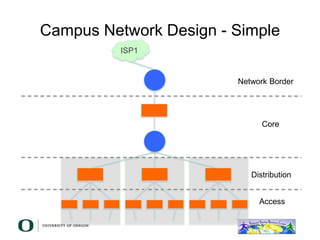
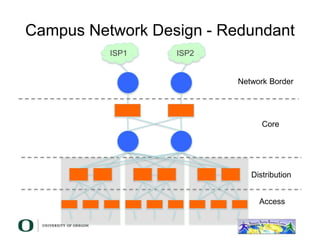
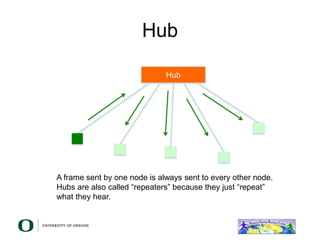
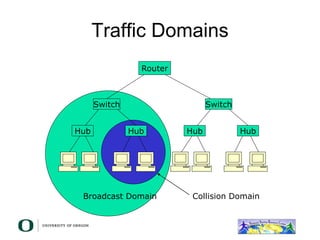
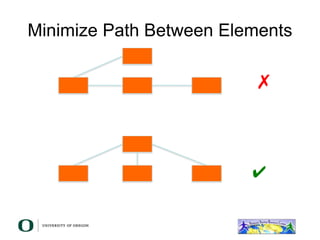
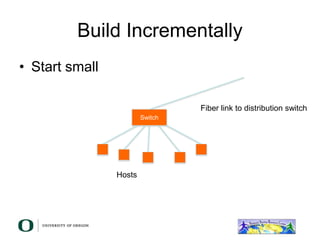
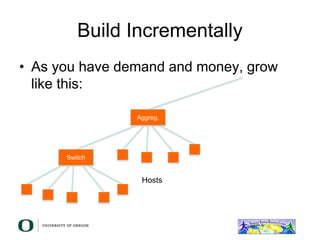
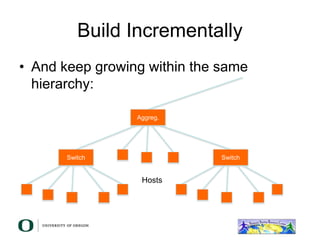
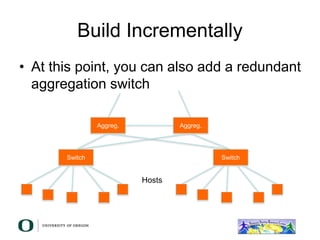
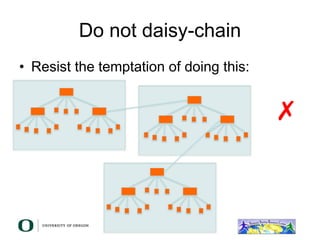
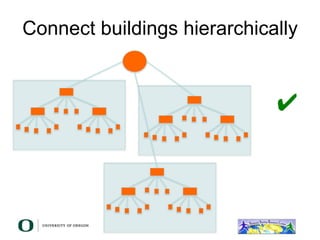
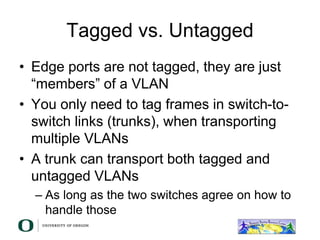
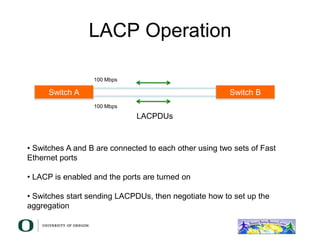
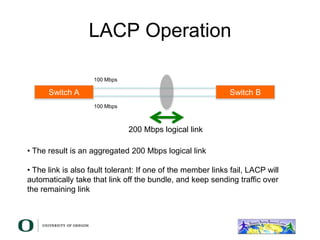
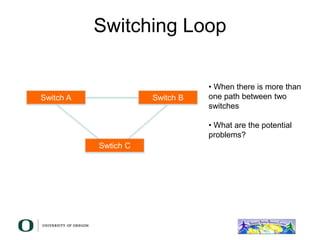
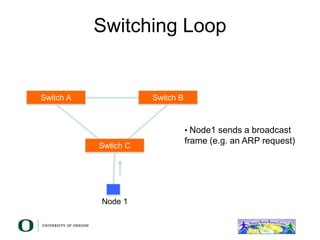
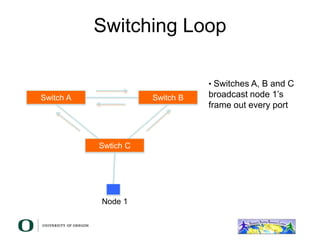
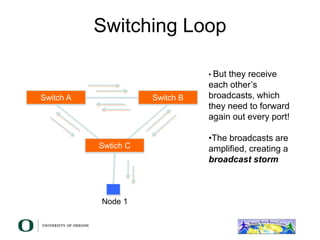
This document discusses layer 2 network design concepts. It recommends designing networks hierarchically with core, distribution, and access layers for modularity and scalability. Switches are preferred over hubs as they reduce collision domains. Routers further reduce broadcast domains. VLANs and link aggregation can increase network capacity and redundancy. Care must be taken to avoid switching loops which can cause broadcast storms. The guidelines emphasize building networks incrementally as needs grow.