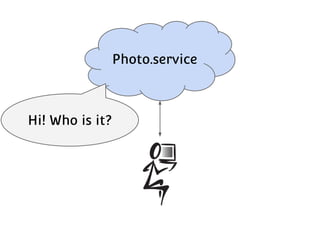
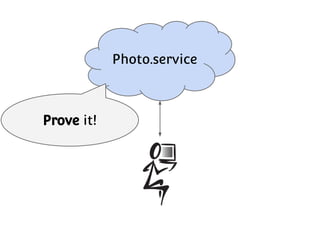
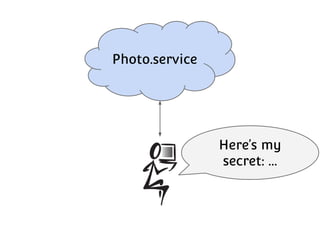
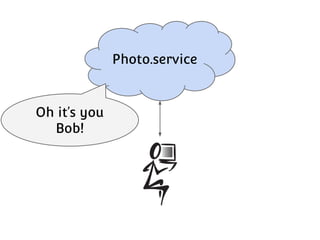
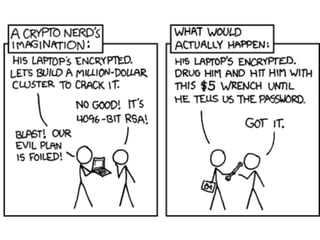
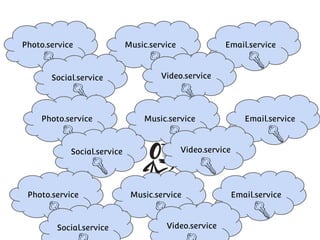
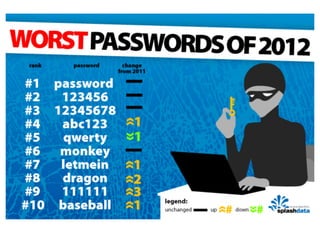
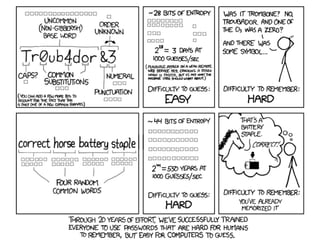
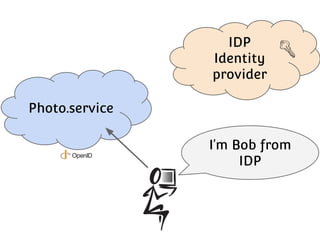
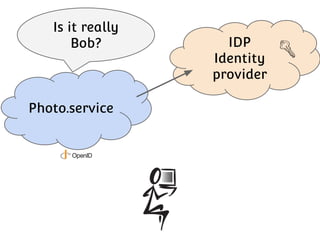
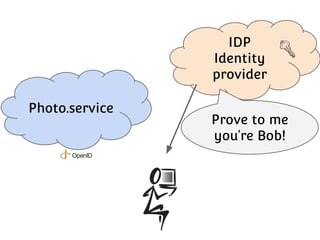
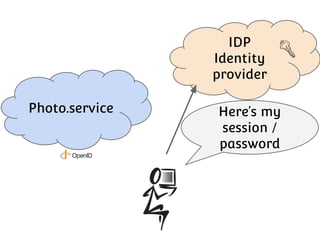
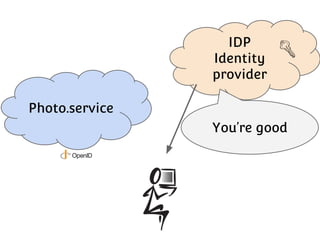
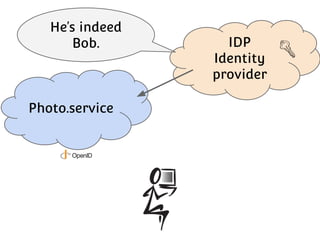
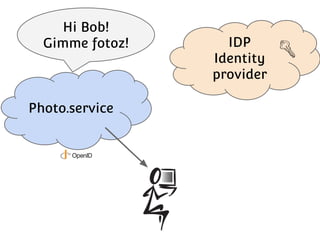
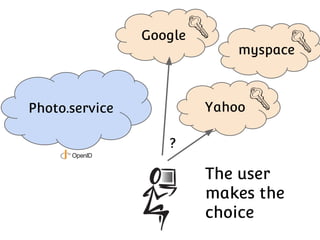
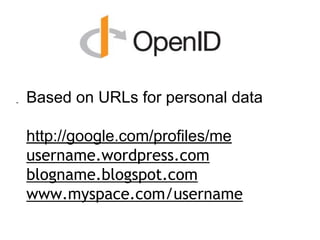
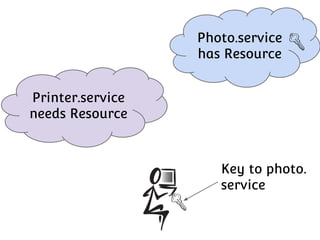
