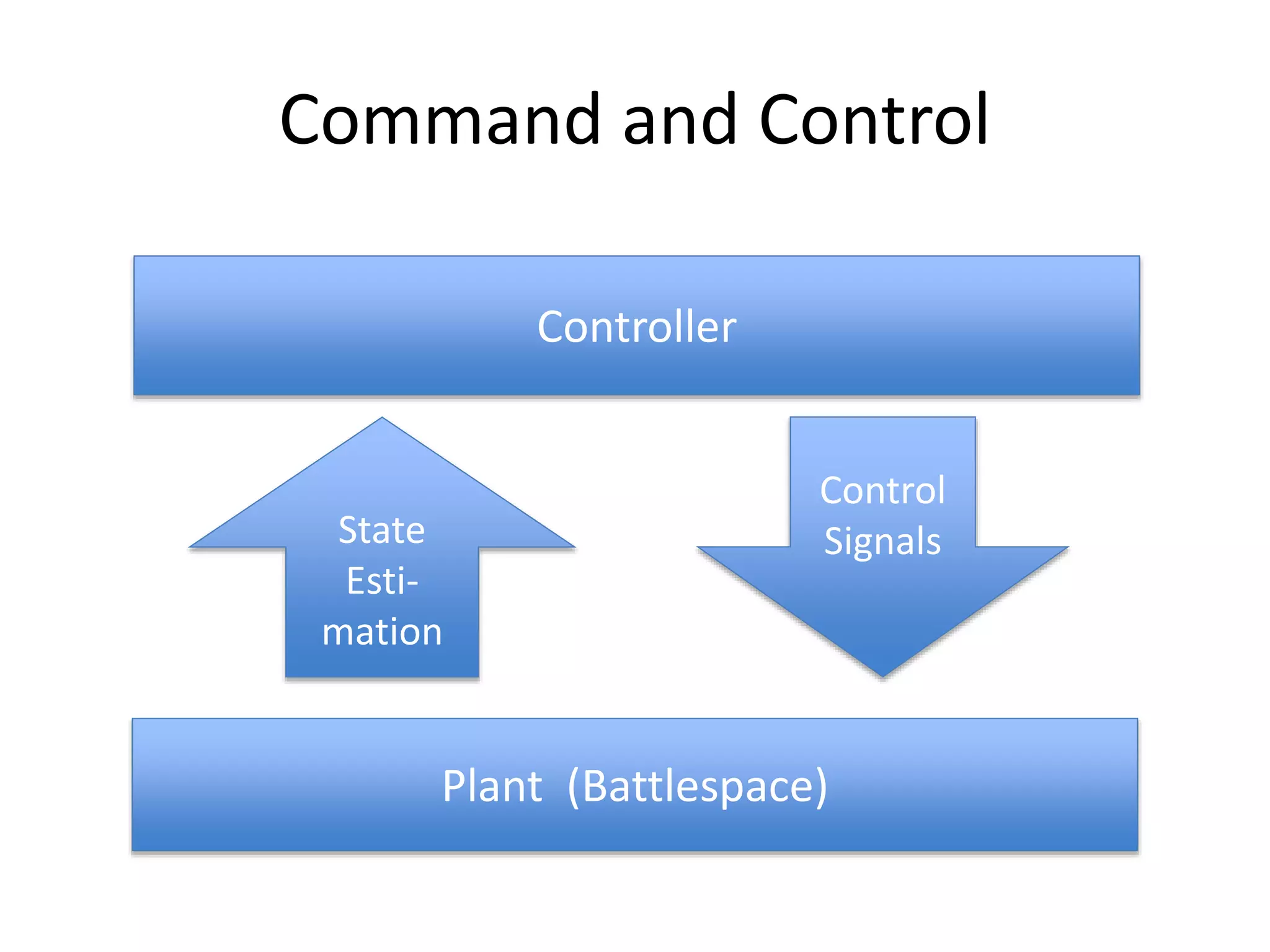
The document discusses Julian Assange's views on conspiracies, defining them as emergent properties of closed information networks rather than deliberate plots. It illustrates how such networks operate through secrecy and information exchange among participants, often against the benefit of broader society. Assange argues that dismantling conspiracies requires targeting their communication flows and that conspiracies, by their nature, prioritize their survival over the common good.

