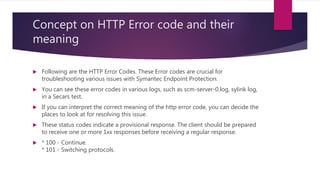
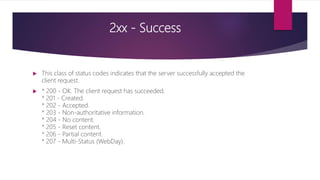
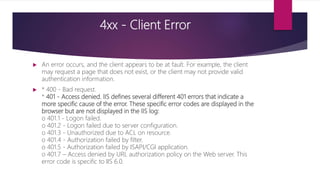
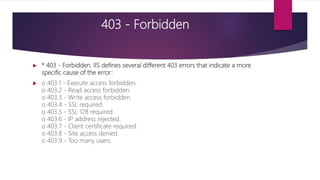
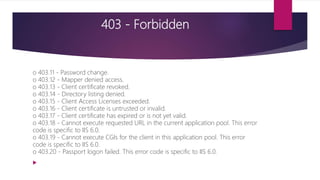
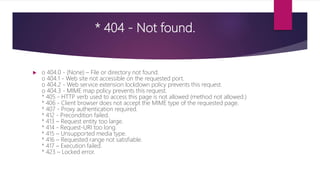
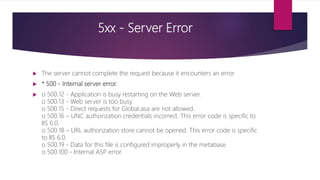
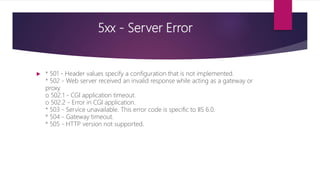
The document provides a comprehensive overview of HTTP error codes, detailing their meanings and significance in troubleshooting issues related to Symantec Endpoint Protection. It categorizes errors into five classes: informational (1xx), success (2xx), redirection (3xx), client errors (4xx), and server errors (5xx), each with specific examples and descriptions. Understanding these codes helps in diagnosing problems effectively by indicating what the client should do or what went wrong.