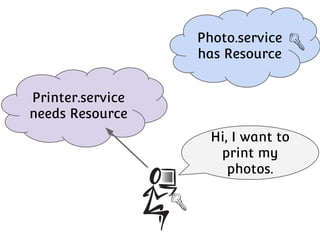
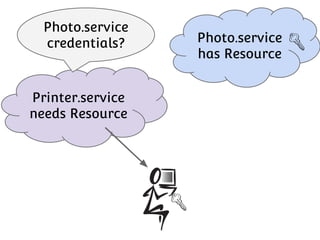
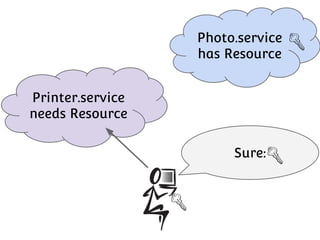
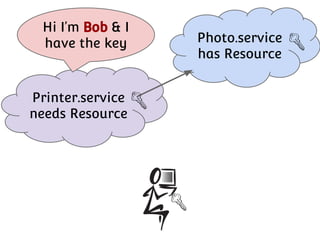
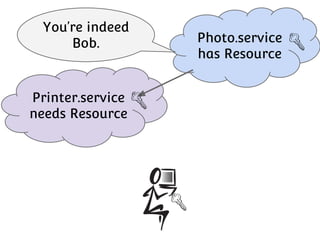
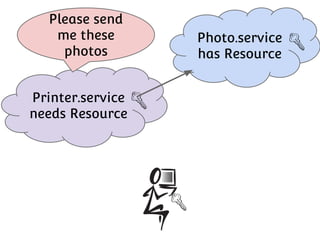
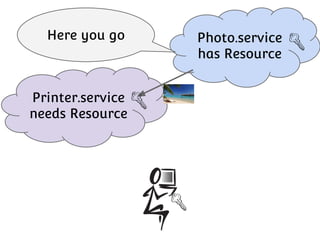
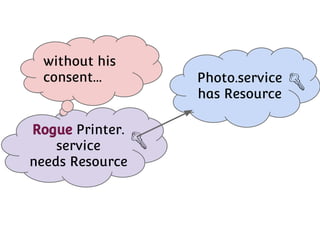
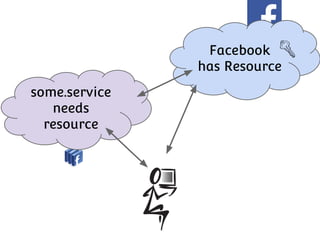
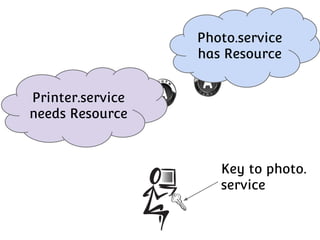
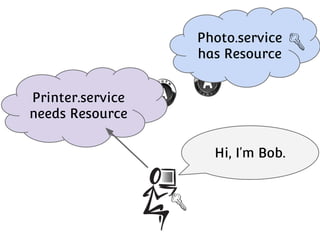
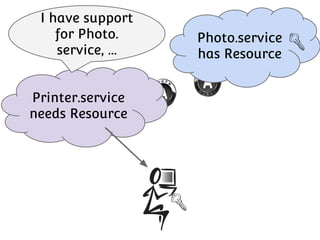
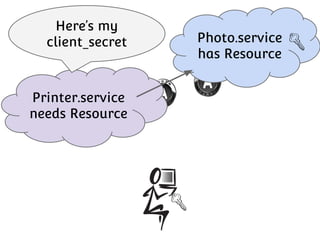
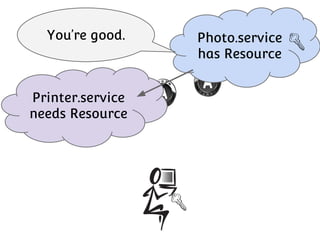
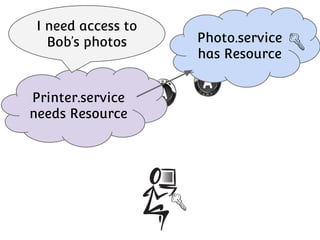
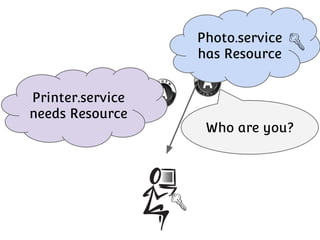
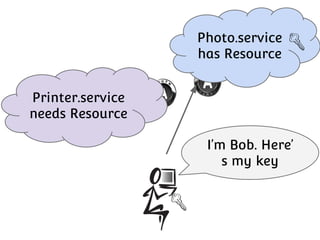
