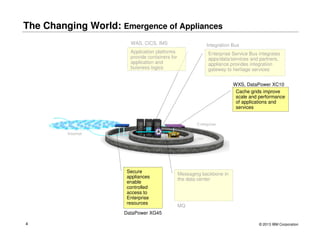
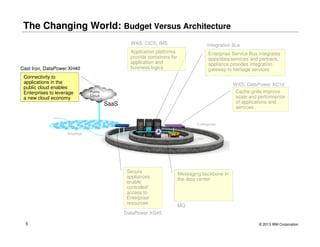
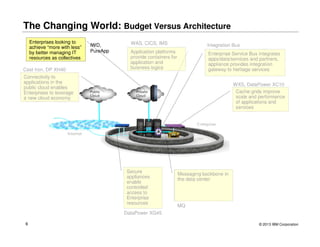
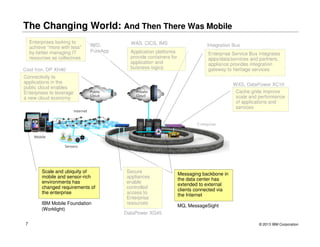
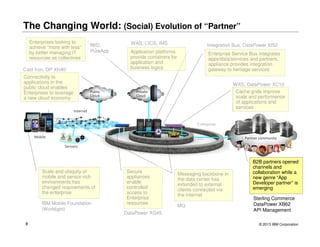
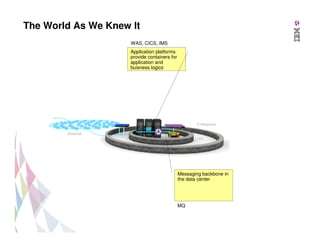
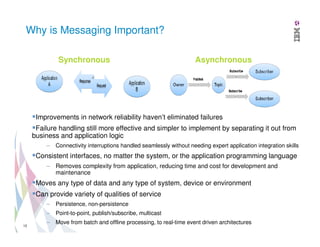
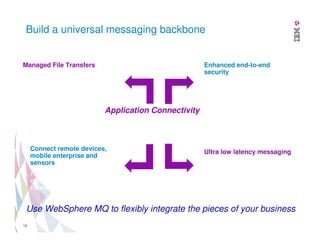
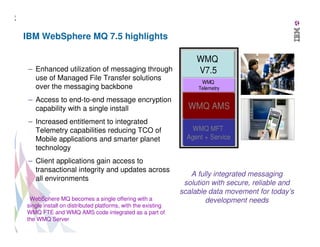
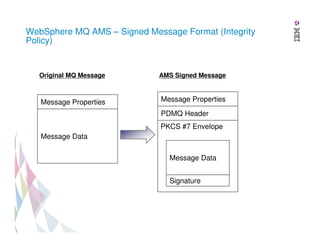
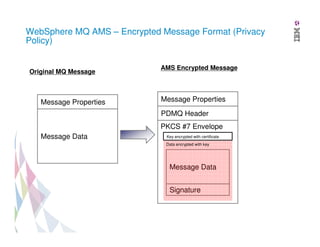
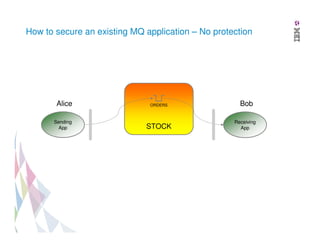
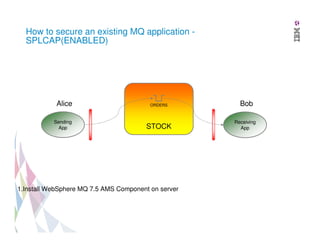
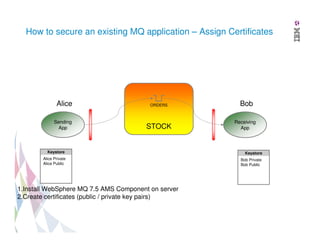
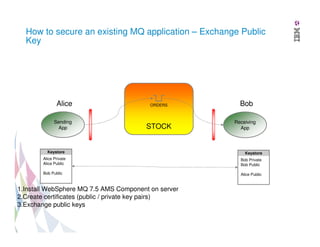
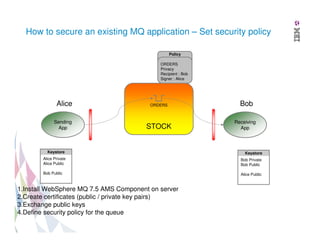
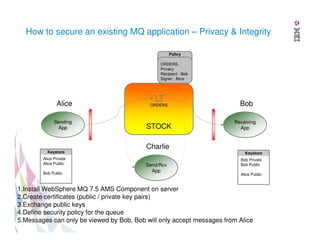
