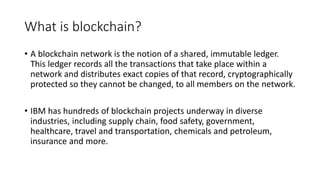
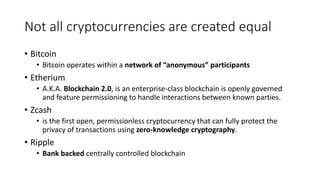
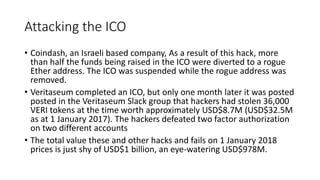
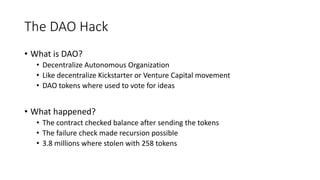
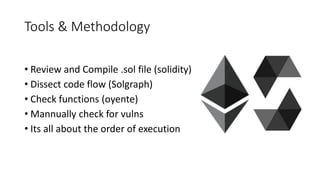
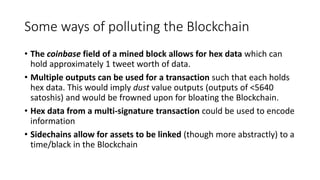
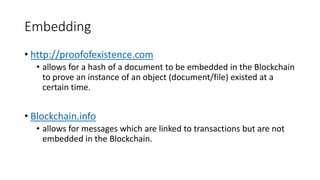
The document discusses the complexities and vulnerabilities of blockchain technology and cryptocurrencies, highlighting its use as a shared immutable ledger across various industries. It details numerous security breaches and hacks affecting cryptocurrency exchanges, ICOs, and smart contracts, emphasizing the necessity for robust security measures. Additionally, it outlines the activities of local hacker groups focused on infosec, hardware hacking, and community engagement in Puerto Rico.