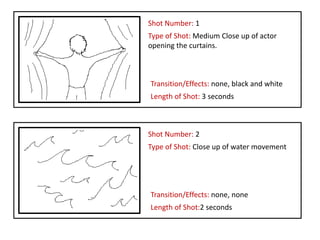
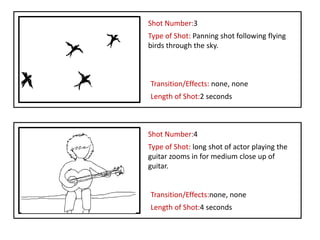
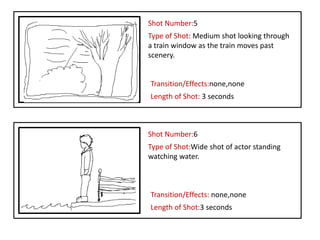
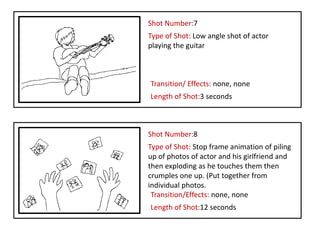
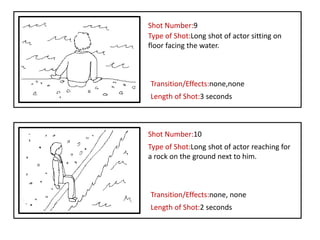
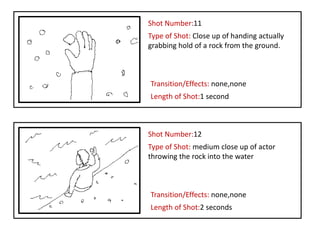
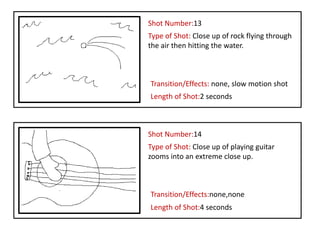
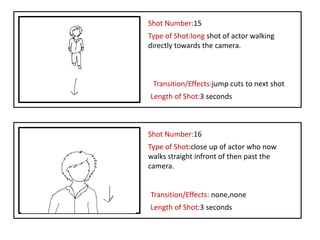
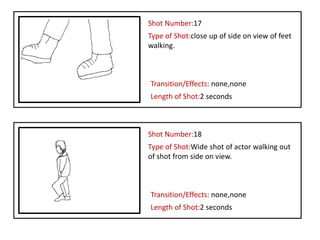
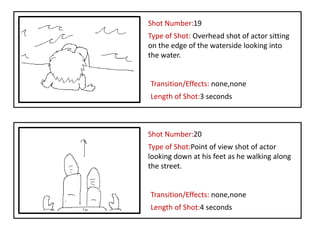
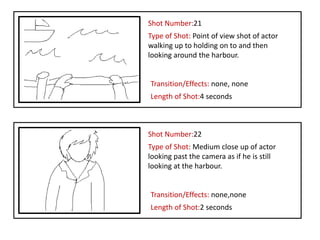
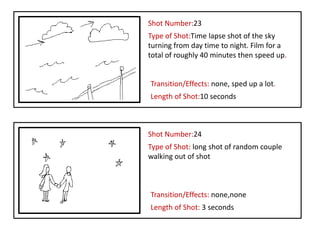
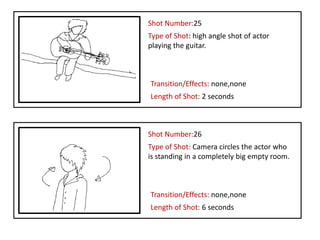
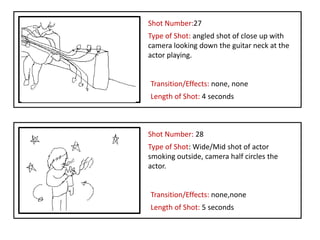
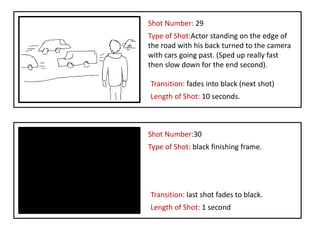
The storyboard document describes 30 shots for a music video for the song "The Boat" by Benjamin Francis Leftwich. The shots include various angles of the actor playing guitar, walking by the water and around town, throwing a rock into water, and depict the passage of time. They range from close-ups to long shots and include transitions like fade to black and jump cuts. The storyboard captures scenic and performance elements to visualize the song.