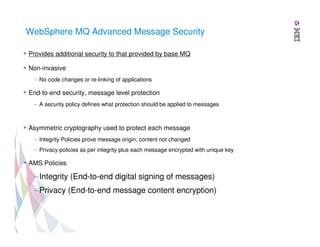
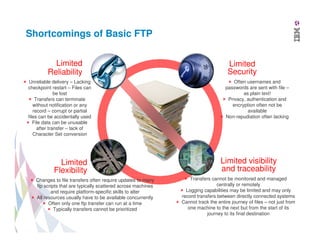
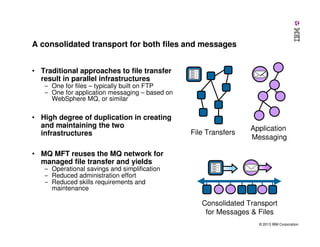
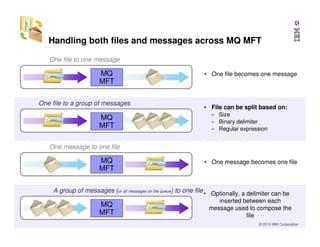
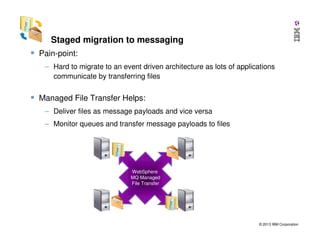
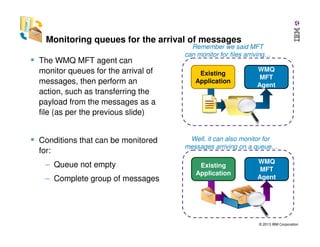
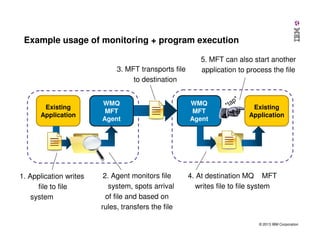
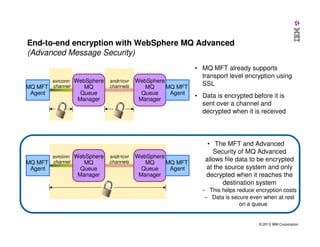
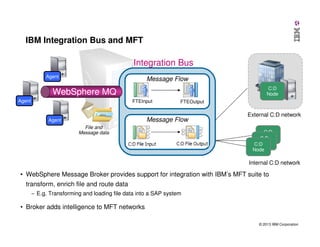
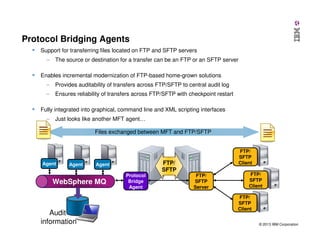
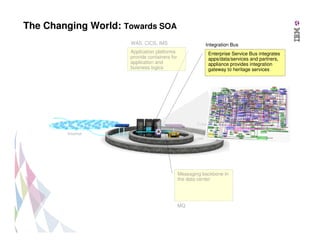
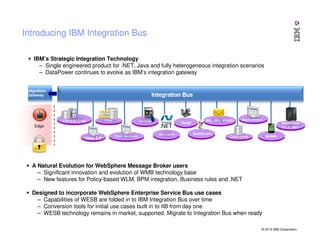
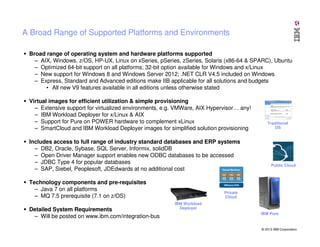
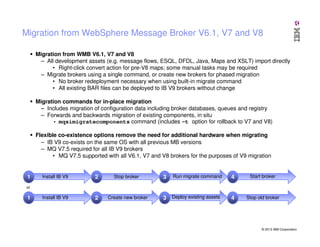
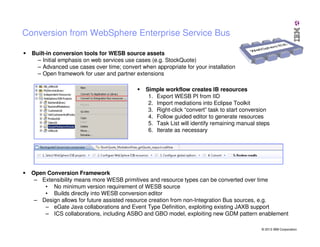
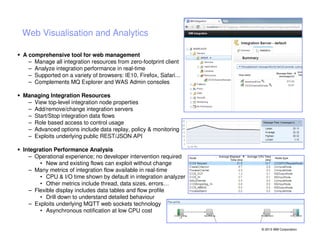
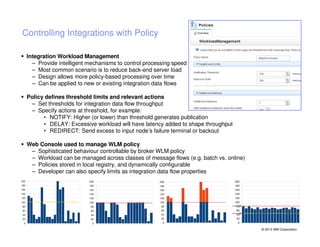
