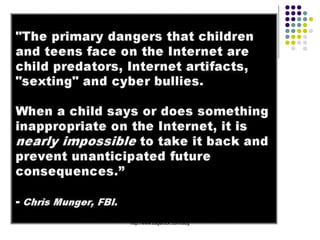
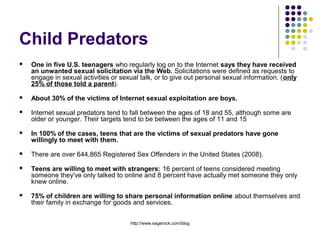
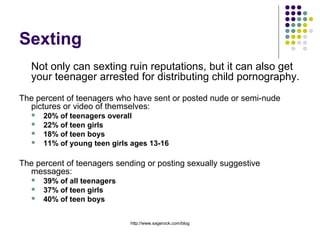
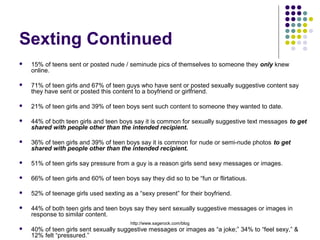
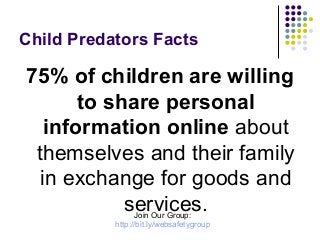
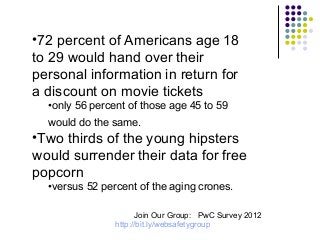
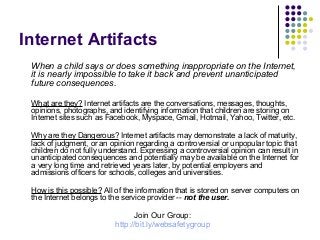
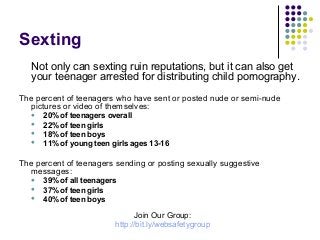
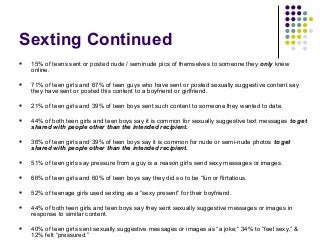
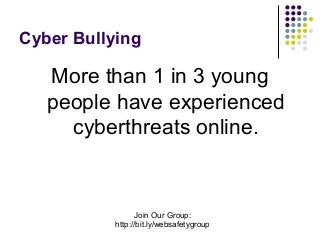
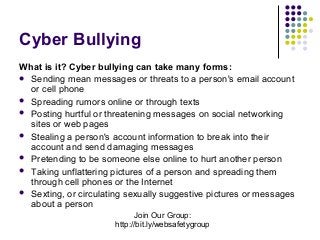
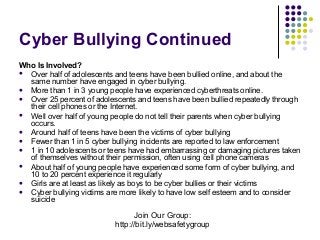
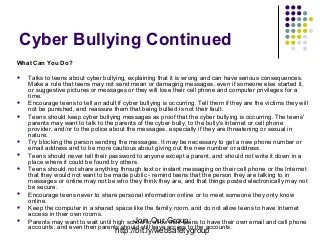
The document discusses internet safety concerns for teenagers, highlighting that a significant percentage have encountered unwanted sexual solicitations online, with many willing to share personal information and engage in risky behavior like sexting. It addresses the prevalence of cyberbullying and its impact on adolescents, emphasizing the need for parental guidance and intervention. Additionally, it warns about the permanent nature of online artifacts and the potential long-term consequences of teenagers' digital behavior.