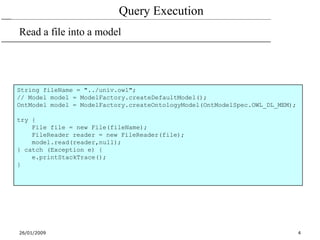
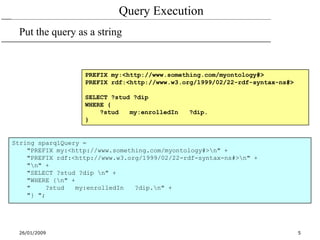
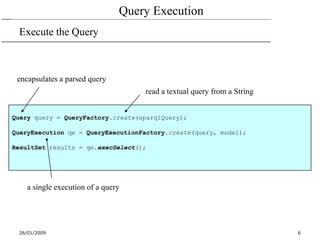
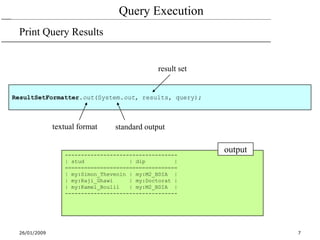
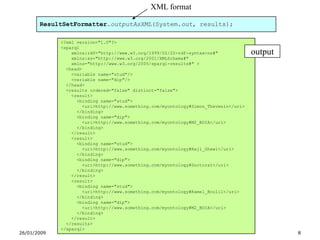
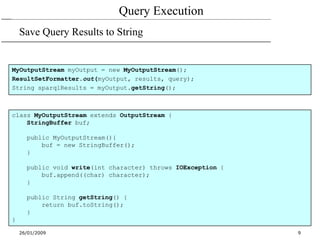
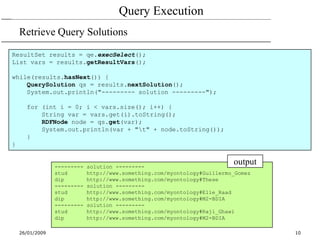
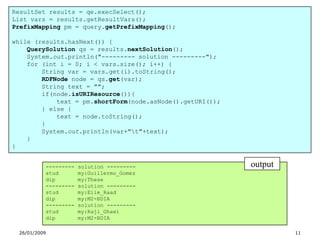
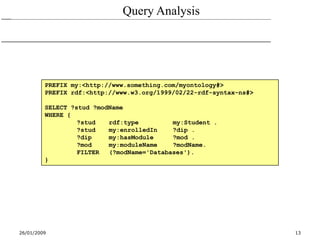
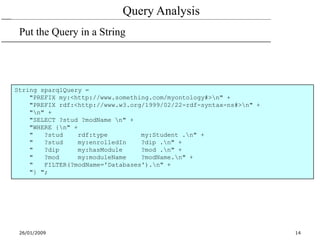
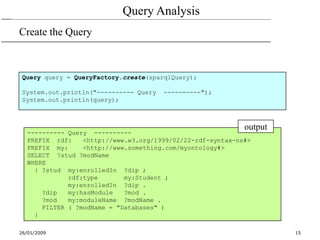
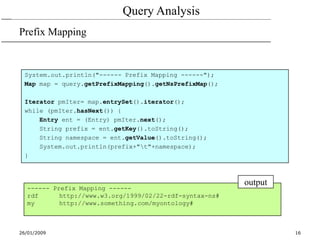
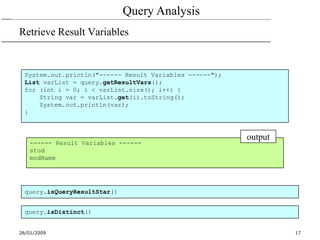
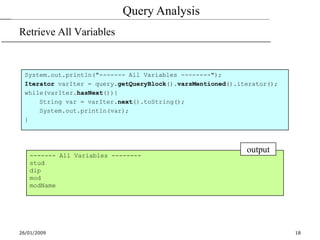
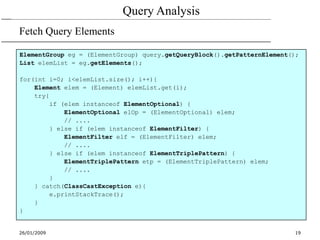
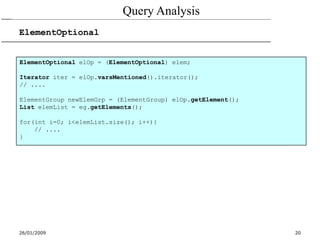
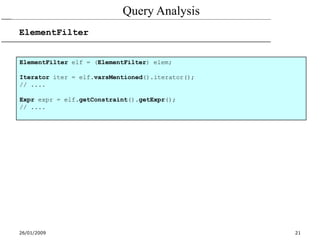
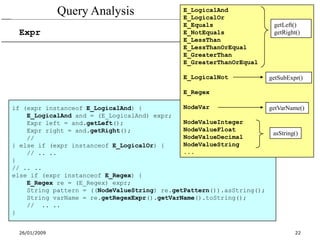
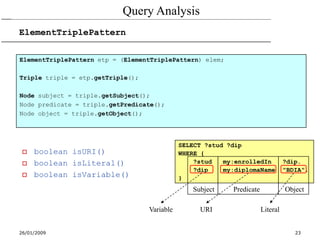
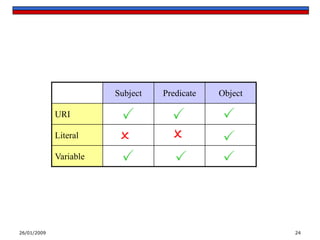
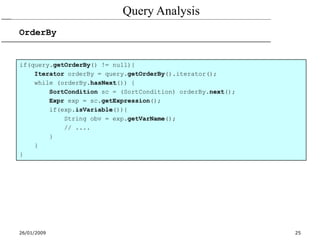
This document discusses processing SPARQL queries using Java with ARQ. It demonstrates how to execute a SPARQL query on an ontology model, print the results, and analyze various aspects of the query such as retrieving result variables, analyzing query elements like triple patterns, and examining the prefix mappings and expressions. The document provides an overview of executing SPARQL queries programmatically using the ARQ processor for Jena.