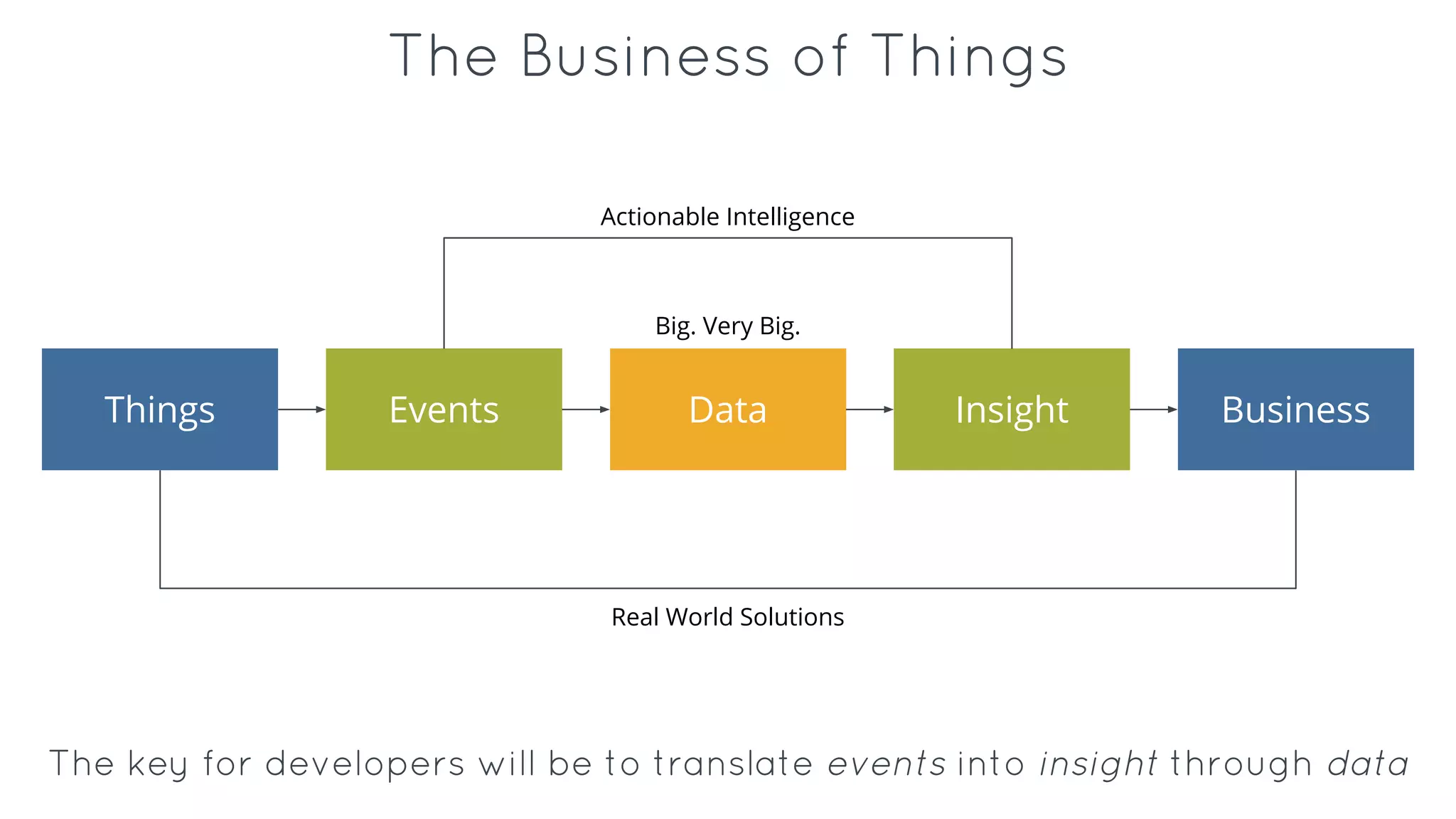
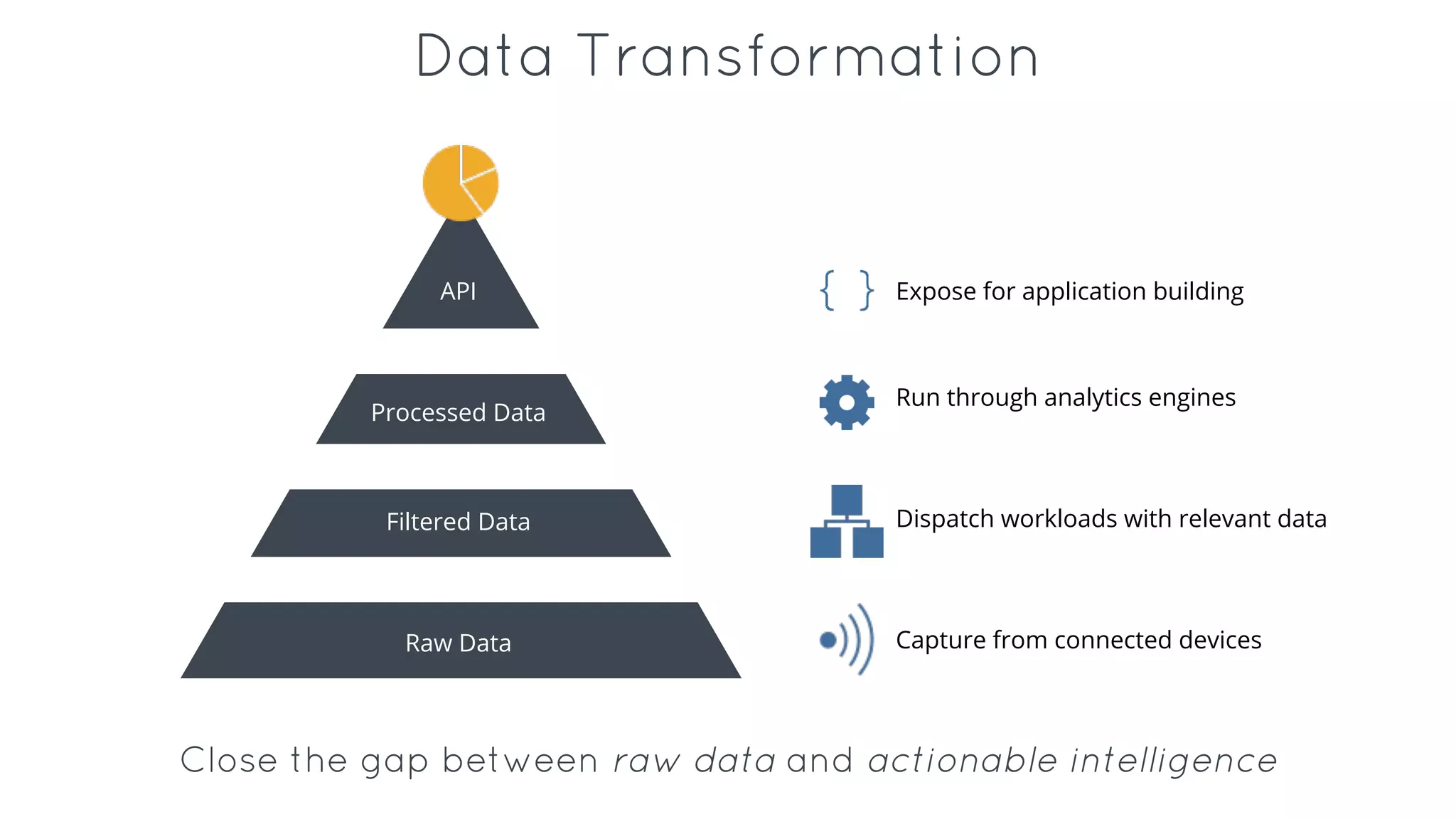
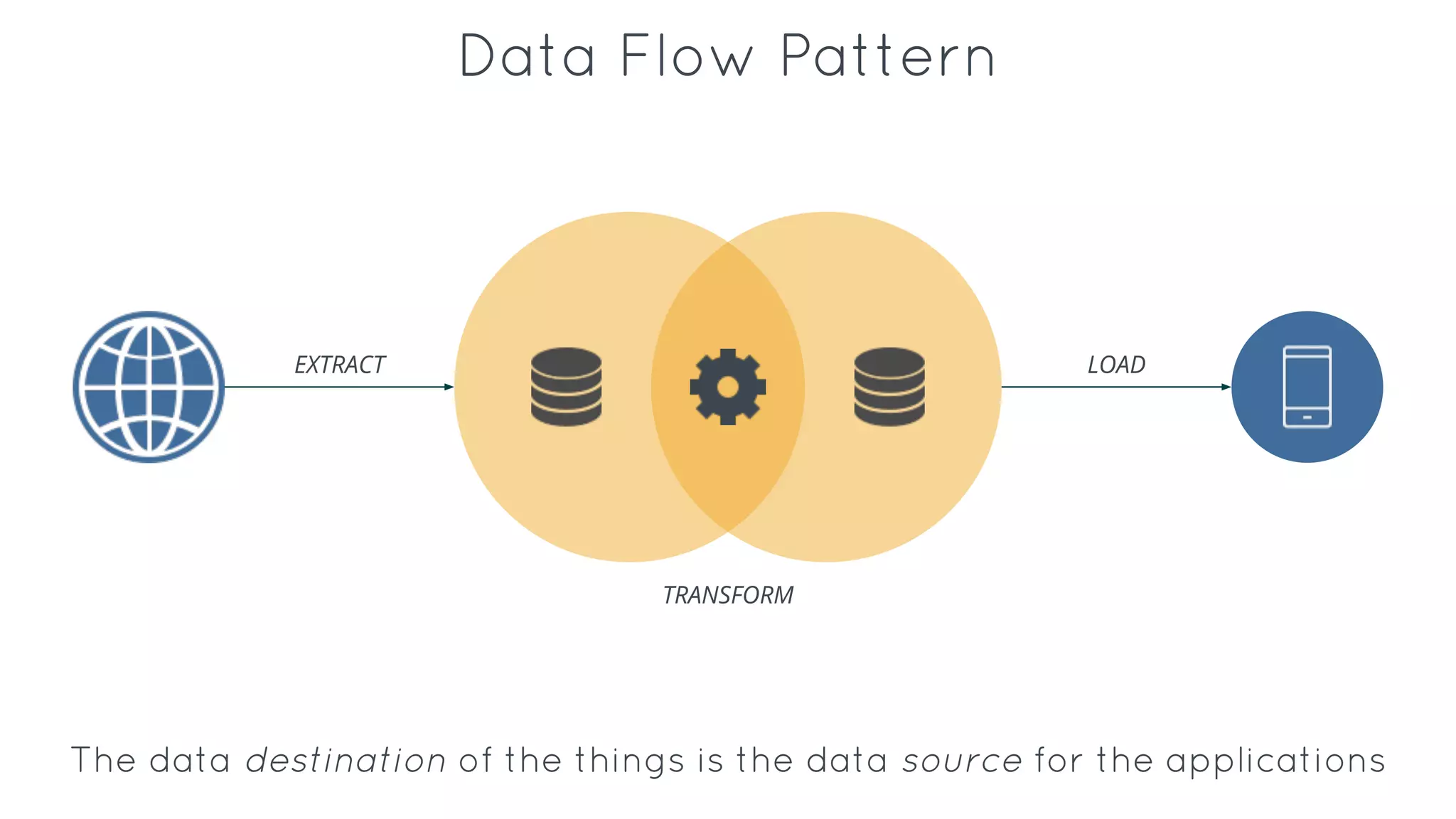
This document discusses the Internet of Things (IoT) and how Iron.io fits into powering IoT