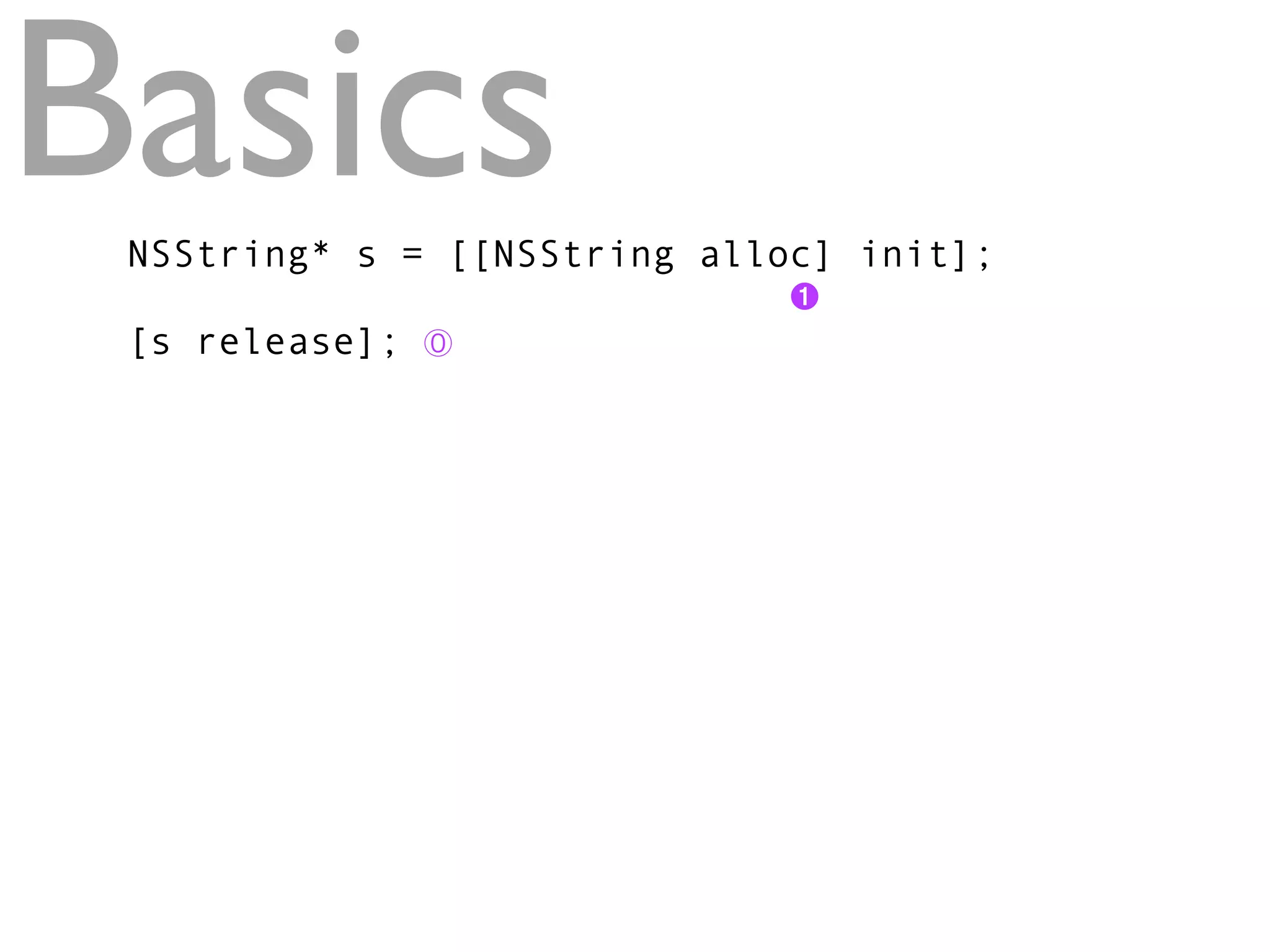
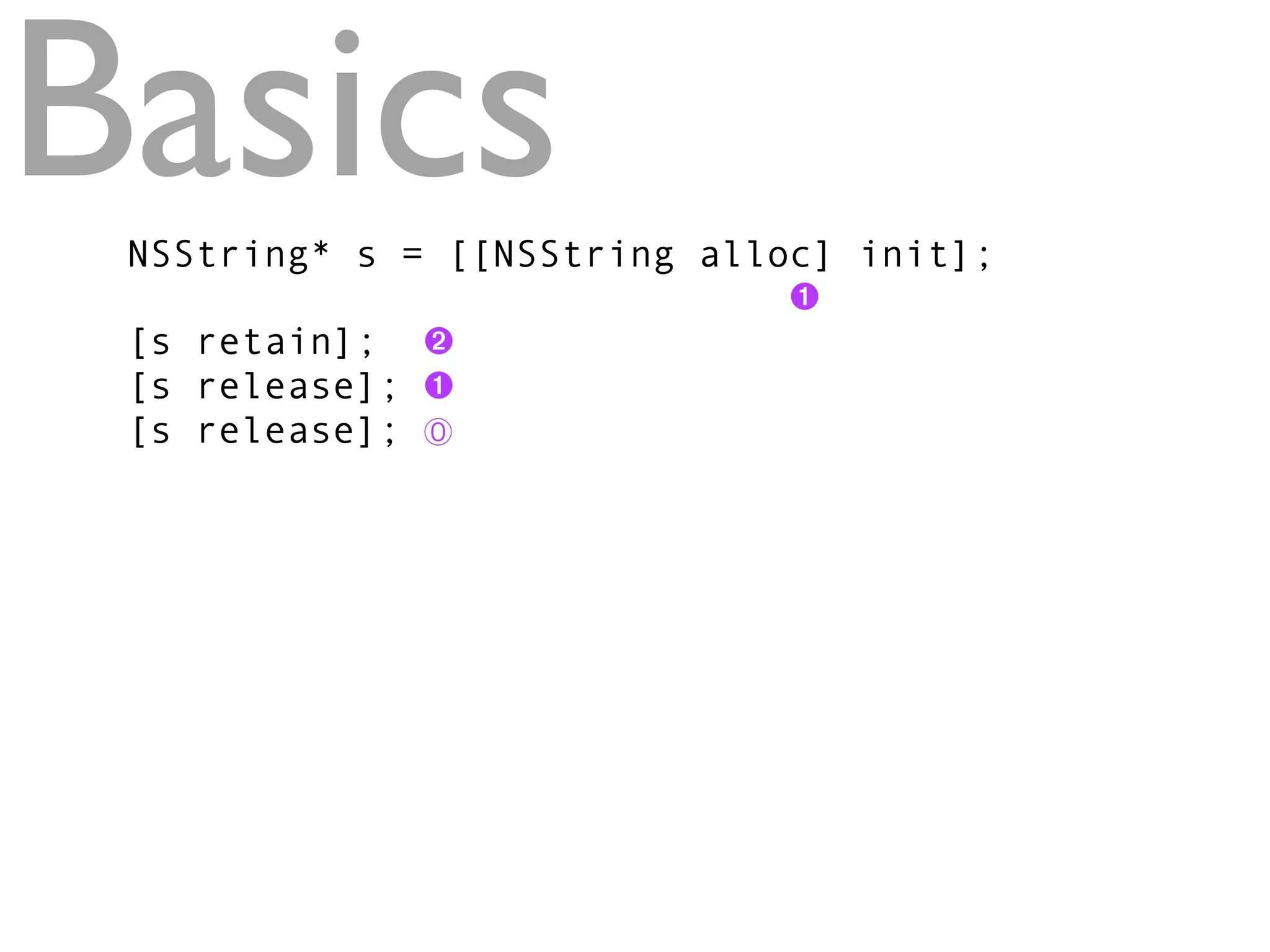
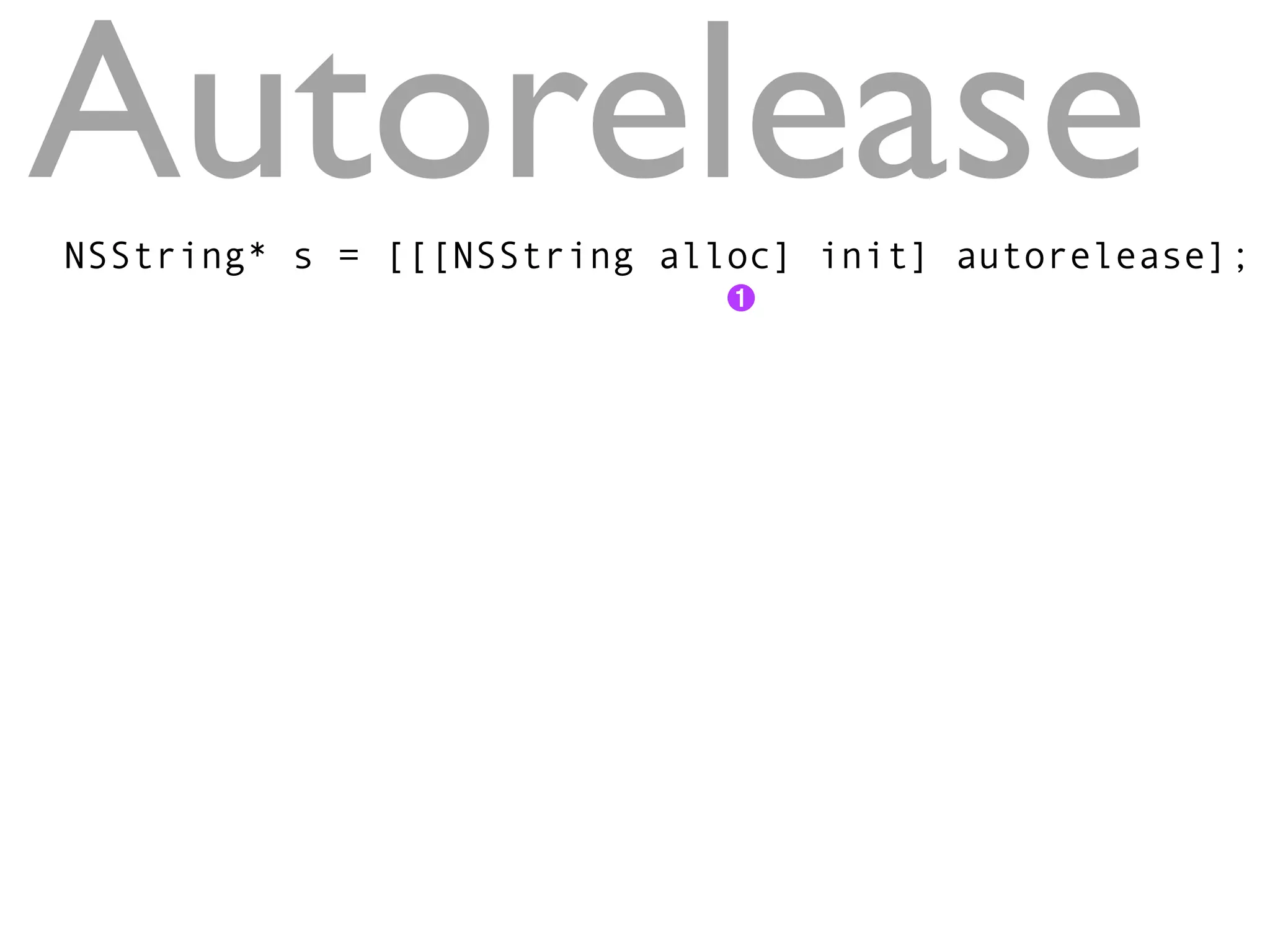
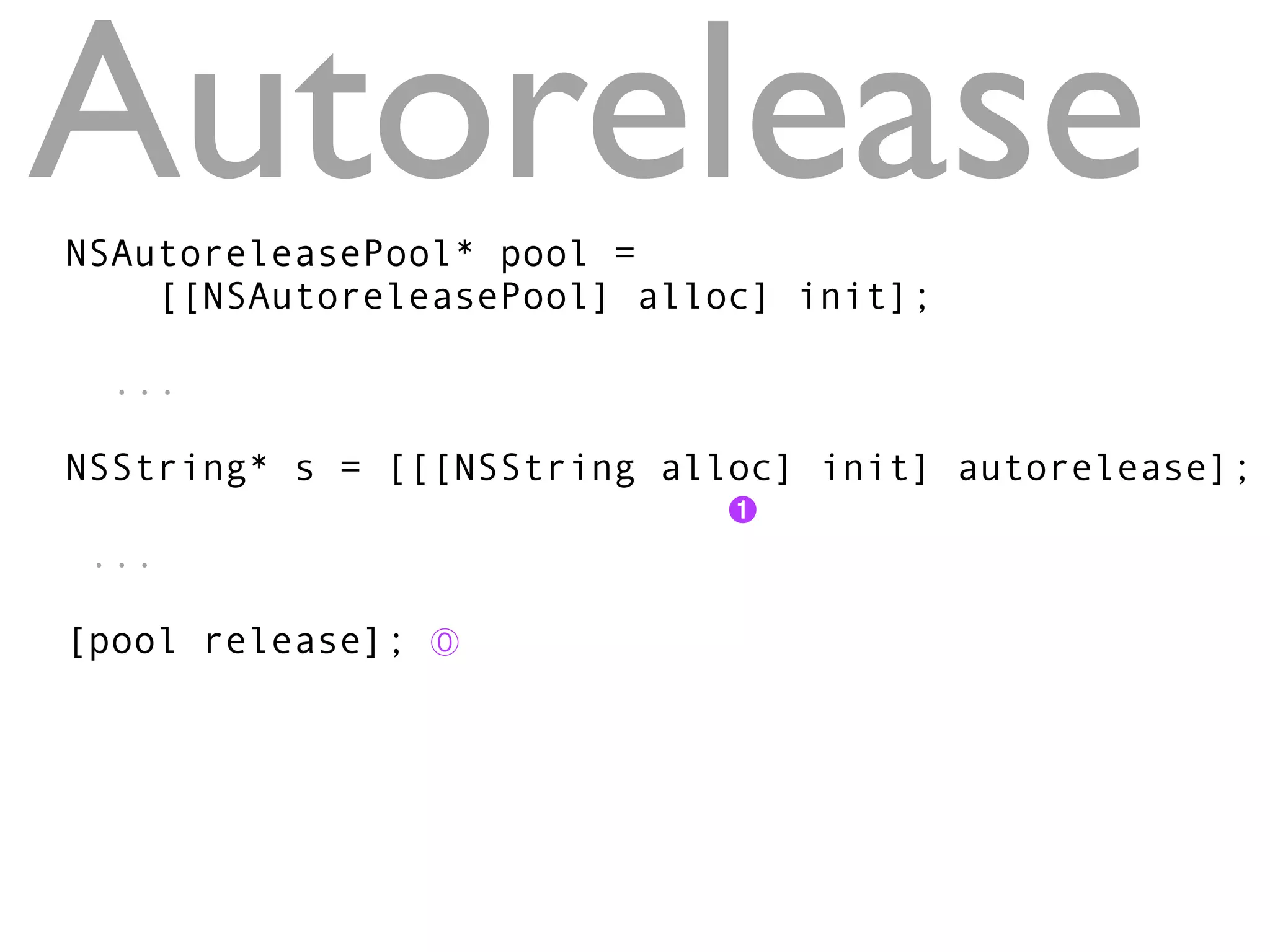
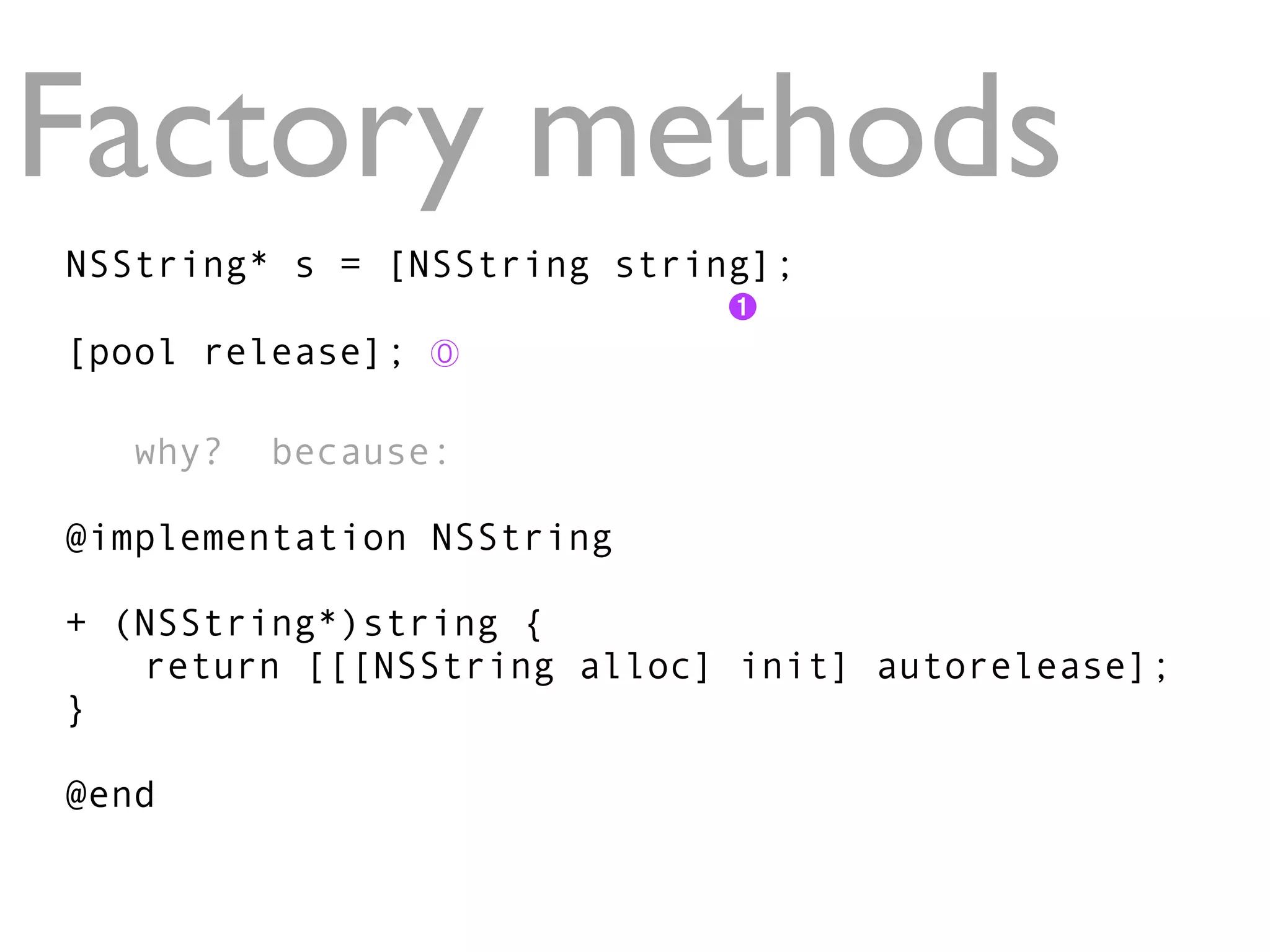
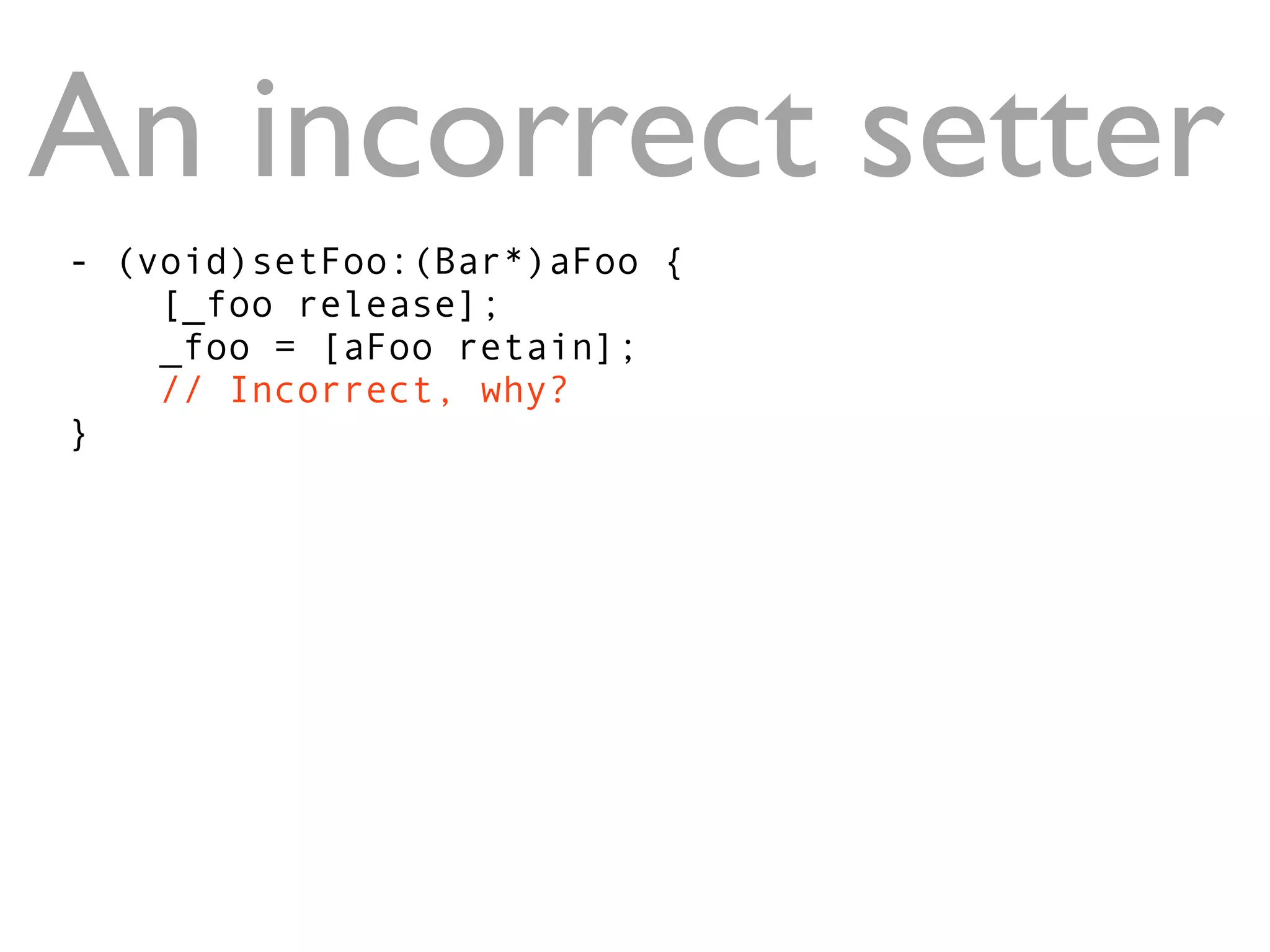