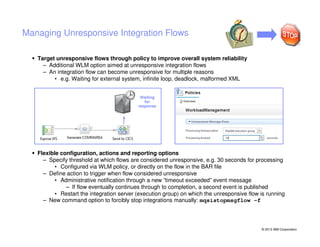
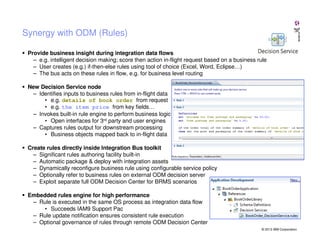
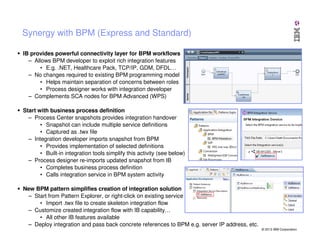
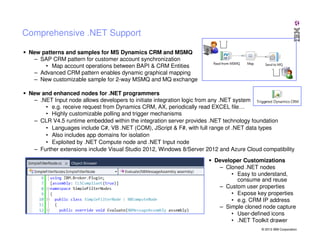
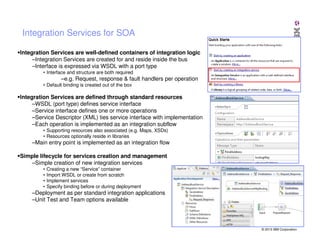
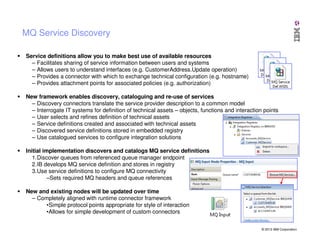
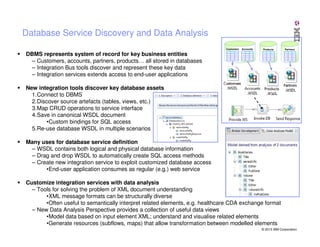
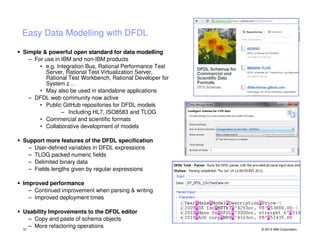
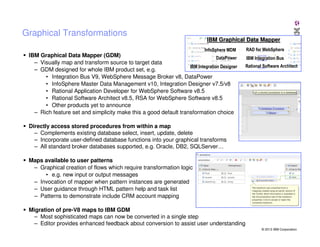
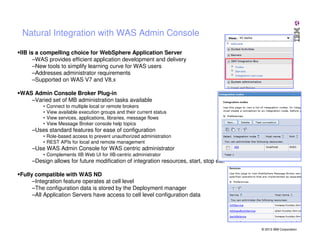
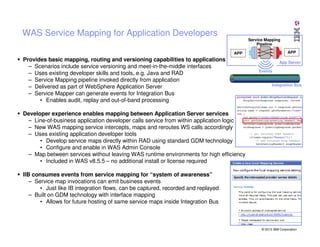
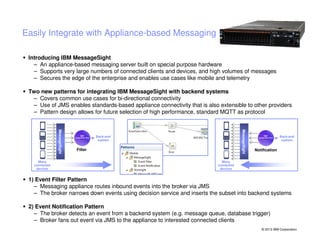
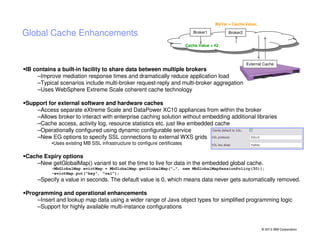
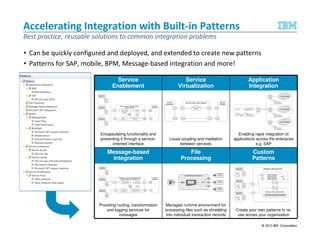
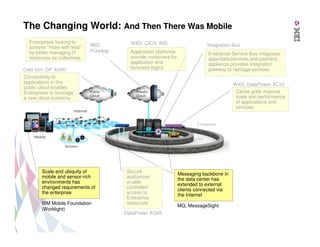
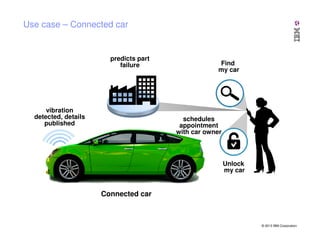
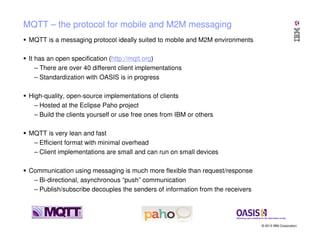
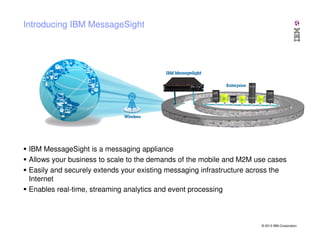
