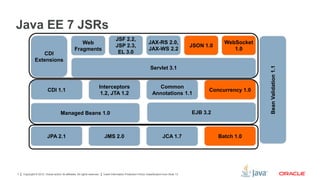
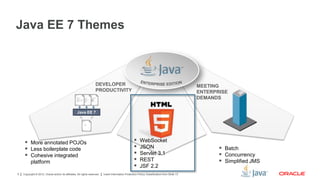
This document outlines a presentation on the new features in Java EE 7. It includes an agenda that covers an introduction to Java EE 7 and hands-on activities. The presentation discusses themes of Java EE 7 like improved developer productivity and meeting enterprise demands. It provides an overview of the Java EE 7 specifications and technologies covered, like JSON, WebSocket, JSF 2.2 and REST. The document concludes by describing hands-on activities using GlassFish 4, NetBeans IDE and the Oracle Learning Library for additional Java EE 7 tutorials.



![Copyright © 2012, Oracle and/or its affiliates. All rights reserved. Insert Information Protection Policy Classification from Slide 136
Java EE 7 / HTML5
WebSocket
WebSocketJSON
JSON-P
{a:”a”,
[1,2,3]
}](https://image.slidesharecdn.com/javaee7newfeaturespulsoconf2013-130917102200-phpapp02/85/Java-EE-7-PulsoConf-2013-6-320.jpg)