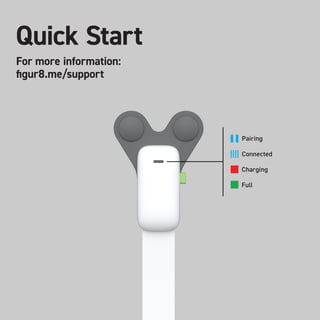
Figur8 Quick start guide
•
0 likes•383 views
This short document appears to be about wireless charging of a device. It mentions pairing, being connected, and having a full charge, suggesting the device was successfully paired and charged wirelessly until fully charged.
Report
Share
Report
Share
Download to read offline
Recommended
Nbranded case: Domus tea 

Situation: "Domus Tea” is a unique restaurant concept slated to open its first location in the Washington, DC, area in spring, 2019. Domus Tea is a sophisticated, health-conscious cafe that combines leisure time for adults with supervised play spaces for children. Project is lead by higly experienced team in HoRaCe and board of international experts.
Goal: Create an appelaing pitch deck for seed round and partnership biulding.
Solution:
- Competitor analysis;
- Structure and sotryline;
- Unique design of Pitch deck
R&D Kit user manual v1.2.1

This document provides a user manual for a research and development kit from figur8, Inc. that allows for collection and analysis of 3D motion capture data. The kit includes figur8 sensors, attachment tape, a charging cable, and data logging and analysis software. Sensors capture movement data and can be attached to the body with tape. Data and video are collected with the data logging app and exported for analysis in the data analysis tool, which allows graphing, statistical analysis, and video synchronization. The kit is designed for researchers, athletes, and healthcare providers to study movement.
Quick start guide v2.1

This short document appears to be about wireless charging of a device. It mentions pairing, being connected, and having a full charge, suggesting the device was successfully paired and is now fully charged wirelessly.
Figur8 Research and development kit user manual

The mission of figur8 is to provide high-quality 3D motion capture using a discreet, lightweight on-body system. It’s uniquely designed to measure both quality and quantity of movement. Wearable motion capture systems of the past have been restricted to expensive laboratory setups or low-resolution results. Plus joint
and muscle movements required multiple devices. This is the problem figur8 is here to solve. figur8 has made 3D motion capture available to everyone in one (much less expensive) easy-to-use kit. The research and development kit includes everything
to collect and analyze motion data for the purposes of training, injury prevention or answering specific research questions. The comprehensive research suite was designed with researchers, athletes and healthcare providers in mind—anyone who needs granular data on neuromuscular feedback.
From eye tracking to deep learning - how technology will change the way we in...

EEG devices and eyetracking technology can provide insights into consumer engagement and behavior. EEG monitors brain activity and can track meditation progress or engagement with content. Eyetracking determines where a person looks and can enhance gaming, movies, and usability testing. These technologies combined with sensors, facial recognition, and attention prediction algorithms will change how brands interact with consumers by providing personalized experiences and feedback.
Project "Fair Trade: awareness raising"

This document summarizes a project funded by the European Union to promote Fair Trade in 3 partner countries through educational activities targeting youth. The project reached over 162,000 people through activities like Fair Trade booths at festivals, educational cartoons about Fair Trade, and a game app to teach about Fair Trade supply chains. These activities aimed to raise awareness of Fair Trade and encourage choosing Fair Trade certified products. Evaluation found they educated over 2,000 game players and engaged tens of thousands of additional people through other events and materials. The overall goal was to contribute to global development by expanding the Fair Trade movement.
Socialinių kampanijų komunikacija – nuo ko pradėti?

Socialinėms (visuomeninėms) kampanijoms labai svarbus matomumas. Norint pasiekti kuo daugiau žmonių reikia tinkamai suplanuoti kampanijos komunikaciją. Šiame pristatyme pateikiu komunikacijos ABC kartu su sėkmingų kampanijų pavyzdžiais.
Pranešimas buvo pristatytas projekto Orus darbas - orus gyvenimas mokymų metu.
16 dienų prieš smurtą prieš moteris renginiai Lietuvoje

Lietuvos moterų lobistinės organizacijos kovos su smurtu komiteto vykdomi renginiai
Recommended
Nbranded case: Domus tea 

Situation: "Domus Tea” is a unique restaurant concept slated to open its first location in the Washington, DC, area in spring, 2019. Domus Tea is a sophisticated, health-conscious cafe that combines leisure time for adults with supervised play spaces for children. Project is lead by higly experienced team in HoRaCe and board of international experts.
Goal: Create an appelaing pitch deck for seed round and partnership biulding.
Solution:
- Competitor analysis;
- Structure and sotryline;
- Unique design of Pitch deck
R&D Kit user manual v1.2.1

