Jeff ballard resume_april_2016
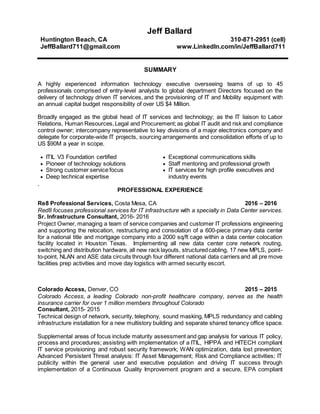
- 1. Jeff Ballard Huntington Beach, CA JeffBallard711@gmail.com 310-871-2951 (cell) www.LinkedIn.com/in/JeffBallard711 SUMMARY A highly experienced information technology executive overseeing teams of up to 45 professionals comprised of entry-level analysts to global department Directors focused on the delivery of technology driven IT services, and the provisioning of IT and Mobility equipment with an annual capital budget responsibility of over US $4 Million. Broadly engaged as the global head of IT services and technology; as the IT liaison to Labor Relations, Human Resources,Legal and Procurement;as global IT audit and risk and compliance control owner; intercompany representative to key divisions of a major electronics company and delegate for corporate-wide IT projects, sourcing arrangements and consolidation efforts of up to US $90M a year in scope. ITIL V3 Foundation certified Exceptional communications skills Pioneer of technology solutions Strong customer service focus Deep technical expertise Staff mentoring and professional growth IT services for high profile executives and industry events . PROFESSIONAL EXPERIENCE Re8 Professional Services, Costa Mesa, CA 2016 – 2016 Red8 focuses professional services for IT infrastructure with a specialty in Data Center services. Sr. Infrastructure Consultant, 2016- 2016 Project Owner, managing a team of service companies and customer IT professions engineering and supporting the relocation, restructuring and consolation of a 600-piece primary data center for a national title and mortgage company into a 2000 sq/ft cage within a data center colocation facility located in Houston Texas. Implementing all new data center core network routing, switching and distribution hardware, all new rack layouts, structuredcabling, 17 new MPLS, point- to-point, NLAN and ASE data circuits through four different national data carriers and all pre move facilities prep activities and move day logistics with armed security escort. Colorado Access, Denver, CO 2015 – 2015 Colorado Access, a leading Colorado non-profit healthcare company, serves as the health insurance carrier for over 1 million members throughout Colorado Consultant, 2015- 2015 Technical design of network, security, telephony, sound masking, MPLS redundancy and cabling infrastructure installation for a new multistory building and separate shared tenancy office space. Supplemental areas of focus include maturity assessment and gap analysis for various IT policy, process and procedures; assisting with implementation of a ITIL, HIPPA and HITECH compliant IT service provisioning and robust security framework; WAN optimization, data lost prevention; Advanced Persistent Threat analysis: IT Asset Management; Risk and Compliance activities; IT publicity within the general user and executive population and driving IT success through implementation of a Continuous Quality Improvement program and a secure, EPA compliant
- 2. Jeff Ballard Page 2 lifecycle management process for all technology and devices. SDI Media, Culver City, CA 2014 – 2014 SDI Media is the largest language localization (media translation) provider in the world, servicing over 40 markets in 37 countries across the globe. Consultant, 2014- 2014 Lent expertise to the SDI Media CIO on high-level technology planning and problem solving with a focus on the growth and mentoring of senior IT leadership. Identified specific cross-training opportunities for extended utilization of limited resources and to insulate the potential business impact at the loss of key IT personnel. ShowMgr.com, Rancho Santa Margarita, CA 2014 - 2014 ShowMgr.com is the leading cloud-based ERP software provider for media and content creators, allowing for the seamless managementof resources,film and television crews and media creation accounting, scheduling and budgeting. Vice President, IT Operations, 2014- 2014 Responsible for IT security, standards, policies and procedures; risk and compliance and the architectural evolution and maturity of ShowMgr's technical IT services. Recommended the consolidation of webhead, SQL and transactional servers into fewer but more robust hosting platforms saving over $18k/mo in expense with increased responsiveness and reliability for the ShowMgr solution. Conducted security baseline and gap analysis, recommending changes to a wide range of internal processes resulting in a significantly reduced threat footprint. Drafted plans for business continuity, disaster recovery and emergency notification processes, and various internal company policies related to acceptable use, network access, two-factor authentication and development code release processes, greatly enhancing internal process maturity. Sony Pictures Entertainment, Culver City, CA 2002 - 2014 A US-based, $30B division of Sony Corporation, Sony Pictures is one of the largest and most successfulmoviestudios in Hollywood and the single largest international TV station owner in the world. Executive Director, Global Head, IT Support Services Lead a group of 45 technicians and 27 offshore analysts and managed 4 Directors and 2 Managers compromising the Global IT Help Desk, US and UK Desktop Support, IT Asset Management, Mobile Technology and Advanced Client Technology groups. Lead the on-site technical support team providing IT, mobility, multimedia and talent technical setup and support to the Summer of Sony (2011, 2012, 1013), the largest private film junket in the world, hosting press conferences, talent interviews and pre-release screenings to over 300 of the world’s most influential news media guests, in Cancun, Mexico. Saved over $40,000 in satellite truck expense per event by working with Publicity and International Marketing to create the studio’s first internet-based interactive media service allowing remote talent real-time interaction with intimate to large format multi-camera media and press Q&A sessions throughout North America, Latin America, Asia Pacific, the UK and Europe. Improved budgetary compliance through management of (10) capital pools representing US
- 3. Jeff Ballard Page 3 $3M- $4M, resulting in annual variance reduction from 12-15% to less than 0.3 % over 8 straight years, despite mid-year reductions exceeding 30% of total. Established a global desktop engineering taskforce addressing the Windows XP remediation through a (3) year plan of strategic asset deployment and repurposing resulting in over 98% of Sony Pictures 8,000 desktop assets converted to Windows 7 by April 1, 2014. Lead the Desktop Support group to Winner, Best Service Excellence award for Sony Pictures IT, 2012 and 2013. Oversaw the partial outsourcing of (11) help desk analysts by establishing level 1 and new level 1.5 IT services with Tata Consulting Services (TCS), Chennai, India, saving Sony Pictures over US $1M annually while introducing self-service options for password reset, instant message chat and FAQ documents into the first-ever 24x7x365 live, multilingual IT help desk for Sony Pictures. Reduced IT capital expenses by working with Sony’s Imageworks, Animation, PlayStation and Electronics groups to consolidate IT purchasing and the renegotiation of newly combined desktop and software maintenance contracts. EDUCATION / TRAINING B.S. Information Technology, Information Systems University of Redlands, Redlands, CA Pink Elephant and Loyalist Certification Services, Culver City, CA ITIL V3 Certification # 86819 CIO Pathways Leadership Program Focus on IT Strategy, Change Leadership and People Development