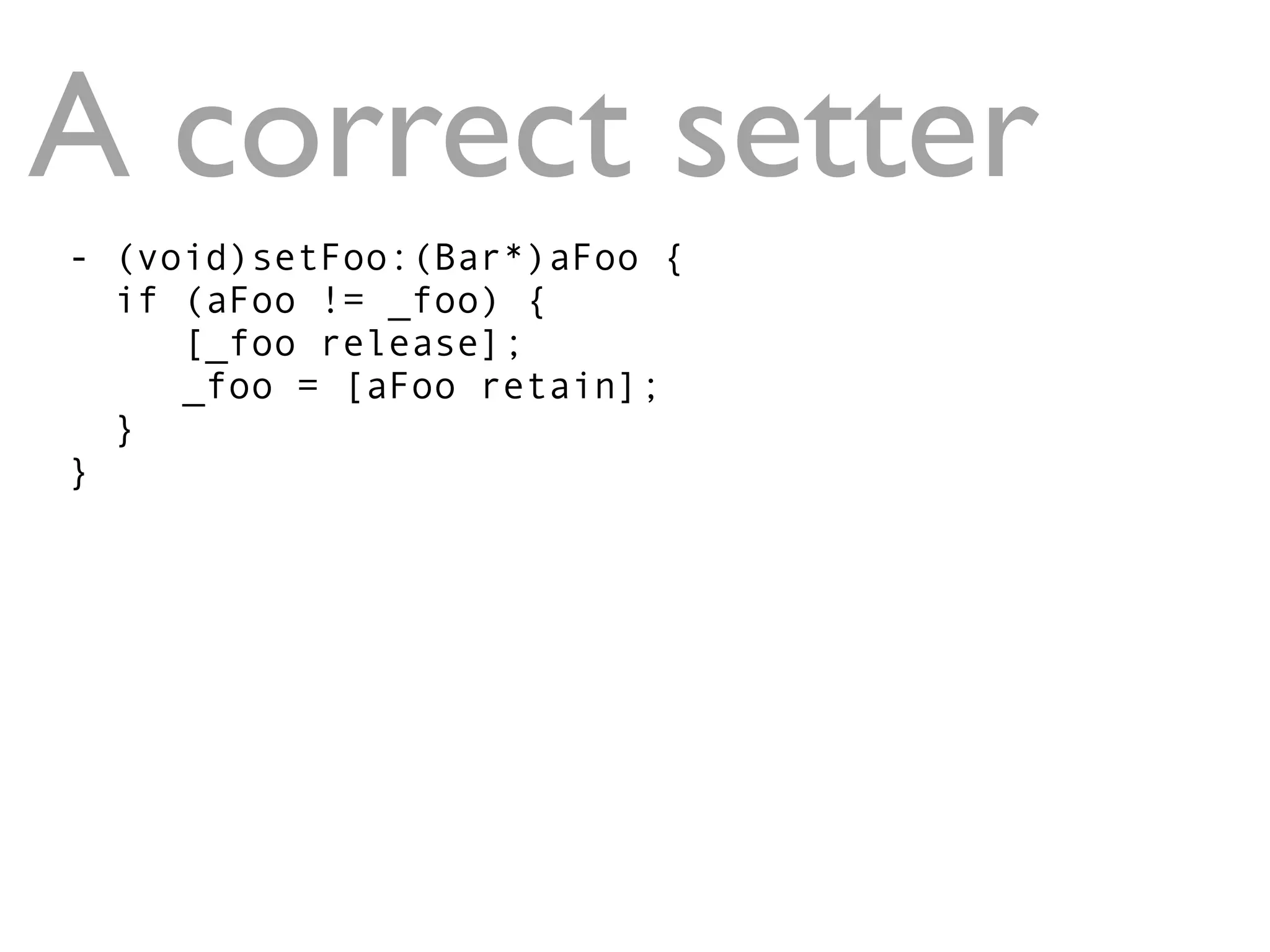
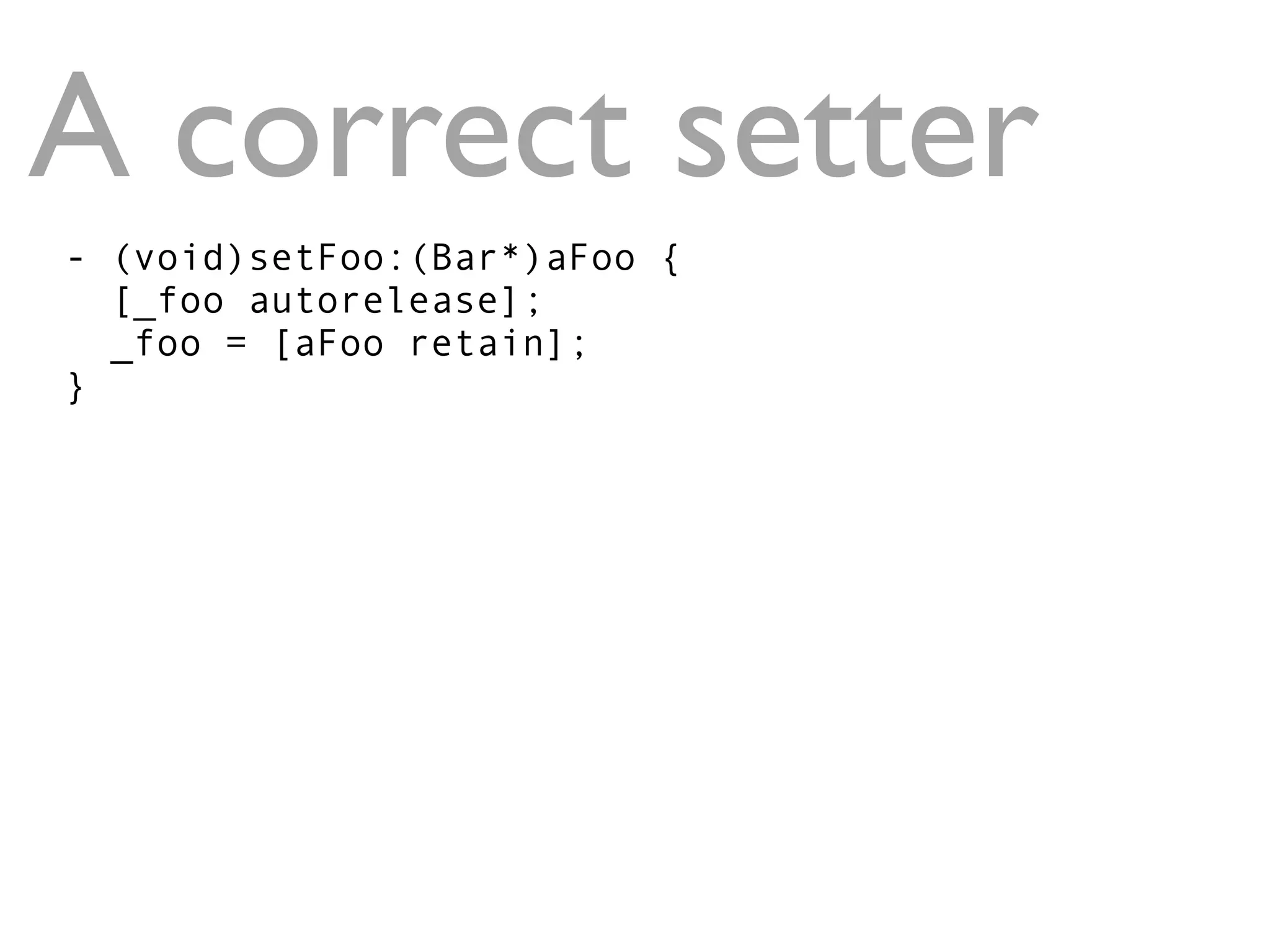
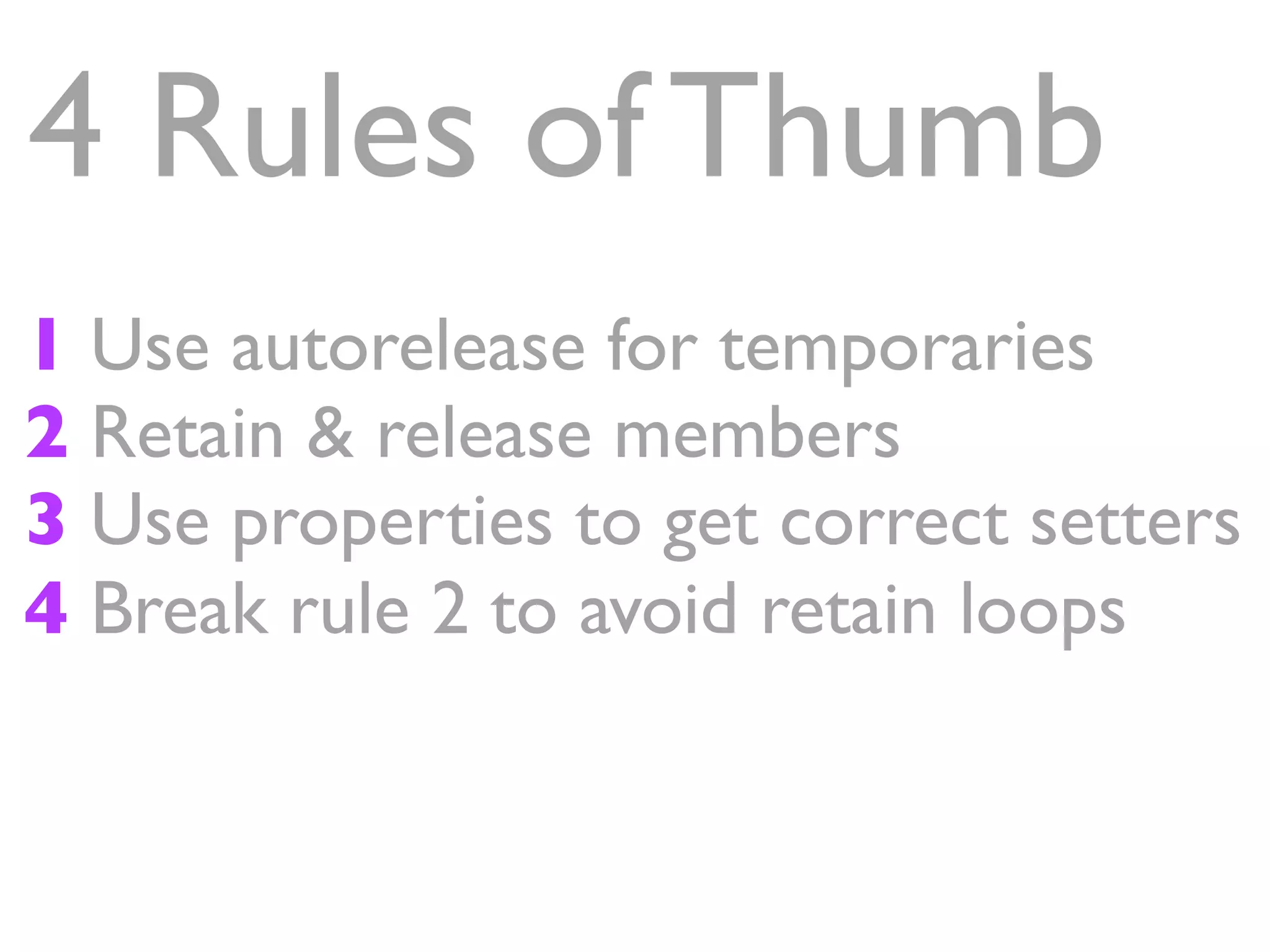
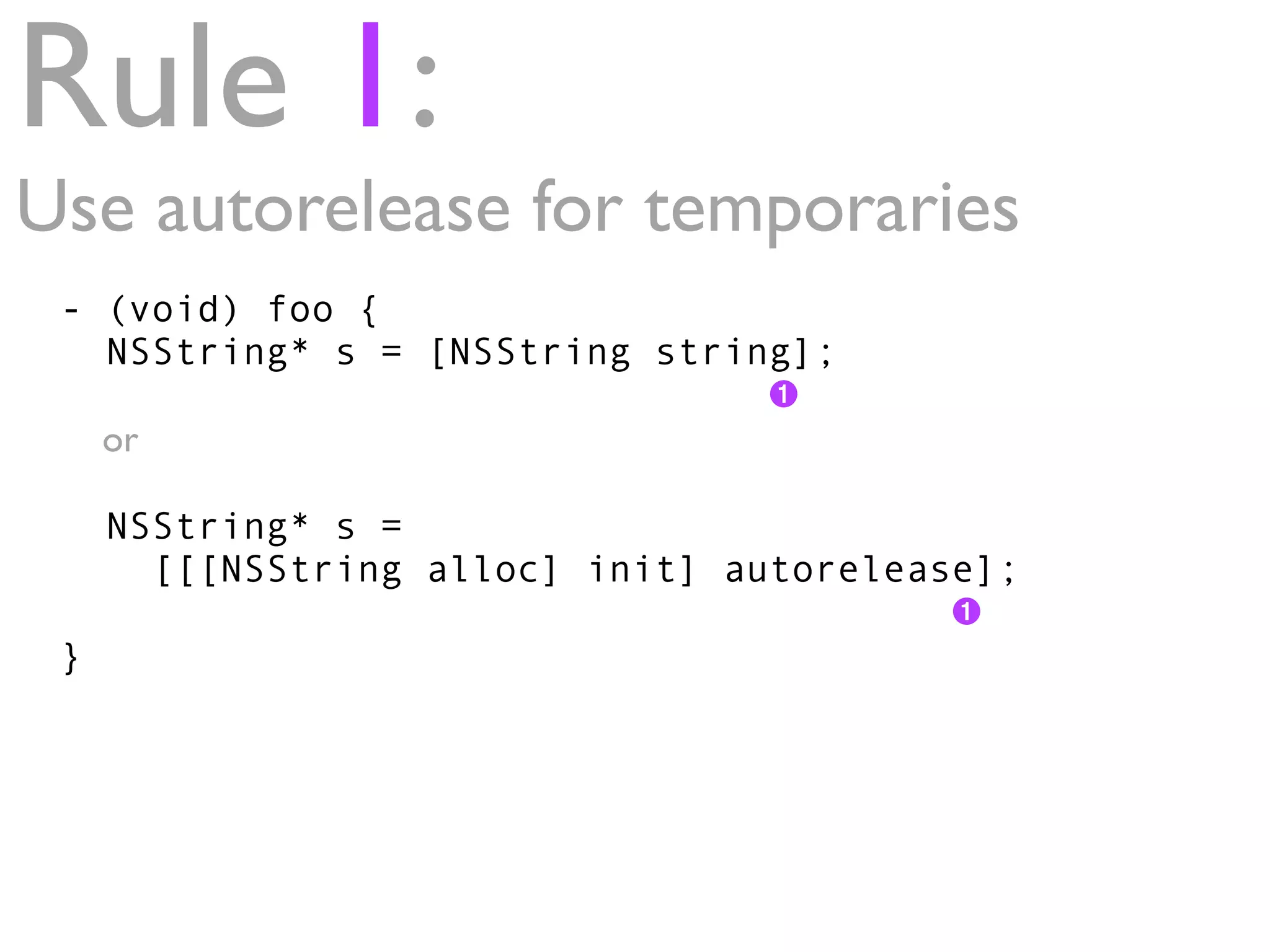
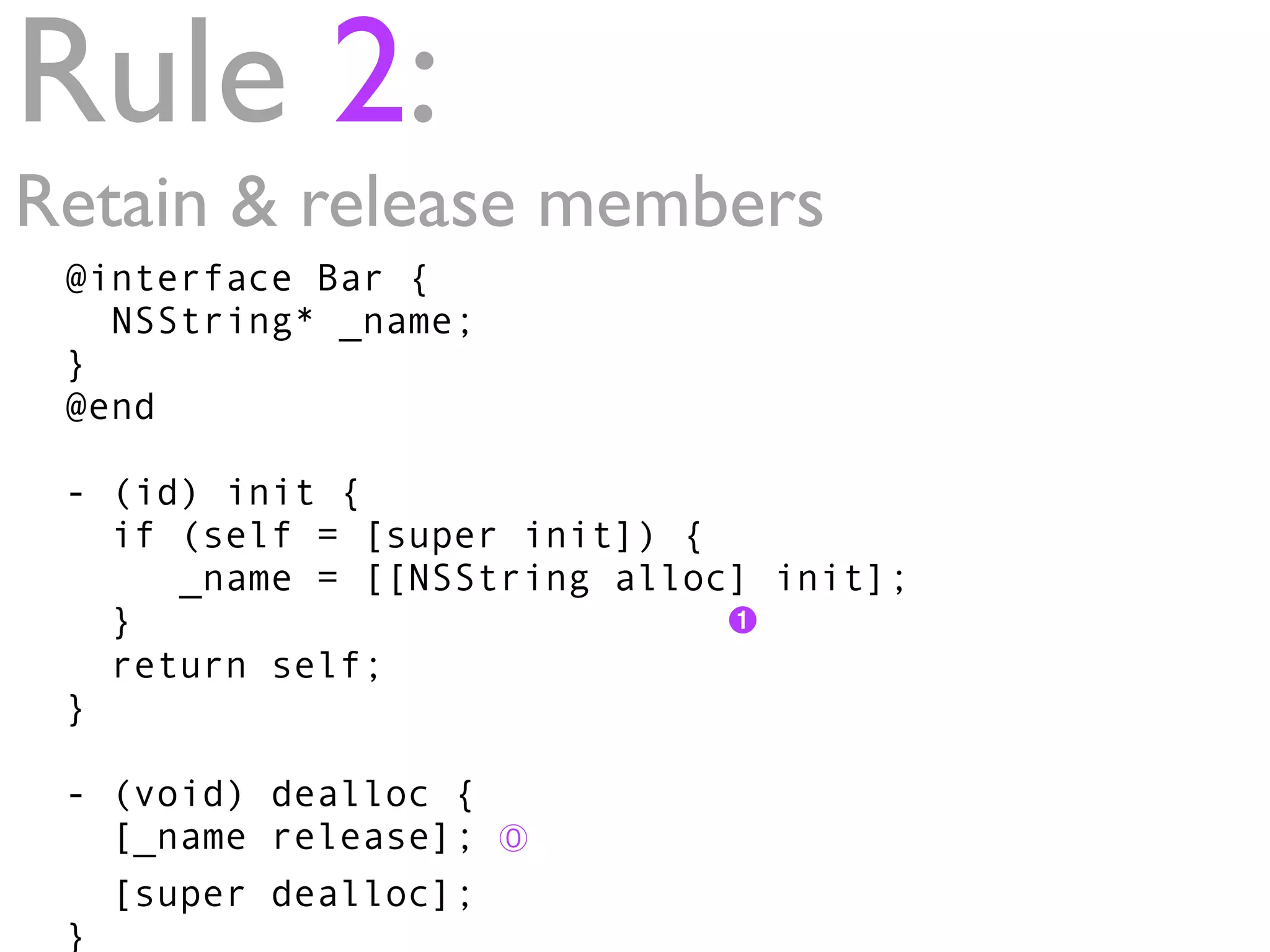