This document provides a user manual for a research and development kit from figur8, Inc. that allows for collection and analysis of 3D motion capture data. The kit includes figur8 sensors, attachment tape, a charging cable, and data logging and analysis software. Sensors capture movement data and can be attached to the body with tape. Data and video are collected with the data logging app and exported for analysis in the data analysis tool, which allows graphing, statistical analysis, and video synchronization. The kit is designed for researchers, athletes, and healthcare providers to study movement.
Quick start guide v2.1

This short document appears to be about wireless charging of a device. It mentions pairing, being connected, and having a full charge, suggesting the device was successfully paired and is now fully charged wirelessly.
Figur8 Research and development kit user manual

The mission of figur8 is to provide high-quality 3D motion capture using a discreet, lightweight on-body system. It’s uniquely designed to measure both quality and quantity of movement. Wearable motion capture systems of the past have been restricted to expensive laboratory setups or low-resolution results. Plus joint
and muscle movements required multiple devices. This is the problem figur8 is here to solve. figur8 has made 3D motion capture available to everyone in one (much less expensive) easy-to-use kit. The research and development kit includes everything
to collect and analyze motion data for the purposes of training, injury prevention or answering specific research questions. The comprehensive research suite was designed with researchers, athletes and healthcare providers in mind—anyone who needs granular data on neuromuscular feedback.
From eye tracking to deep learning - how technology will change the way we in...

EEG devices and eyetracking technology can provide insights into consumer engagement and behavior. EEG monitors brain activity and can track meditation progress or engagement with content. Eyetracking determines where a person looks and can enhance gaming, movies, and usability testing. These technologies combined with sensors, facial recognition, and attention prediction algorithms will change how brands interact with consumers by providing personalized experiences and feedback.
Project "Fair Trade: awareness raising"

This document summarizes a project funded by the European Union to promote Fair Trade in 3 partner countries through educational activities targeting youth. The project reached over 162,000 people through activities like Fair Trade booths at festivals, educational cartoons about Fair Trade, and a game app to teach about Fair Trade supply chains. These activities aimed to raise awareness of Fair Trade and encourage choosing Fair Trade certified products. Evaluation found they educated over 2,000 game players and engaged tens of thousands of additional people through other events and materials. The overall goal was to contribute to global development by expanding the Fair Trade movement.
Socialinių kampanijų komunikacija – nuo ko pradėti?

Socialinėms (visuomeninėms) kampanijoms labai svarbus matomumas. Norint pasiekti kuo daugiau žmonių reikia tinkamai suplanuoti kampanijos komunikaciją. Šiame pristatyme pateikiu komunikacijos ABC kartu su sėkmingų kampanijų pavyzdžiais.
Pranešimas buvo pristatytas projekto Orus darbas - orus gyvenimas mokymų metu.
16 dienų prieš smurtą prieš moteris renginiai Lietuvoje

Lietuvos moterų lobistinės organizacijos kovos su smurtu komiteto vykdomi renginiai
Kaip susikurti youtube kanalą

Prezentacija padės nevyriausybinei organizacijai ar įmonei lengvai ir paprastai susikurti savo Youtube kanalą.
"Saugumas man patinka!" programa jaunimui

Saugumas man patinka! - edukacinės programos jaunimui. pagrindinis programos tikslas kalbėti su jaunimu apie saugumą elektroninėje erdvėje, suteikti jiems praktinių patarimų kaip apsaugoti save elektroninėje erdvėje. Programa taip pat siekia kovoti su patyčiomis elektroninėje erdvėje skatindama neigiamą jaunimo požiūrį į patyčias.
Kvietimas į mokymus "Log In - saugumas man patinka!"

Kvietimas mokykloms į mokymus Log In - saugumas man patinka. Mokymų temos:smurtas jaunimo tarpe, lyčių lygybė, saugumas internetinėje erdvėje.
Mokymus veda profesionalūs lektoriai.
Dalyvavimas mokymuose - nemokamas
Xgeneration manual en

The document discusses best practices from organizations in Estonia working to combat violence against women. It provides background on the establishment of women's shelters starting in 2002. It describes the challenges faced by the shelters during an economic recession in 2009, including decreased funding and a draft law that would have undermined shelter services. The shelters' union lobbied to ensure the continued operations and sustainability of shelters during this difficult period.
Legislative recommendations global

The document proposes 12 legislative modifications and 5 new legislative proposals related to domestic violence and gender violence in Spain. The proposed modifications aim to strengthen protections for victims by extending probation and protection orders, introducing stalking as a crime, and ensuring rehabilitation programs for abusers. The proposals also seek to improve the judicial process by allowing related cases to be tried together and considering victims' statements during investigation. Overall, the recommendations aim to improve security for victims and legal processes regarding domestic violence cases in Spain.
Webinar: Designing a schema for a Data Warehouse