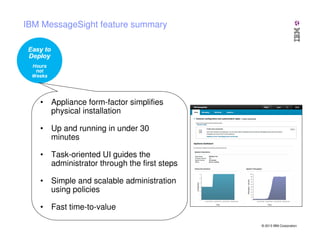
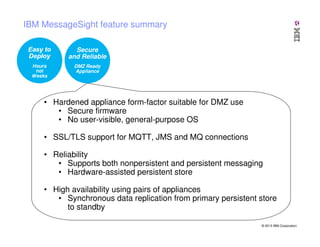
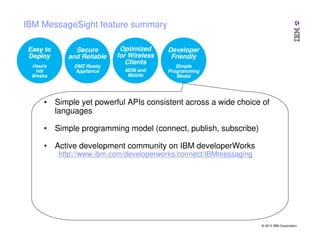
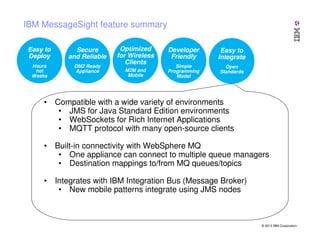
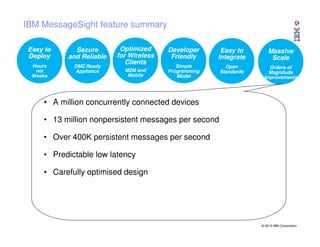
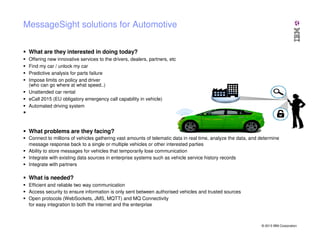
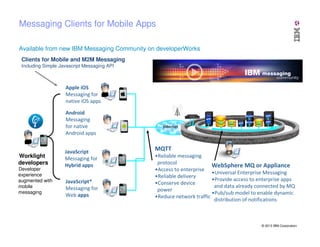
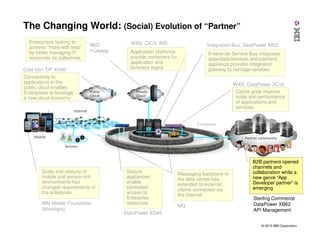
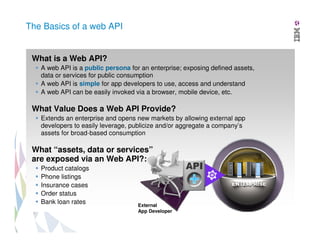
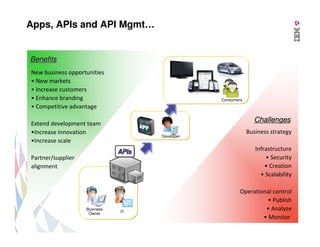
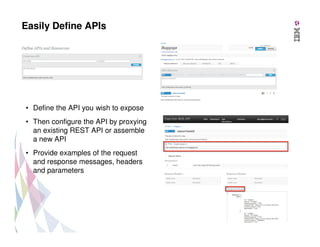
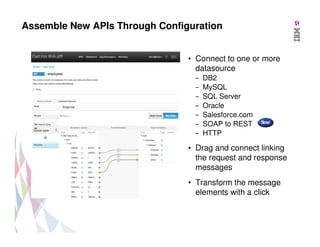
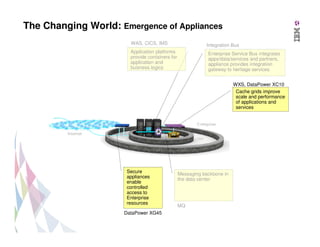
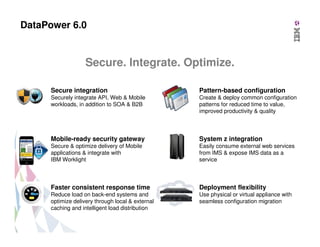
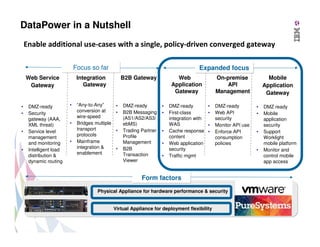
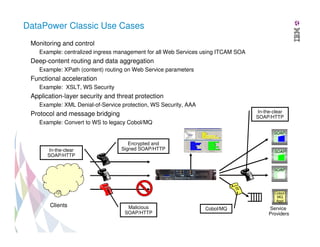
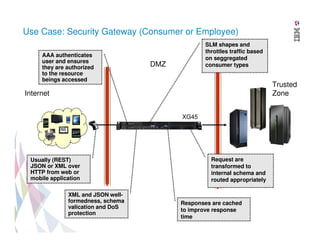