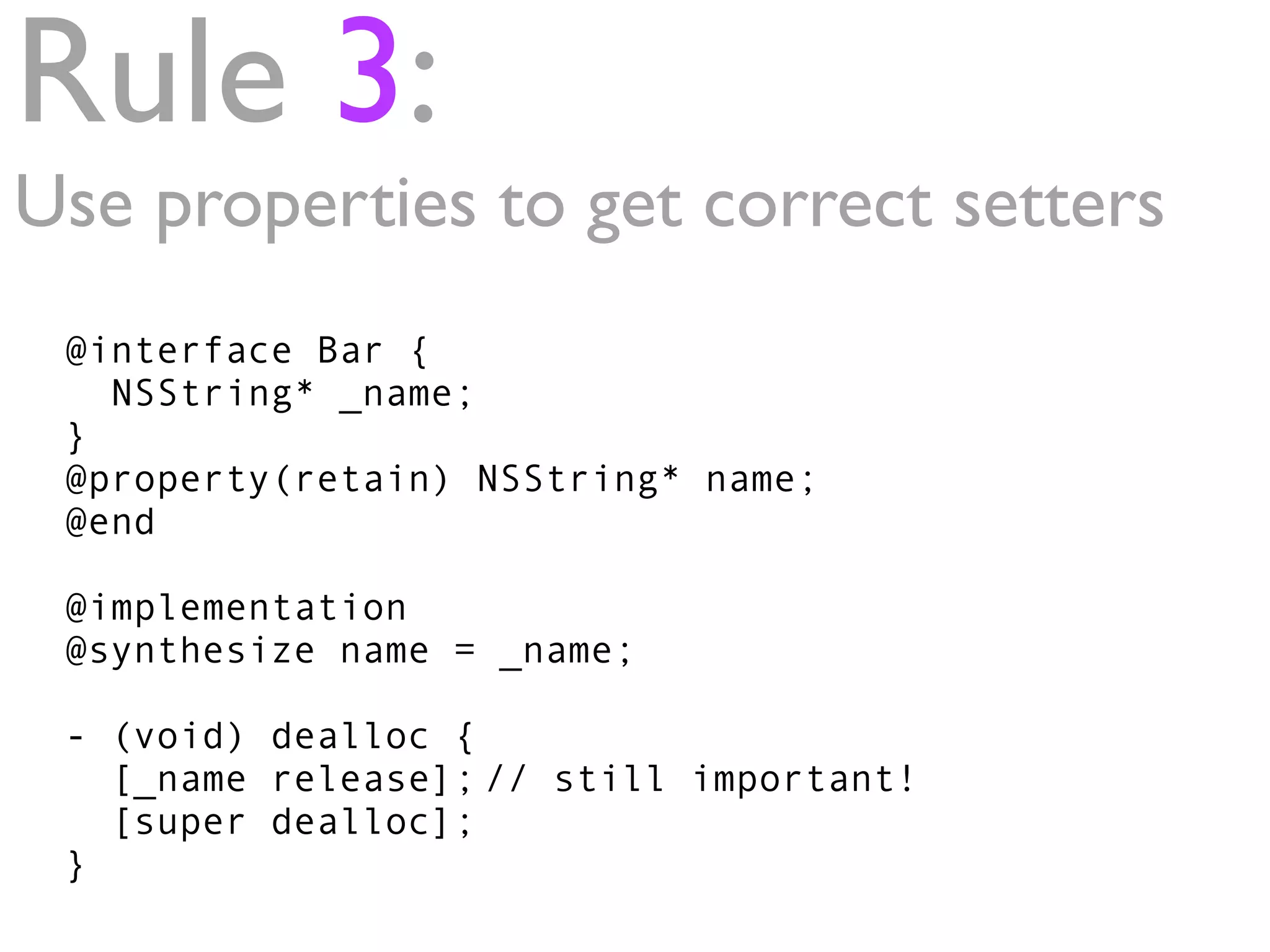
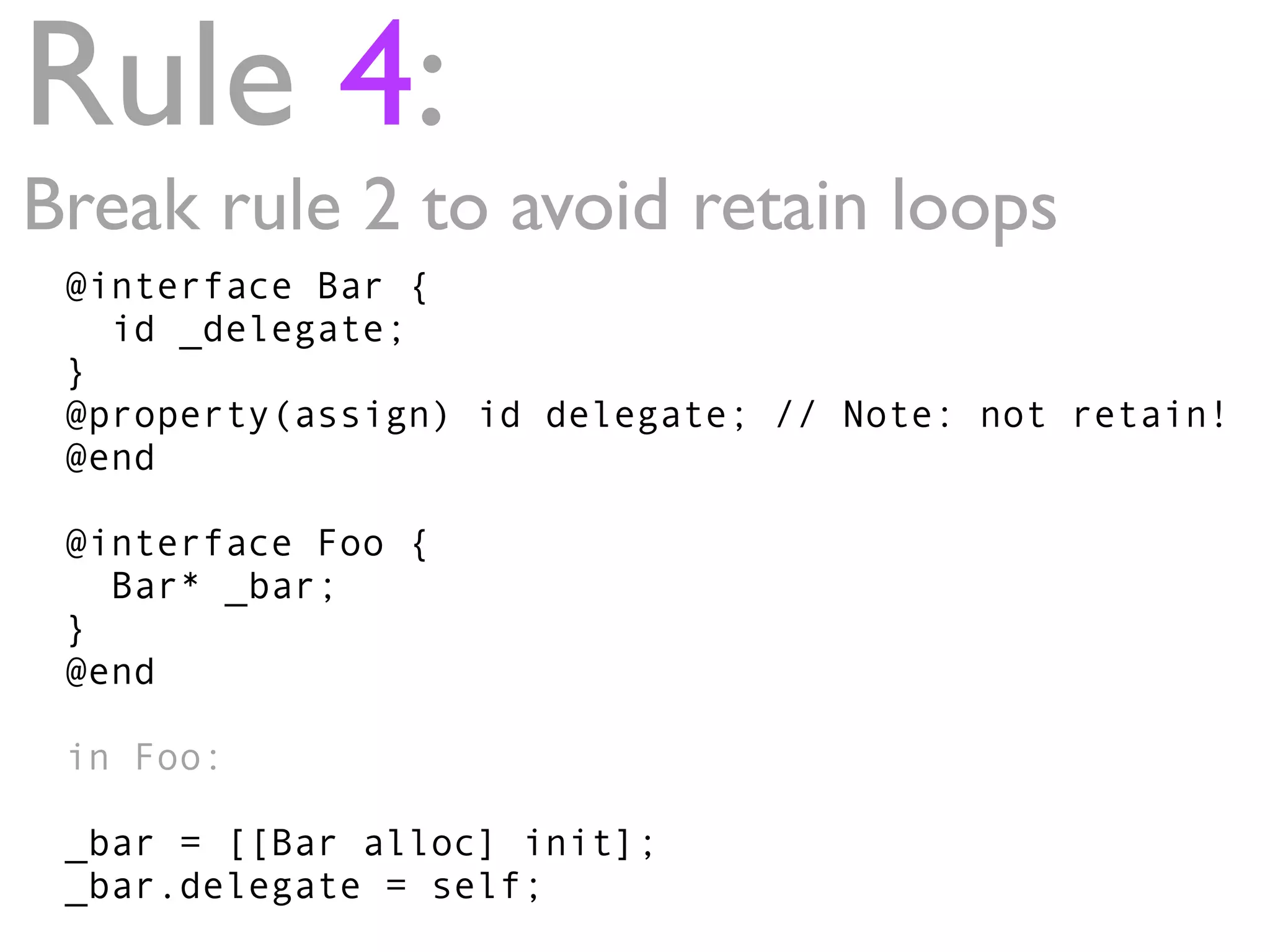

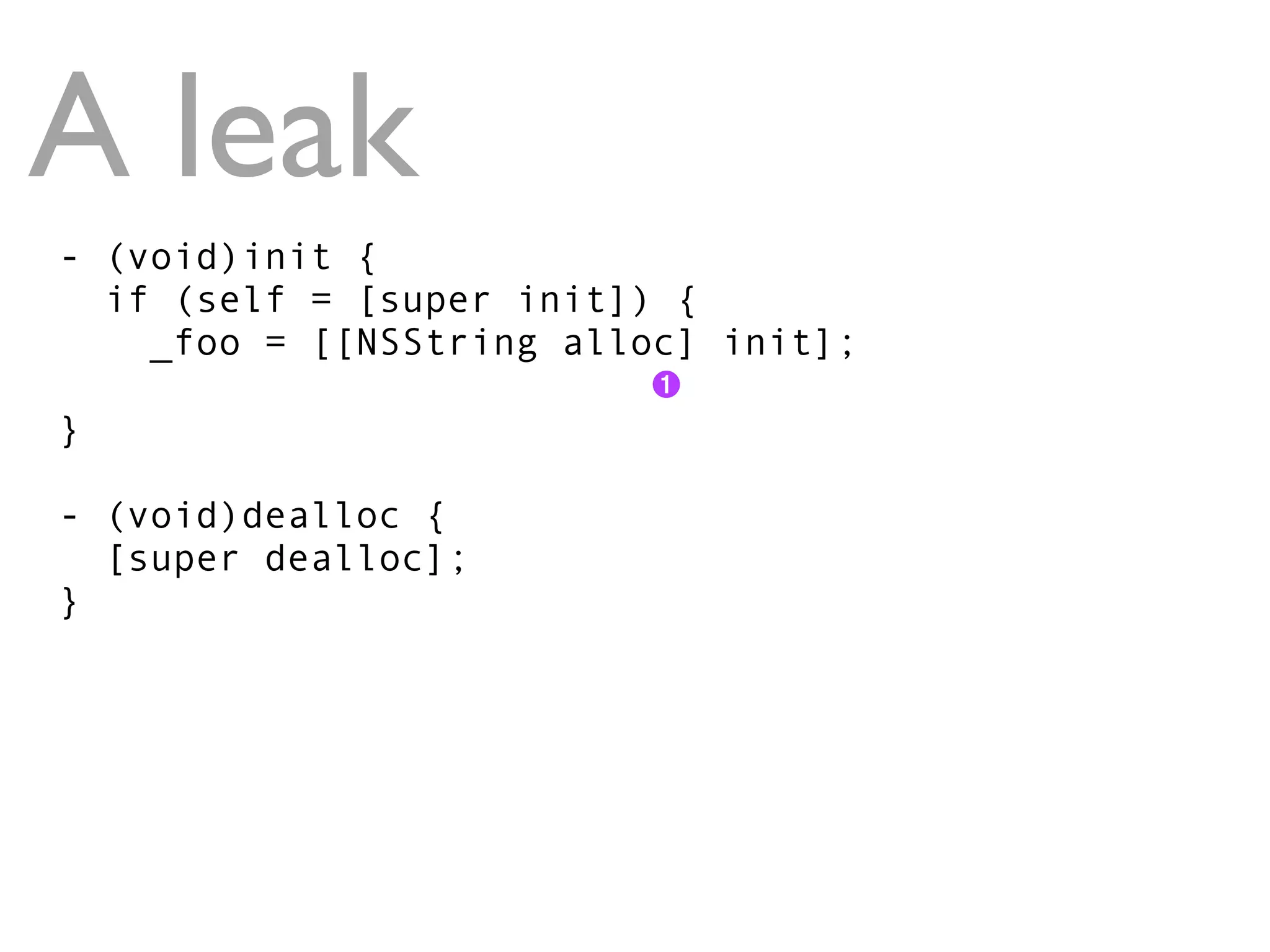

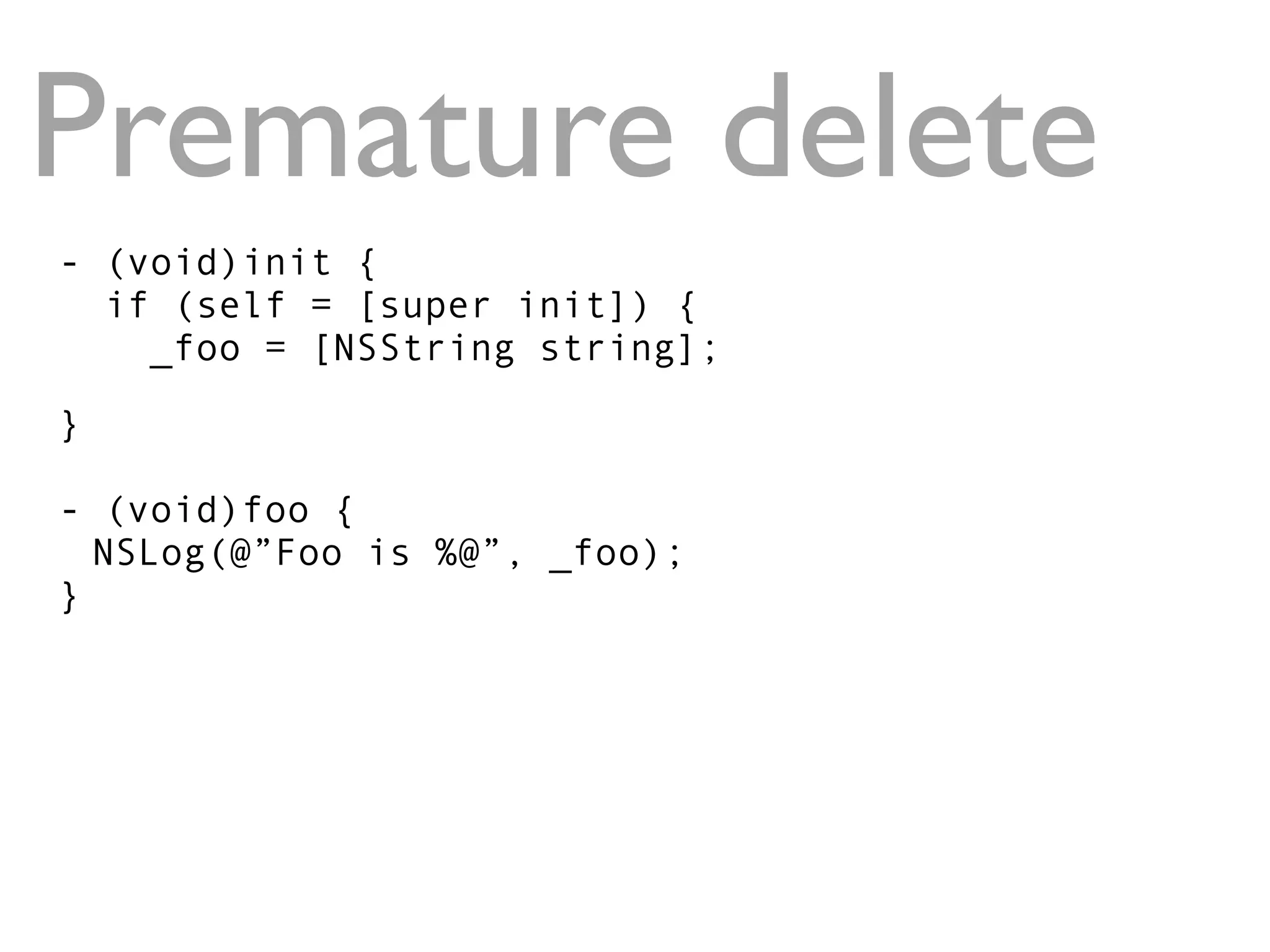

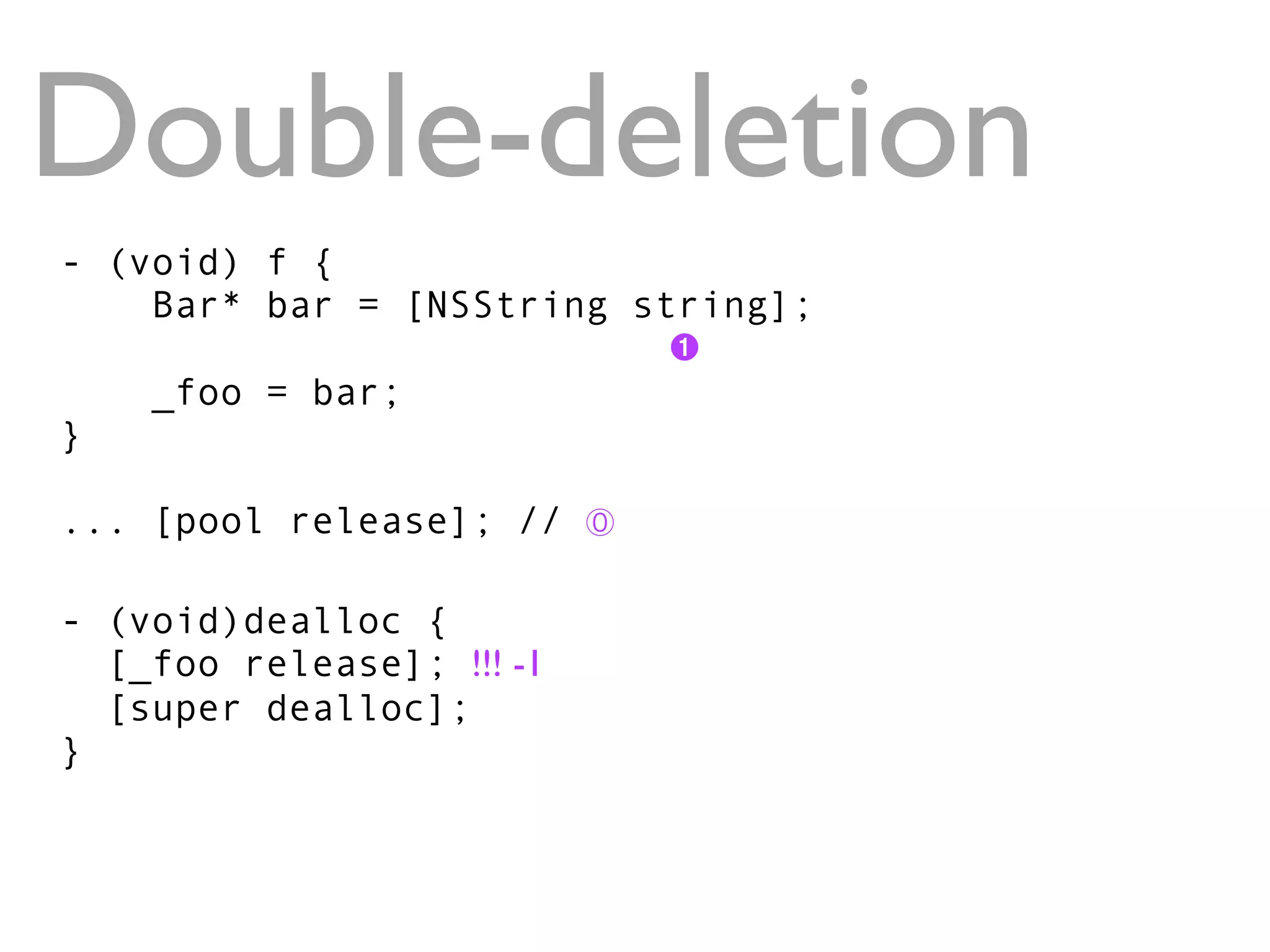



