Embed presentation
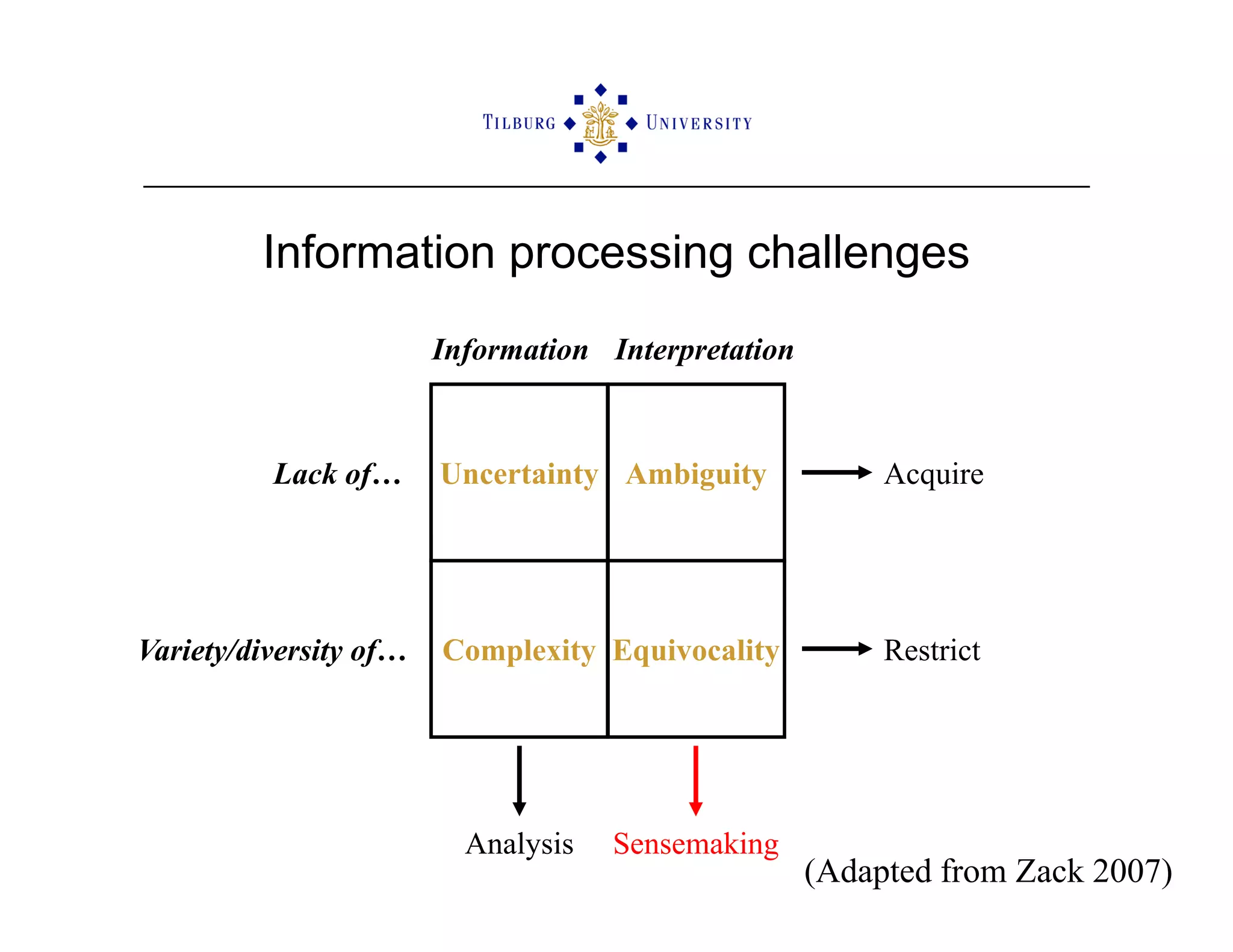
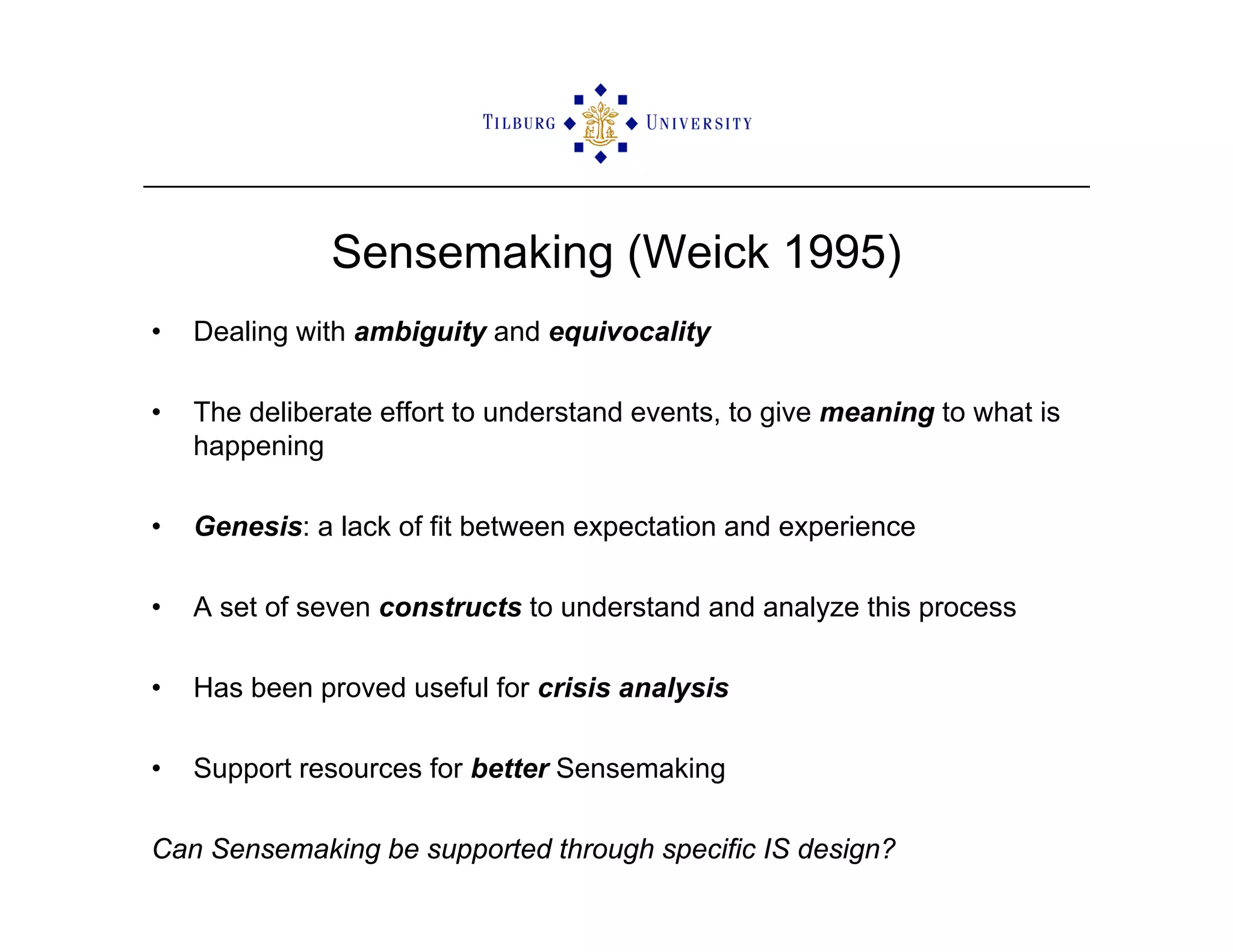
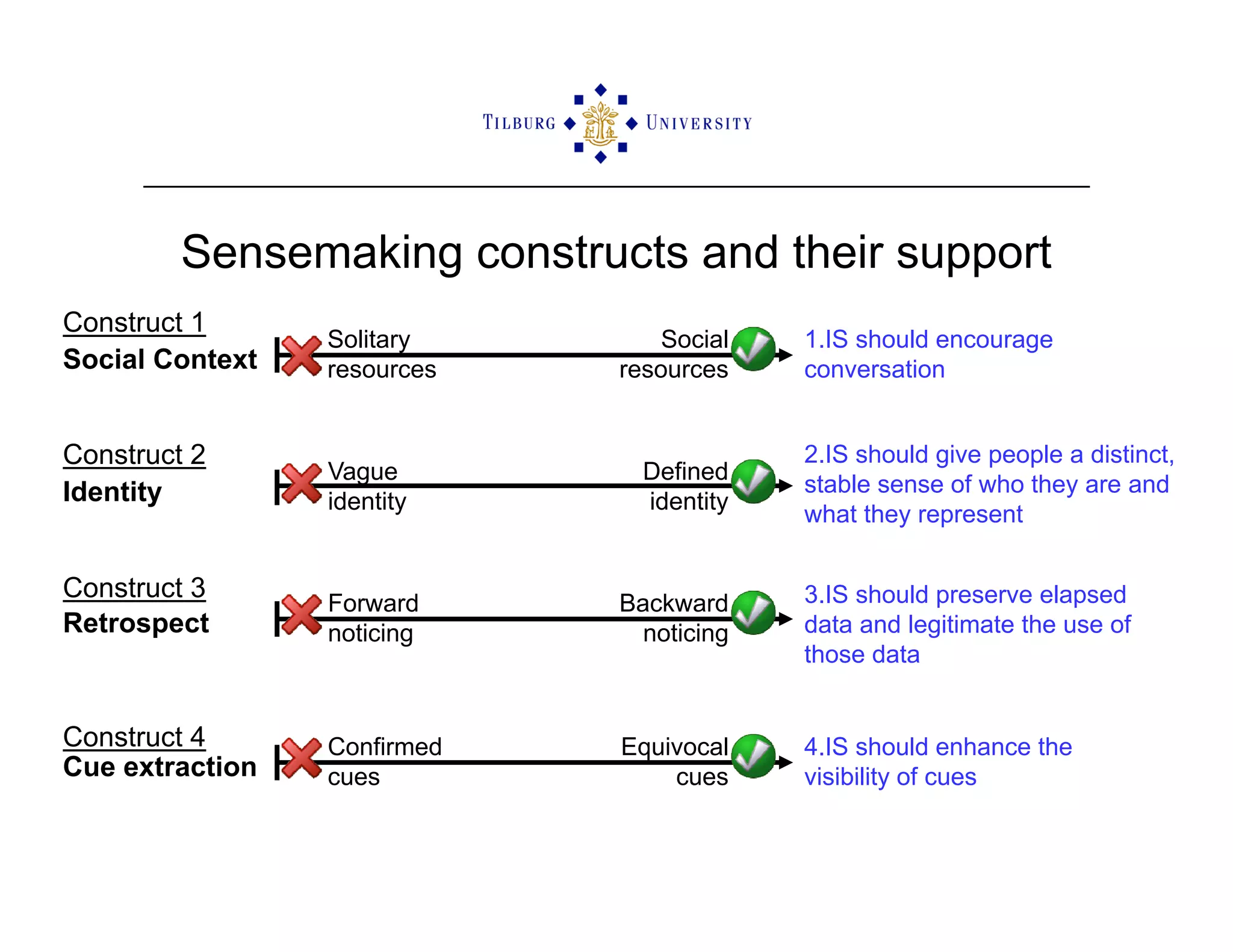