![Assange on Networks
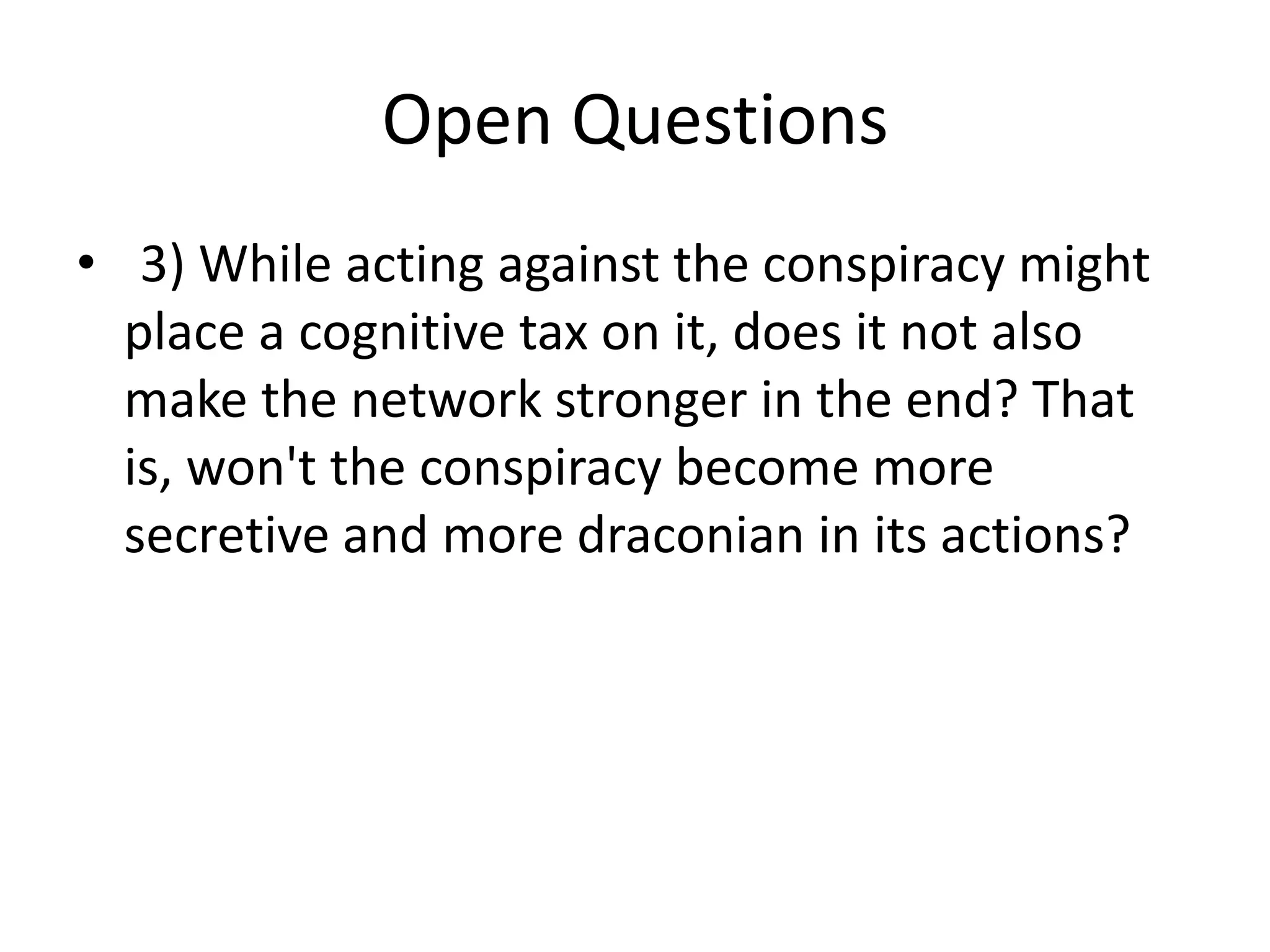
• “Call the twine connecting two nails a link [in
network theory an ‘edge’]. Unbroken twine
means it is possible to travel from any nail to
any other nail via twine and intermediary
nails...Information flows from conspirator to
conspirator [in network theory a ‘path’].”](https://image.slidesharecdn.com/hacktivism6-200625033543/75/Hacktivism-6-Networks-and-Conspiracy-22-2048.jpg)
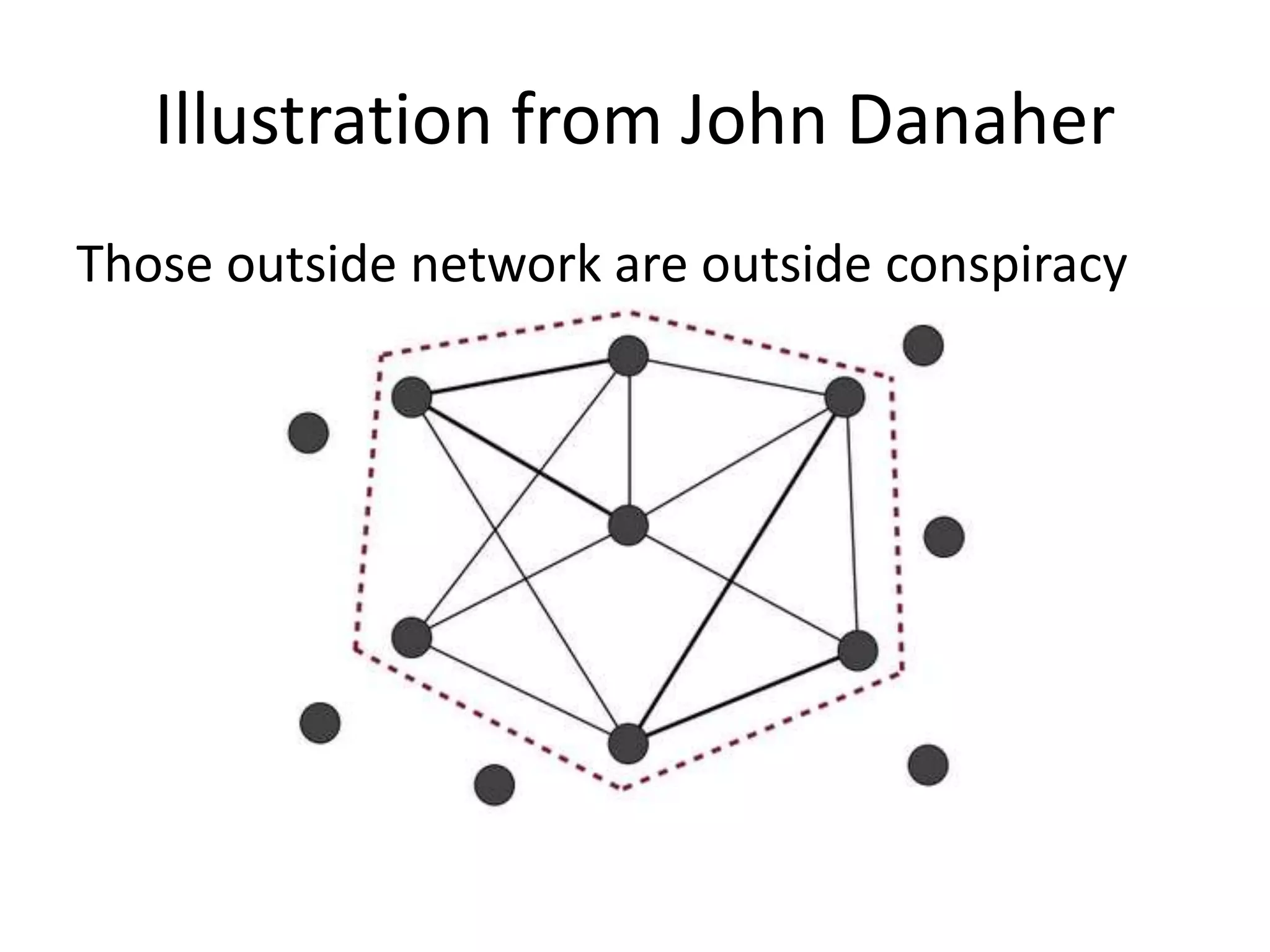
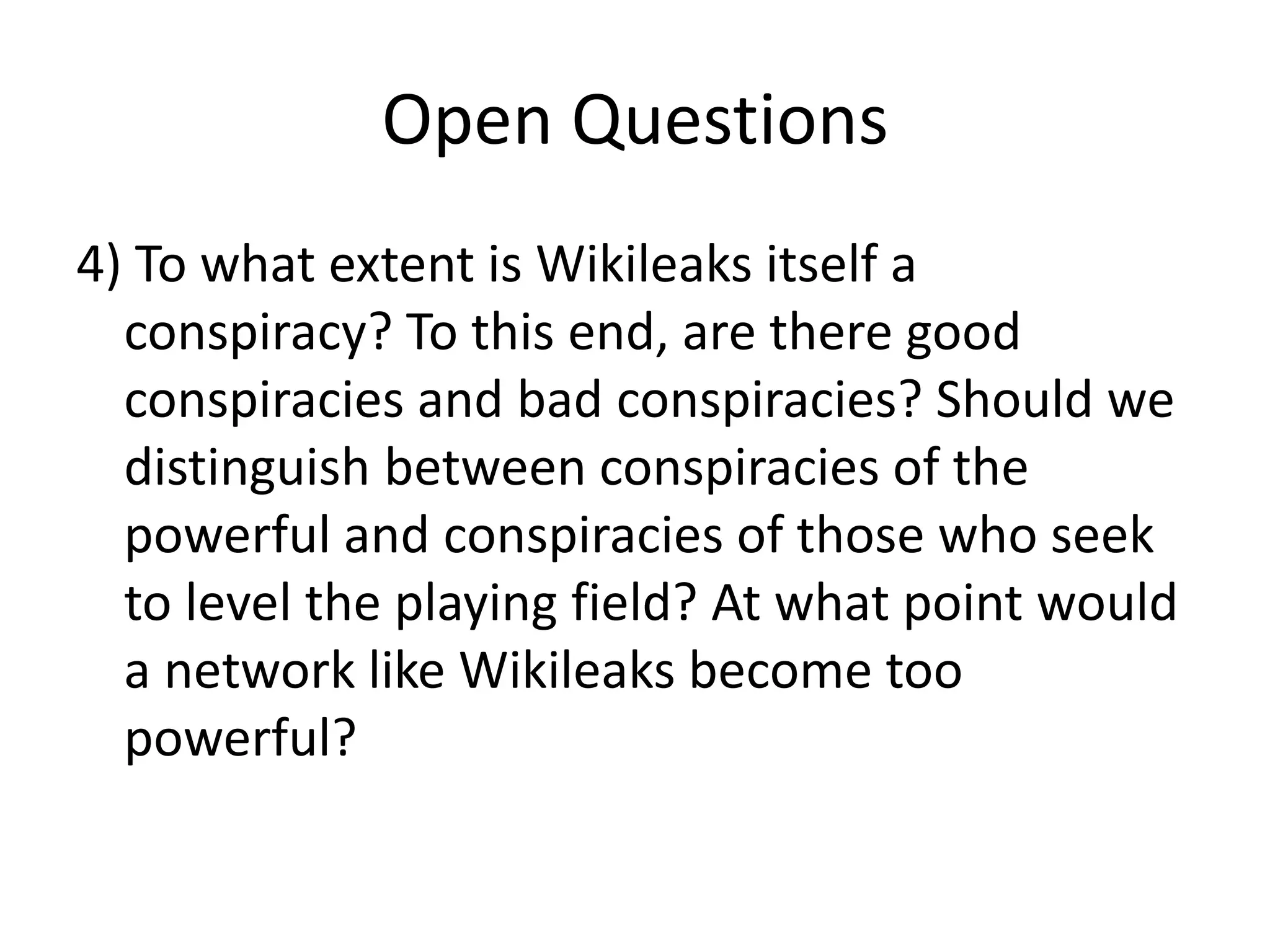
![Assange on Networks
