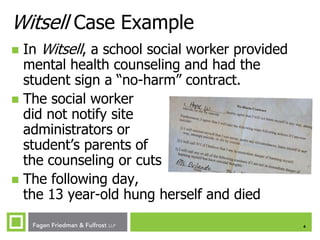
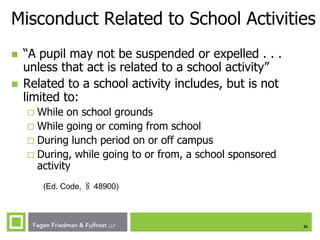
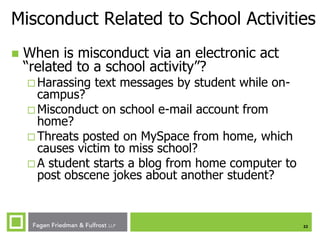
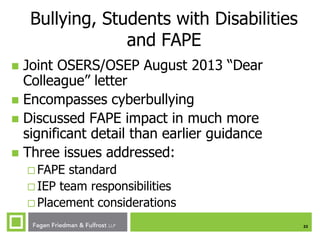
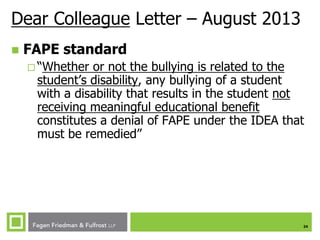
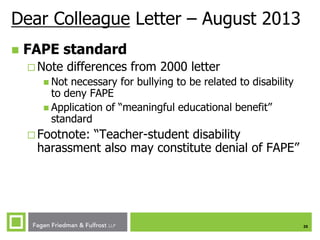
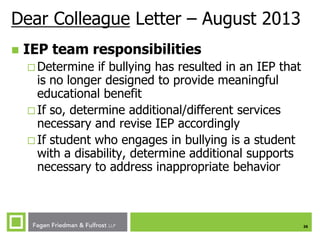
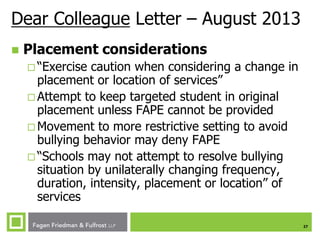
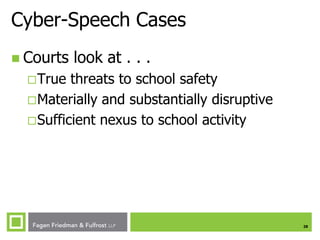
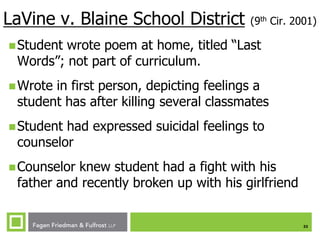
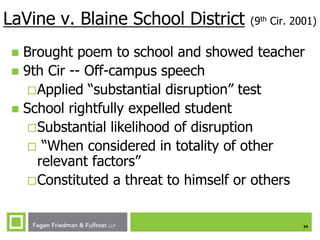
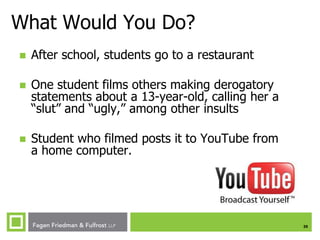
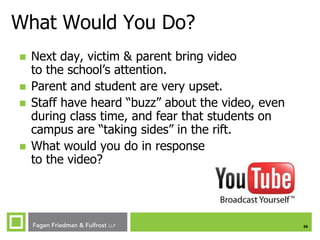
This document discusses several issues related to students and cyberspace including sexting, cell phone searches and seizures, bullying and cyberbullying, denial of services to students with disabilities, and disciplining students for cyber-speech. It provides examples of cases involving these issues and offers policy pointers for school districts to address these challenges in a legally compliant manner while protecting students.