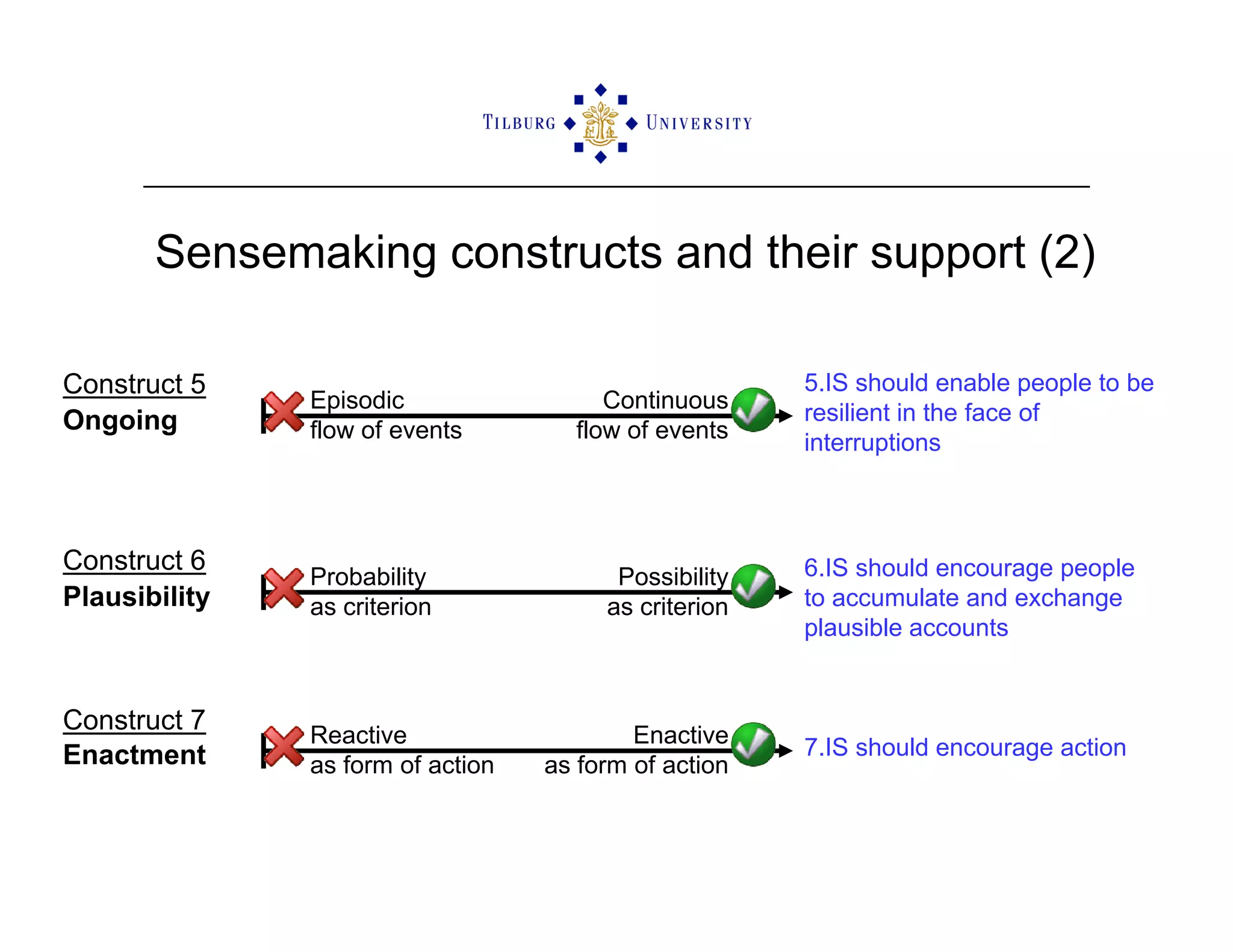

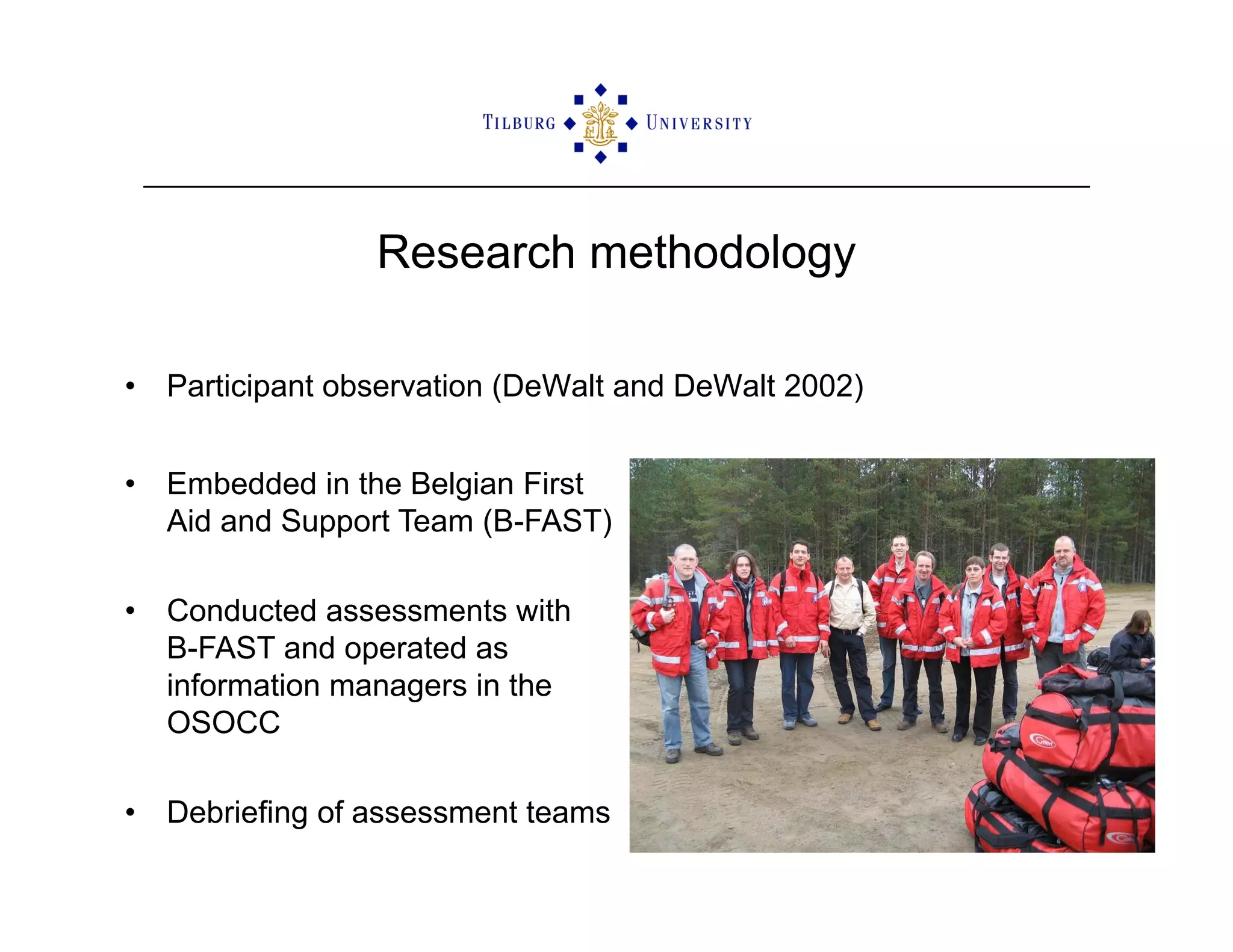
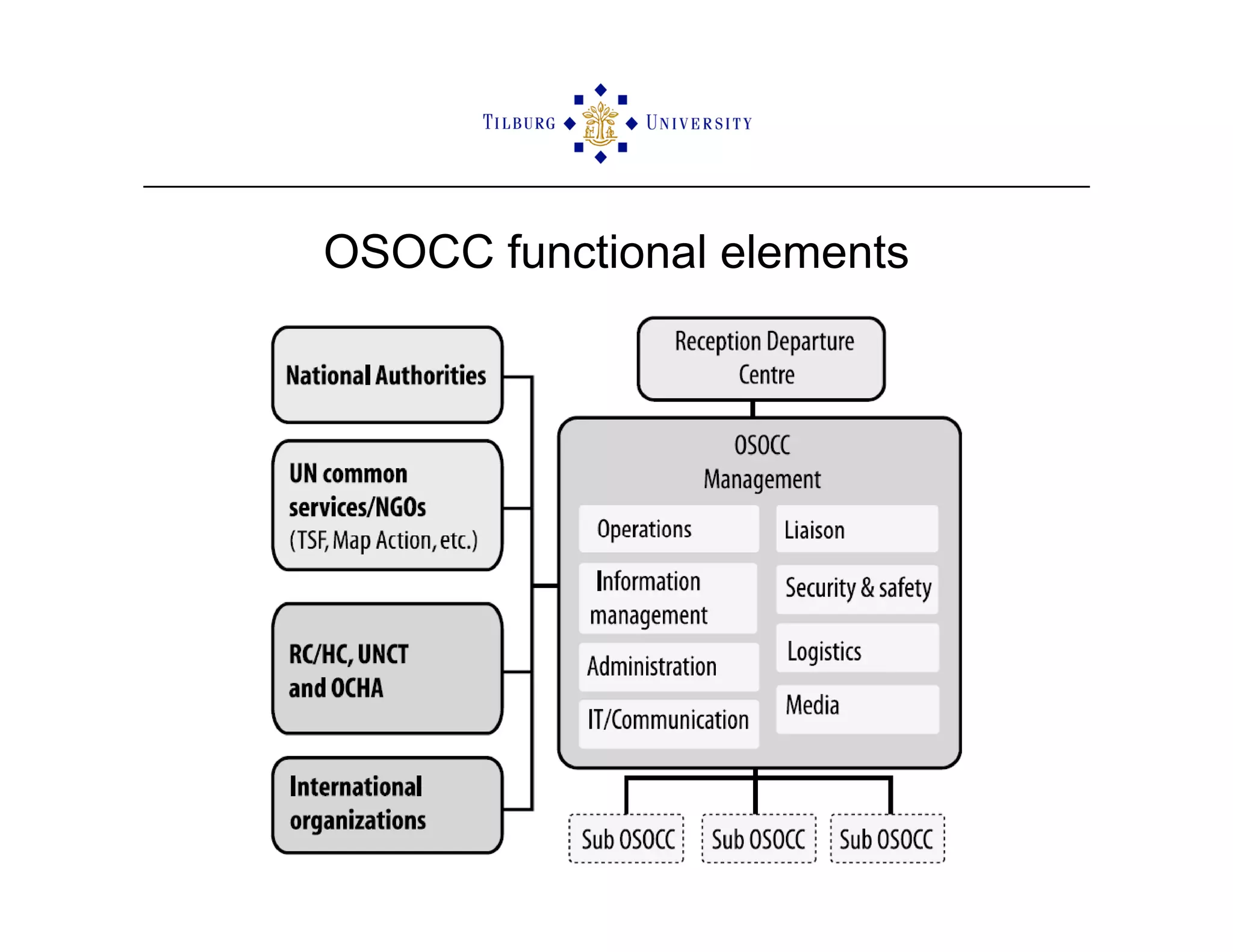

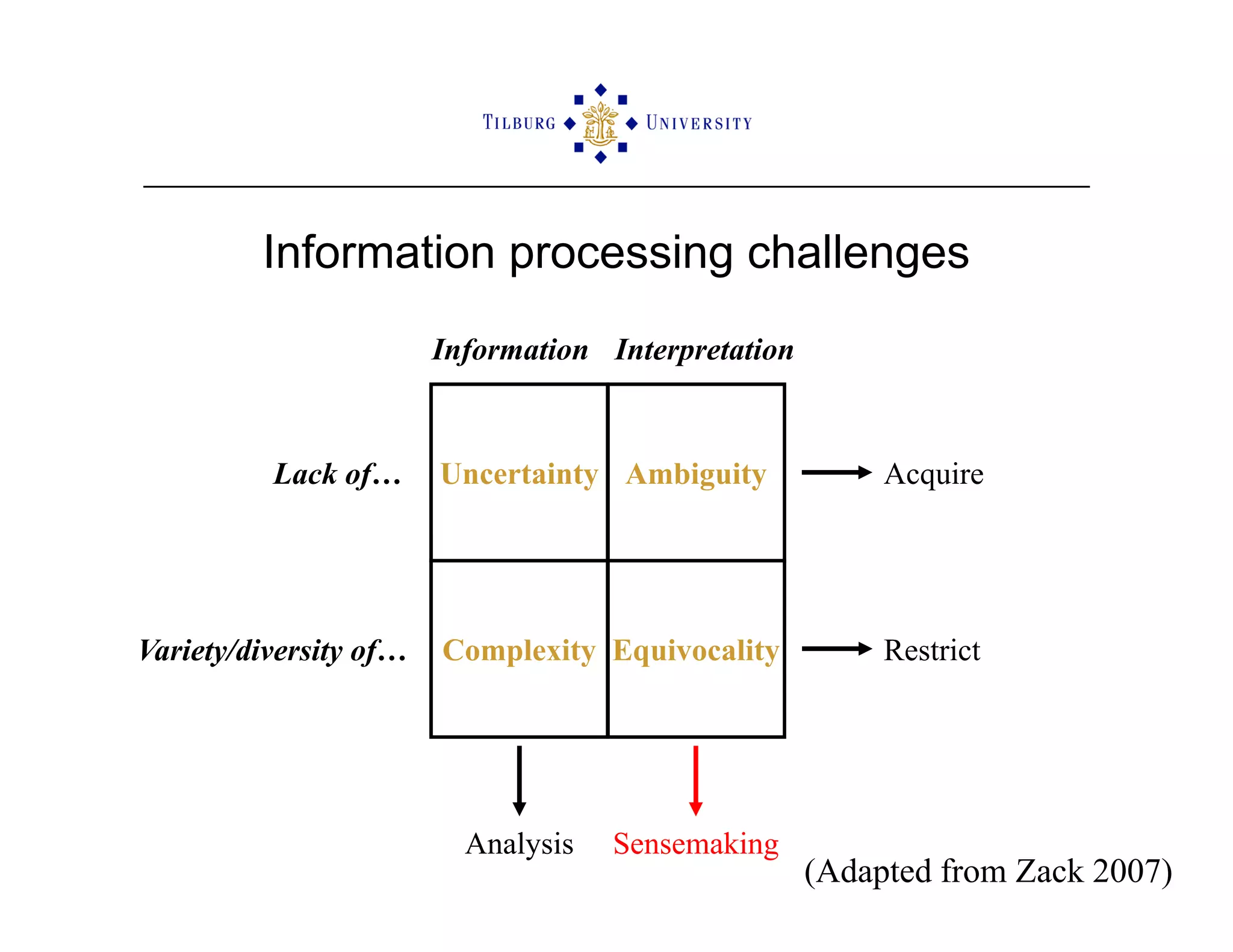