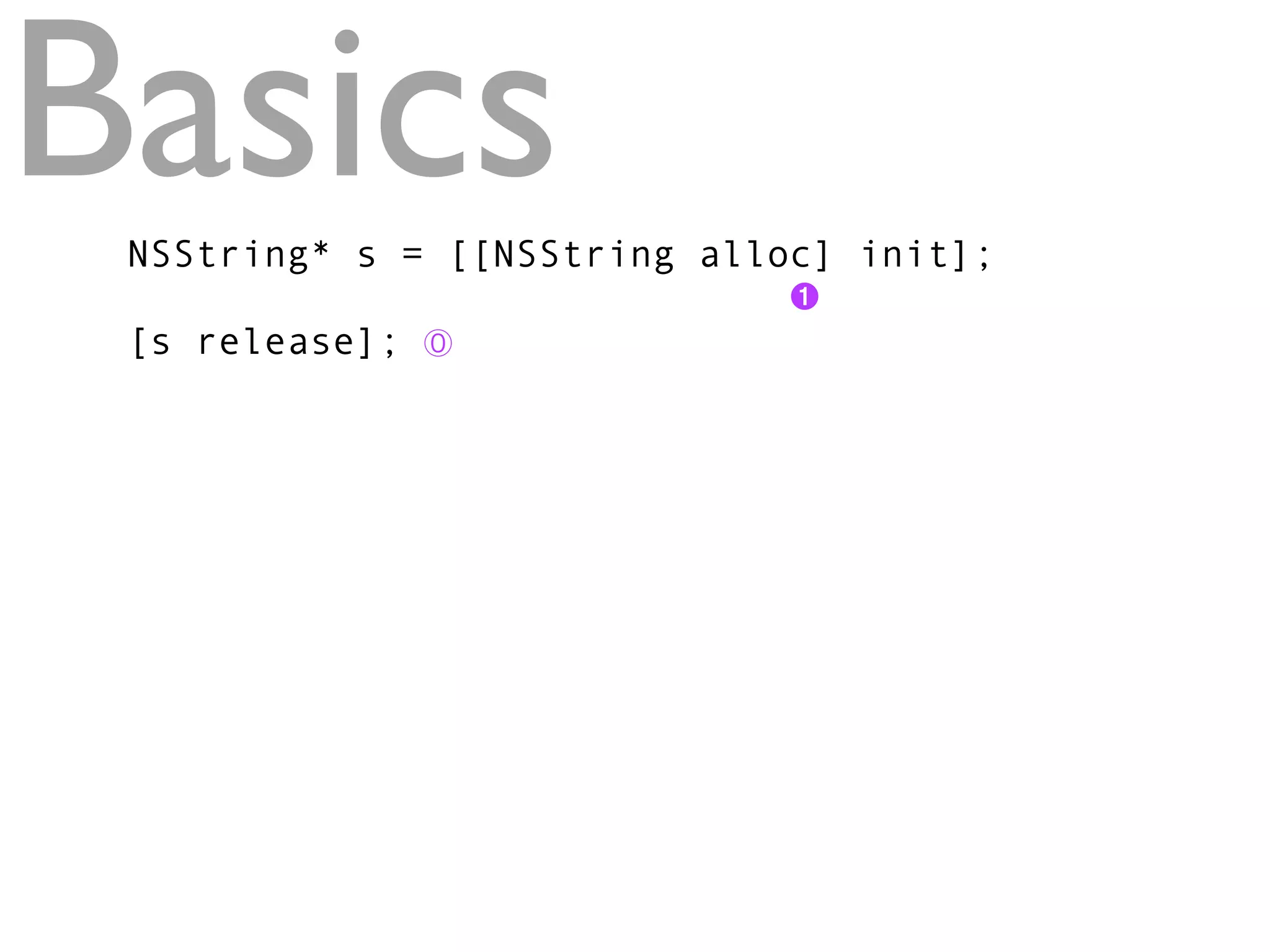
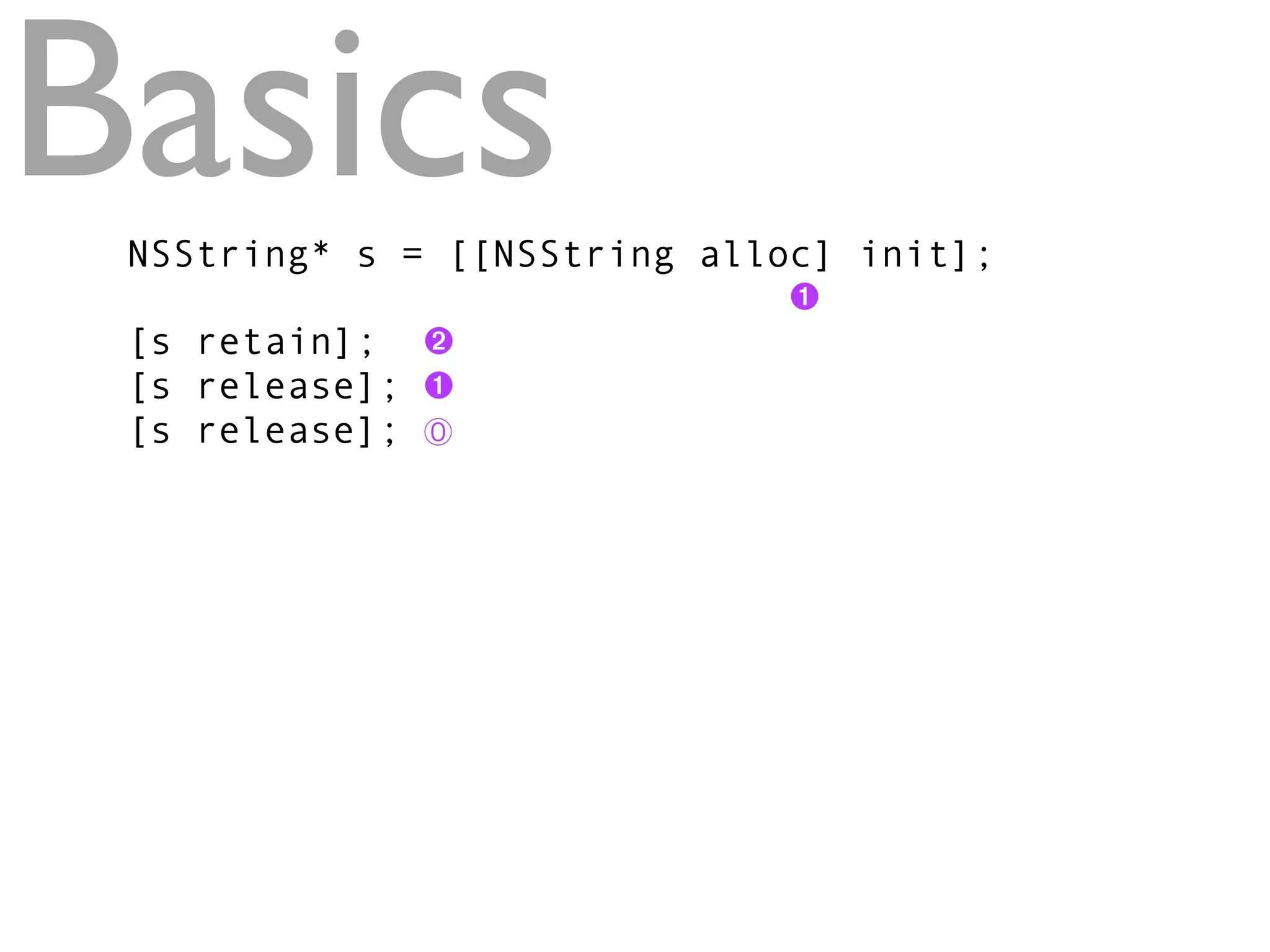
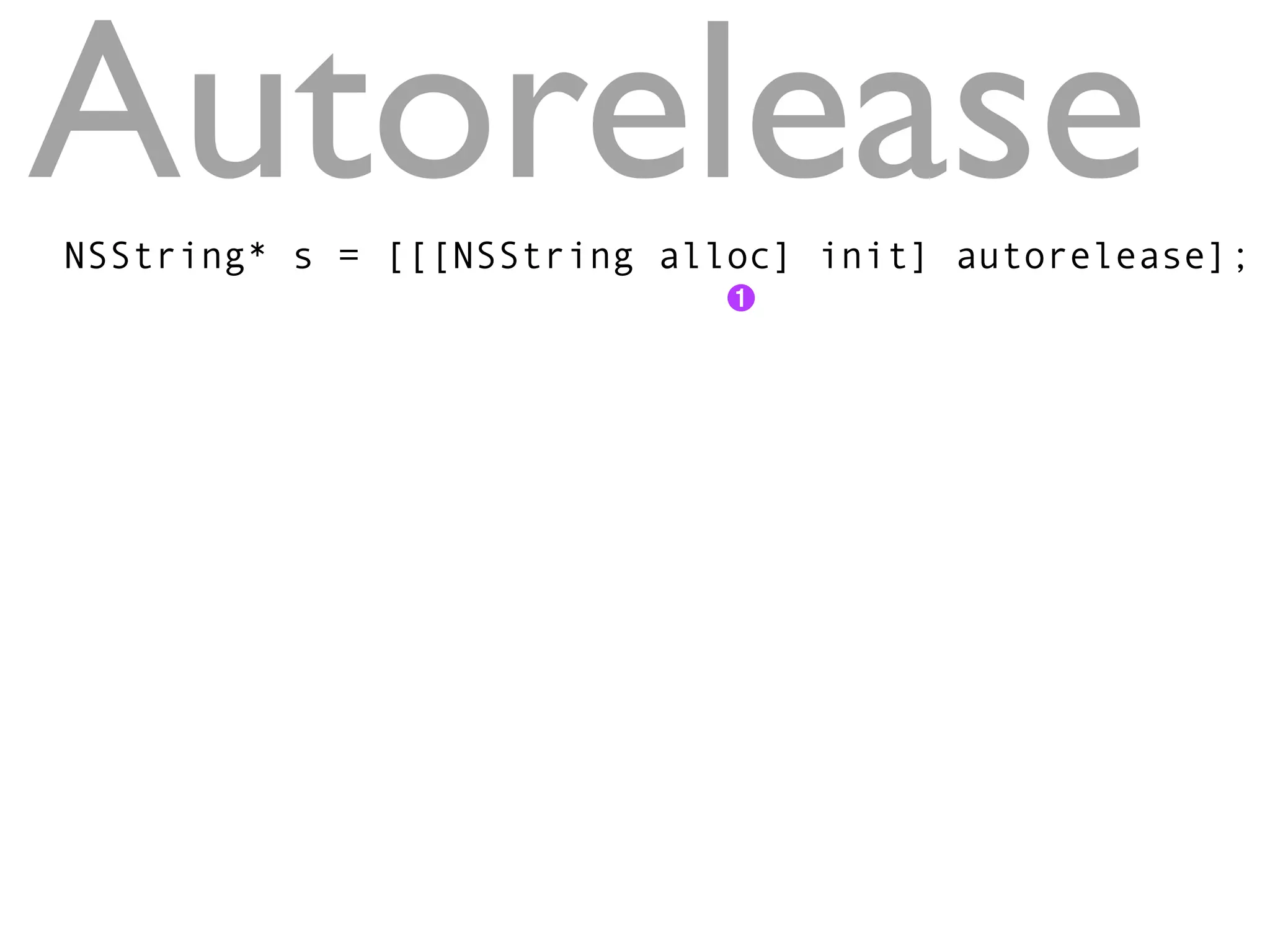
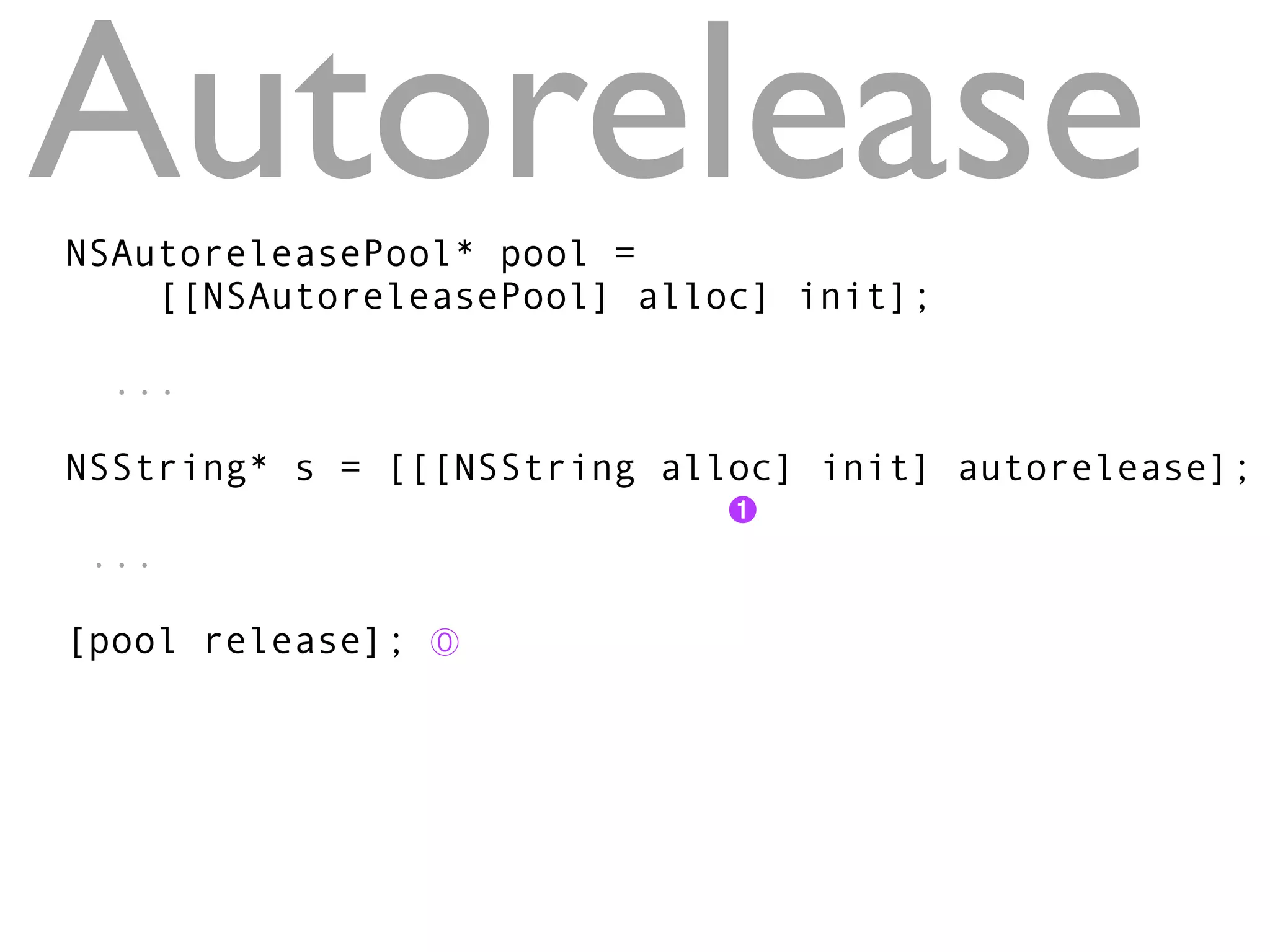
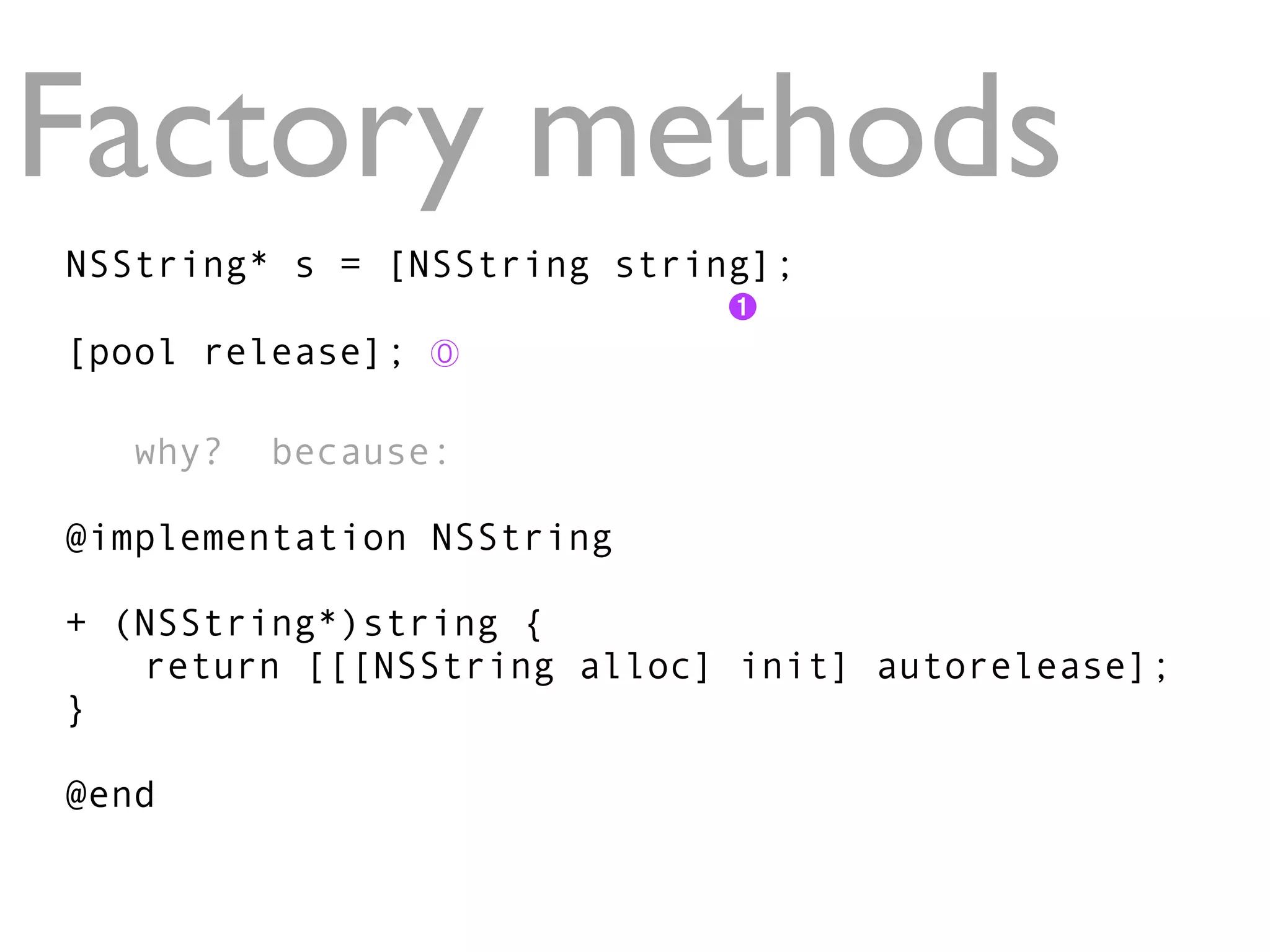
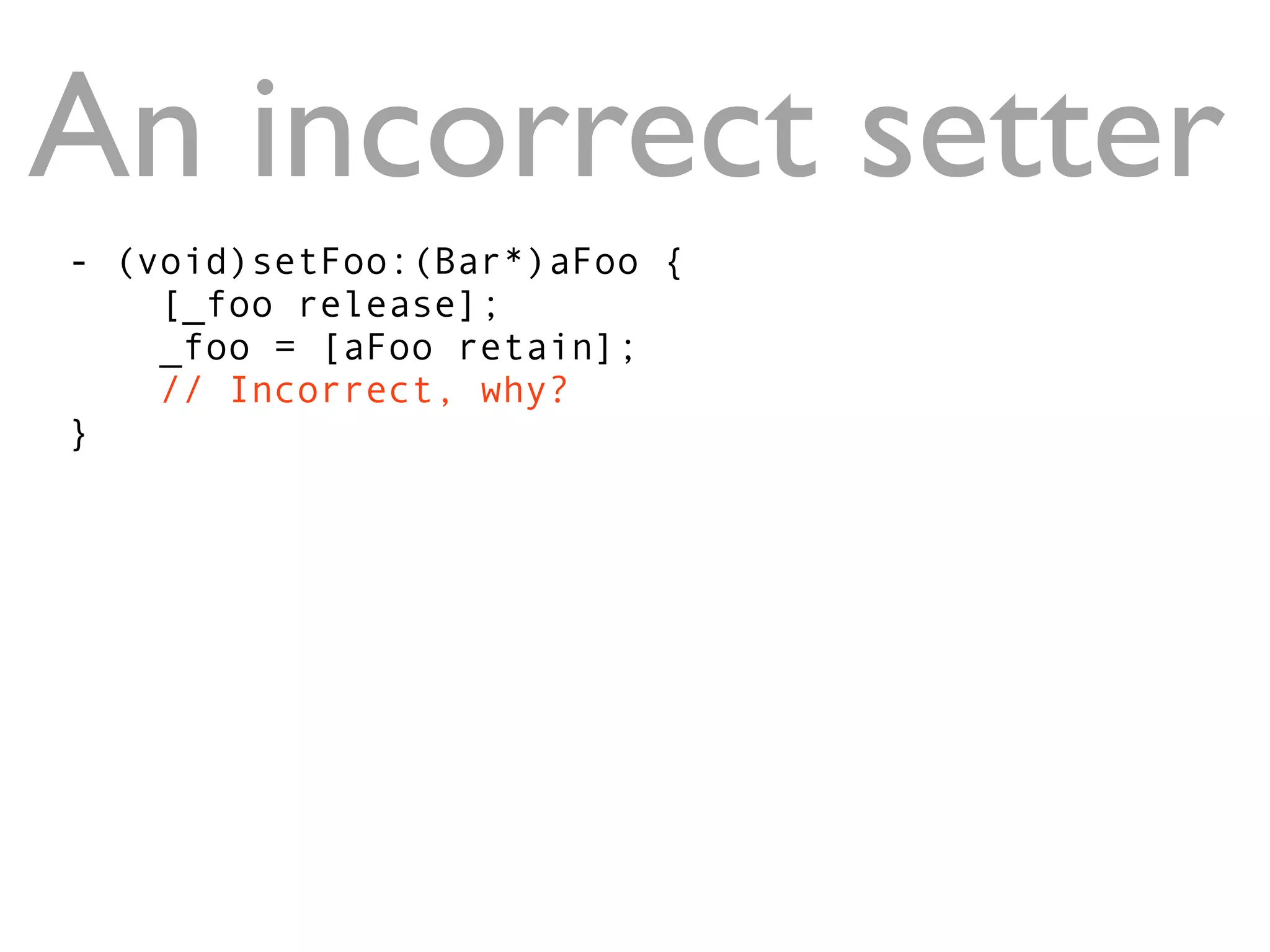