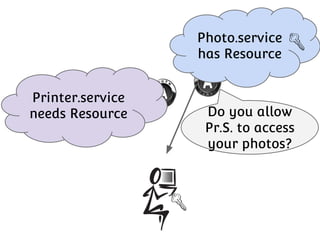
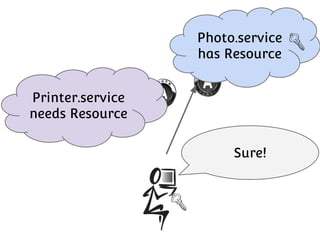
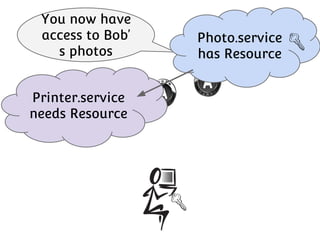
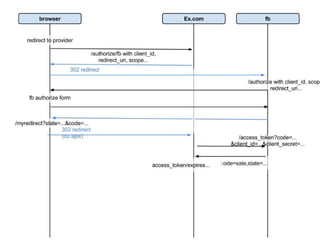
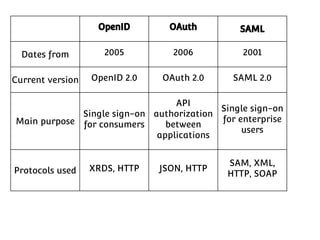
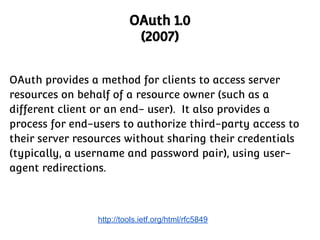
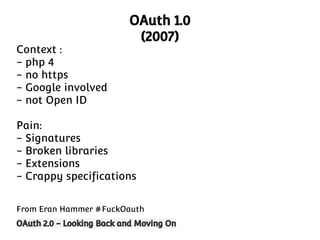
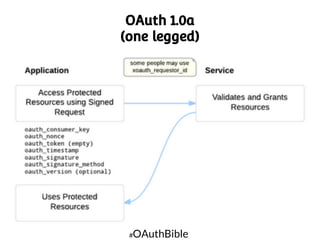
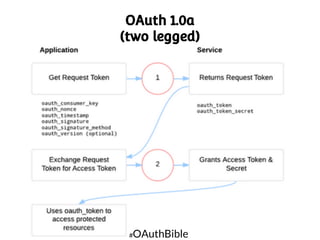
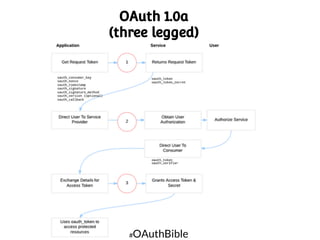
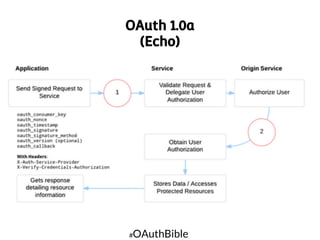
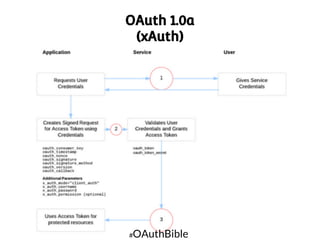
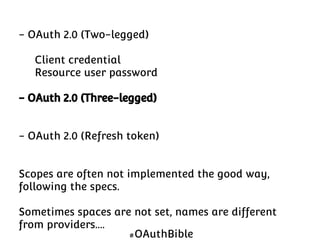
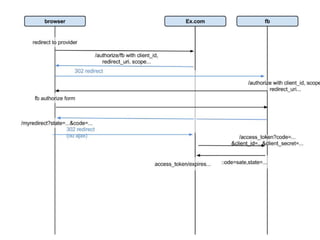
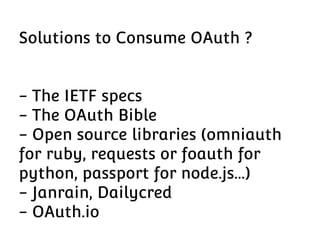
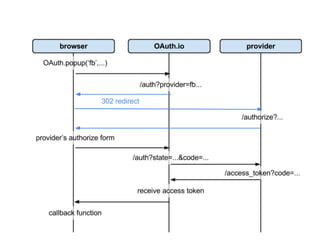
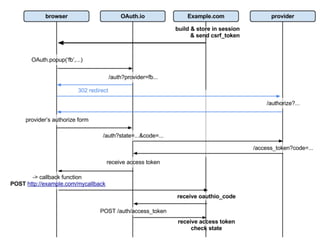
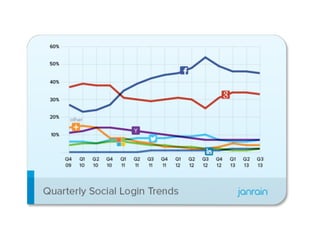
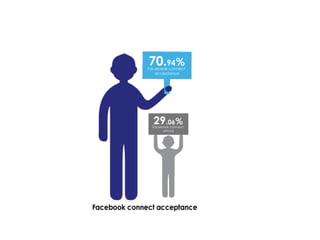
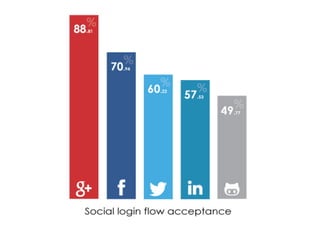
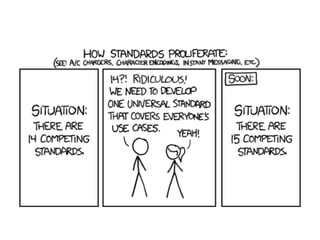
The document discusses the challenges of authentication and identity management through passwords and the emergence of single sign-on (SSO) solutions to enhance user experience and security. It explores the evolution of OAuth protocols, highlighting the differences between OAuth 1.0 and 2.0, and the importance of identity providers in granting access to user resources without sharing credentials. The author emphasizes the need for better user experience and security in authorization processes, while noting the fragmentation and limitations within current OAuth implementations.