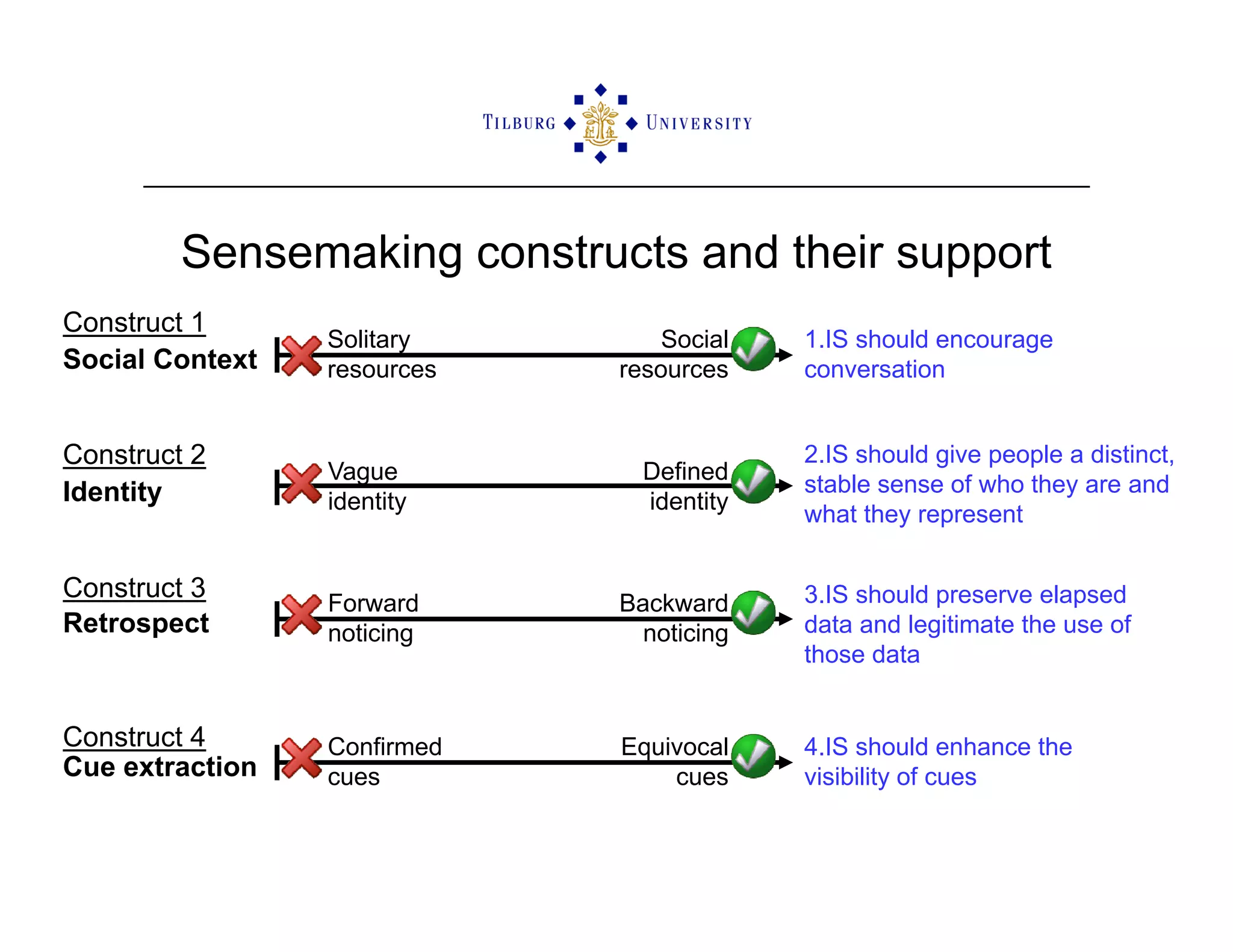
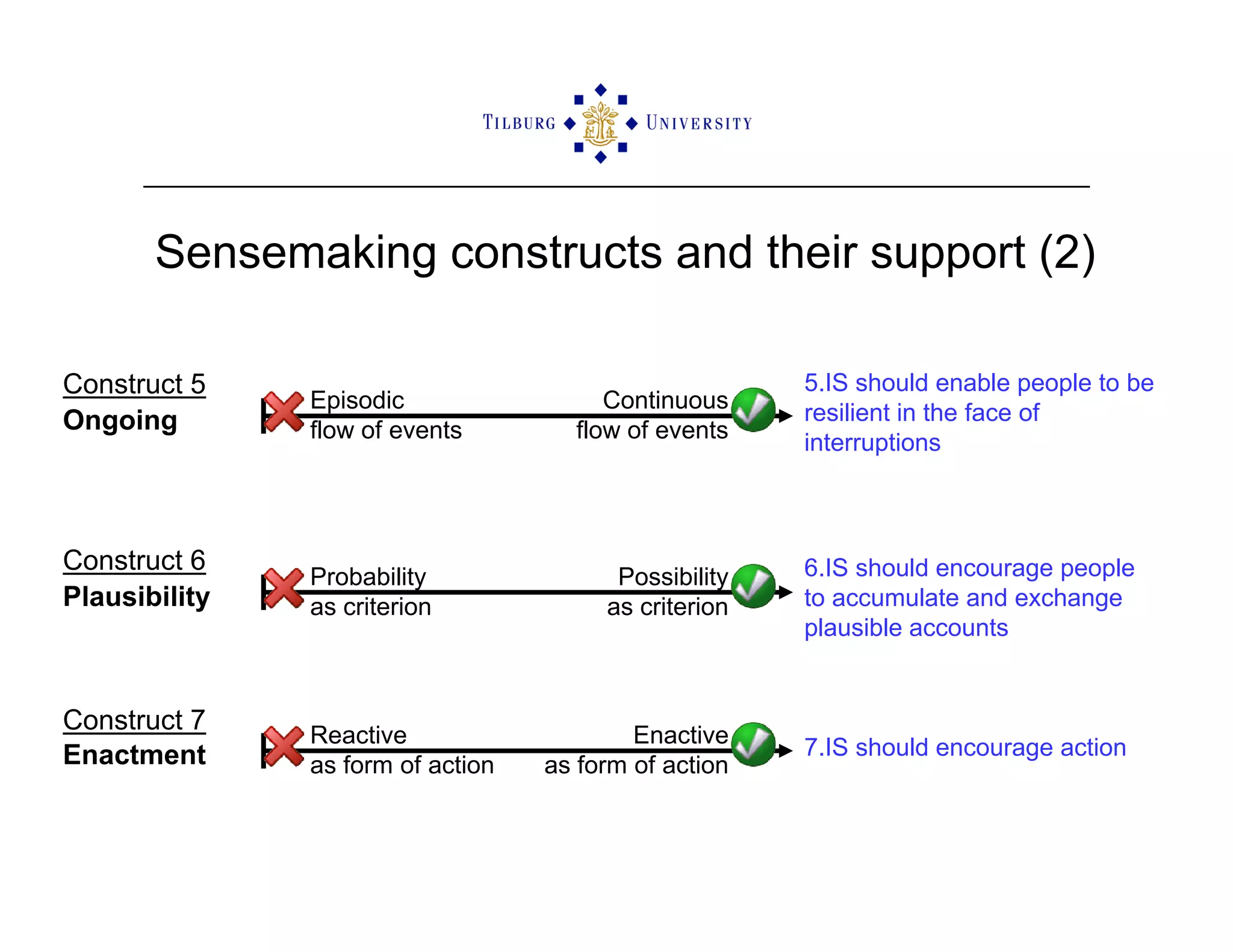
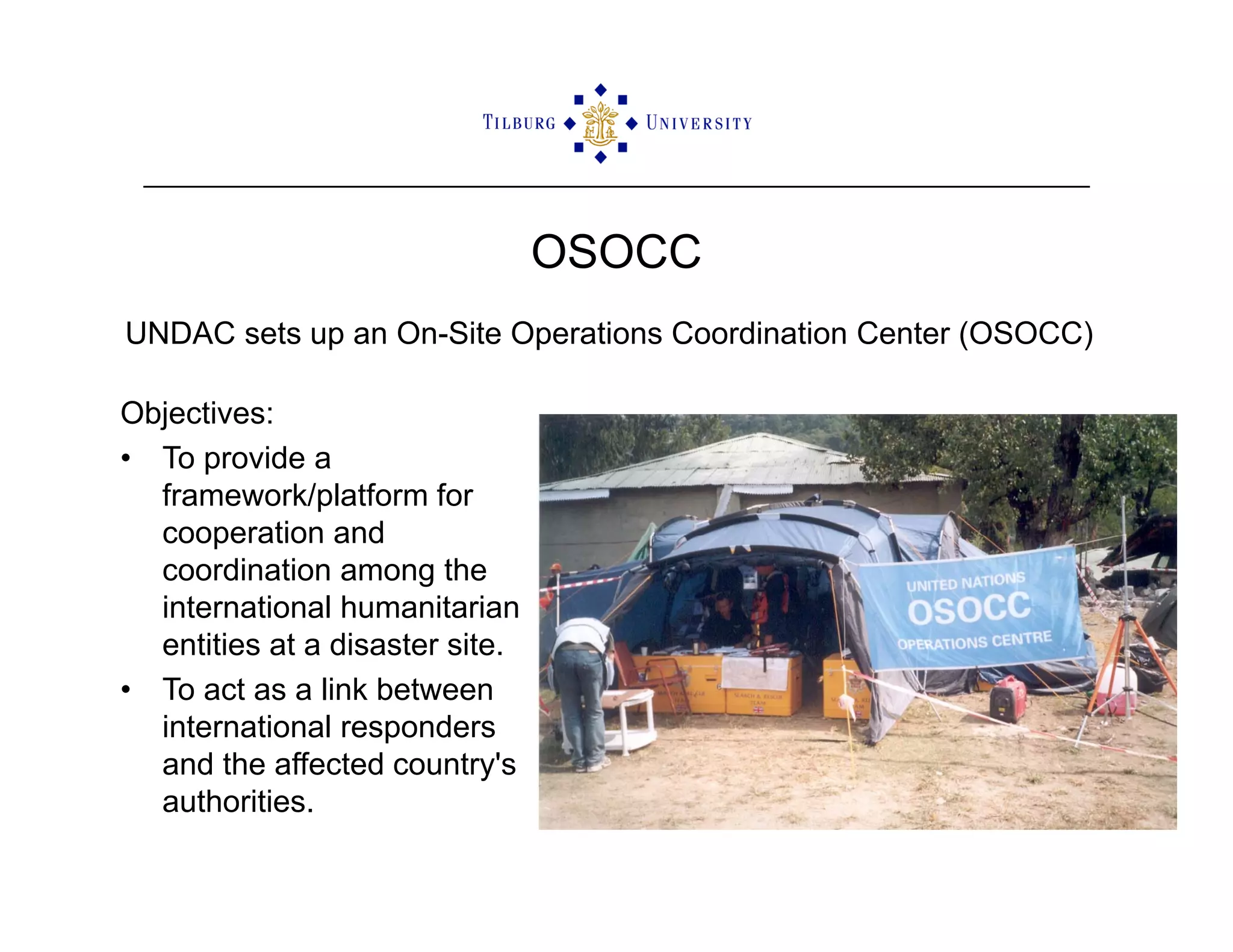