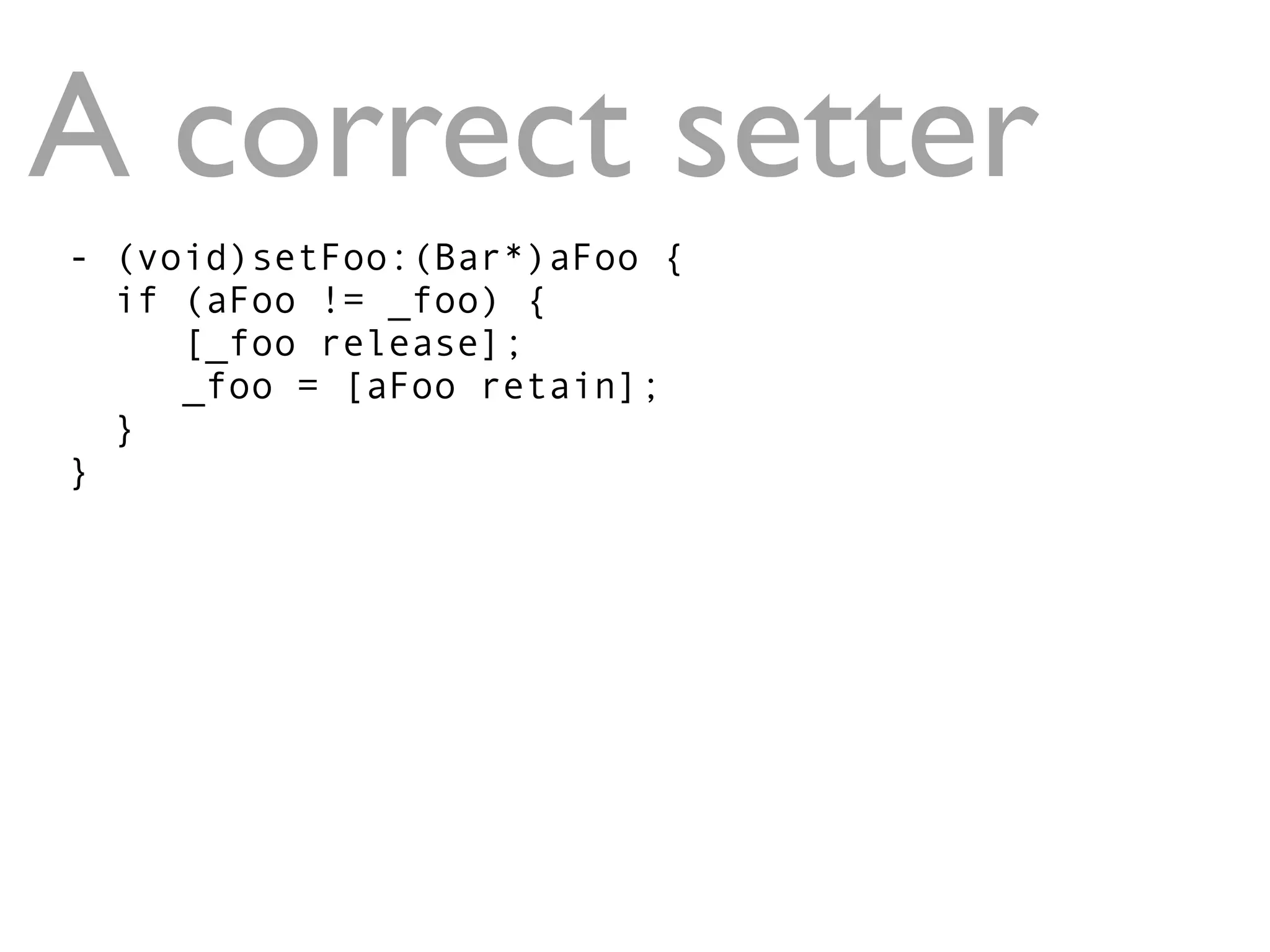
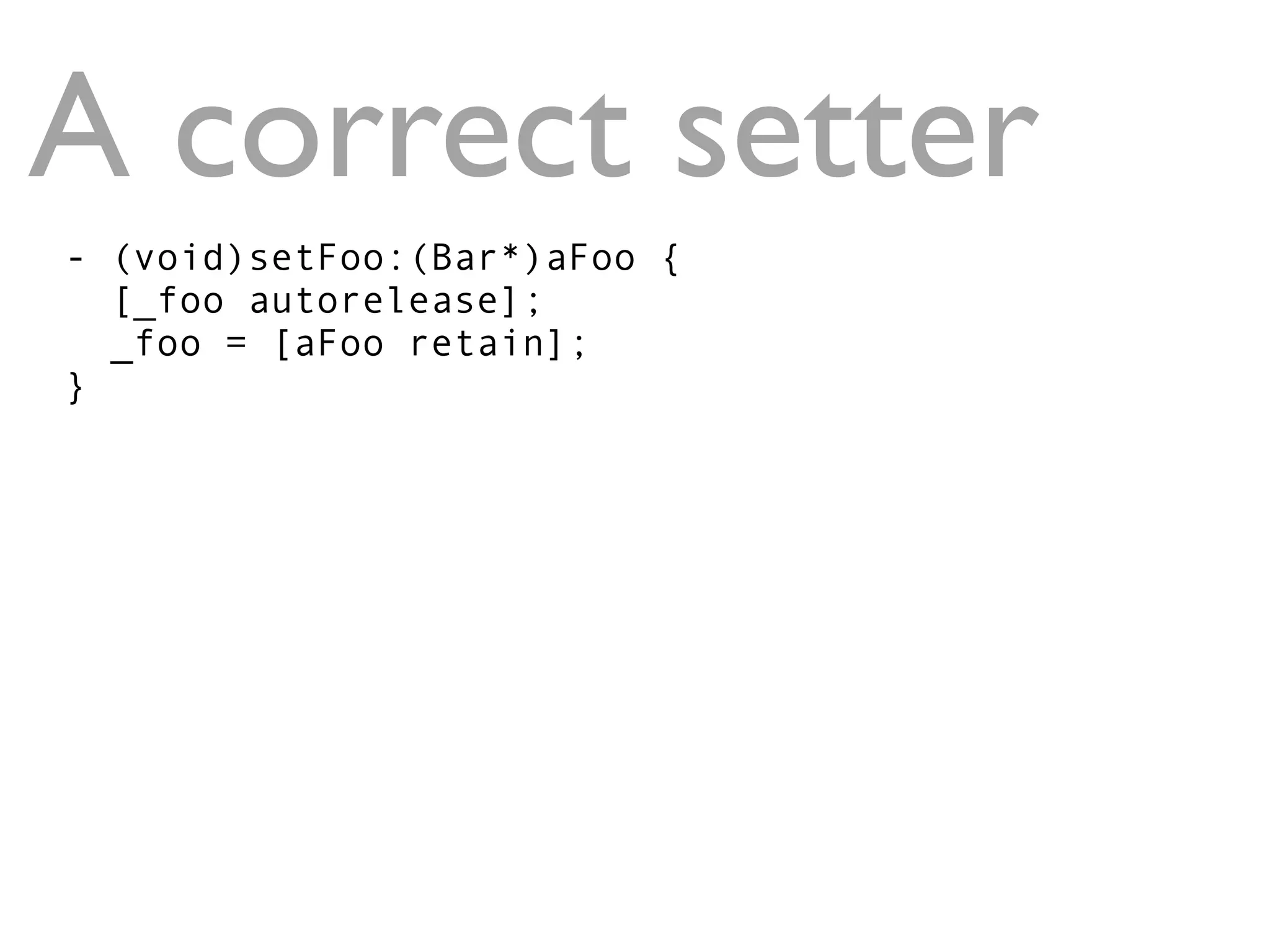
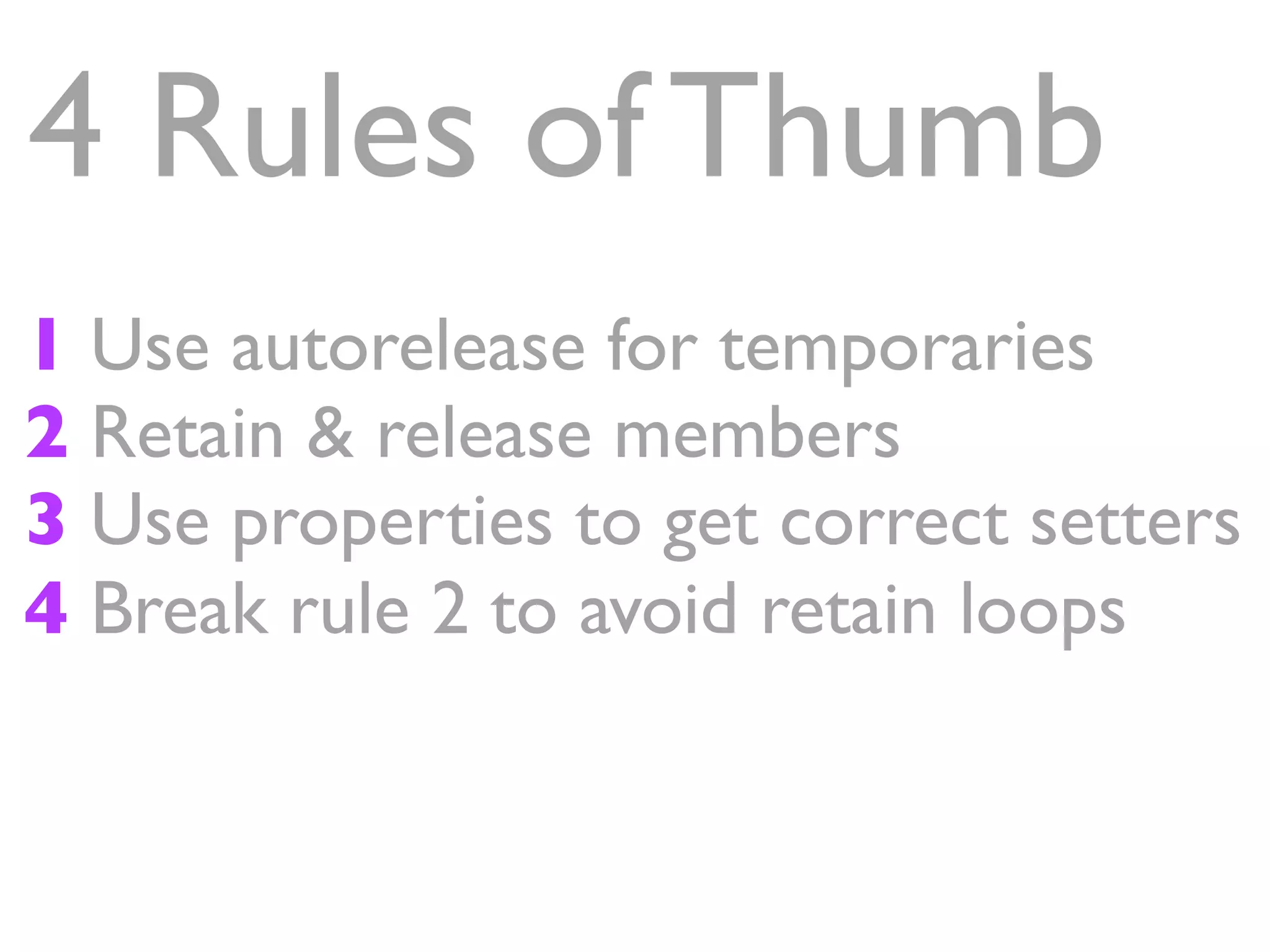
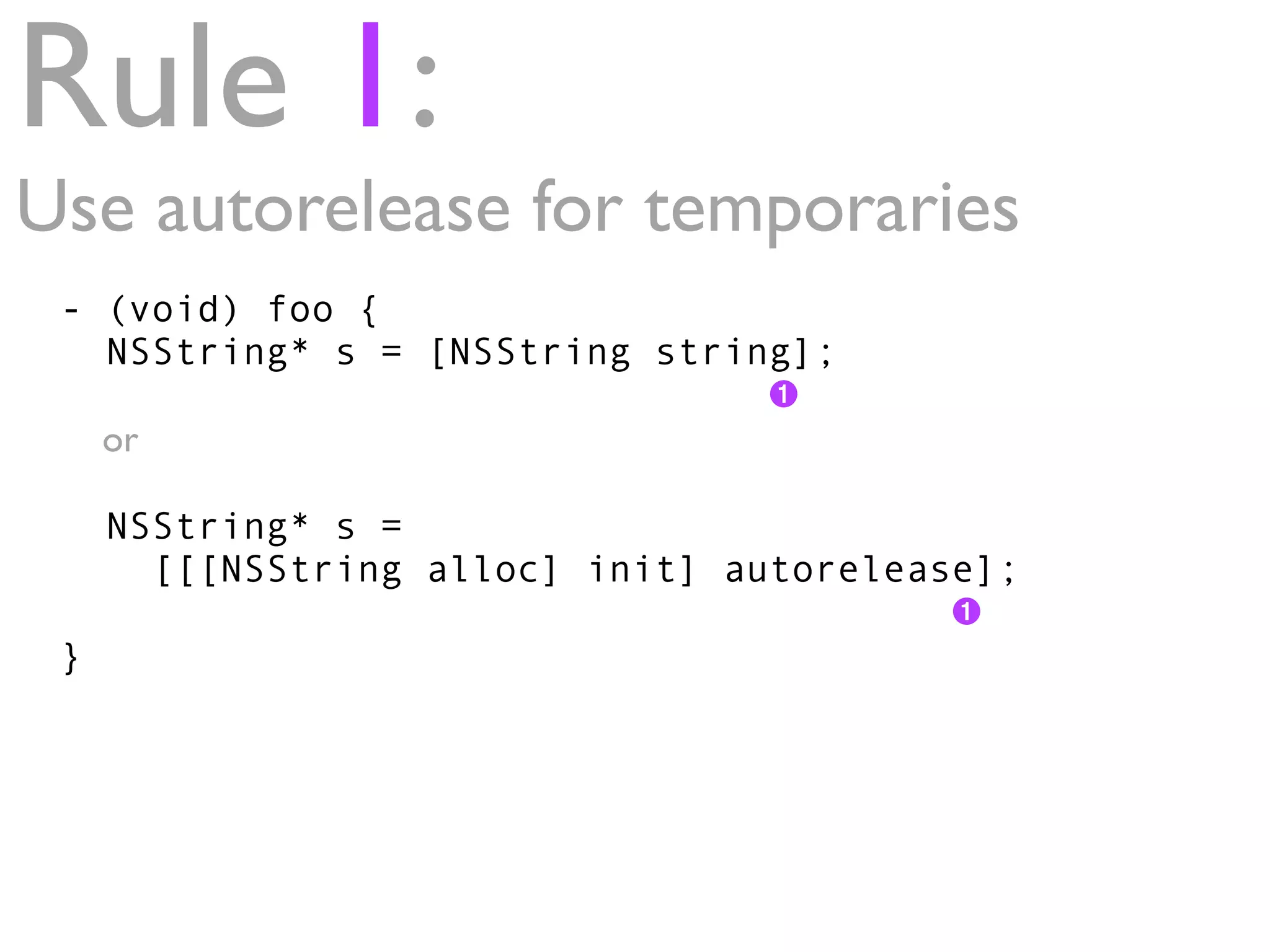
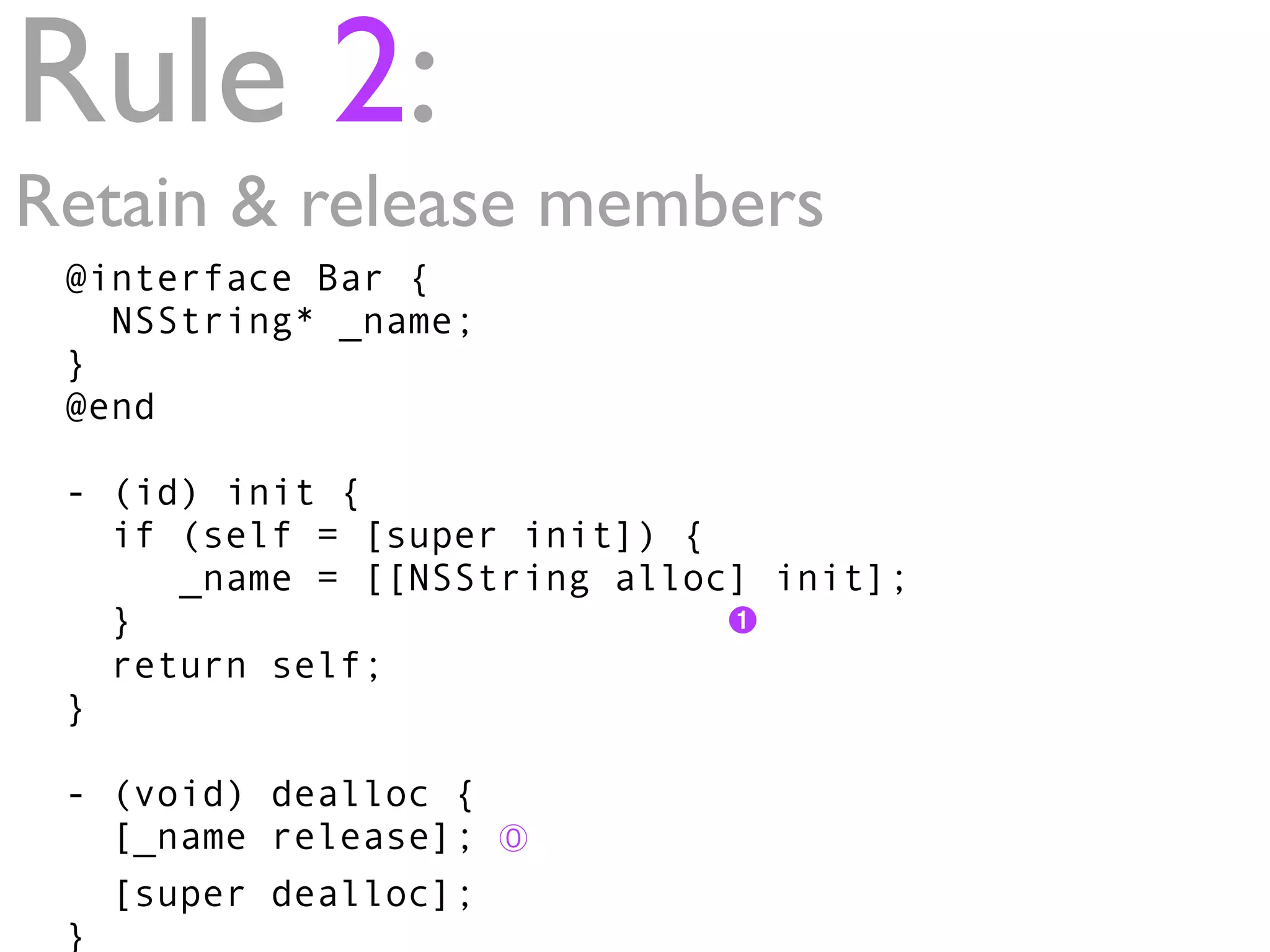
