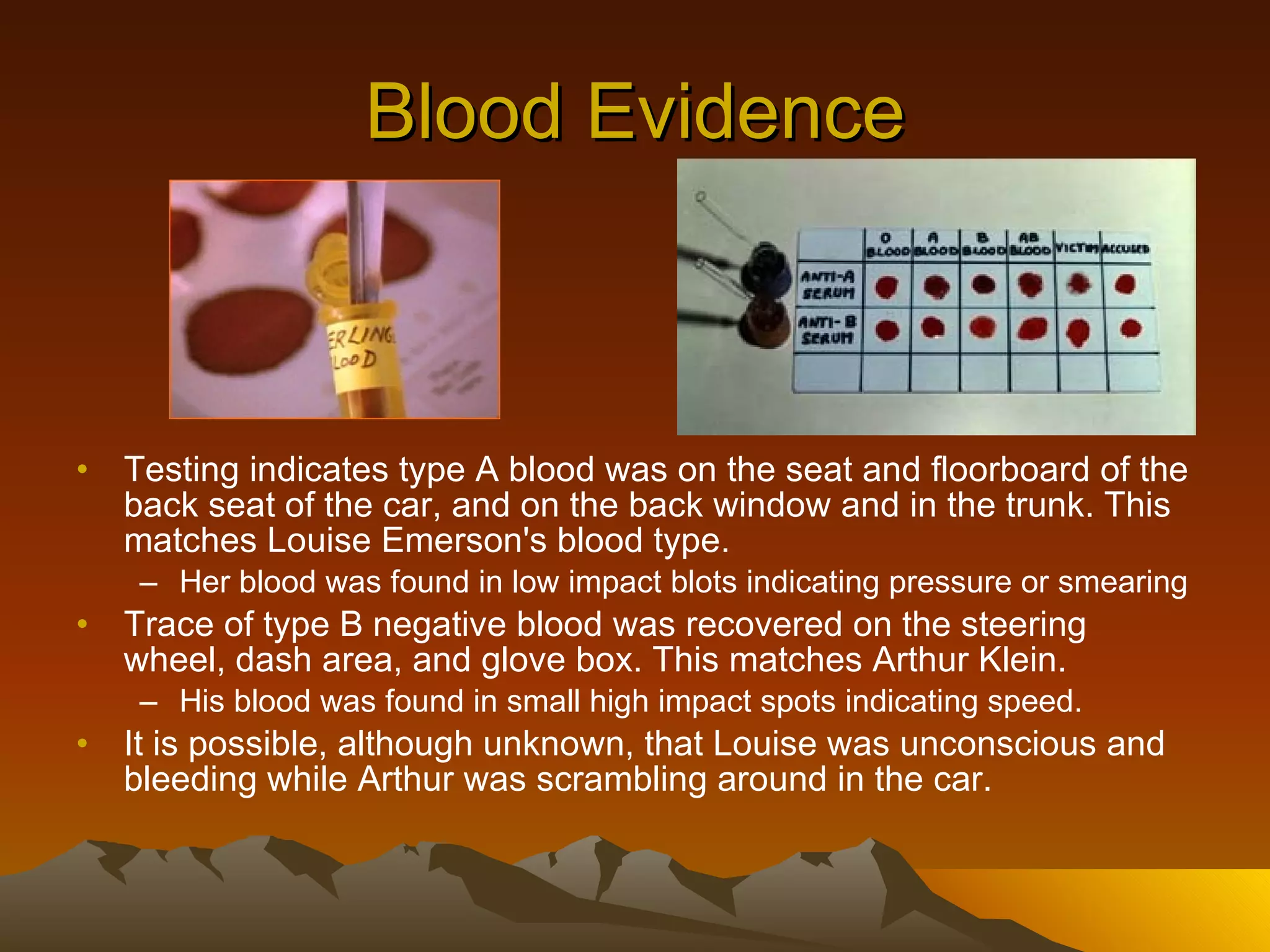
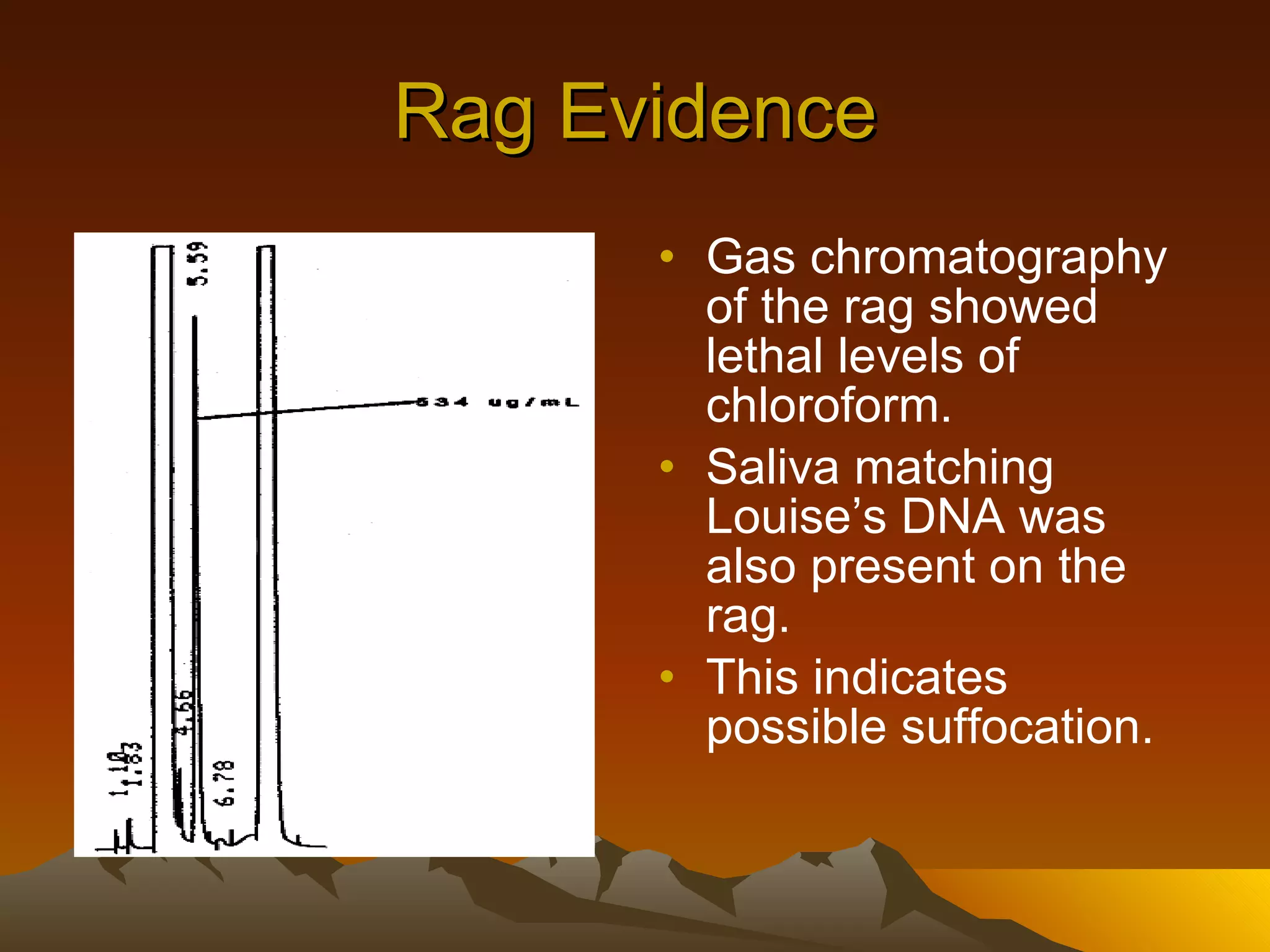
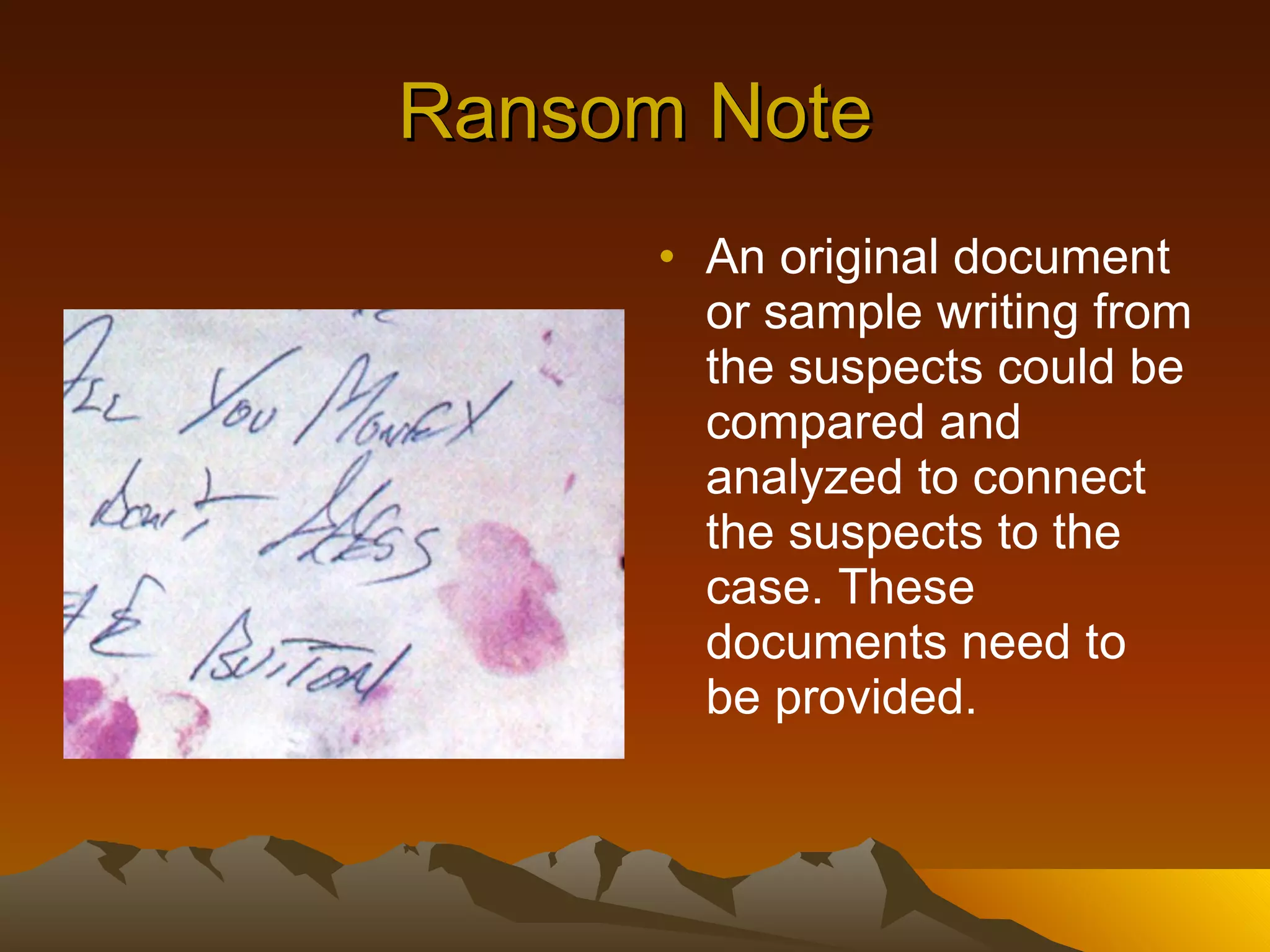
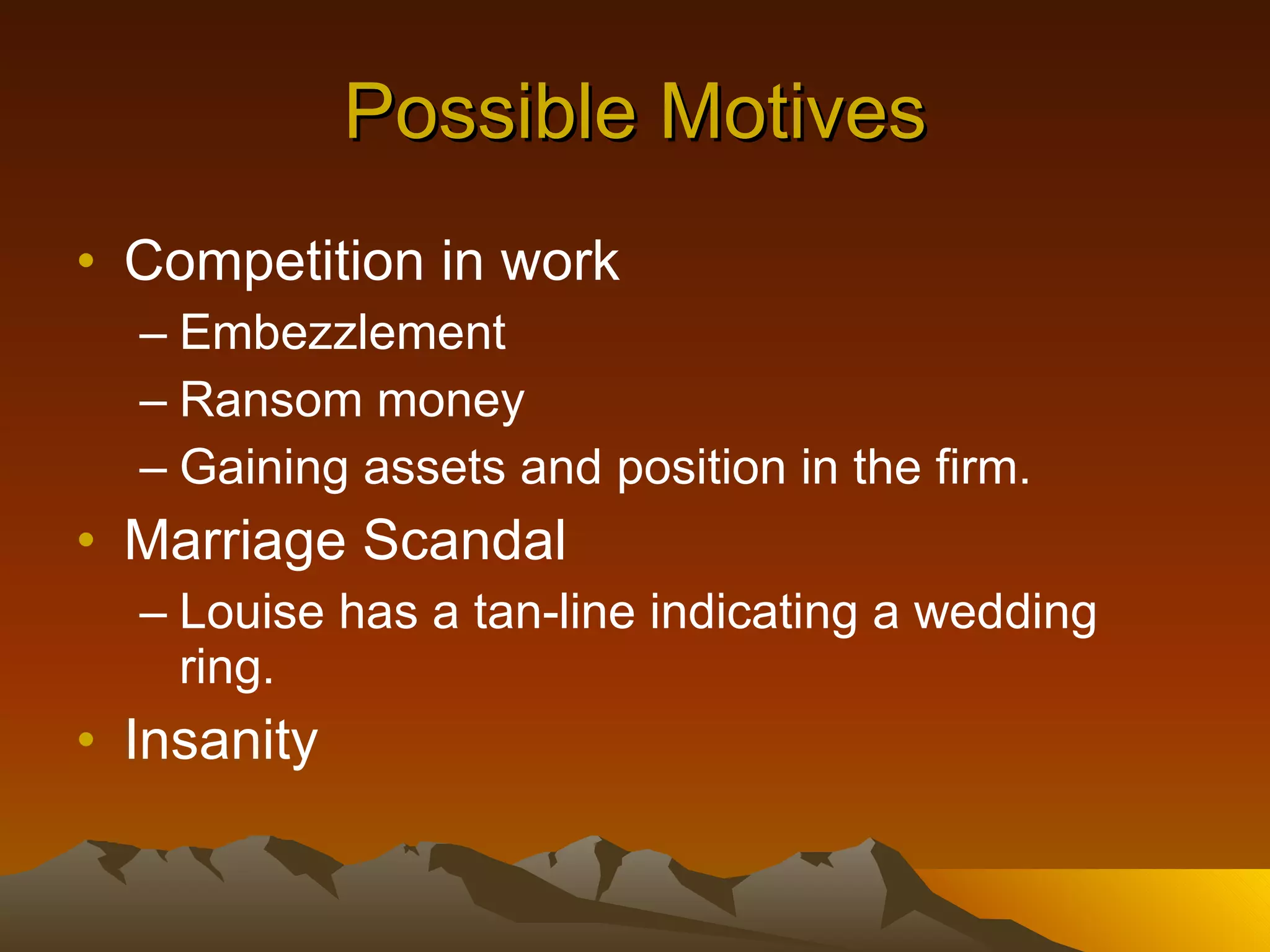
The document summarizes evidence from a kidnapping case involving Louise Emerson. DNA evidence from a rag and car matched Louise and one of the suspects. Blood evidence in the car also matched Louise and another suspect. Fingerprints in the car belonged to the owner, who is the brother of one of the suspects. Hair, soil, and fiber evidence also linked the suspects and Louise. A ransom note could provide a sample writing for comparison. Possible scenarios are that the brothers worked together to kidnap Louise for ransom money or to gain her position, and she may be dead or hidden at a nearby sawmill.