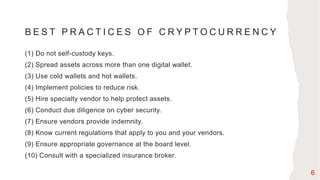
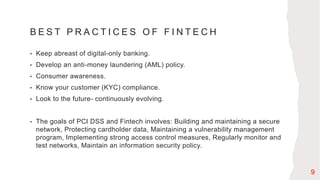
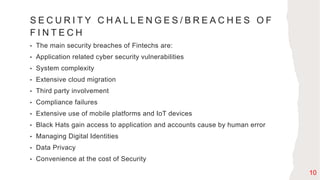
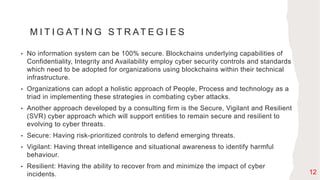
This document provides information on blockchain technology, cryptocurrency, fintech, and cybersecurity best practices related to these topics. It defines blockchain as a digital ledger that records transactions across a network of computers. Cryptocurrency uses cryptography to secure digital currency that is decentralized and not managed by a central authority. Fintech refers to the use of innovative technology in financial services. The document outlines security challenges and mitigation strategies for blockchain, cryptocurrency and fintech, including major security breaches at cryptocurrency exchanges that have resulted in billions stolen.