applications and workloads. Some key points:
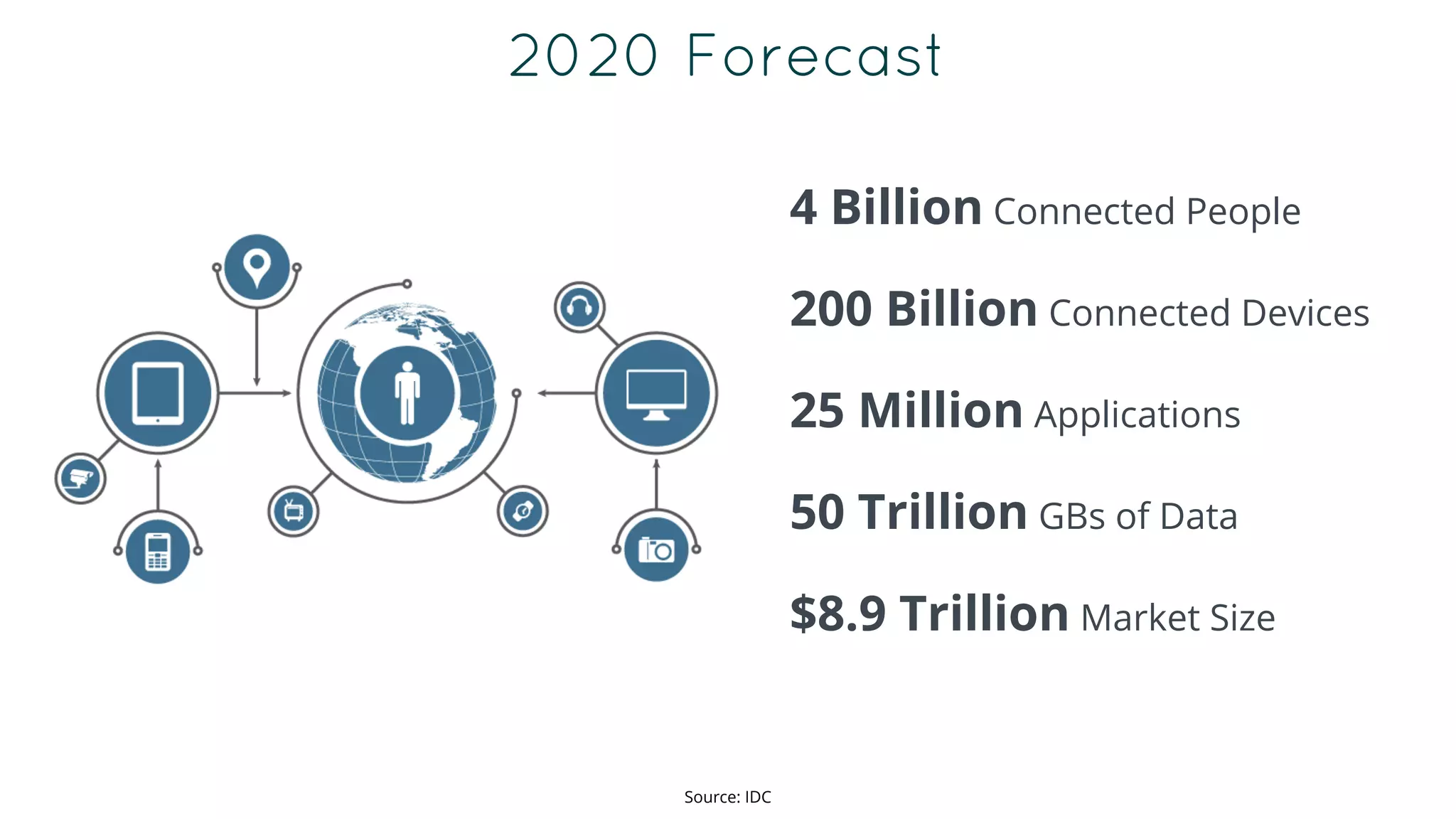
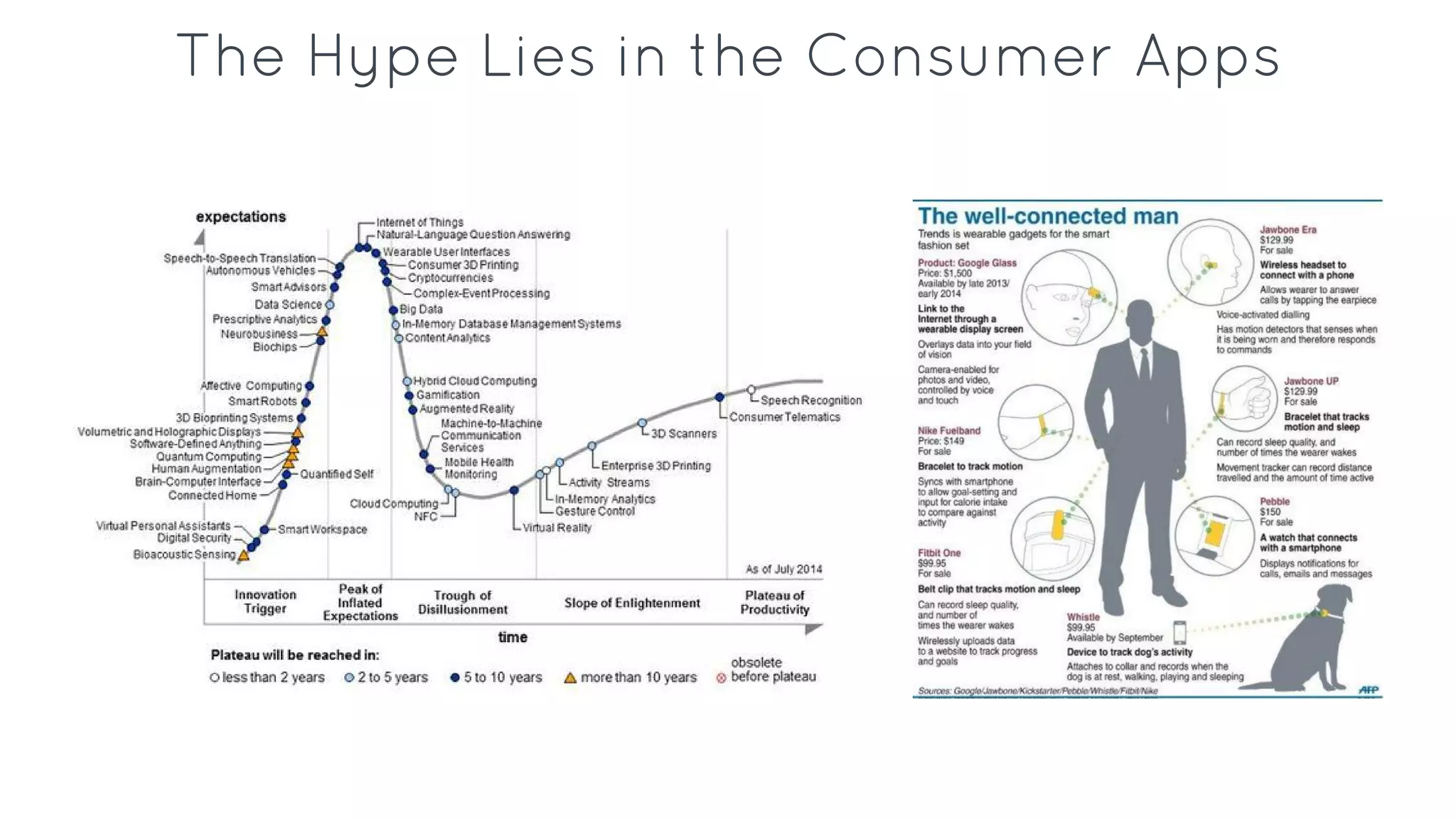
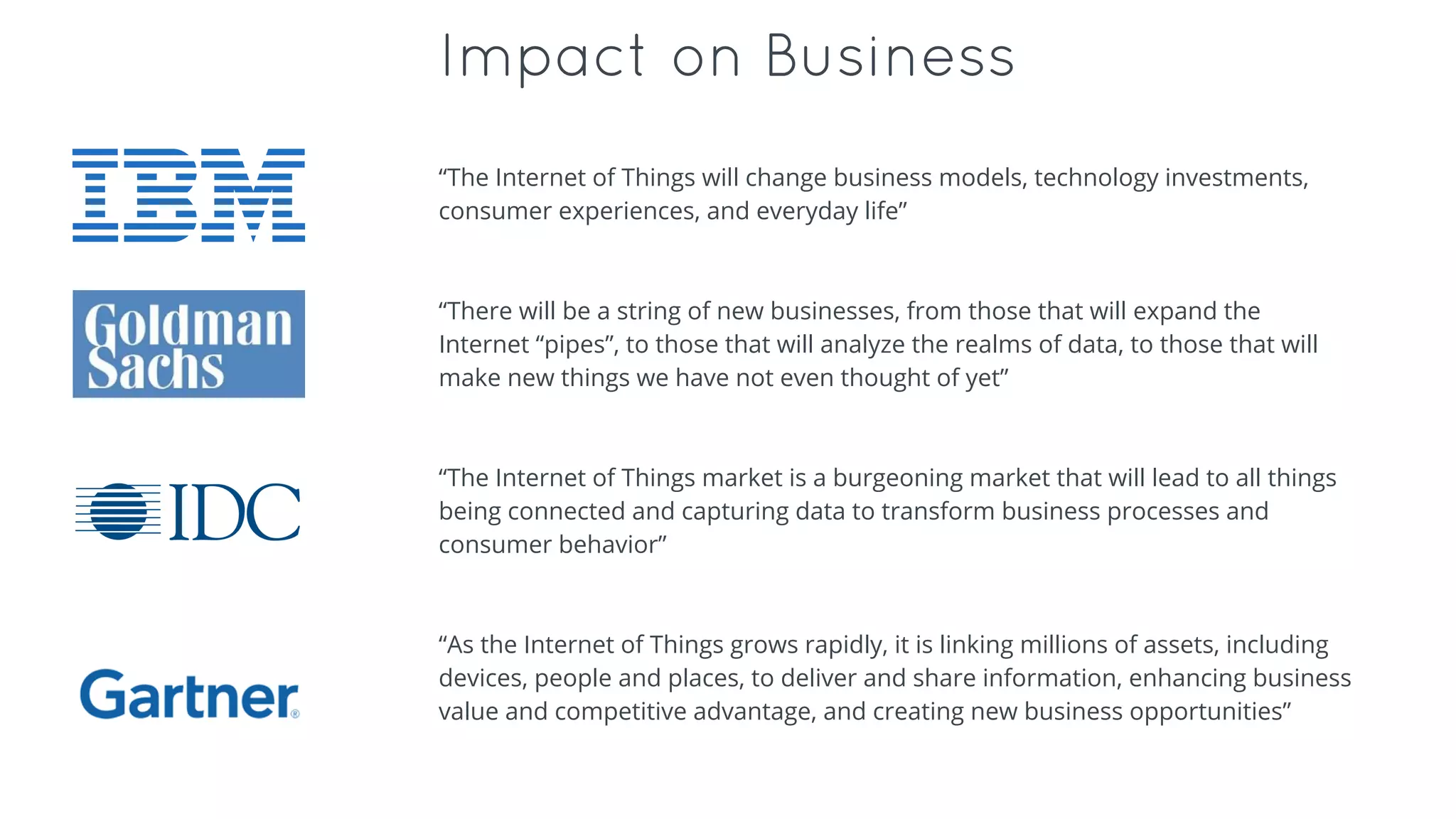
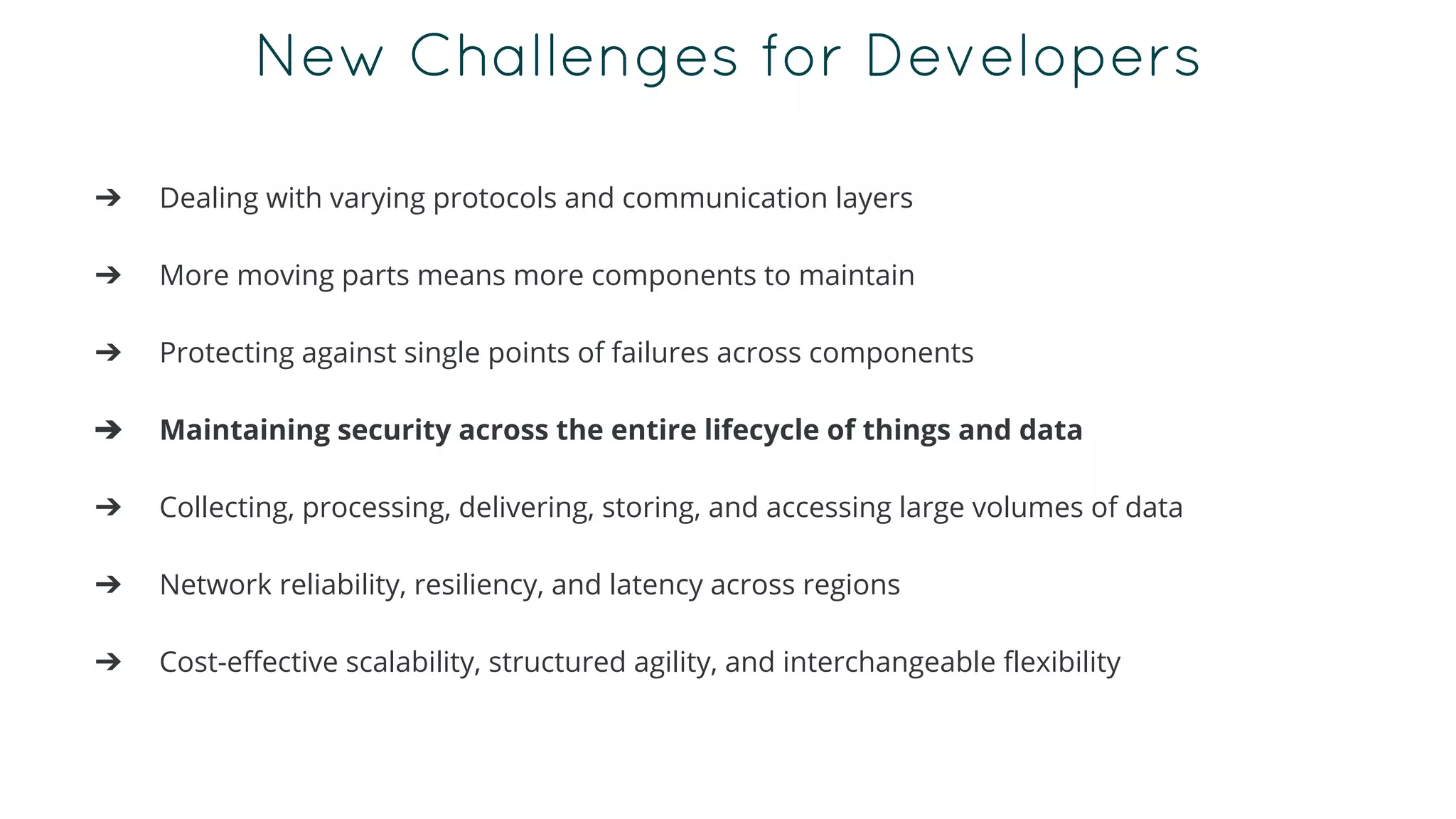
