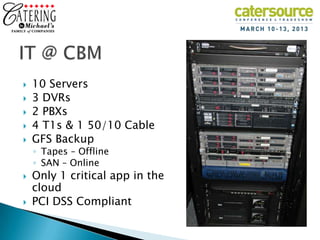
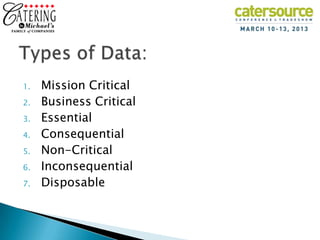
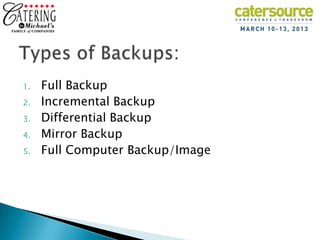
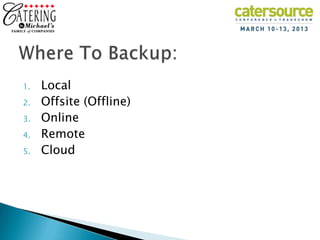
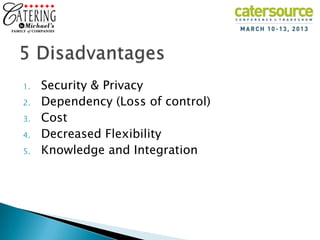
Jeff Ware gave a presentation on IT strategies for Catering By Michaels, a catering company founded in 1980. He discussed how the company uses IT for communication, transactions, research, marketing, and operations. He emphasized the importance of data management, connectivity, and regular backups using both online and offline methods. The company's IT infrastructure includes servers, DVRs, PBXs, internet connections, and a backup storage area network. Only one non-critical application is hosted in the cloud due to concerns about security, costs, and loss of control. Ware also discussed the company's PCI compliance standards.