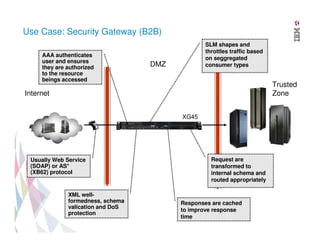
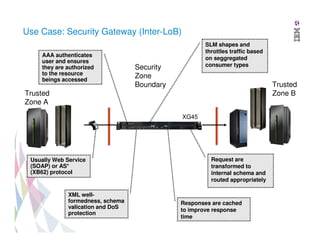
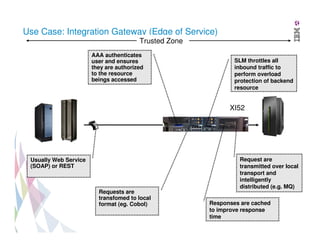
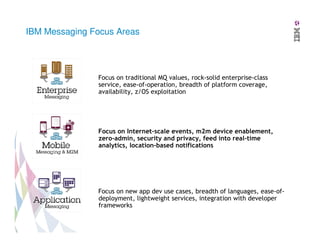
The document discusses IBM's integration and messaging technologies, focusing on the evolution from traditional application platforms to service-oriented architecture (SOA) and cloud computing. It highlights various IBM products, such as WebSphere MQ and integration bus, and emphasizes the importance of secure, reliable messaging and file transfer in modern enterprises. The content outlines how enterprises can adapt to new requirements driven by mobile and cloud environments while leveraging existing IT resources effectively.