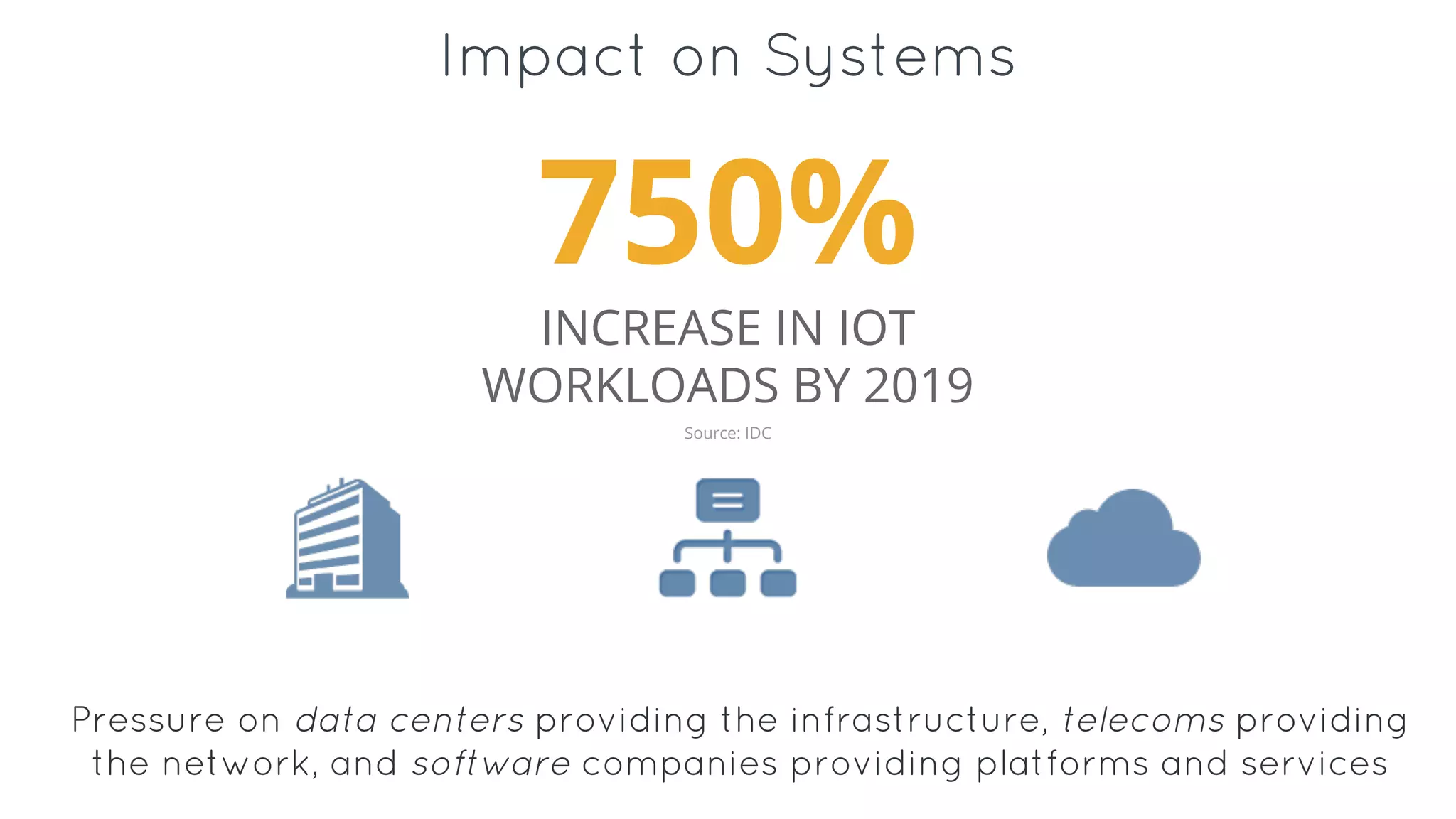
- The IoT is expected to include billions of connected devices generating huge amounts of data by 2020, creating opportunities for developers.
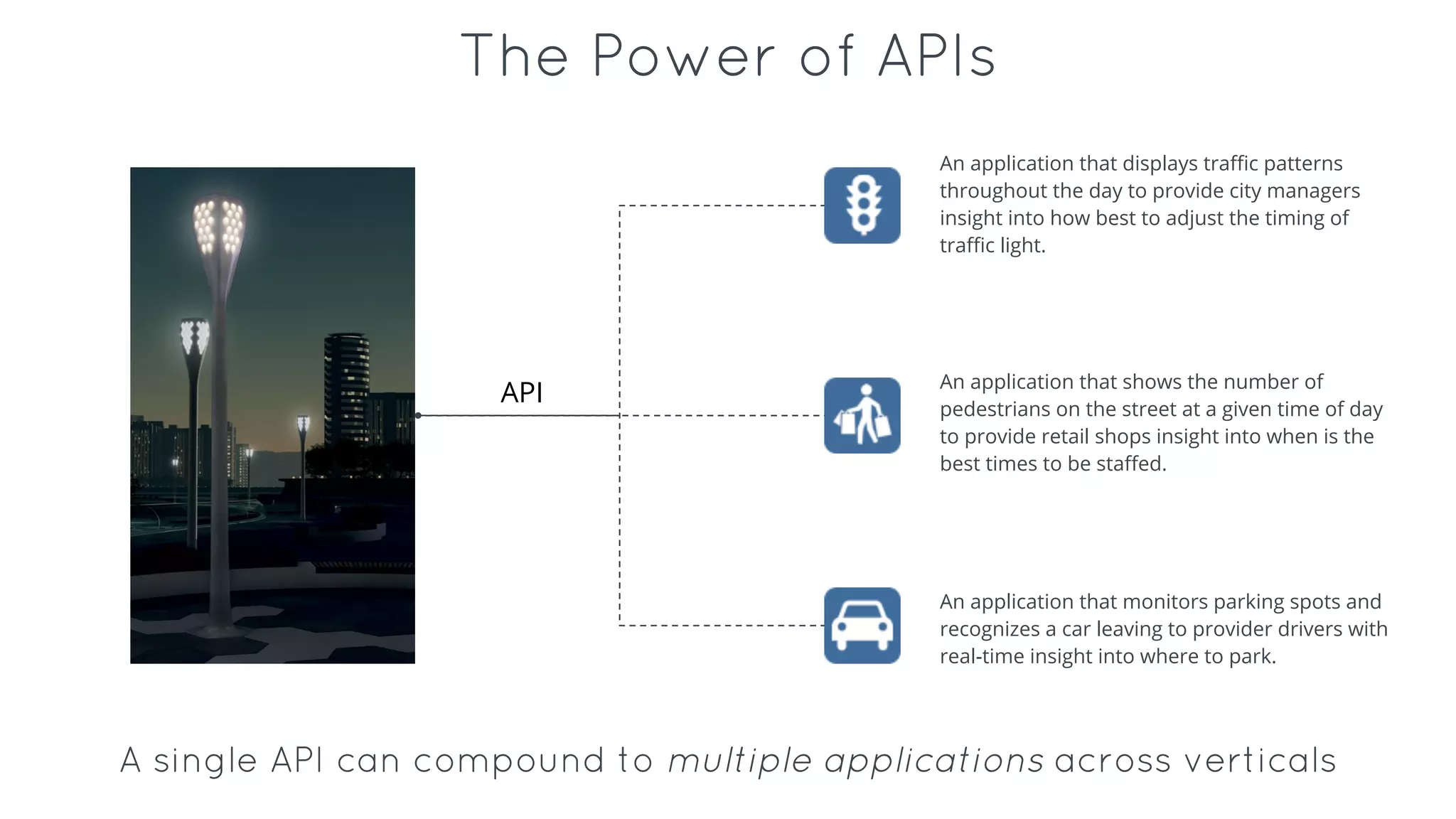