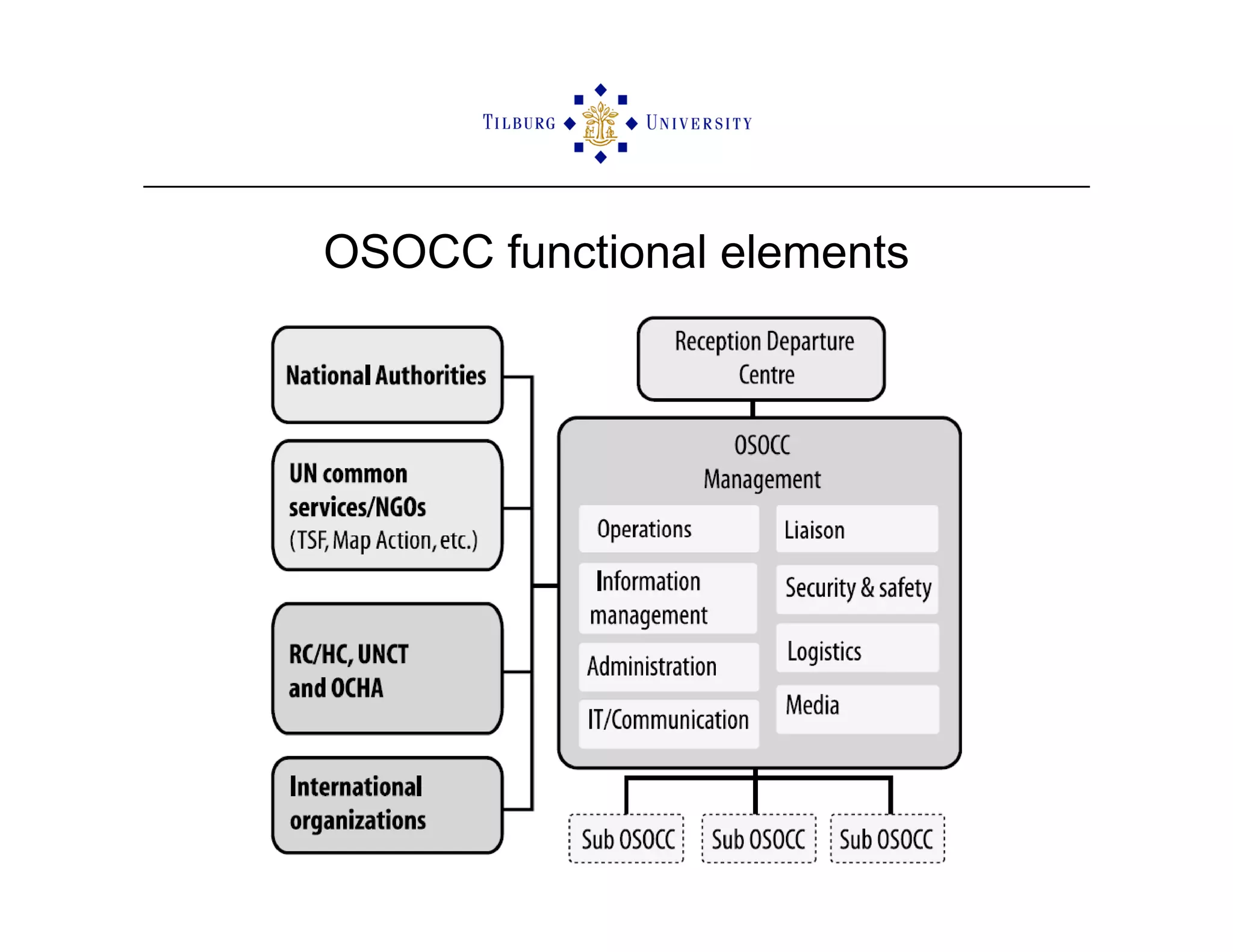
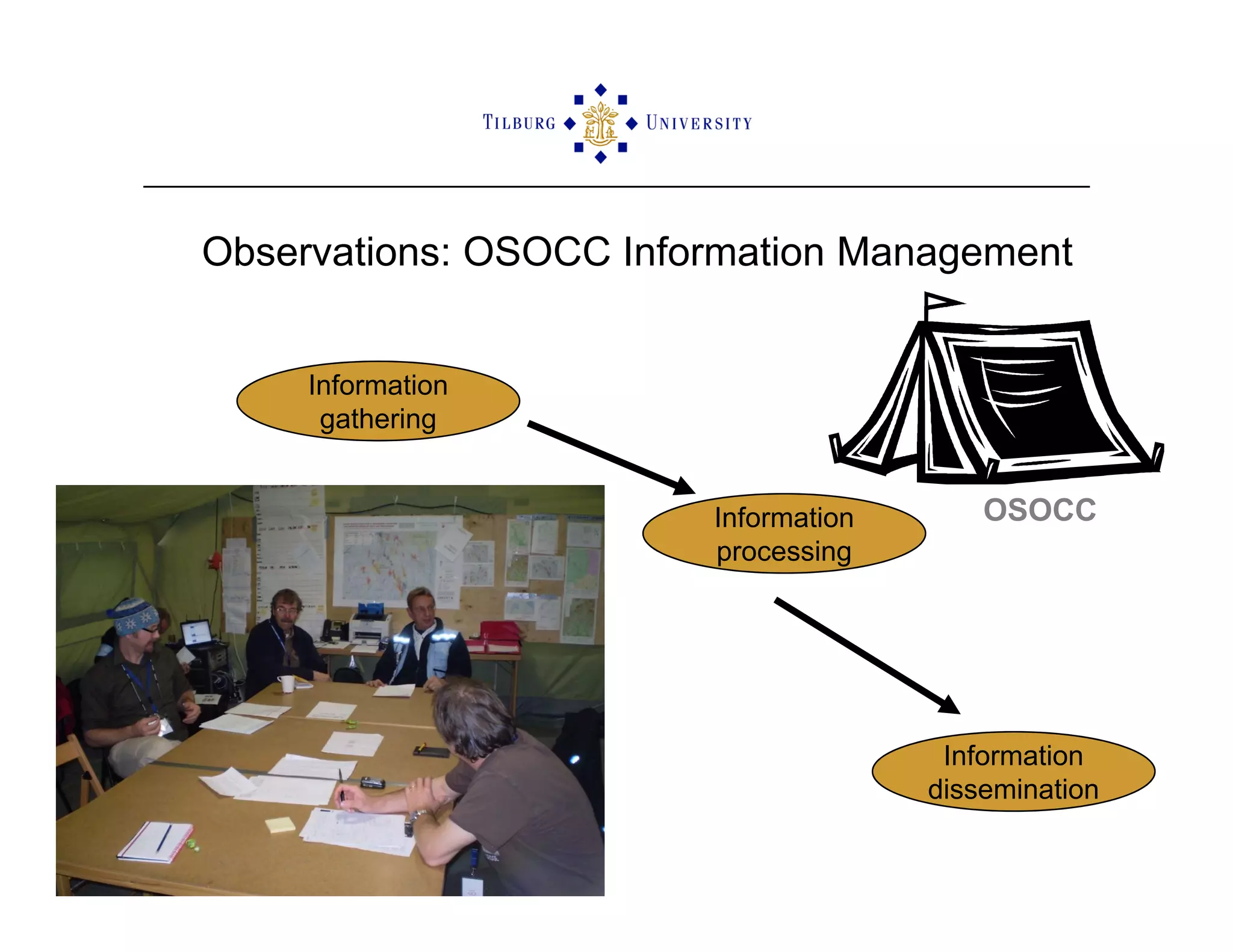
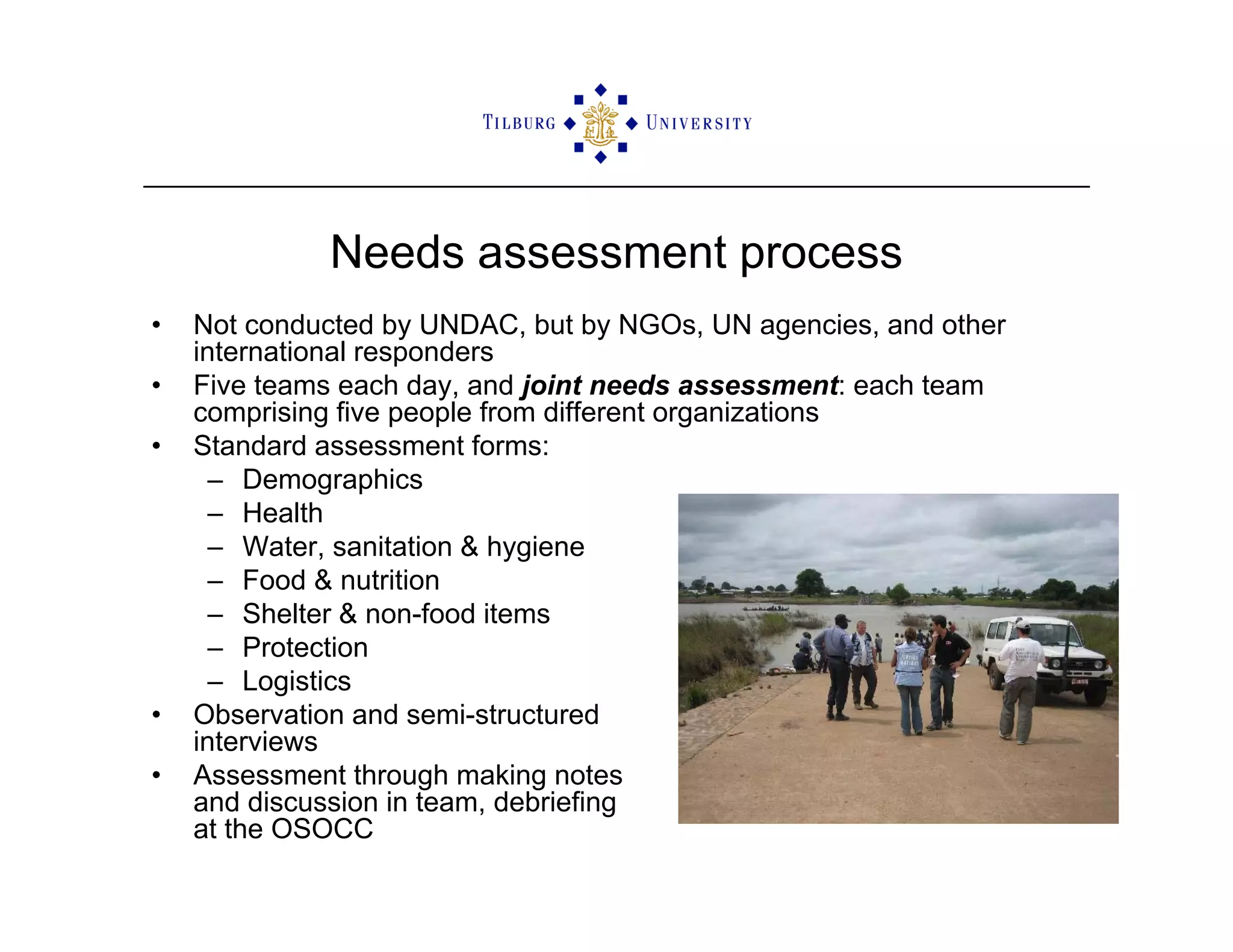
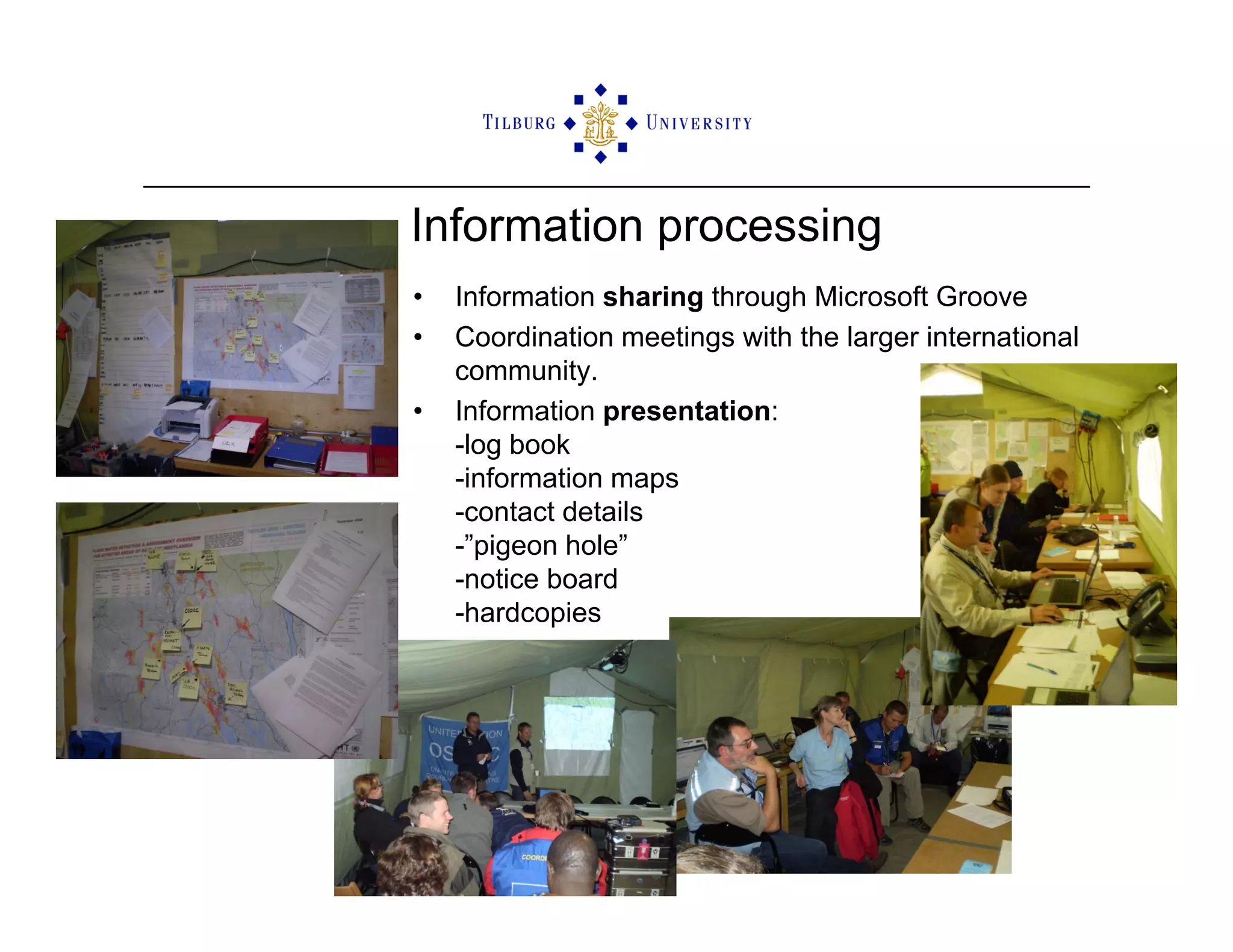
