FIB MIT208.pdf
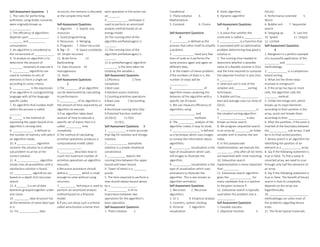
- 1. Self-Assessment Questions 1 1. The rules for performing arithmetic using Arabic numerals were originally known as _____________. 2. The efficiency of algorithms depends upon ____________, ________ and __________ consumption. 3. An algorithm is considered as the cornerstone of ____________. 4. To analyze an algorithm is to determine the amount of ________ necessary to execute it. 5. __________ algorithms are used to combine to sets of elements to form a single set according to some criteria. 6. ___________ is the expression of an algorithm in a programming language with all the language specific codes. 7. An algorithm that invokes itself within the process is called _______. 8. ______ is the method of expressing the upper bound of an algorithm's running time. 9. _____________ is defined as the number of memory cells which an algorithm needs. 10. A ____________ algorithm converts the solution to a simpler sub problem to arrive at the correct solution. 11. A ______________ algorithm simply tries all possibilities until a satisfactory solution is found. 12. ___________ algorithms are based on a depth-first recursive search. 13. A ______ is a set of data elements grouped together under one name. 14. _________ data structure has all the elements of same data type in it. 15. For ____________ data structure, the memory is allocated at the compile time itself. Self-Assessment Questions 1. Algorism 2. Speed, size, resources 3. Good programming 4. Resources 5. Merging 6. Programs 7. Direct recursive 8. Big – O 9. Space complexity 10. Simple recursive 11. Brute force 12. Backtracking 13. Data structure 14. Homogeneous 15. Static Self-Assessment Questions 2 1.The ________ of an algorithm can be determined by calculating its performance. 2.___________ of an algorithm is the amount of time required by an algorithm to execute. 3.If an algorithm takes least amount of time to execute a specific set of inputs then it is called __________ time complexity. 4.The method of calculating primitive operations produces a computational model called _______________. 5._________ describes how to count the maximum number of primitive operations an algorithm executes. 6.Recursive procedure should define a ________ which is small enough to solve without using recursion. 7.__________ technique is used to perform an amortized analysis method based on a financial model. 8.If you can setup such a scheme called amortization scheme then each operation in the series has an_______. 9._____________ technique is used to perform an amortized analysis method based on an energy model. 10.The running time of the algorithm prefixAverages1 is _______. 11.The running time of the algorithm prefixAverages2 is _______. 12.In prefixAverages2 algorithm ________ is the time taken for initiating the variable s. Self-Assessment Questions 1.Efficiency 2.Time complexity 3.Best case 4.Random assess machine 5.Counting primitive operations 6.Base case 7.Accounting method 8.Amortised running time O(a) 9.Potential function method 10.O(n2) 11.O(n) 12.O(1) Self-Assessment Questions 3 1. ___________ is more accurate than Big Oh notation and Omega notation. 2. ____________ asymptotic notation is a simple notational convenience. 3. ___________ depicts the running time between the upper bound and lower bound. 4. Tower of Hanoi is a ________ puzzle. 5. The time required to perform a step should always bound above by a ________________. 6. ____________ is of no importance between two operations for the algorithm’s basic operation. Self-Assessment Questions 1. Theta notation 2. Conditional 3. Theta notation 4. Mathematical 5. Constant 6. Choice Self-Assessment Questions 4 1. _________ is defined as the process that refers itself to simplify a problem. 2. _____________ need very few lines of code as it performs the same process again and again on different data. 3. In the towers of Hanoi problem, if the numbers of disks is n, the number of steps will be ___________. 4. ___________________ of algorithm means analyzing the behavior of the algorithm with a specific set of inputs. 5. We can measure efficiency of algorithms using ________________ and _______________ methods. 6. The __________ analysis of the algorithm makes it easy to study 7. _________________ is defined as a technique which uses images to convey the information about algorithms. 8. ___________ visualization is the type of visualization which uses still images to illustrate the algorithm. 9. ___________ visualization is the type of visualization which uses animations to illustrate the algorithm. This is also known as algorithm animation. Self-Assessment Questions 1. Recursion 2. Recursive algorithms 3. 