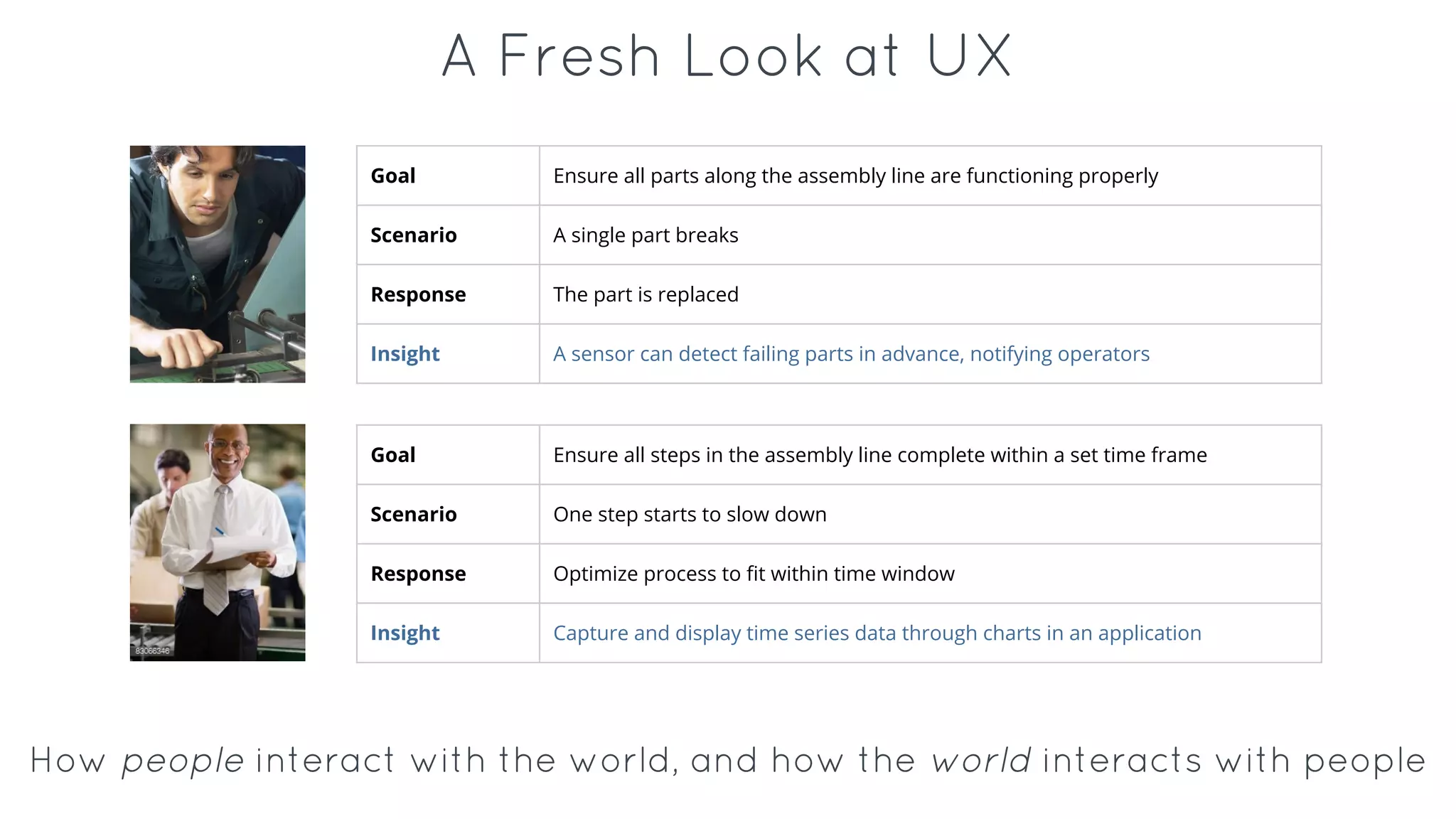
- IoT value comes from real-world solutions across various industries like healthcare, cities, transportation and manufacturing.
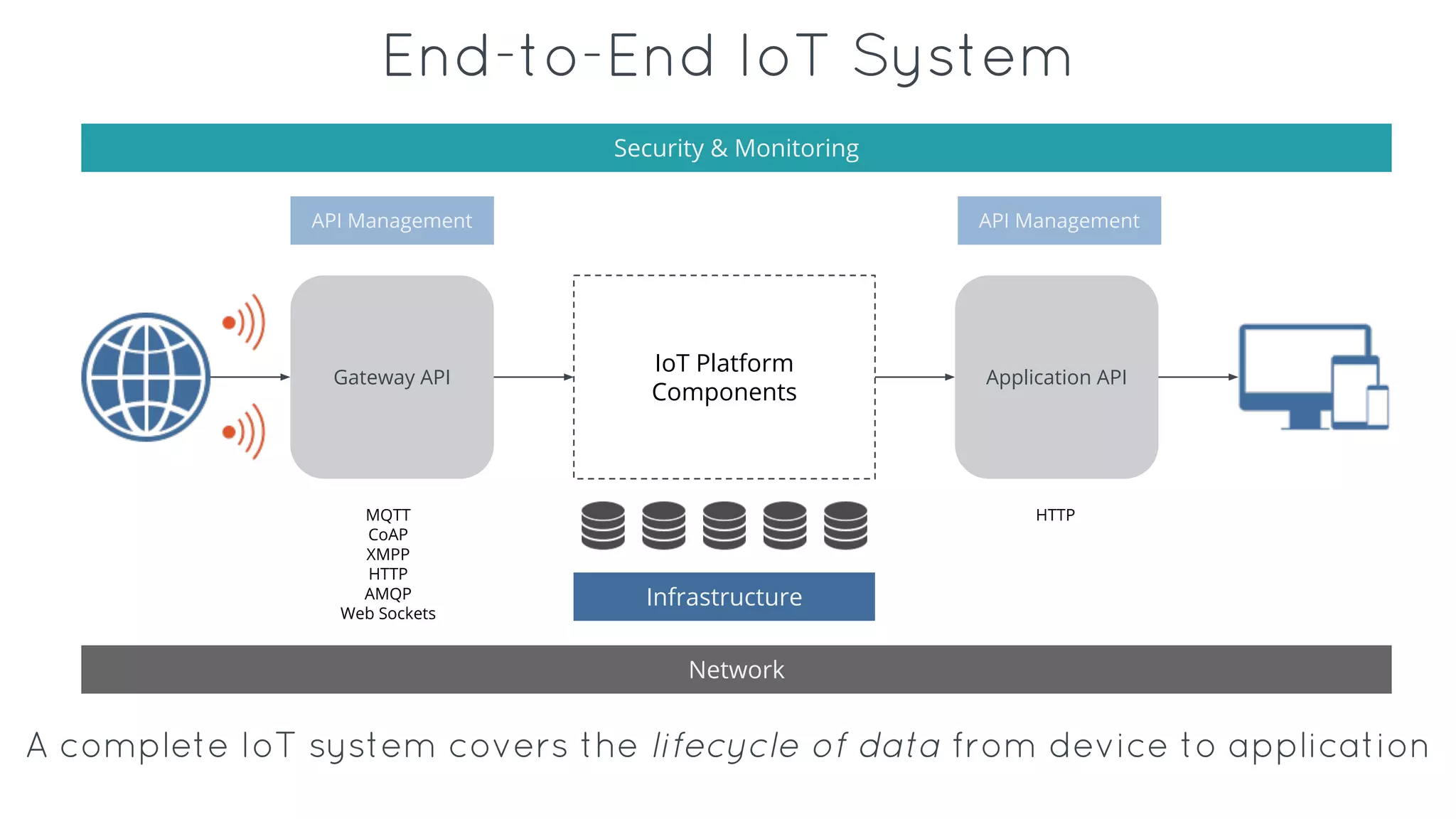
