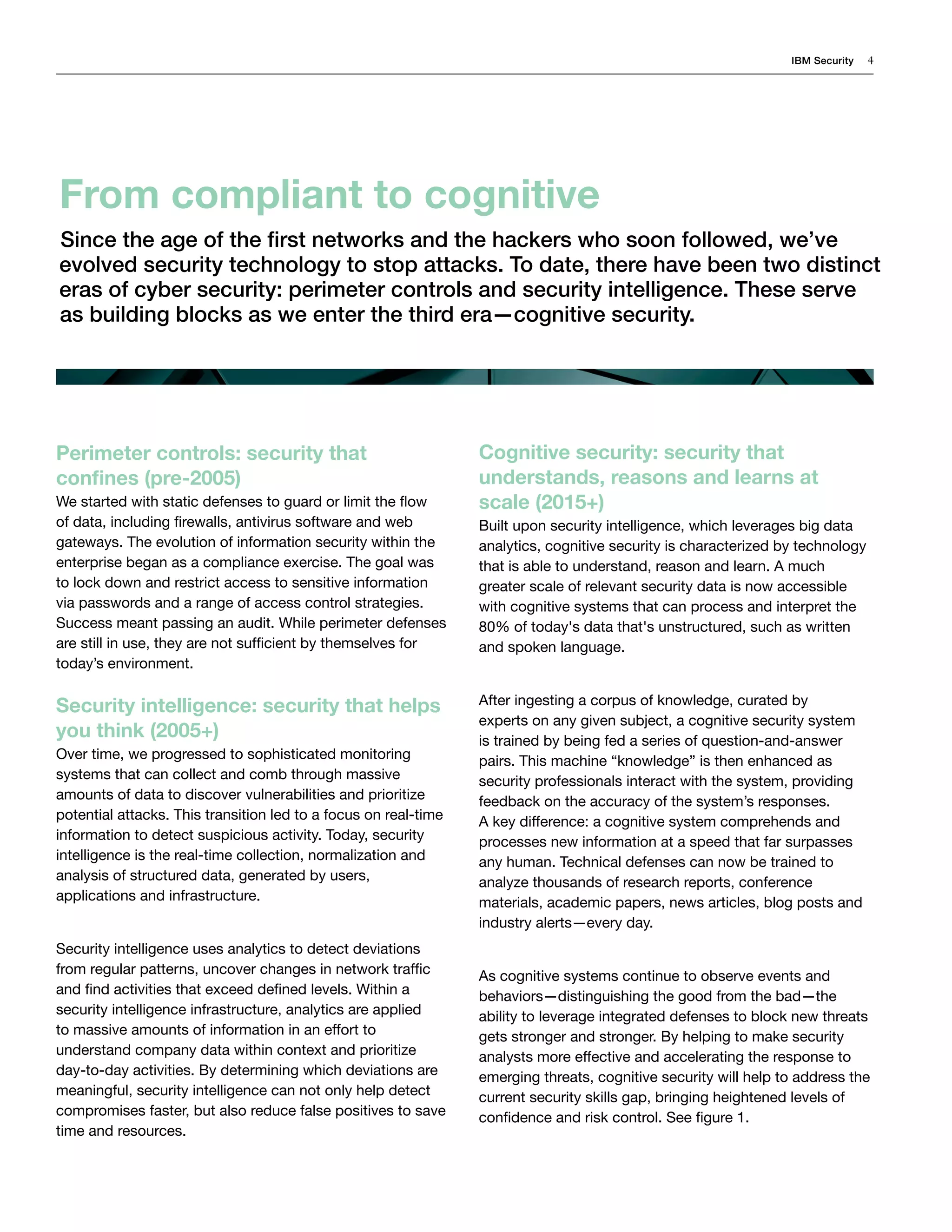
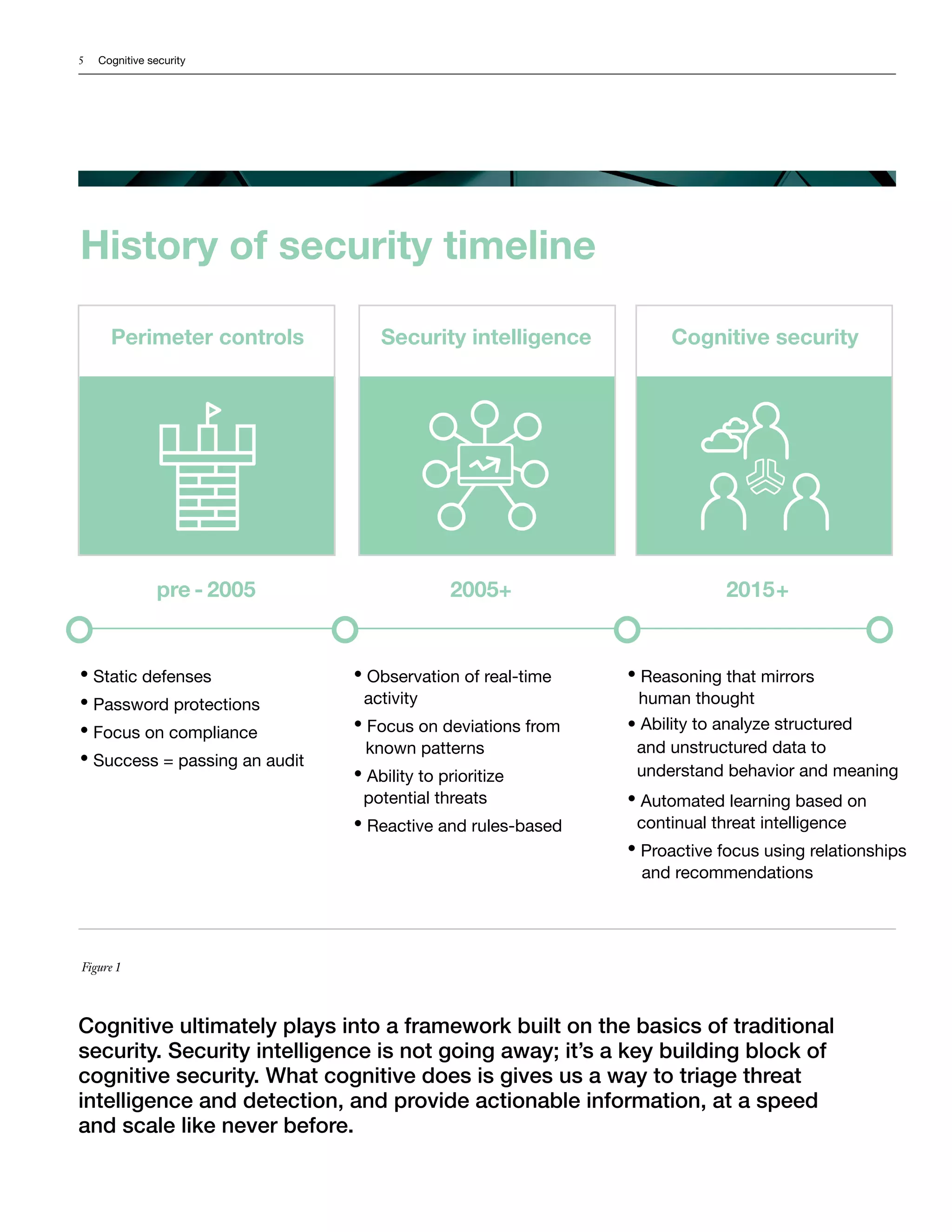
Cognitive security uses cognitive systems to analyze large amounts of structured and unstructured security data to understand threats and provide recommendations to security analysts. It learns from data and interactions to enhance its knowledge over time. This allows it to process more data, including unstructured sources like text, than traditional rule-based systems. Cognitive security aims to help analysts respond faster by automating some tasks and providing new insights. It also seeks to increase organizations' security by adapting quickly to emerging threats.