• “Not every conspirator trusts or knows every
other conspirator even though all are
connected. Some are on the fringe of the
conspiracy, others are central and
communicate with many conspirators and
others still may know only two conspirators
but be a bridge between important sections or
groupings of the conspiracy…” [Conspiracy as
Governance, p. 2] [i.e. it is a ‘small worlds
network’]](https://image.slidesharecdn.com/hacktivism6-200625033543/75/Hacktivism-6-Networks-and-Conspiracy-23-2048.jpg)
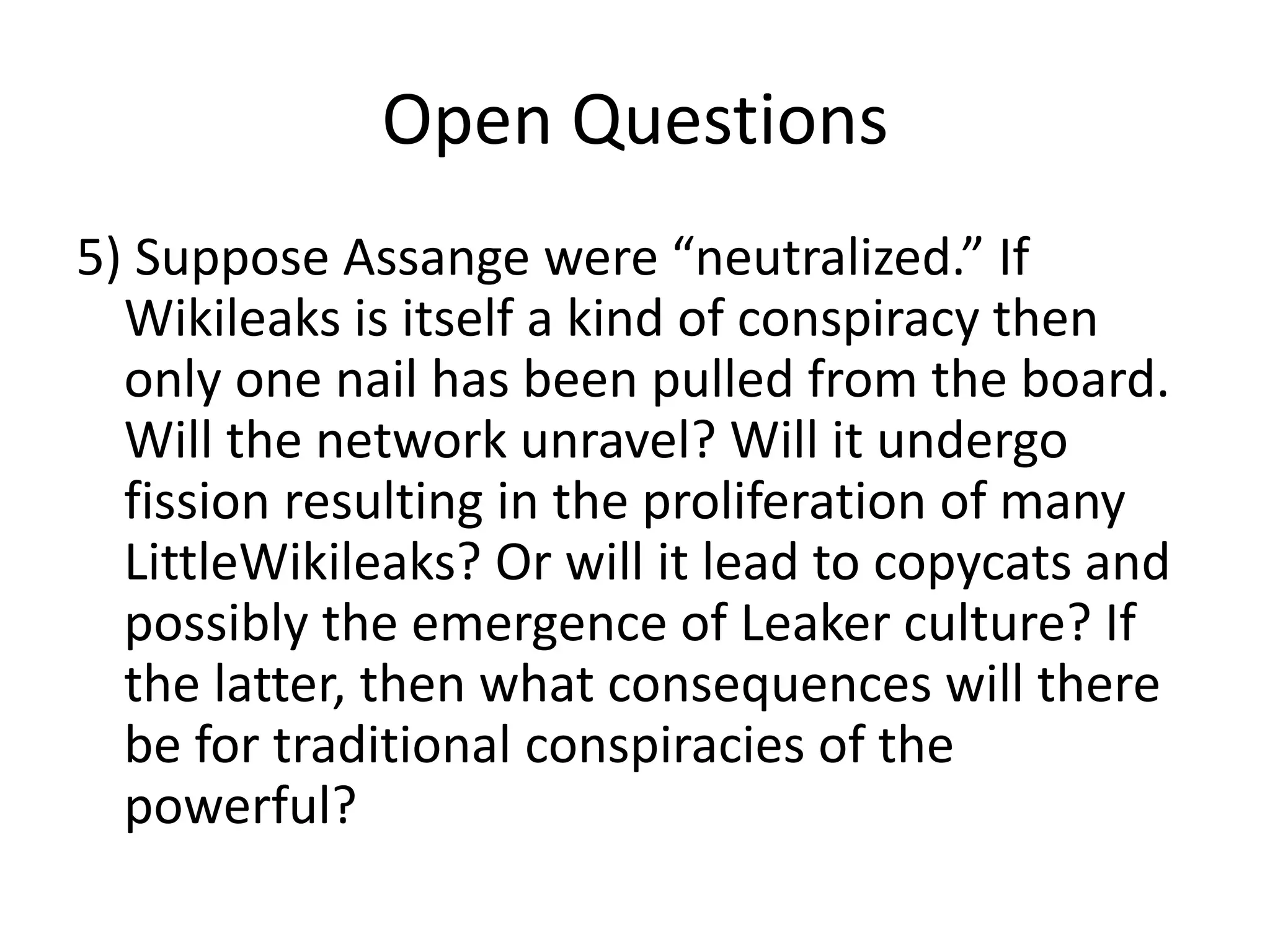
![Conspiracies as Cognitive Devices
