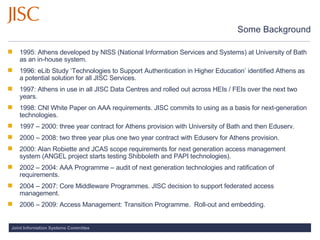
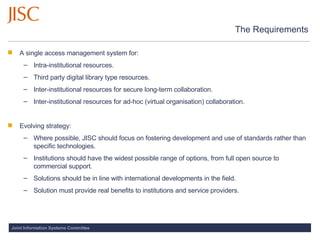
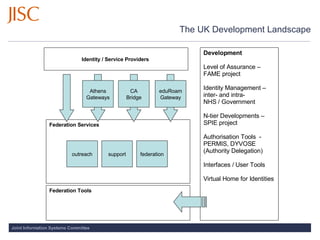
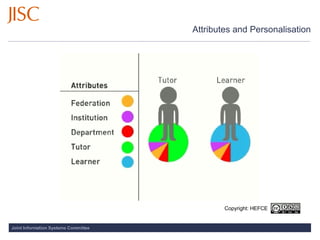
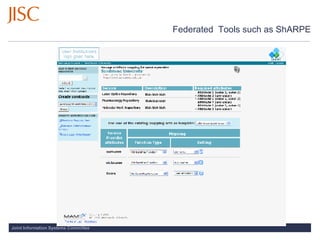
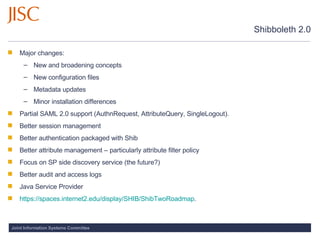
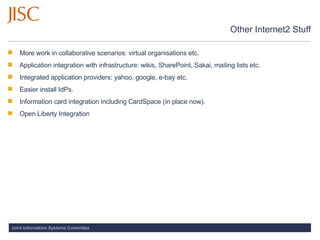
The document outlines the access management transition program led by Jisc, detailing the evolution of the Athens system for authentication in higher education from 1995 to various international collaborations and developments. It highlights the aims of creating a unified access management system for both intra- and inter-institutional resources and emphasizes the importance of standards over specific technologies. Additionally, it mentions ongoing projects, federated identity management, and international partnerships to enhance collaboration in digital resource access.