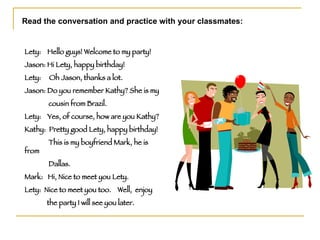
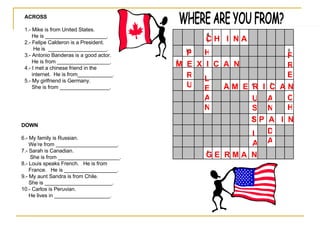
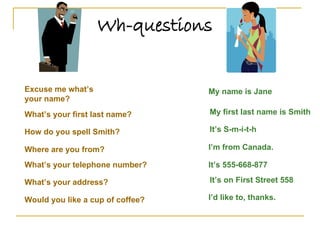
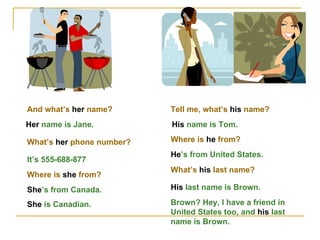
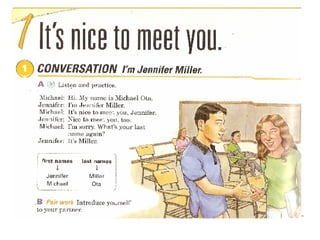
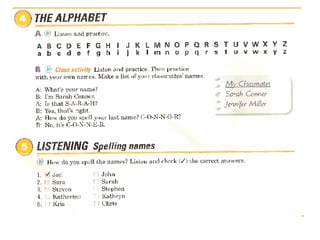
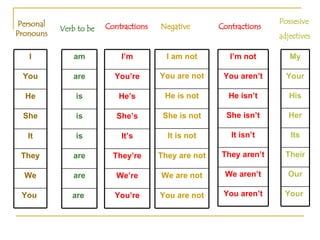
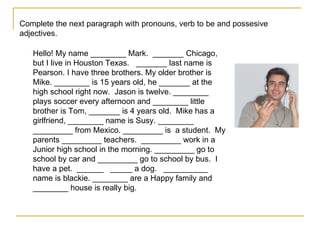
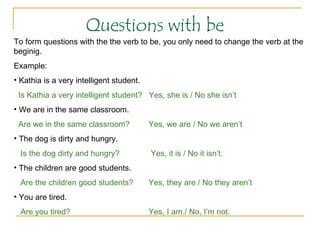
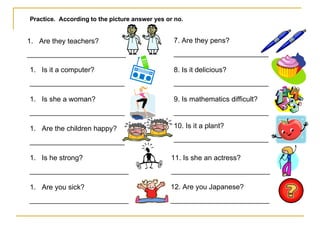
The document features a conversational practice exercise for introducing oneself at a party, providing examples of greetings and connections between individuals. It includes a list of countries and nationalities, along with exercises for completion and questions related to personal information and the verb 'to be.' Additionally, it outlines various pronouns, contractions, and provides practice questions for comprehension.




![Let’s continue in your books!! More information: [email_address]](https://image.slidesharecdn.com/introducing-yourself2517/85/Introducing-Yourself-17-320.jpg)