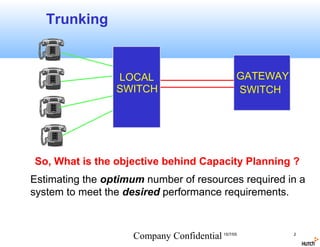
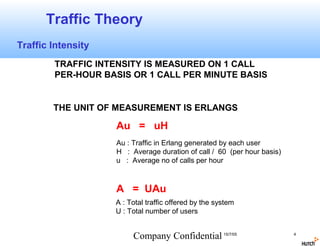
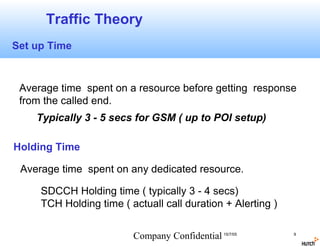
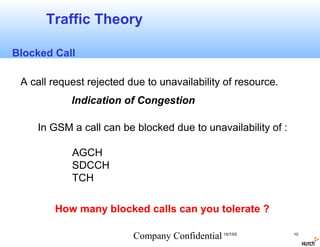
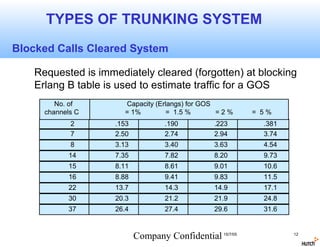
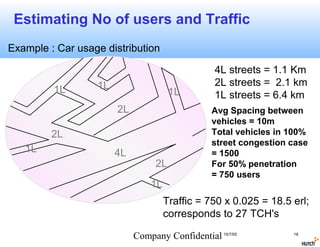
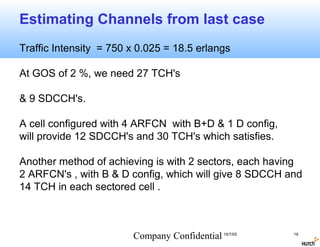
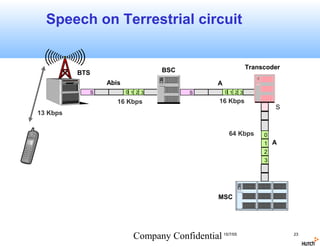
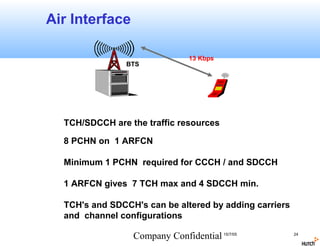
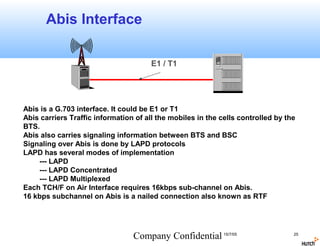
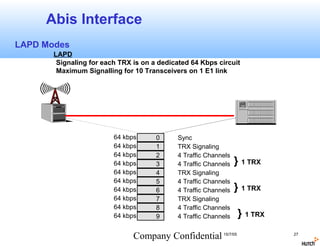
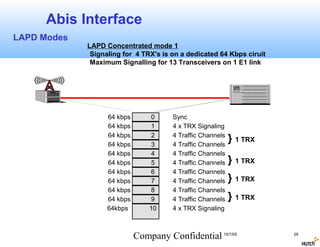
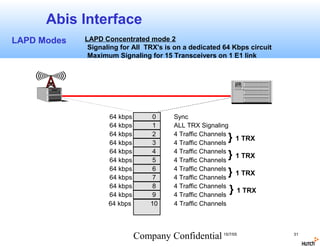
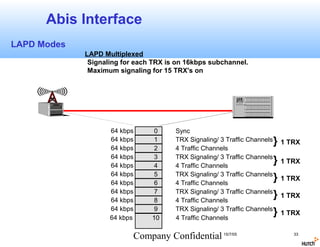
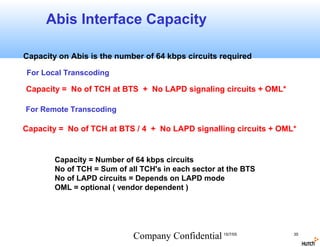
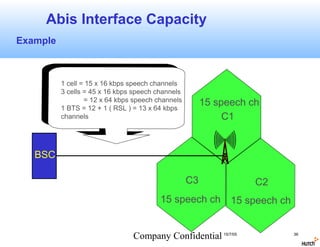
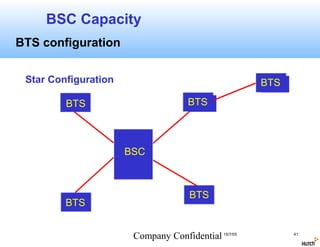
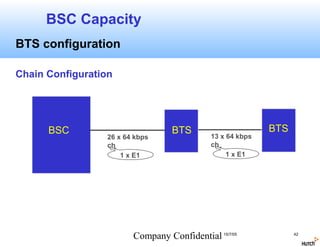
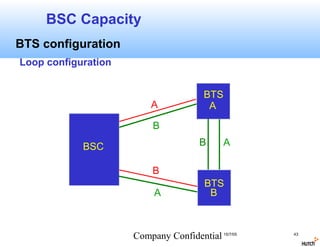
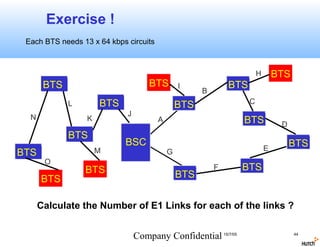
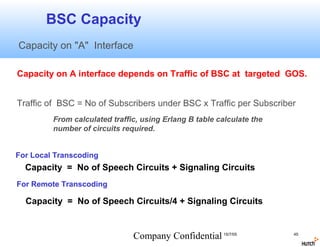
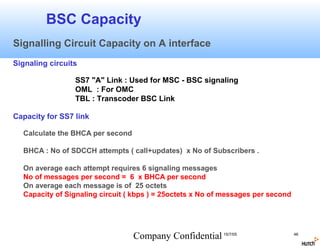
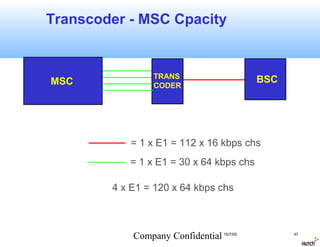
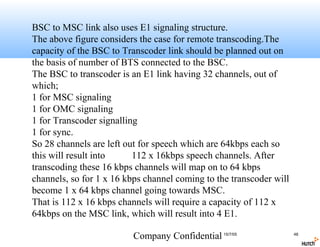
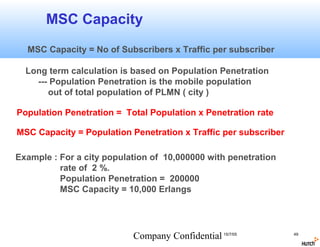
This document discusses capacity planning for GSM networks. It covers topics like trunking, traffic theory including traffic intensity, grade of service, busy hour, and request rate. It describes how to dimension traffic channels and SDCCH channels based on factors like traffic intensity and grade of service. It also discusses connectivity planning between network elements like MSC, BSC, transcoder, and BTS. It provides details on air interface, Abis interface between BSC and BTS, and different LAPD modes for signaling concentration over Abis. The objective is to estimate the optimal number of resources needed to meet performance requirements based on traffic analysis and engineering principles.