2n-1 4. Empirical analysis 5. Counters, system clocking 6. Pictorial 7. Algorithm visualization 8. Static algorithm 9. Dynamic algorithm Self-Assessment Questions 5 1. A value that satisfies the constraint is called a ___________. 2. ____________ is a function that is associated with an optimization problem determining how good a solution is. 3. The running time needed to determine whether a possible value of a feasible solution is O(n) and the time required to compute the objective function is also O(n) is ________. 4. Selection sort is one of the simplest and ________ sorting techniques. 5. Bubble sort has __________, best and average case run-time of O(n2). 6. ______________________ is the simplest sorting algorithm. 7. ________________ is also known as linear search. 8. We program sequential search in an array by _________an index variable until it reaches the last index. 9. In this pseudocode implementation, we execute the __________ only after all list items are examined with none matching. 10. Exhaustive search implementation is more important than _________. 11. Exhaustive search algorithm gives the ______________ for every candidate that is a solution to the given instance P. 12. Exhaustive search is typically used when the problem size is ___________. Self Assessment Questions 1. Feasible solution 2. Objective function 3. O(n2n). 4. Performance oriented 5. Worst 6. Bubble sort 7. Sequential search 8. Stepping up 9. Last line 10. Speed 11. Output 12. Limited Self-Assessment Questions 6 1. Mergesort is a perfect example of a successful application of the _________ and ____________ methodology. 2. ____________ is a comparison- based sorting. 3. What are the three steps involved in mergesort? 4. If the array has two or more cells, the algorithm calls the ________ method. 5. Unlike the merge sort, which breaks up its input elements according to their position in the array, quick sort breaks them according to their ____________. 6. After the partition, if the pivot is inserted at the boundary between the ___________ sub-arrays, it will be in its final sorted position. 7. Binary search is an algorithm for identifying the position of an element in a ____________ array. 8. Say if the following statement is true or false. To find a value in unsorted array, we need to scan through only half the elements of an array. 9. Say if the following statement is true or false. The benefit of binary search is that its complexity depends on the array size logarithmically. 10. ________________________ methodology can solve most of the problems regarding binary trees. 11. The three typical traversals:
- 2. _____________, _____________, and _____________ are the most important Divide and Conquer algorithms of binary trees. 12. Two kinds of traversal are _____________ and _____________. 13. At the expense of a slight increase in the number of additions, the strassen’s matrix multiplication algorithm will _____________ the total number of multiplications performed. 14. The normal method of matrix multiplication of two n X n matrices takes ___________ operators. 15. By the strassen’s matrix multiplication algorithm, two 2 X 2 matrices takes 2 only 7 multiplicators and _______ adders. Self-Assessment Questions 1. Divide, Conquer 2. Mergesort 3. Divide, recur, conquer 4. Partition 5. Value 6. Left and right 7. Sorted 8. False 9. True 10. Divide and Conquer 11. Pre-order, in-order, post-order 12. Breadth-first traversal, depth- first traversal 13. Decrease 14. O( ) 15. 18 Self Assessment Questions 7 1. Decrease and conquer can be implemented by a ________________ or ____________ approach. 2. Decrease and conquer is also known as ______________ approach. 3. Decrease and conquer is a method by which we find a solution to a given problem based upon the __________ of a number of problems. 4. There are ________ major categories in insertion sort. 5. In insertion sort, the best-case input is an array that is already __________. 6. To carry out an insertion sort, begin at the ______ most element of the array 7. DFS uses the __________ technique. 8. It is easier to use a ________ to trace the working of a depth first search. 9. Depth-first search starts exploring vertices of a graph at a _______ vertex. 10. The data structure which is used to track the working of Breadth-first search is a ___________. 11. Breadth-first search is an algorithm which travels in such a way that all vertices are finished along every ___________. 12. The data structure which is used to track the working of Breadth-first search is a ______________. 13. Topological ordering of a _________ is a linear ordering of its nodes. 