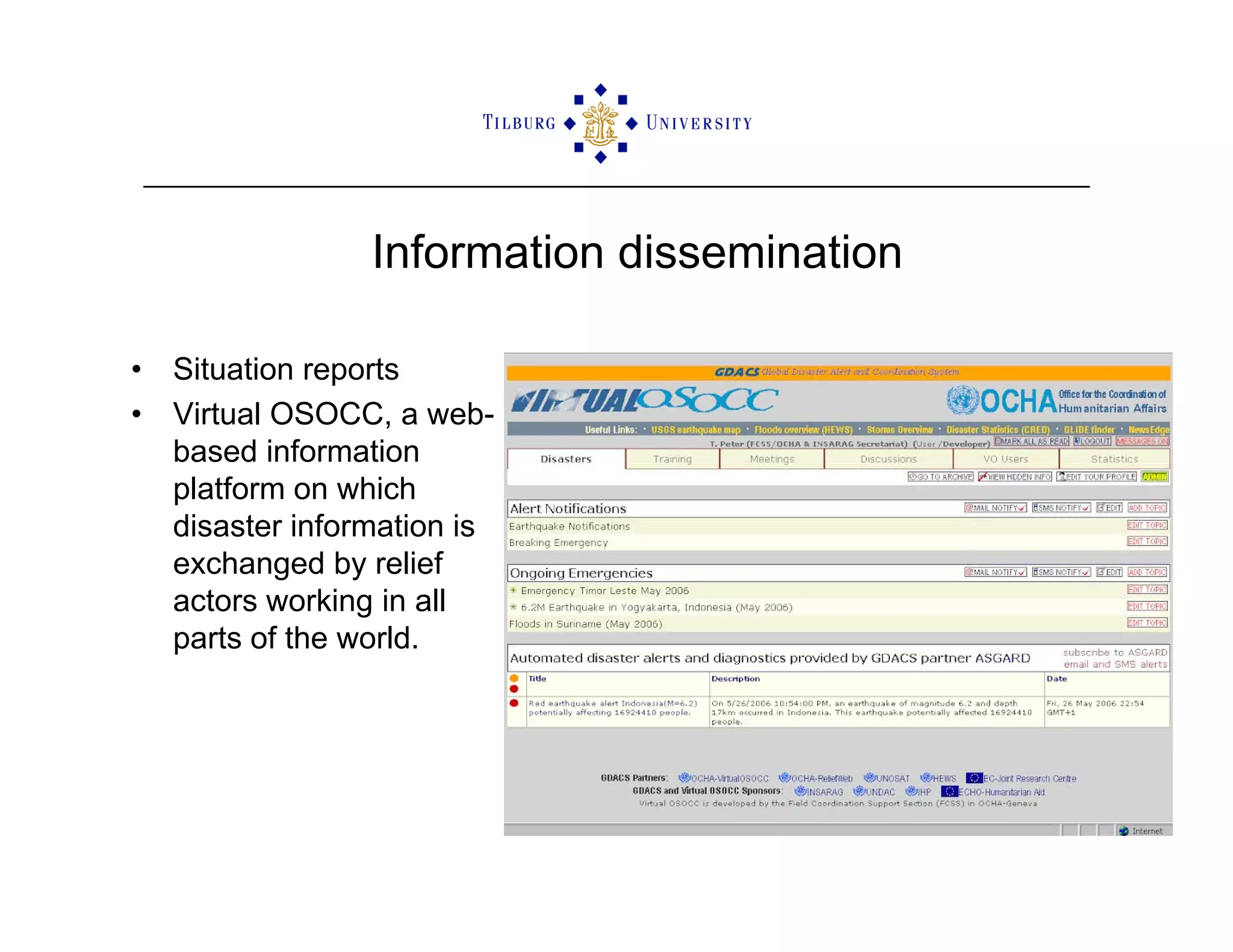
The document discusses the challenges of sensemaking and information management in humanitarian disaster response, focusing on the UN's Disaster Assessment and Coordination (UNDAC) team. It outlines the importance of effective information processing and the need to improve sensemaking to reduce ambiguity during disaster assessments. The authors propose that information systems can support sensemaking constructs, ultimately enhancing the coordination and response effectiveness of international humanitarian efforts.