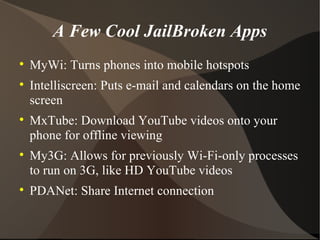
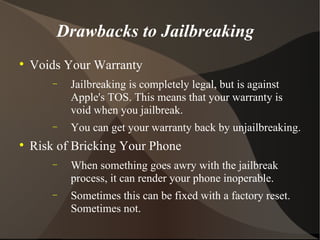
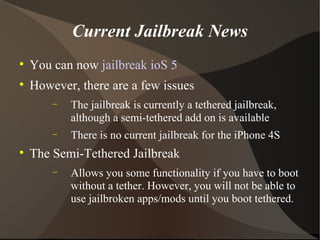
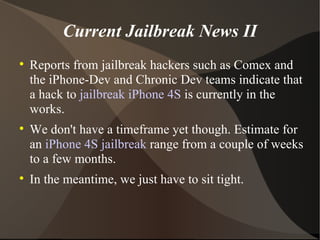
iPhone jailbreaking involves removing Apple-imposed restrictions, allowing users access to third-party apps and features like 3G FaceTime. While jailbreaking can save money and enhance functionality, it voids warranties and carries risks such as bricking the device. Current jailbreaks for iOS 5 exist, but the iPhone 4S remains without a jailbreak, with rumors of future solutions being explored by various hacker communities.