14. In topological sorting the jobs are denoted by _________. 15. Being a DAG is also a necessary condition for ______________sorting to be possible. 16. Theoretically, the traveling salesman problem can always be solved by specifying all _____________ Hamiltonian circuits. 17. The cities are represented by ____________ and the roads between them are shown as edges. 18. Each of the cities is connected to another city by a road a complete _____________________ is obtained. Self Assessment Questions 1. Top down or Bottom-up 2. Incremental 3. Solution 4. Two 5. Sorted 6. Left 7. Backtracking 8. Time and space 9. Backtracks 10. Graph 11. Uninformed 12. Goal 13. Directed acyclic graph 14. Vertices 15. Topological 16. Combinatorial 17. Subset 18. Decrease-by- one Self Assessment Questions 8 1. _______, ________ & ________ are three instances of transform and conquer technique. 2. The worst case efficiency of brute force algorithm is _______. 3. The searching requires _______ comparisons to in the worst case, when the array is sorted first. 4. Gaussian elimination is an algorithm for solving systems of __________ equations. 5. In Gaussian elimination we make the ________ coefficient matrix zero. 6. Gaussian elimination can be used to find the _________of a matrix. 7. An AVL tree is a _________ tree. 8. The _________________ is the mirror image of the RL-rotation. 9. The two nodes of 2-3 tree are ___________ and ____________. 10. _________ heap construction algorithm is less efficient than its counterpart. 11. A heap can be defined as ________ with keys assigned to its nodes. 12. The time efficiency of heapsort is ________ in both worst and average cases. 13. Greatest common divisor can be computed easily by ________. 14. The problem of counting a graph’s paths can be solved with an algorithm for an appropriate power of its __________. 15. What is the formula obtained to find the lcm in the problem reduction approach to find the lcm? Self Assessment Questions 1. Instance simplification, problem reduction , representation change 2. ө(n2) 3. [log2 n] +1 4. Linear 5. Lower triangular 6. Rank 7. Binary search 8. LR-rotation 9. 2-node, 3- node 10. Top-down 11. Binary trees 12. O(n log n) 13. Euclid’s algorithm 14. Adjacent matrix 15. Self Assessment Questions 9 1. Input enhancement is based on ___________________ the instance. 2. The information which is used to place the elements at proper positions is accumulated sum of frequencies which is called as __________. 3. Sorting is an example of input enhancement that achieves ___________. 4. Input enhancement is to _____________ the input pattern. 5. In Horspool’s algorithm, the characters from the pattern are matched __________________. 6. The two heuristics in Boyre- Moore algorithm are _______________ and ________________. 7. Each slot of a hash table is often called a _____________. 8. Collision occurs when a hash function maps two or more keys to the ____________________________ . 9. When the interval between probes is computed by another hash function it is ______________________. 10. As the ______________________ increases the height of the tree decreases thus speeding access. 11. Access time increases slowly as the number of records __________. 12. The insertions in a B-Tree start from a ________. Self Assessment Questions 1. Preprocessing 2. Distribution 3. Time efficiency 4. Preprocess 5. Right to left 6. Good suffix and bad character shift 7. Bucket 8. Same hash value 9. Double hashing 10. Branching factor 11. Increases 12. Leaf node Self Assessment Questions 10 1. The ____________ and _____________ are the two approaches to dynamic programming. 2. __________ is a technique to store answers to sub-problems in a table. 3. The _________________ algorithm is similar to the dynamic approach. 4. The formula to calculate the nth Fibonacci series is _______________. 5. The asymptotic running time when we first run to calculate the nth Fibonacci number is _______. 6. To compute the nth Fibonacci number we followed the __________ dynamic approach. 7. What formula can we use to find the value of the binomial coefficient? 8. The gamma function z! (z 1) allows the binomial coefficient to be generalized to non-integer arguments like _________________. 9. Binomial coefficients are a study of _____________. 10. Both Warshall’s and Floyd’s algorithms have the run time as ________. 11. The Warshall’s algorithm is used to solve _______________ problems. 12. The Floyd’s algorithm is used to solve ________________ problems. Self Assessment Questions 1. Top-down, bottom-up 2. Memoization 3. Divide and conquer 4. 5. O(n) 6. Bottom-up 7. 8. Complex n and k 9.