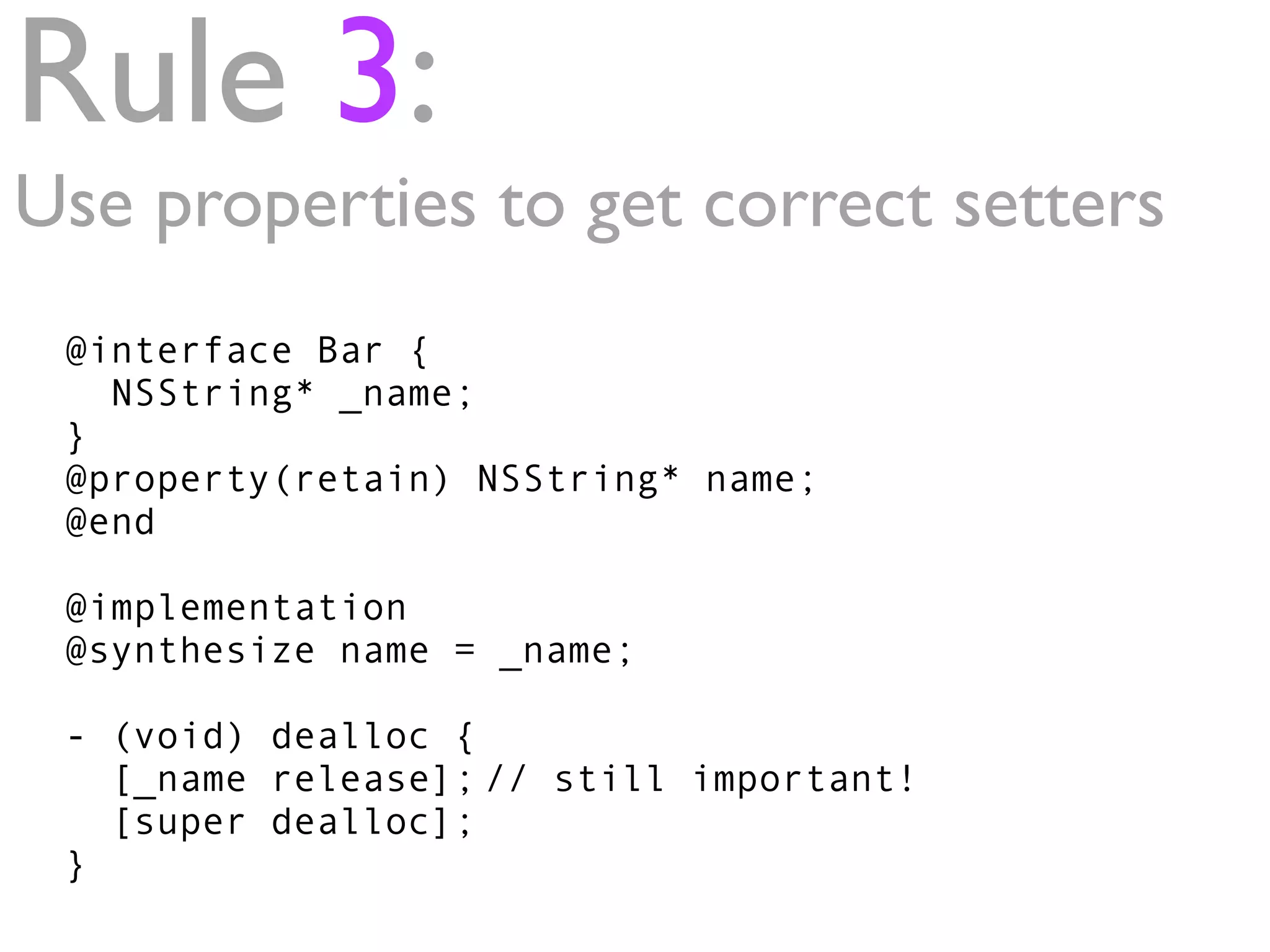
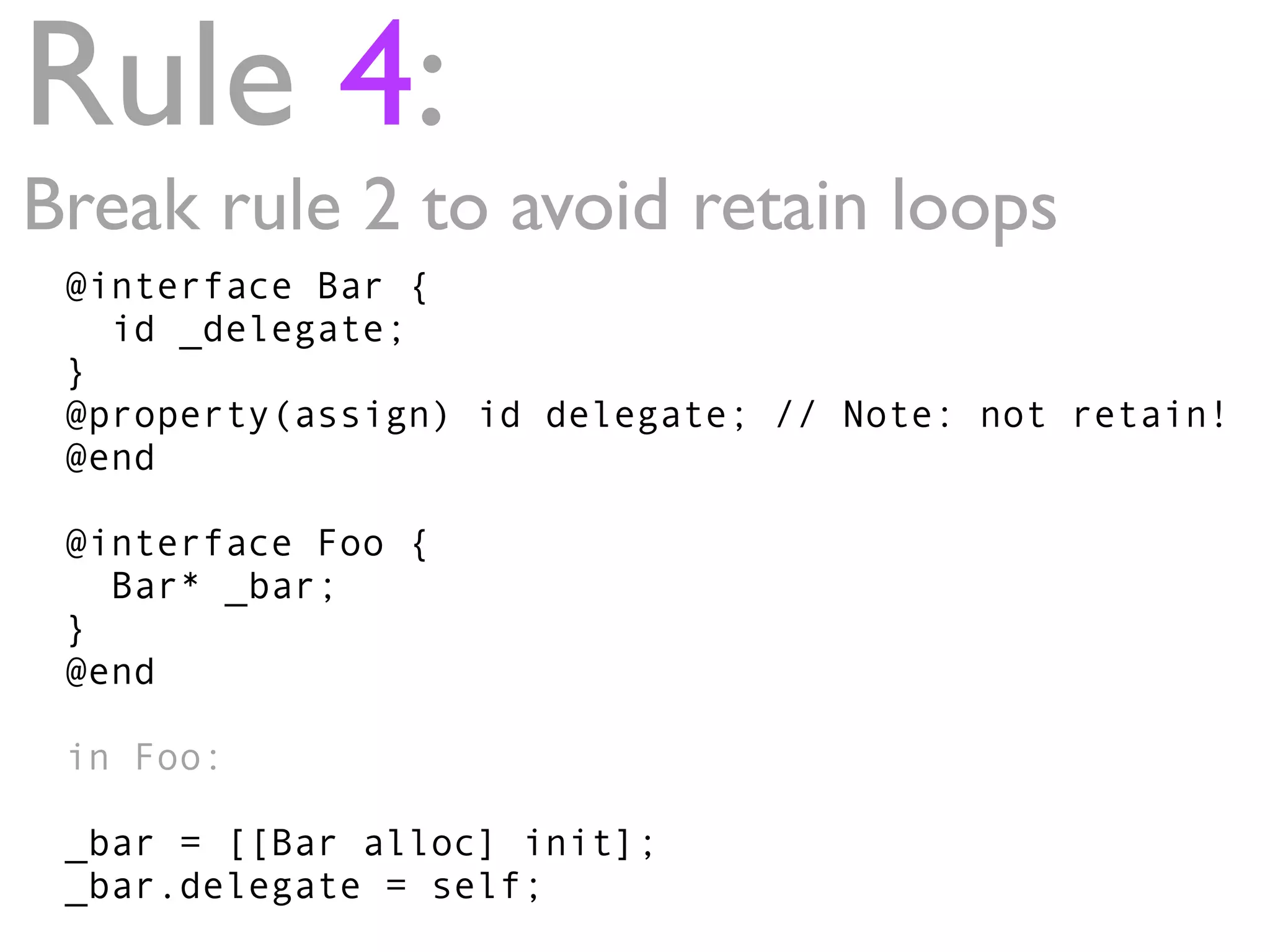
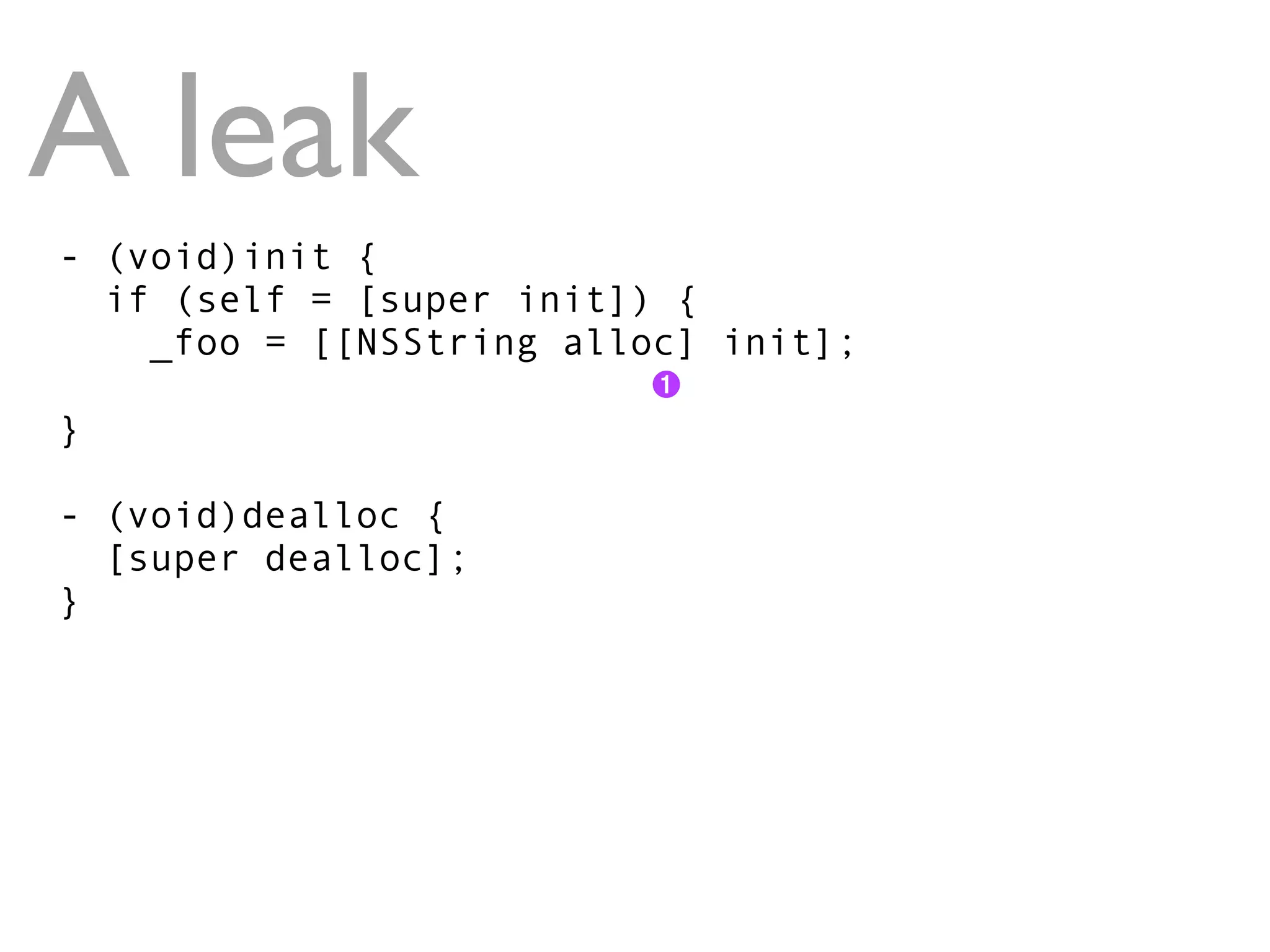
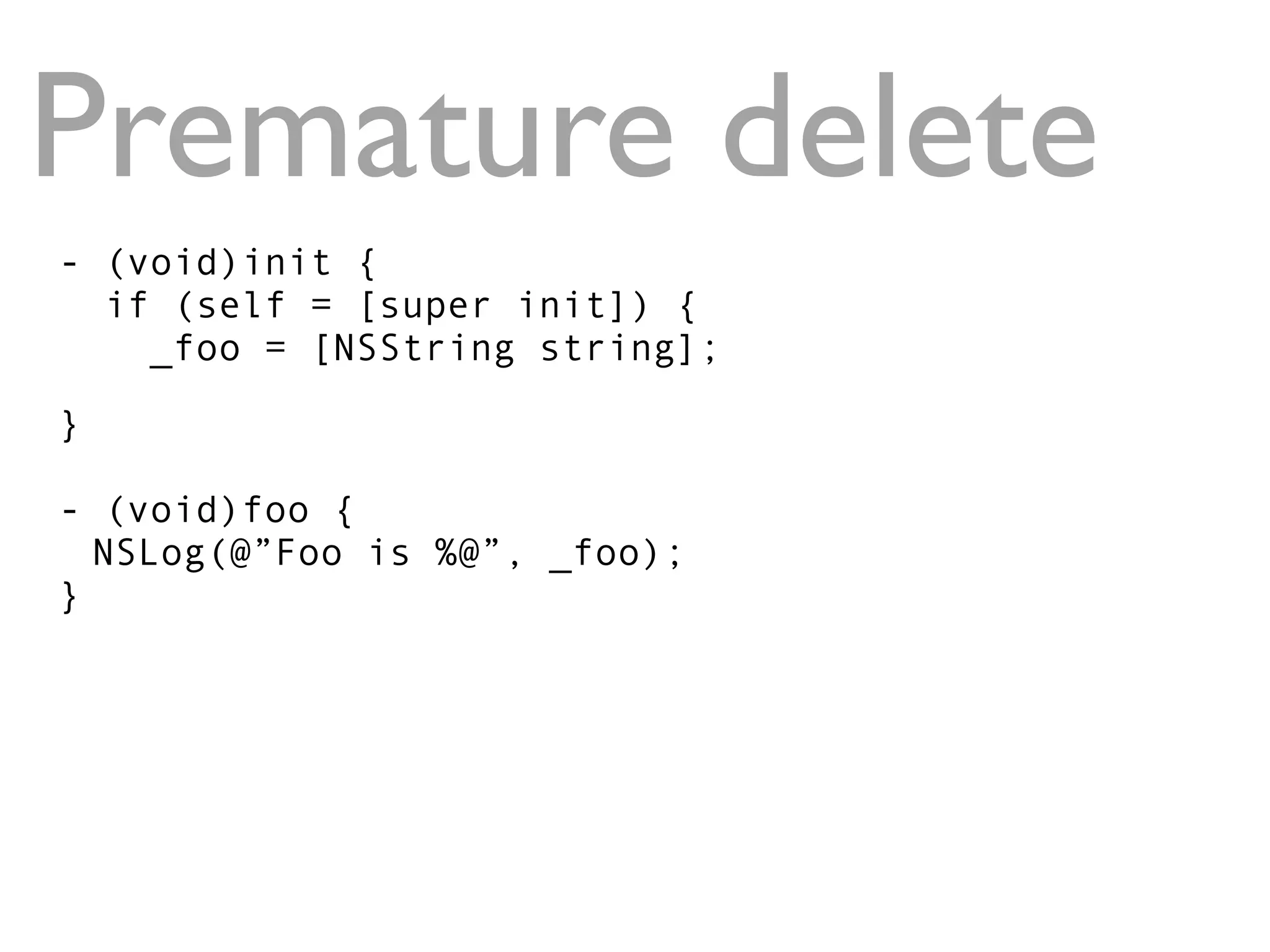
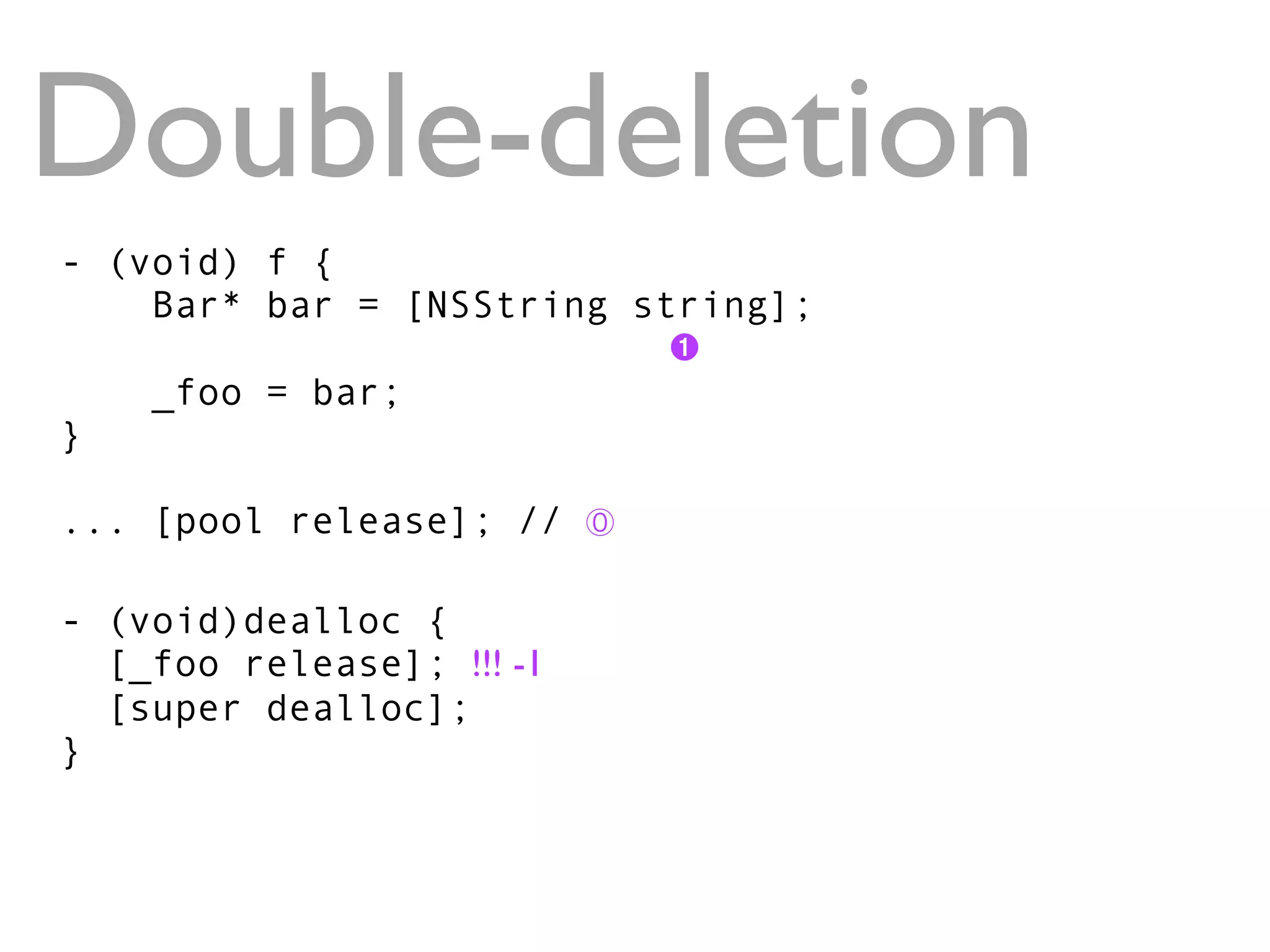
The document provides a quick introduction to iPhone memory management, highlighting key concepts such as object allocation, memory release, and best practices for using retain and autorelease methods. It outlines four main rules for memory management in Objective-C, including the use of properties for correct setters and strategies to avoid retain loops. Additionally, it discusses common memory management bugs and introduces the concept of using NSZombieEnabled to help debug memory issues.