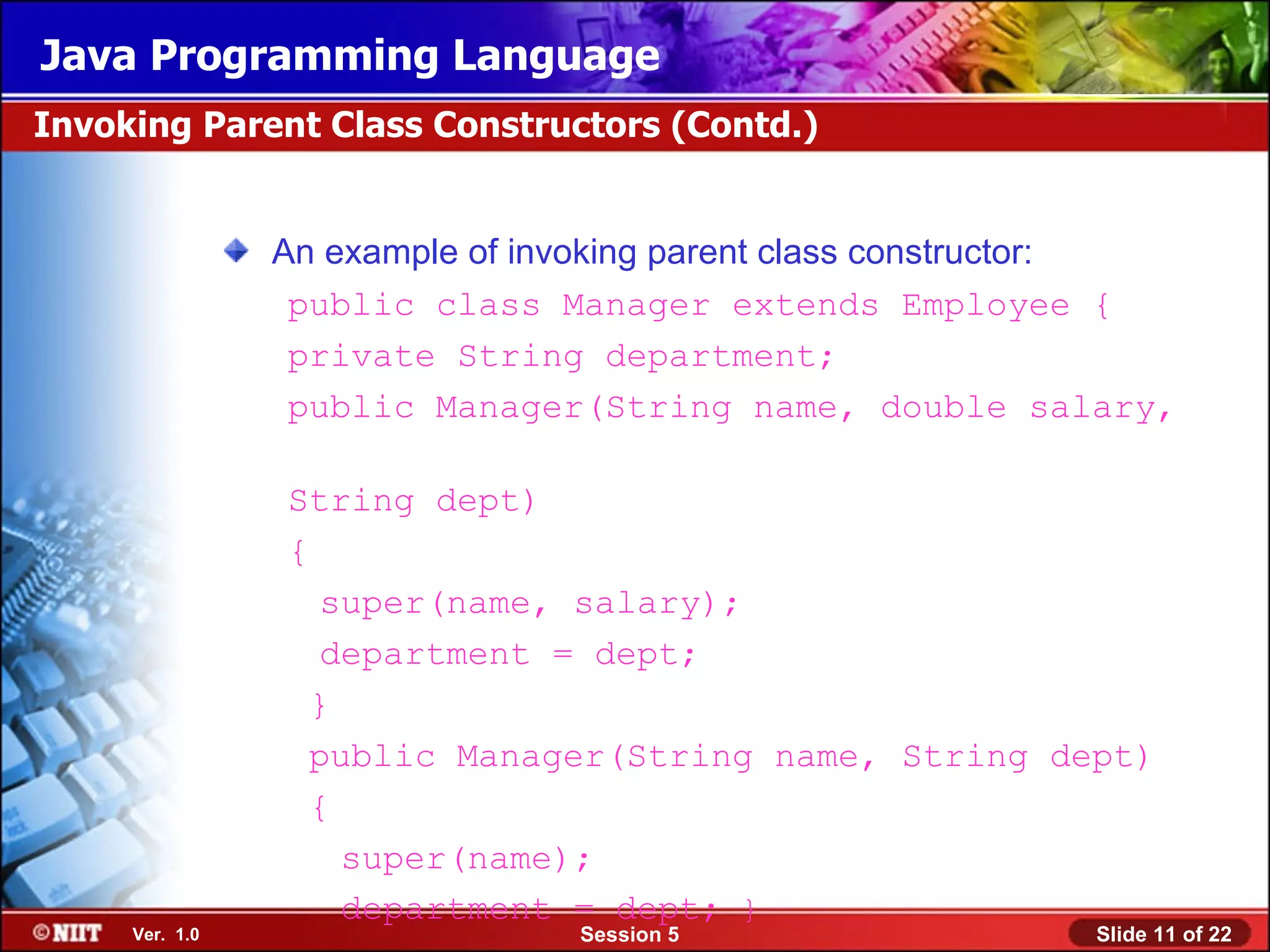
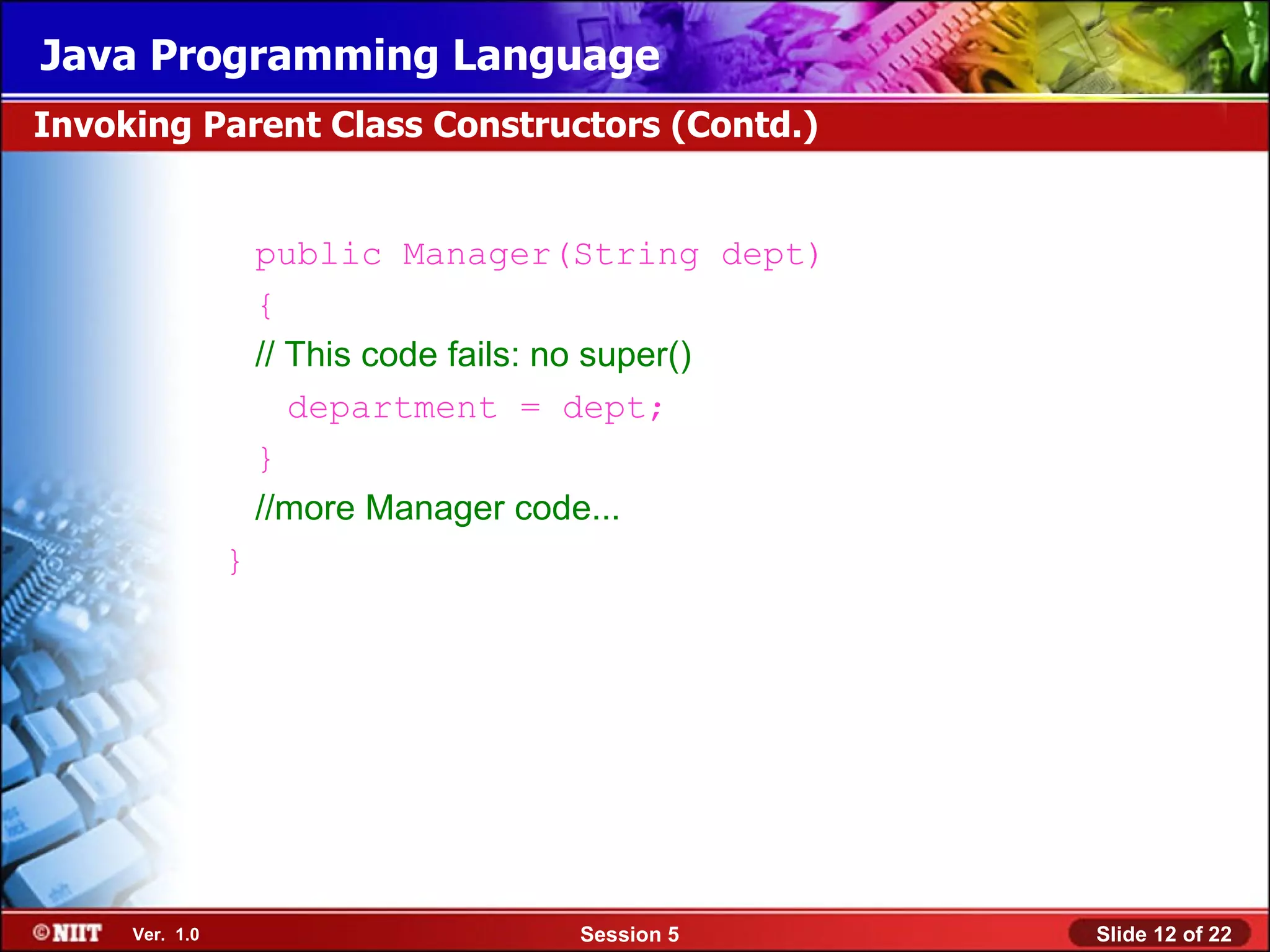
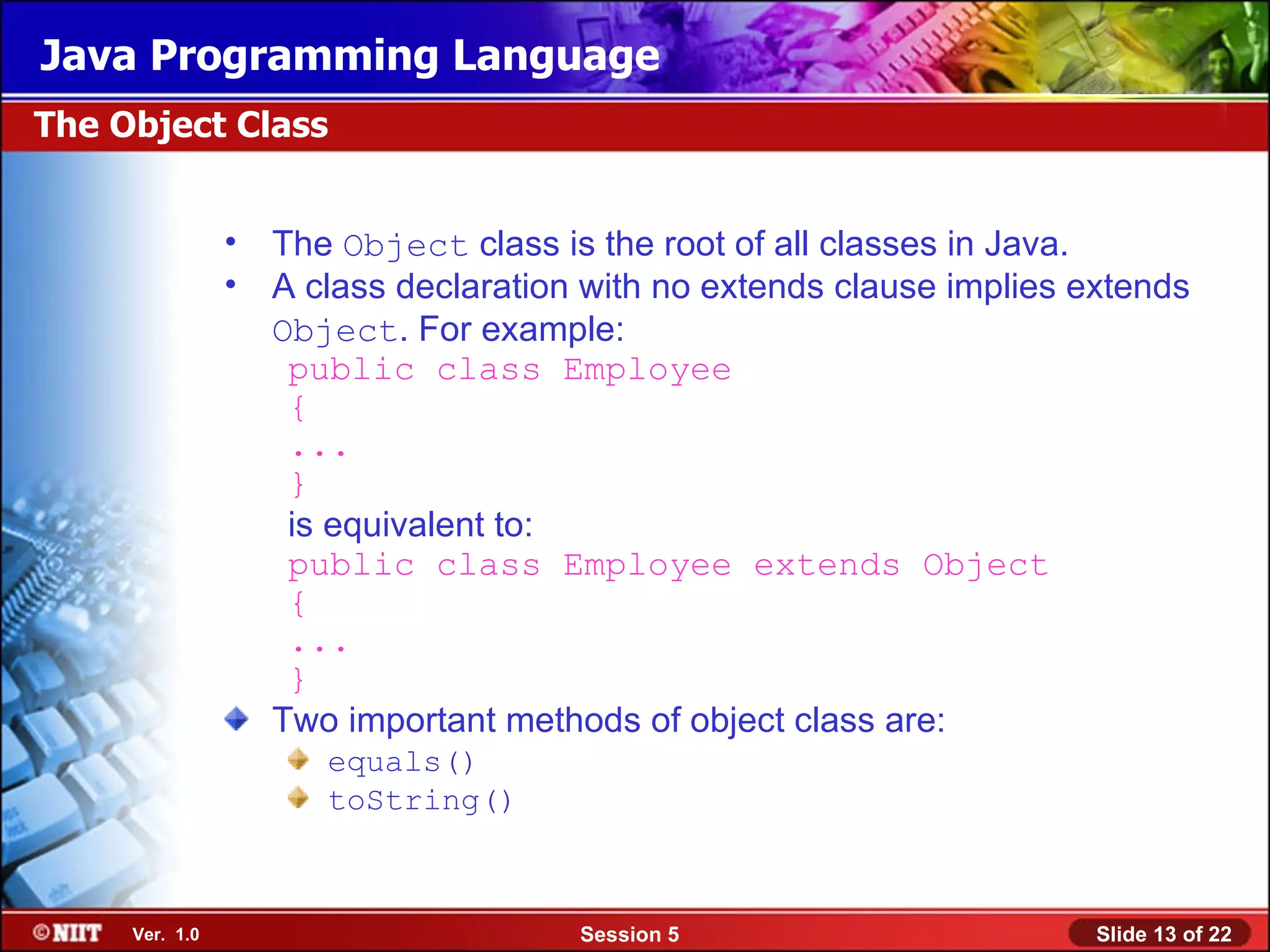
This document provides an overview of key Java programming concepts including casting objects, overloading methods and constructors, wrapper classes, autoboxing, and using static variables and methods. Specifically, it discusses casting objects to access subclass functionality, defining methods with the same name but different parameters, using variable arguments, invoking parent class constructors, the equals() and toString() methods of the Object class, boxing and unboxing primitive types, and declaring static class members.
