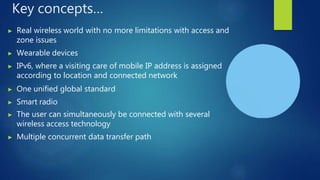
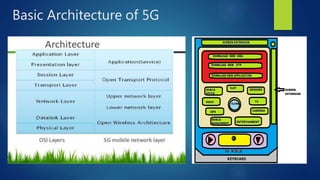
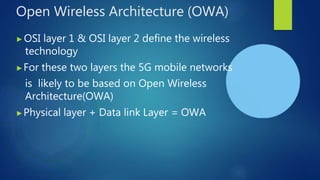
The document provides an overview of 5G wireless technology, detailing its evolution from previous generations (1G to 4G) and highlighting its key features such as extraordinary data capabilities and high connectivity. It describes the architecture, hardware, and software components of 5G and emphasizes its advantages, including faster transmission speeds and lower costs. Additionally, it discusses the concept of a real wireless world with limited constraints and implications for various applications and devices.