Are you new to data warehouses (DWH)? Do you need to check whether your data warehouse follows the best practices for a good design? In both cases, this webinar is for you.
A data warehouse is a central relational database that contains all measurements about a business or an organisation. This data comes from a variety of heterogeneous data sources, which includes databases of any type that back the applications used by the company, data files exported by some applications, or APIs provided by internal or external services.
But designing a data warehouse correctly is a hard task, which requires gathering information about the business processes that need to be analysed in the first place. These processes must be translated into so-called star schemas, which means, denormalised databases where each table represents a dimension or facts.
We will discuss these topics:
- How to gather information about a business;
- Understanding dictionaries and how to identify business entities;
- Dimensions and facts;
- Setting a table granularity;
- Types of facts;
- Types of dimensions;
- Snowflakes and how to avoid them;
- Expanding existing dimensions and facts.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
More Related Content
More from Kamilė Butkevičiūtė
Kaip susikurti youtube kanalą

Prezentacija padės nevyriausybinei organizacijai ar įmonei lengvai ir paprastai susikurti savo Youtube kanalą.
"Saugumas man patinka!" programa jaunimui

Saugumas man patinka! - edukacinės programos jaunimui. pagrindinis programos tikslas kalbėti su jaunimu apie saugumą elektroninėje erdvėje, suteikti jiems praktinių patarimų kaip apsaugoti save elektroninėje erdvėje. Programa taip pat siekia kovoti su patyčiomis elektroninėje erdvėje skatindama neigiamą jaunimo požiūrį į patyčias.
Kvietimas į mokymus "Log In - saugumas man patinka!"

Kvietimas mokykloms į mokymus Log In - saugumas man patinka. Mokymų temos:smurtas jaunimo tarpe, lyčių lygybė, saugumas internetinėje erdvėje.
Mokymus veda profesionalūs lektoriai.
Dalyvavimas mokymuose - nemokamas
Xgeneration manual en

The document discusses best practices from organizations in Estonia working to combat violence against women. It provides background on the establishment of women's shelters starting in 2002. It describes the challenges faced by the shelters during an economic recession in 2009, including decreased funding and a draft law that would have undermined shelter services. The shelters' union lobbied to ensure the continued operations and sustainability of shelters during this difficult period.
Legislative recommendations global

The document proposes 12 legislative modifications and 5 new legislative proposals related to domestic violence and gender violence in Spain. The proposed modifications aim to strengthen protections for victims by extending probation and protection orders, introducing stalking as a crime, and ensuring rehabilitation programs for abusers. The proposals also seek to improve the judicial process by allowing related cases to be tried together and considering victims' statements during investigation. Overall, the recommendations aim to improve security for victims and legal processes regarding domestic violence cases in Spain.
More from Kamilė Butkevičiūtė (18)
Kvietimas į mokymus "Log In - saugumas man patinka!"

Kvietimas į mokymus "Log In - saugumas man patinka!"
Moterų informacijos centro metinė veiklos ataskaita 2011 m.

Moterų informacijos centro metinė veiklos ataskaita 2011 m.
Recently uploaded
Webinar: Designing a schema for a Data Warehouse

Are you new to data warehouses (DWH)? Do you need to check whether your data warehouse follows the best practices for a good design? In both cases, this webinar is for you.
A data warehouse is a central relational database that contains all measurements about a business or an organisation. This data comes from a variety of heterogeneous data sources, which includes databases of any type that back the applications used by the company, data files exported by some applications, or APIs provided by internal or external services.
But designing a data warehouse correctly is a hard task, which requires gathering information about the business processes that need to be analysed in the first place. These processes must be translated into so-called star schemas, which means, denormalised databases where each table represents a dimension or facts.
We will discuss these topics:
- How to gather information about a business;
- Understanding dictionaries and how to identify business entities;
- Dimensions and facts;
- Setting a table granularity;
- Types of facts;
- Types of dimensions;
- Snowflakes and how to avoid them;
- Expanding existing dimensions and facts.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

Imagine a world where machines not only perform tasks but also learn, adapt, and make decisions. This is the promise of Artificial Intelligence (AI), a technology that's not just enhancing our lives but revolutionizing entire industries.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
OpenID AuthZEN Interop Read Out - Authorization

During Identiverse 2024 and EIC 2024, members of the OpenID AuthZEN WG got together and demoed their authorization endpoints conforming to the AuthZEN API
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Recently uploaded (20)
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

AI 101: An Introduction to the Basics and Impact of Artificial Intelligence
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
