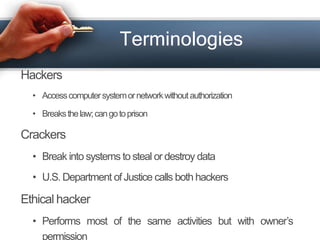
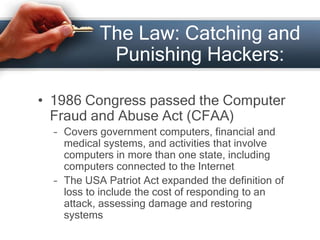
This document discusses hacking (cybercrime) and defines it as illegally accessing computer systems or networks without authorization. It outlines the history of hacking from the early positive use of the term to refer to clever programming to the modern negative connotation involving illegal activity. It describes different types of hackers (black hat, white hat, grey hat) and types of cybercrimes like hacking, denial of service attacks, and software piracy. Laws around catching and punishing hackers are also summarized.