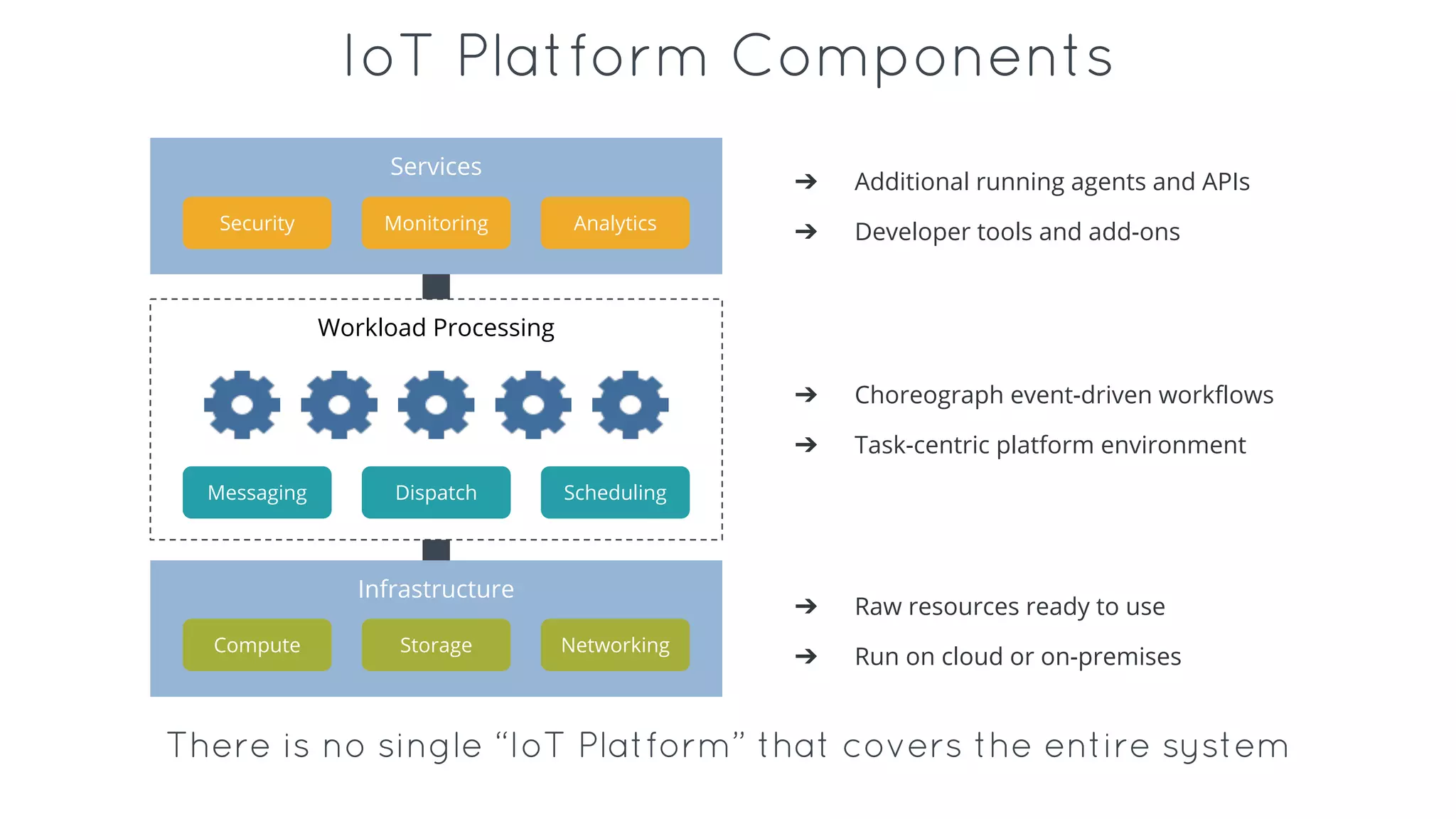
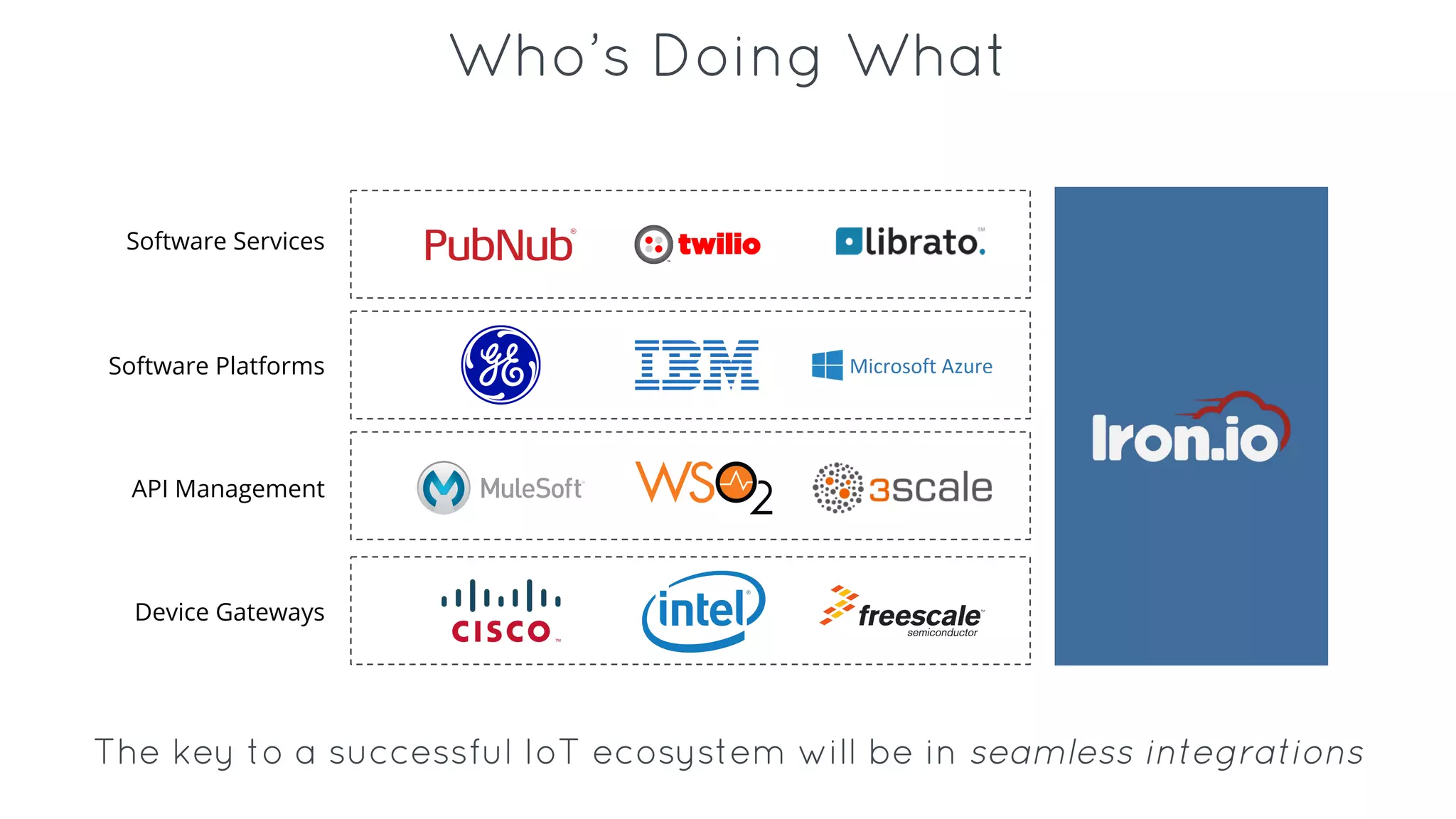
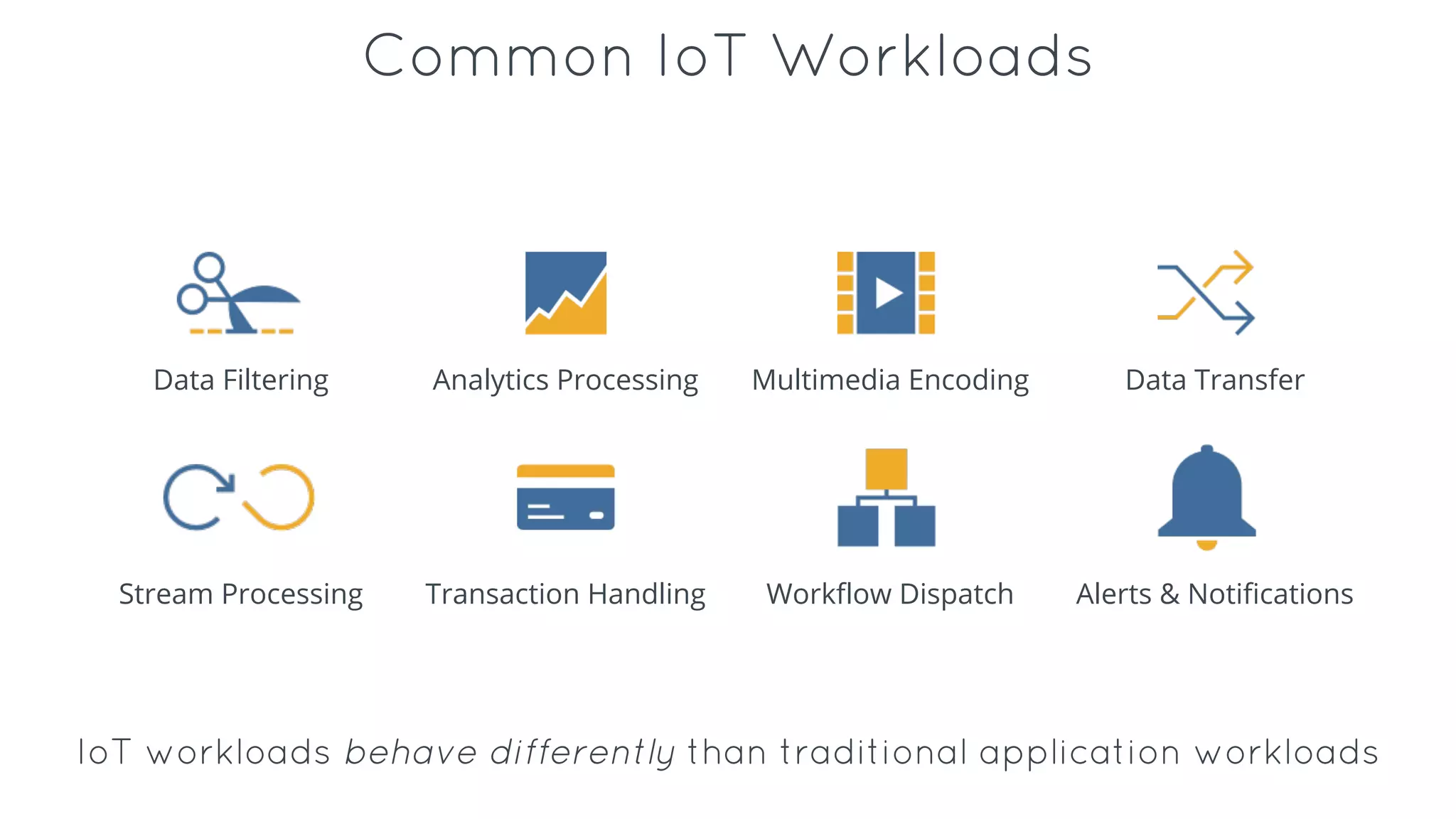
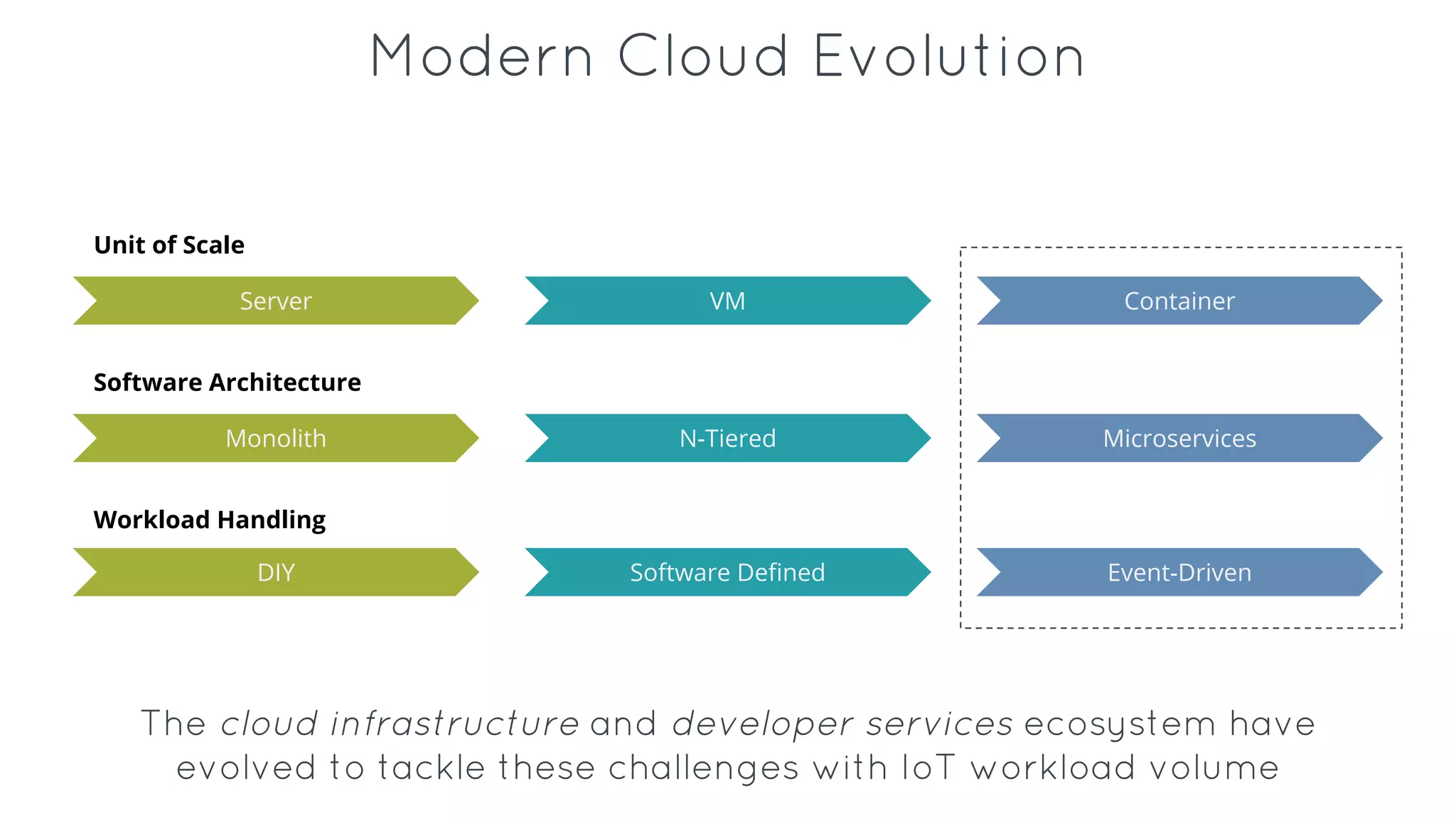
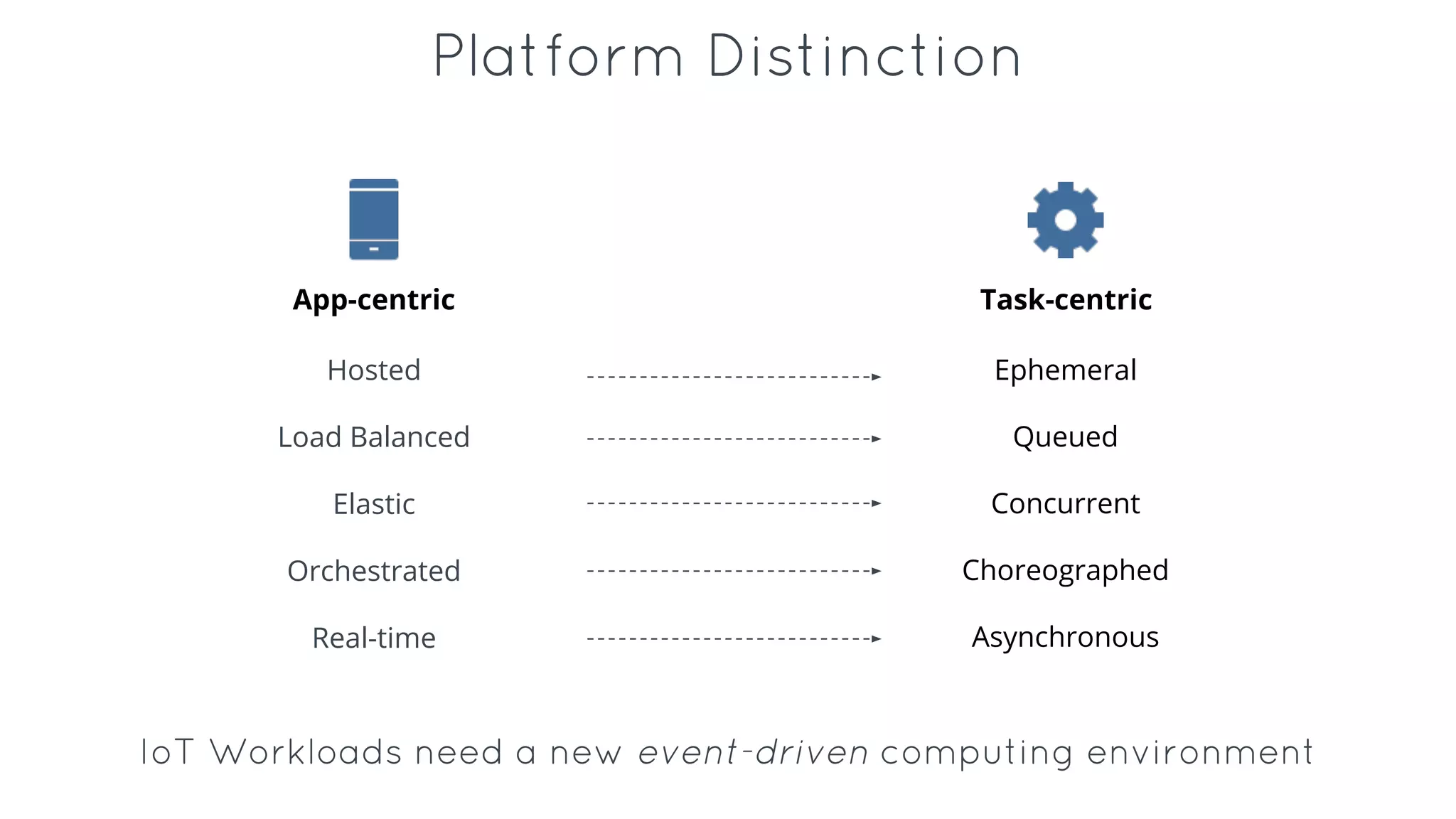