![Java Programming Language
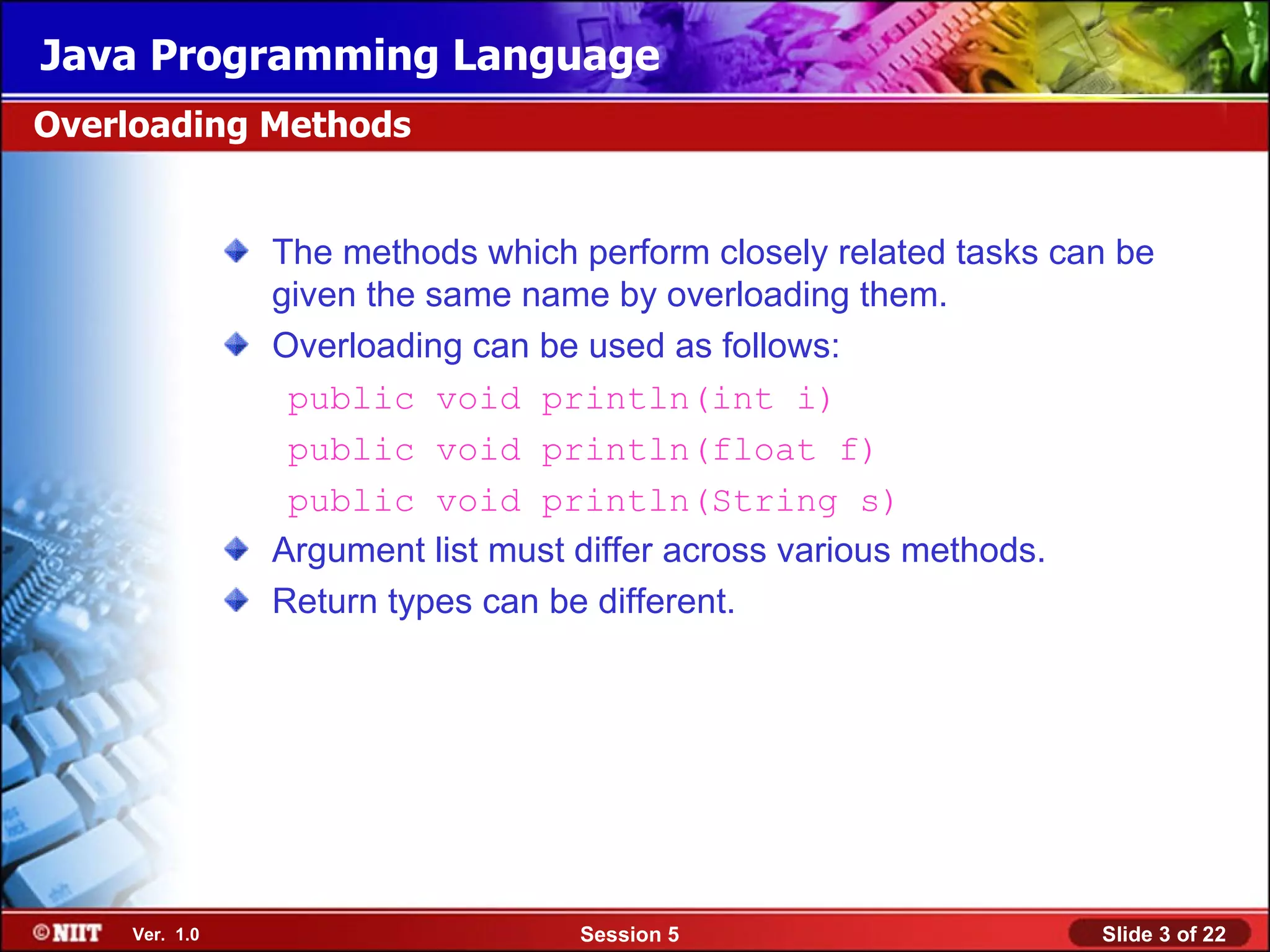
Methods Using Variable Arguments (Contd.)
• The following example demonstrates the usage of
varargs:
public class Statistics {
public float average(int... nums) {
int sum = 0;
for ( int x : nums ) { nums is an array
of type int[]
sum += x;
}
return ((float) sum) / nums.length;
}
}
We can invoke the average method by passing any number
of arguments as integers.
Ver. 1.0 Session 5 Slide 5 of 22](https://image.slidesharecdn.com/javasession05-120423054252-phpapp01/75/Java-session05-5-2048.jpg)