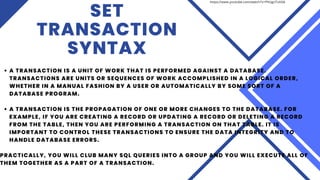
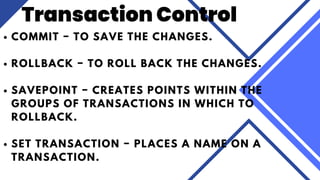
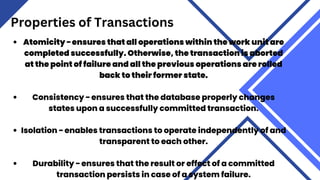
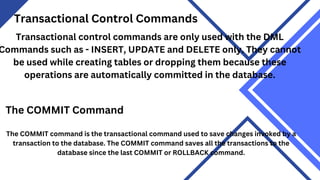
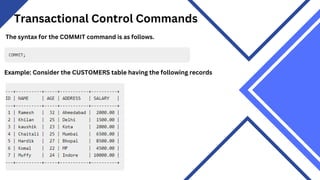
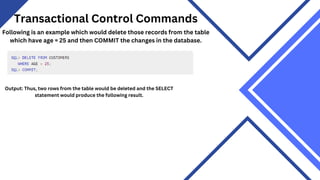
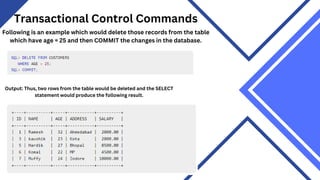
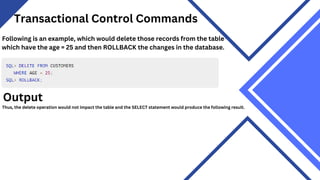
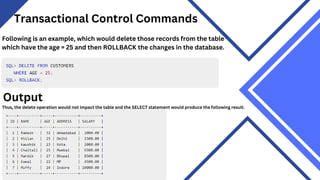
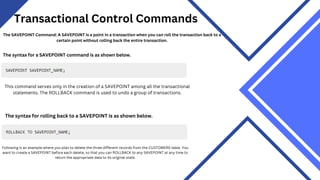
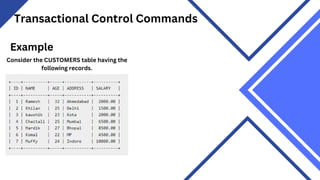
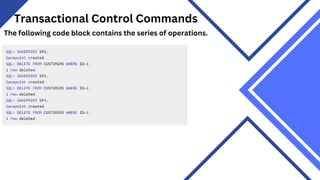
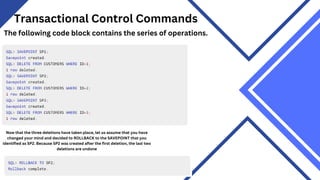
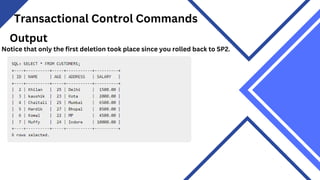
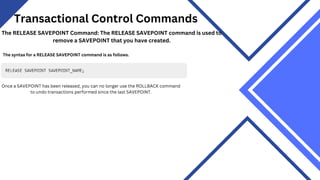
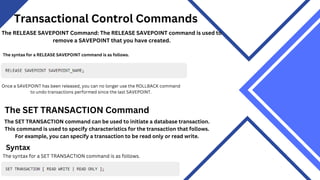
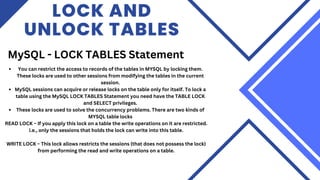
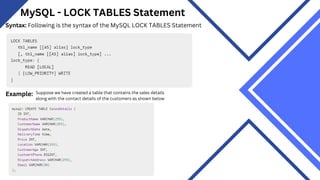
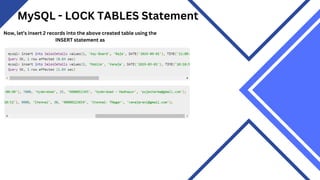
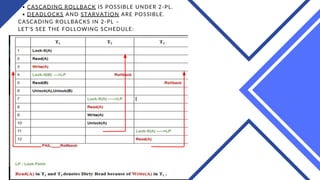
A transaction is a unit of work performed against a database that must adhere to the properties of atomicity, consistency, isolation, and durability. Transactions can be committed to save changes to the database or rolled back to undo changes. Additional commands like savepoints allow rolling back parts of transactions. The scheduler in a database manages the concurrent execution of transactions to maintain data consistency.