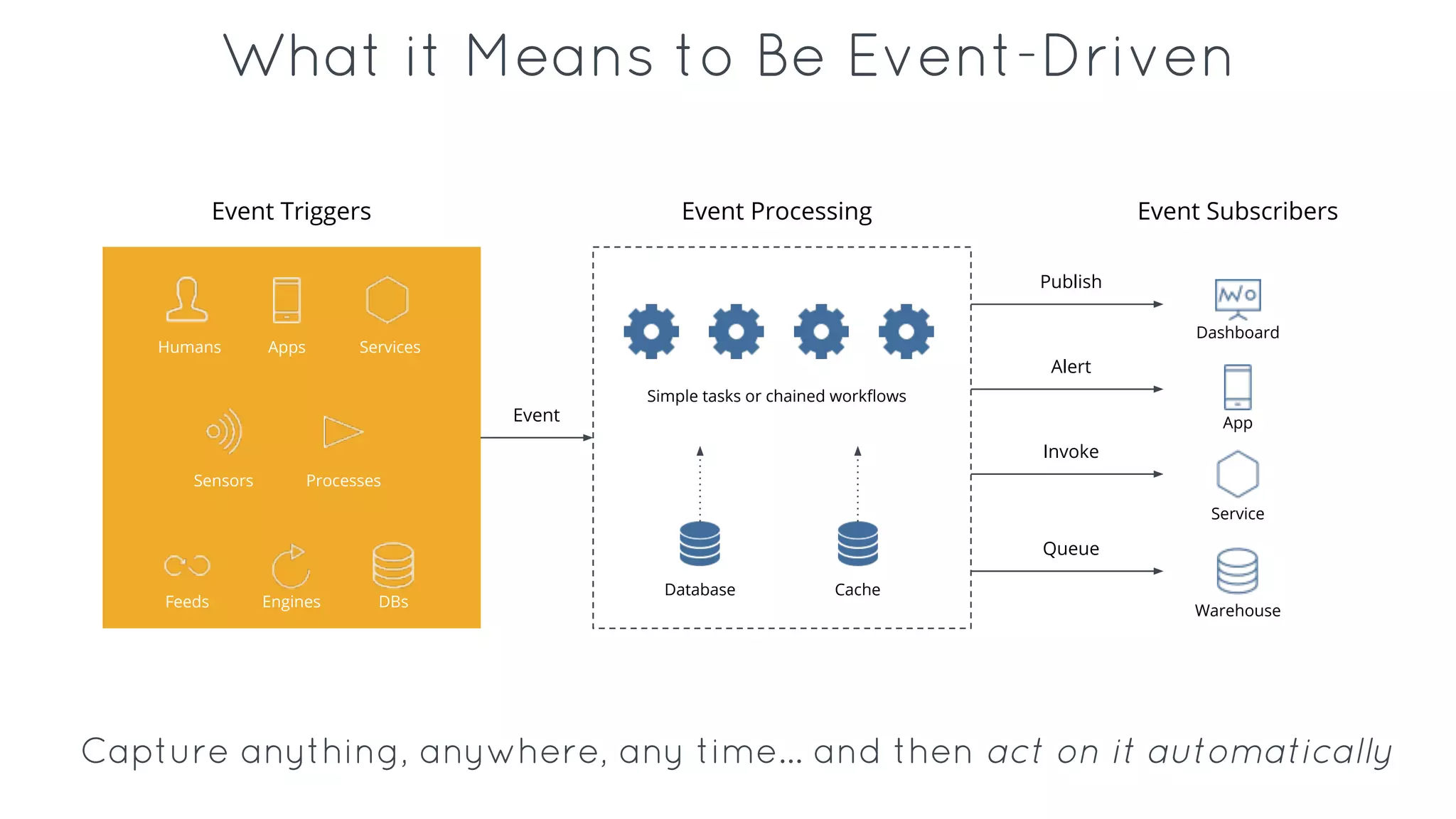
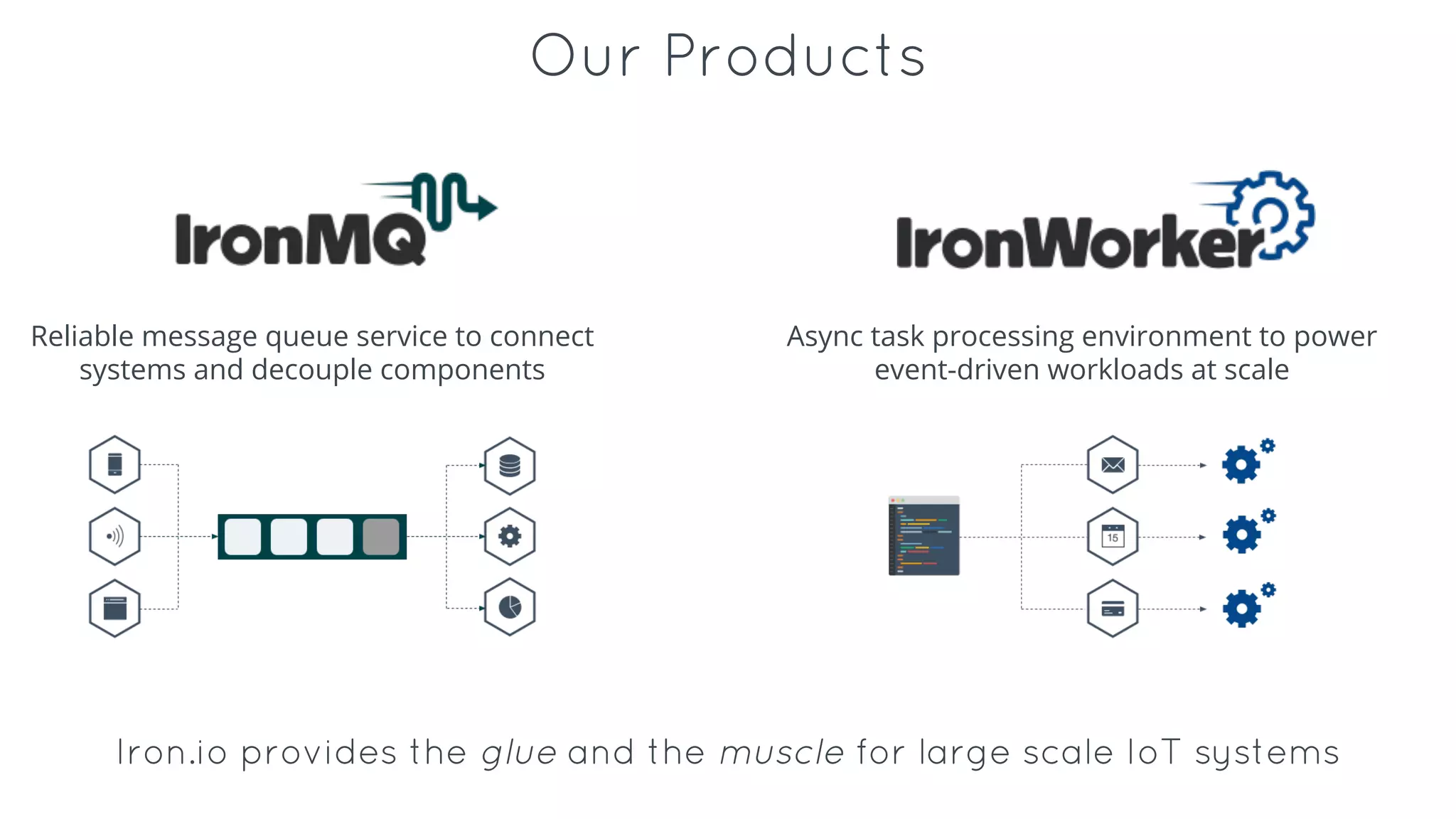
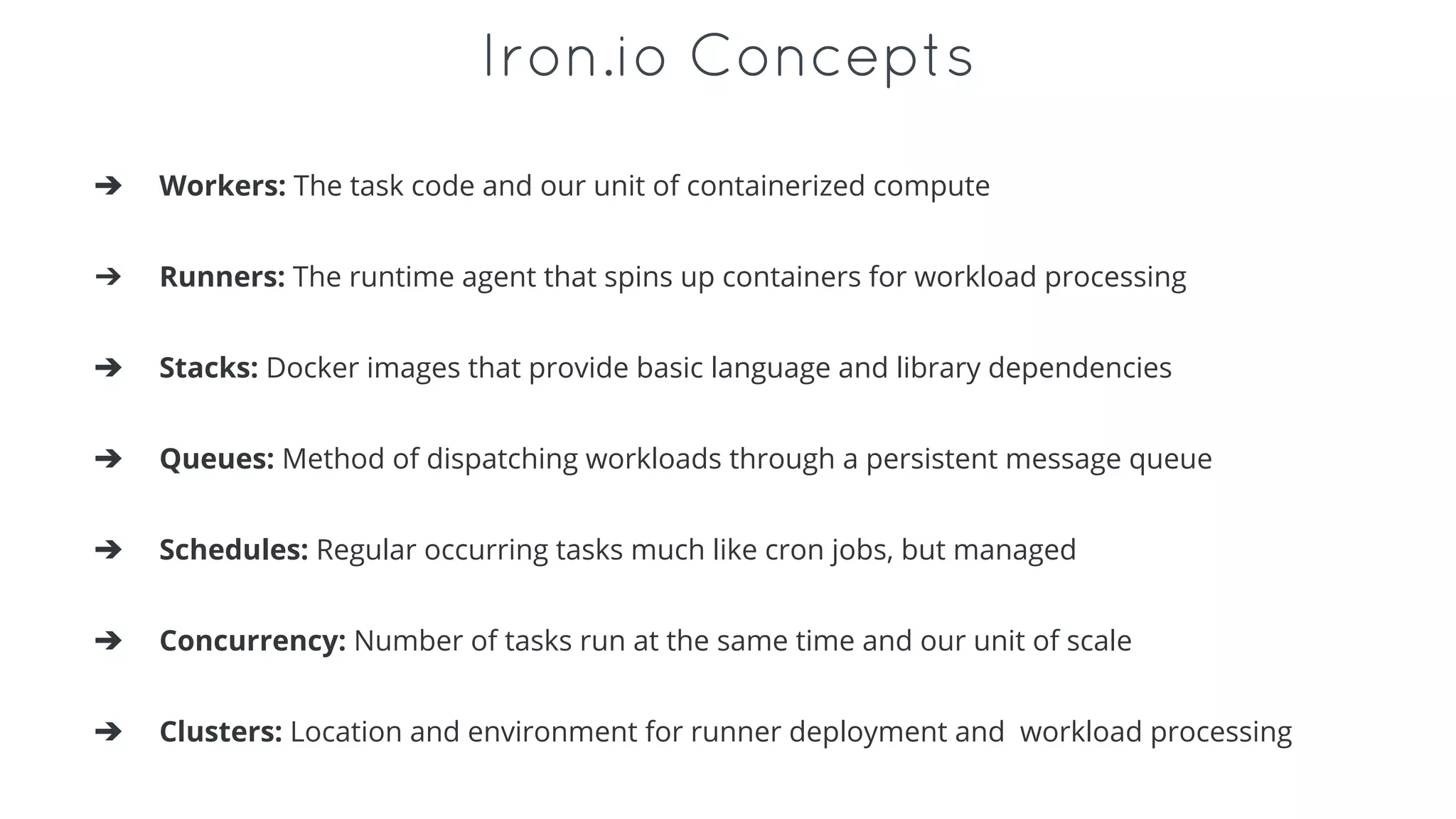
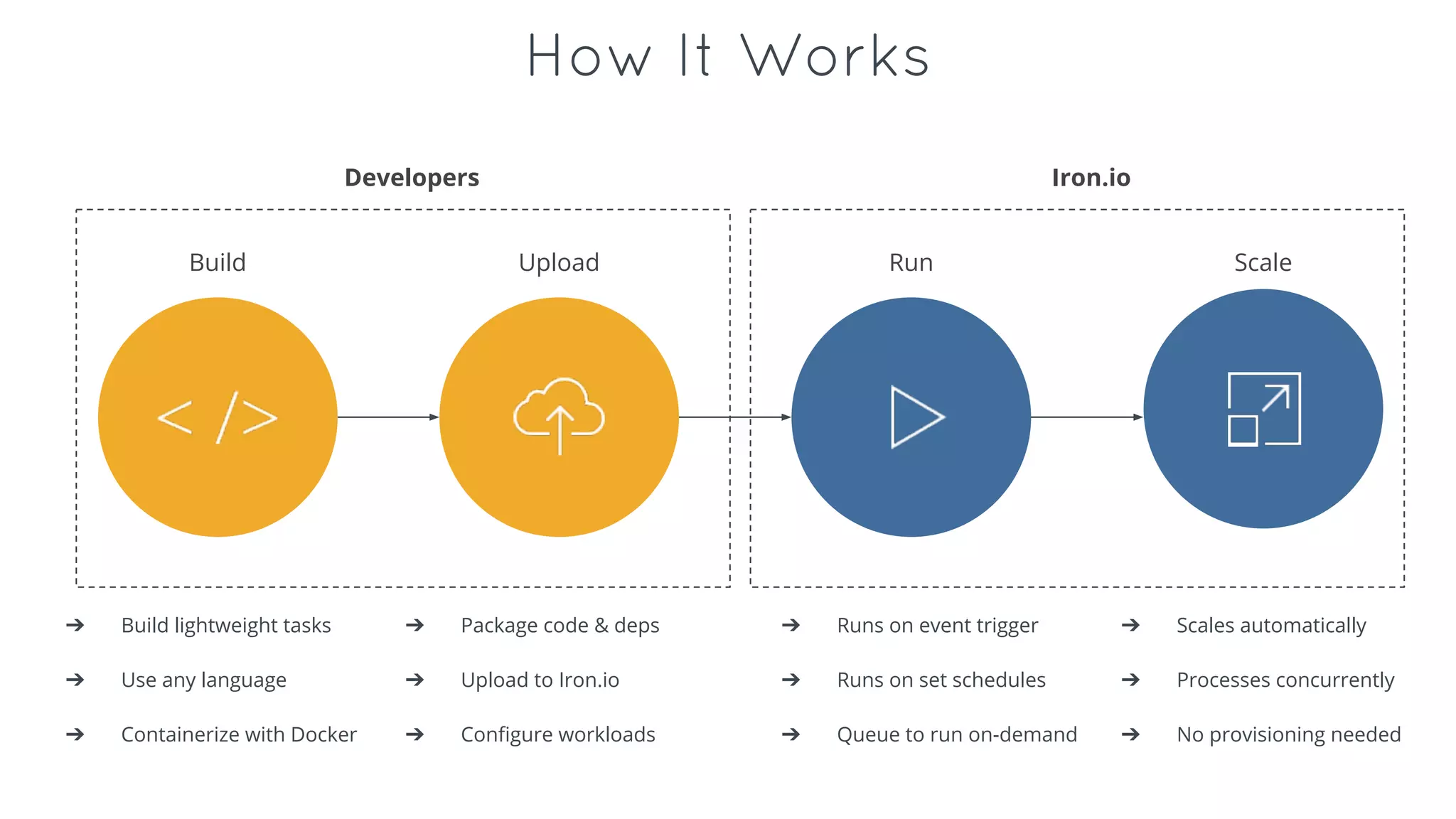
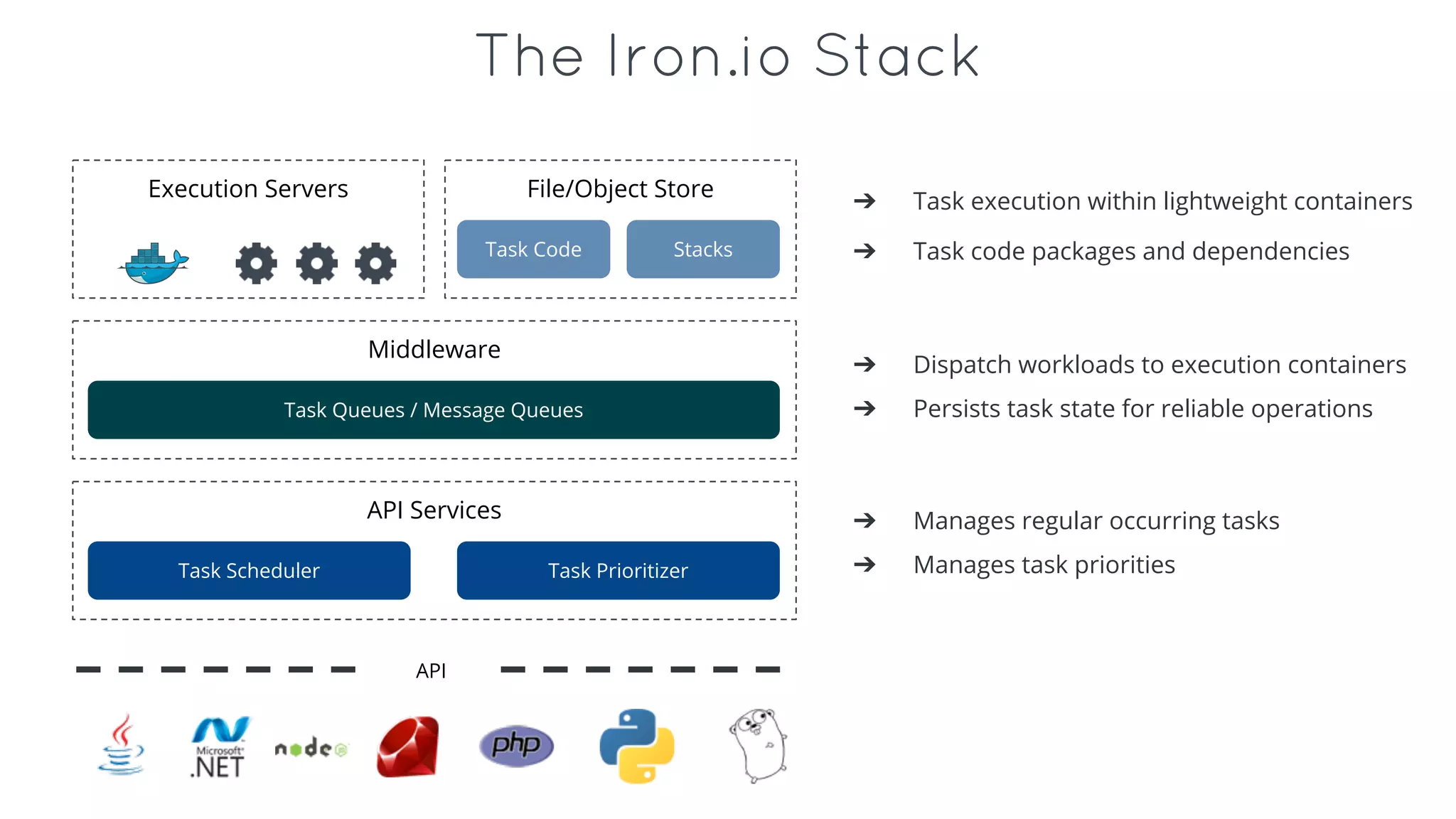