“Conspiracies are cognitive devices. They are able
to outthink the same group of individuals acting
alone. Conspiracies take information about the
world in which they operate (the conspiratorial
environment), pass through the conspirators and
then act on the result. We can see conspiracies as
a type of device that has inputs (information
about the environment), a computational
network (the conspirators and their links to each
other) and outputs (actions intending to change
or maintain the environment).” ["Conspiracy as
Govenance", p. 3]](https://image.slidesharecdn.com/hacktivism6-200625033543/75/Hacktivism-6-Networks-and-Conspiracy-27-2048.jpg)

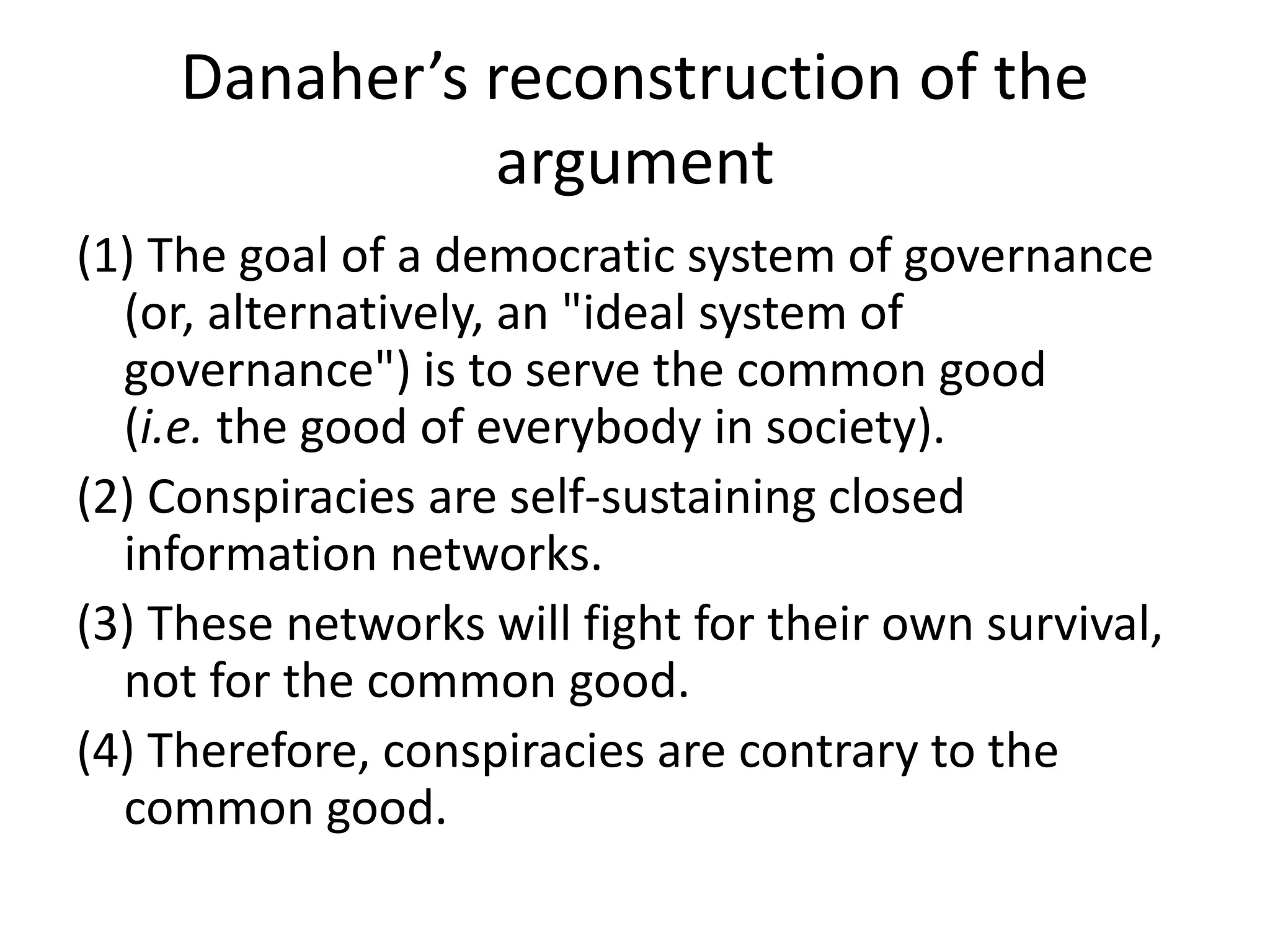
![Assange:
“How can we reduce the ability of a conspiracy
to act?...We can split the conspiracy, reduce or
eliminating important communication
between a few high weight links or many low
weight links.” ["State and Terrorist
Conspiracies," Nov. 10, 2006, p. 4]](https://image.slidesharecdn.com/hacktivism6-200625033543/75/Hacktivism-6-Networks-and-Conspiracy-39-2048.jpg)
![A. Brady
• [Assange’s] model for imagining the
conspiracy, then, is not at all the cliché that
people mean when they sneer at someone for
being a “conspiracy theorist.” After all, most
the “conspiracies” we’re familiar with are pure
fantasies, and because the “Elders of Zion” or
James Bond’s SPECTRE have never existed,
their nonexistence becomes a cudgel for
beating on people that would ever use the
term or the concept.](https://image.slidesharecdn.com/hacktivism6-200625033543/75/Hacktivism-6-Networks-and-Conspiracy-58-2048.jpg)
![Brady on killing conspiracies.
• You destroy the conspiracy, in other words, by making
it so paranoid of itself that it can no longer conspire:
• The more secretive or unjust an organization is, the
more leaks induce fear and paranoia in its leadership
and planning coterie. This must result in minimization
of efficient internal communications mechanisms (an
increase in cognitive “secrecy tax”) and consequent
system-wide cognitive decline resulting in decreased
ability to hold onto power as the environment demands
adaption. [Assange]](https://image.slidesharecdn.com/hacktivism6-200625033543/75/Hacktivism-6-Networks-and-Conspiracy-71-2048.jpg)