TraceViewer is an application that allows tracing of network elements and subscribers to monitor network quality and troubleshoot problems. It collects trace data from elements and stores it in a database where it can be viewed as reports. Key features of TraceViewer include activating new traces, stopping traces, deleting traces, and viewing trace reports. The architecture involves TraceViewer installing on Linux servers with a GUI accessed via Java WebStart, while background tracing processes activate traces in network elements and collect data.

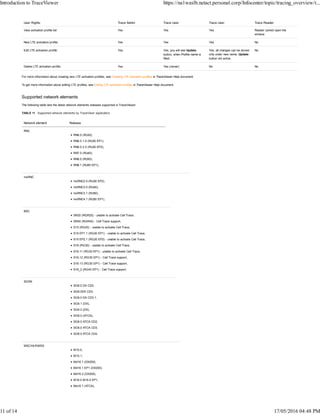
![Identifier Description
activate_trace
stop_trace
remove_trace
copy_trace
restart_trace
Effect code Identifies whether the operation was create (C) or delete (D).
For TraceViewer operations these are:
copy 'C'
restart 'C'
activate_trace 'C'
deactivate_trace 'D'
remove_trace 'D'
Client address IP address from which the user was connected.
Category code Subscriber-sensitive configuration (SUBC).
Timestamp Timestamp of the operation, which should also include the time zone.
Format for this entry is:
2011-12-05T13:06:55.792+0200
Element Name of the element on which the operation was performed.
Identifier Identifies whether the operation succeeded or not.
T=succeeded
F=failure
Operation identifier Identifiers of the operations:
Activation
Deactivation
Copy
Restart
Deletion
Resource type The resource type for the following resource values that the operation affected.
This depends on the application and the operation (for example access_point, msisdn, imsi).
Resource Resource value, for example, target IMSI/IMEI/MSISDN number.
Cause code The reason for the operation failure. The allowed values are:
‘N/A’
The following is an example of a possible application startup entry in a log file:
trace activation:
2015-04-06T14:07:45.795+0200 | (104,713) | OSS_CHANGE |
com.nsn.nas.trc.trc_core.beans.act.TraceOperationManagerBean.requestActivation | audit[ | Source='Server' | User
identity='omc' | Operation identifier='Activation' | Success code='T' | Cause code='N/A' | Identifier='SUCCESS' | Target
element='TraceViewer' | Client address='10.9.167.172' |
Resource type='NetworkElements' |
Resource='PLMN-123/RNC-124,PLMN-123/RNC-123' | Resource
type='TraceReference' | Resource='952' | Source session
identifier='' | Target session identifier='' | Category code='SUBC' | Effect code='C' | Network Transaction
identifier='' | Source user identity='' | Target user
identity='' | Timestamp='1323083215791']
noticication about trace activation:
2015-04-06T14:07:46.637+0200 | (104,810) | OSS_CHANGE |
com.nsn.nas.trc.trc_core.beans.nh.handlers.ReportOperationStatusHandler.process
| audit[ | Source='Server' | User identity='omc' | Operation
identifier='Activation' | Success code='T' | Cause code='N/A' |
Identifier='SUCCESS' | Target element='PLMN-123/RNC-124' |
Client address='10.9.167.172' | Resource type='TraceReference'
| Resource='952' | Source session identifier='' | Target session
identifier='' | Category code='SUBC' | Effect code='C' | Network
Transaction identifier='' | Source user identity='' | Target
user identity='' | Timestamp='1323083216636']
Tracing concepts
Introduction to TraceViewer https://na1waslb.netact.personal.corp/Infocenter/topic/tracing_overview/t...
3 of 14 17/05/2016 04:48 PM](https://image.slidesharecdn.com/introductiontotraceviewer-170530185026/85/Introduction-to-trace-viewer-3-320.jpg)