- 3. Combinatorics 10. θ(n3) 11. Transitive closure 12. Shortest path Self Assessment Questions 11 1. Principle of __________ is defined as a basic dynamic programming principle which helps us to view problems as a sequence of sub problems. 2. ______________, a mathematician, invented the Principle of Optimality. 3. All optimization problems tend to minimizing cost, time and maximizing ________. 4. ________________are node based data structures used in many system programming applications for managing dynamic sets. 5. The Insertion, deletion and search operations of a binary search tree has an average case complexity of _________. 6. The time taken to perform operations on a binary search tree is directly proportional to the _______ of the tree. 7. The __________ expresses the problem using its sub-instances. 8. ________________ is an NP- hard optimization problem. 9. The Knapsack problem minimizes the total _________ and maximizes the total value. 10. The goal of using ______________ is to solve only the sub problems which are necessary. 11. Memory functions use a dynamic programming technique called _____ in order to reduce the inefficiency of recursion that might occur. 12. Memory functions method solves the problem using _________approach. Self Assessment Questions 1. Optimality 2. Richard Ernest Bellman 3. Profits 4. Binary search trees 5. O(log n) 6. Height 7. Recurrence relation 8. Bounded Knapsack problem 9. Weight 10. Memory functions 11. Memoization 12. Top down Self Assessment Questions 12 1. The choices made in a greedy algorithm cannot depend on _________ choices. 2. The __________________ is greedy in the sense that at each iteration it approximates the residual possible by a single function. 3. A greedy strategy usually progresses in a ___________ fashion. 4. The _______________________ is obtained by selecting the adjacent vertices of already selected vertices. 5. Each _________________ generated by prim’s algorithm is a part of some other minimum spanning tree. 6. The greedy strategy in prim’s algorithm is greedy since the tree is added with an edge that contributes the __________ amount possible to the tree's weight. 7. In Kruskal’s algorithm if the graph is not connected, then the algorithm yields a __________________. 8. The Union-Find data structure is helpful for managing _____________ which is vital for Kruskal’s algorithm. 9. Correctness of Kruskal’s algorithm can be proved by saying that the constructed spanning tree is of _______________. 10. Dijkstra’s algorithm solves the single-source ____________ problem for a tree. 11. The algorithm finds the path with lowest cost between the ________ vertex and every other vertex. 12. The time complexity of Dijkstra’s algorithm can be improved for _____________ graphs. 13. Huffman codes are digital _________________ codes. 14. The Huffman Encoding scheme falls in the category of ____________. 15. Static Huffman coding is done with the help of ___________ tables. Self Assessment Questions 1. Future 2. Pure greedy algorithm 3. Top-down 4. Minimum spanning tree 5. Sub-tree 6. Minimum 7. Minimum spanning forest 8. Equivalence classes 9. Minimal weight 10. Shortest path 11. Originating 12. Sparse 13. Data compression 14. Variable length encoding 15. Statistical symbol frequency Self Assessment Question 13 1. _____________________ means calculating the minimum amount of work required to solve the problem. 2. Trivial lower bound is obtained by the count of the input data that the algorithm reads and the output it produces. 3. _______________________ method defines the lower bound of an algorithm based on the amount of the comparisons the algorithm makes. 4. Comparison is the basic operation of _____________algorithm. 5. For sorting algorithms the average case efficiencies are better than their worst case efficiencies. 6. We use a ________________ decision tree to represent an algorithm for searching a sorted array with three way comparisons. 7. Problems that are solved within polynomial time are called _________. 8. ____________ problem finds the chromatic number of the given graph. 9. An algorithm in which every operation is exclusively defined is called ______________ algorithm. Self Assessment Questions 1. Lower – bound 2. True 3. Information – theoretic 4. Sorting 5. True 6. Ternary 7. Tractable 8. Graph coloring 9. Deterministic Self Assessment Questions 14 1. We can implement Backtracking by constructing the _______________. 2. Backtracking, in the _______ case may have to generate all possible candidates in a problem state that is growing exponentially. 3. The n-Queens problem, the _____________ circuit and the Subset Sum problem are some examples of problems that can be solved by Backtracking. 4. ___________________________ organizes details of all candidate solutions, and discards large subsets of fruitless candidate solutions. 5. A ________ is a solution that satisfies all the constraints of a problem. 6. In Branch and Bound algorithm, the ratio of the number of solutions verified largely _______________ as the size of the problem increases. 7. ________________ algorithms can be used to solve NP-Hard problems that have small instances. 8. Minimum Spanning tree provides us a good basis for constructing a _________ approximation tour. 9. We select the items in __________ order of their weights in order to use the knapsack capacity efficiently. Self Assessment Questions 1. State-space tree 2. Worst 3. Hamiltonian4. Branch and Bound 5. Decreases 6. Optimal 7. Exhaustive search 8. Shortest 9. Decreasing