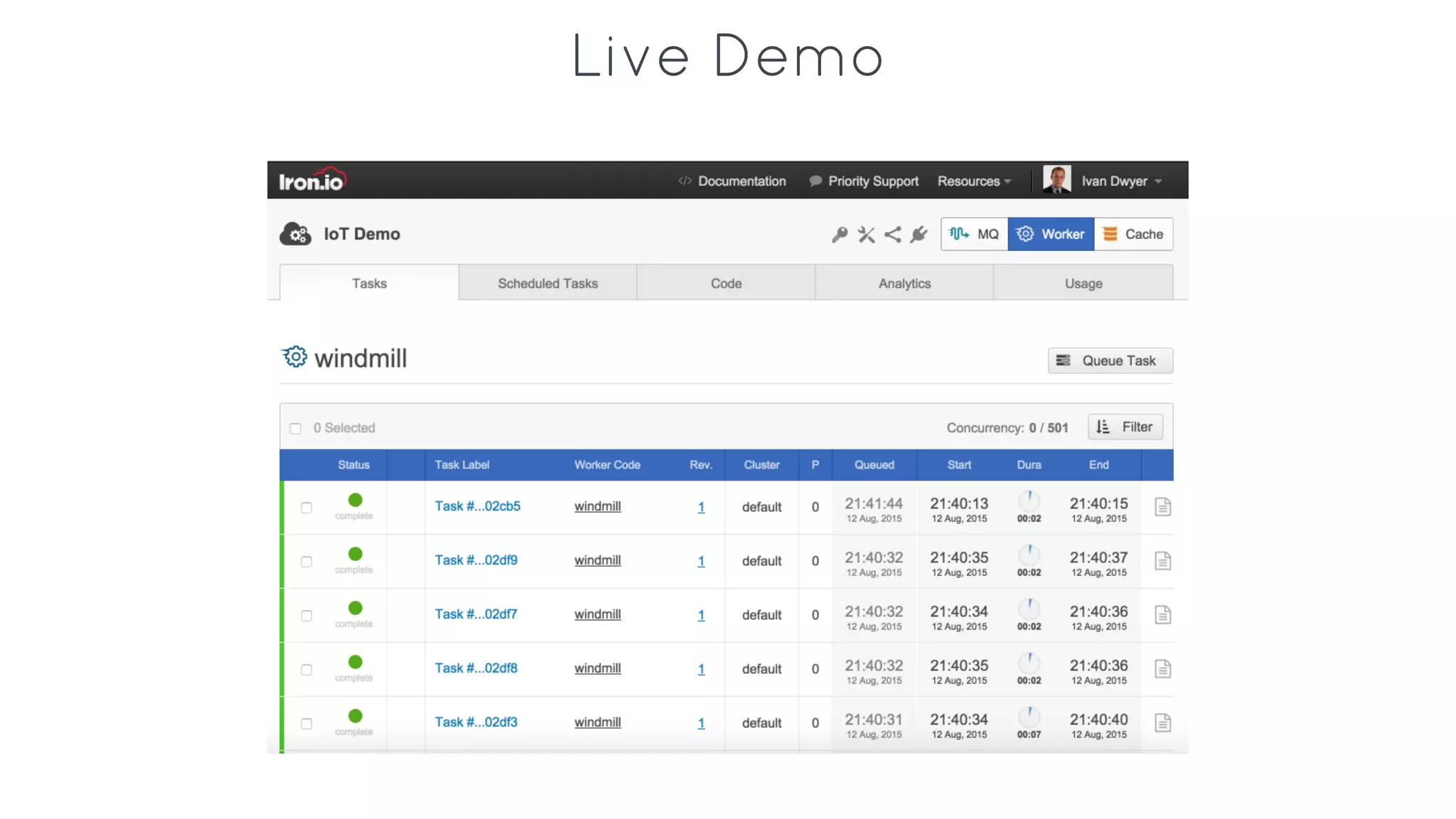
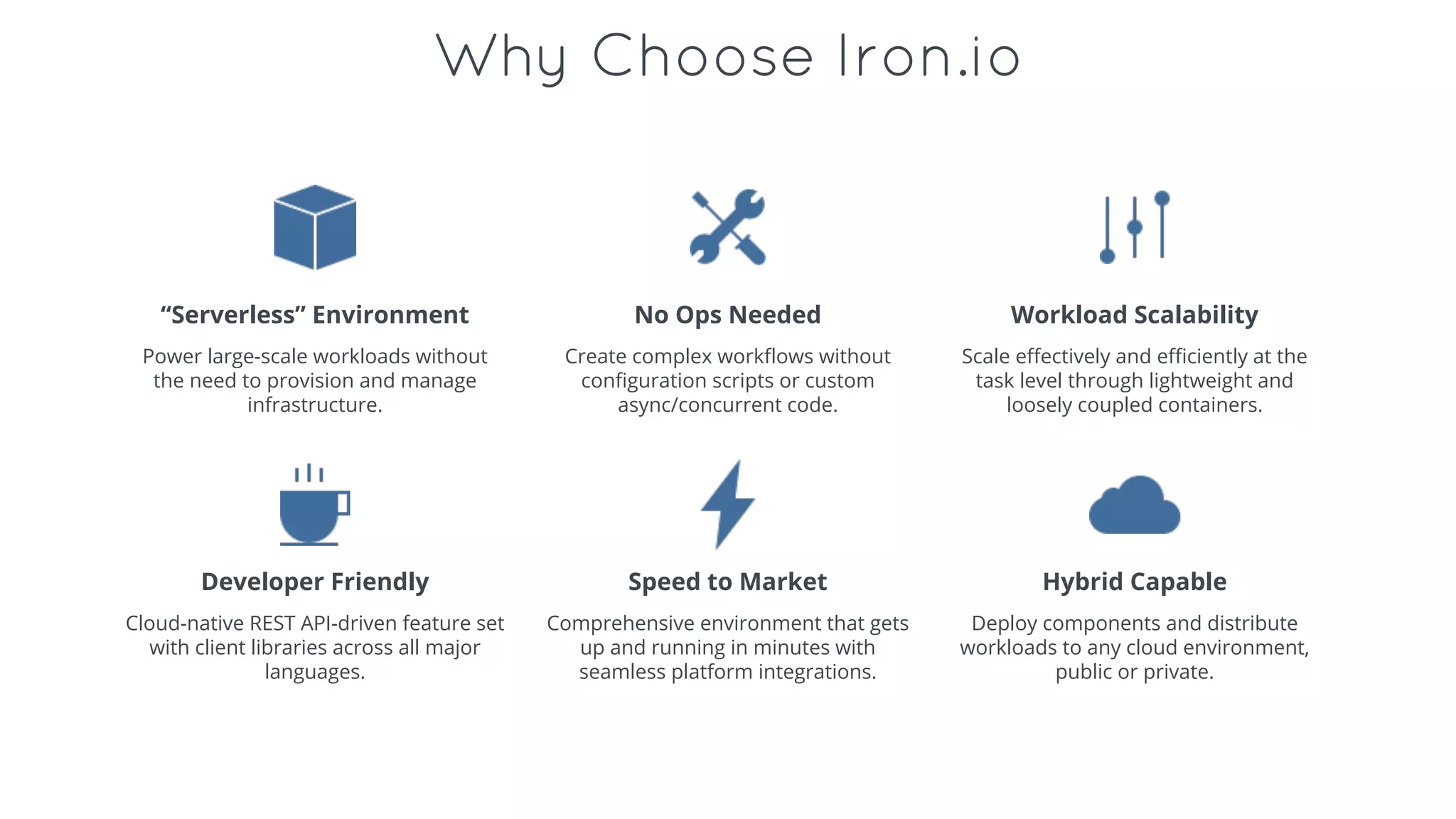
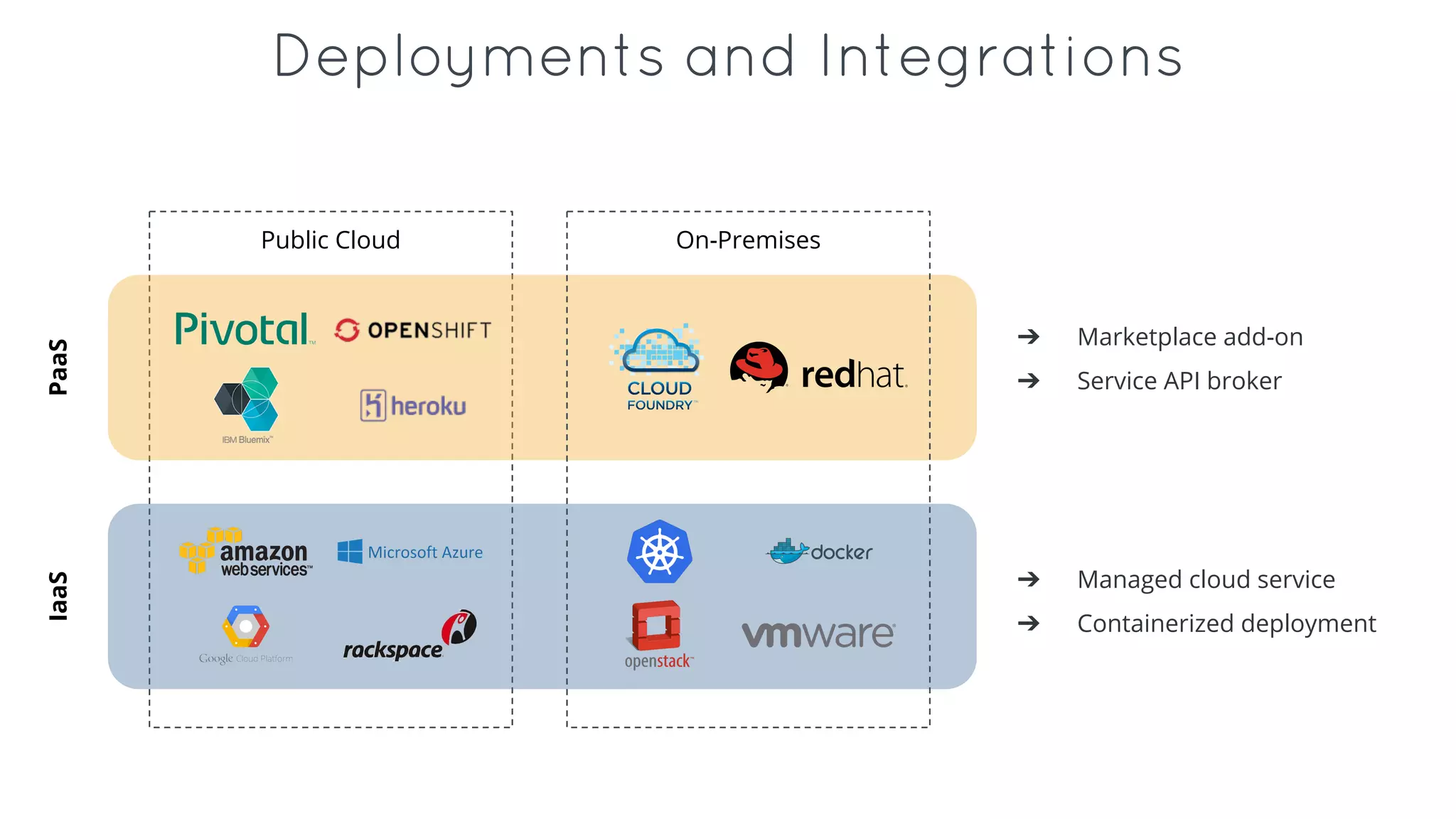
- Iron.io provides an event-driven computing platform as a service to process the large-scale, asynchronous workloads generated from IoT data in a scalable and reliable way without the need to manage infrastructure.
- It allows developers to easily build and deploy containerized tasks across public clouds and private