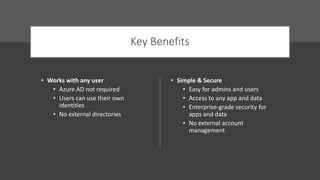
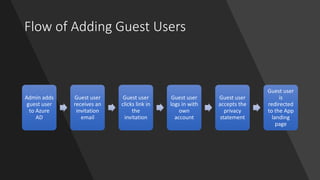
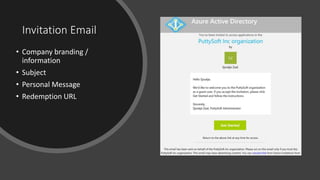
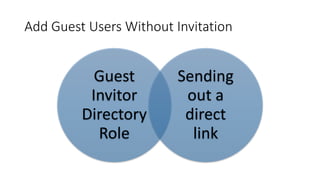
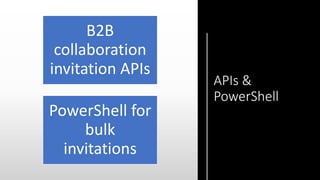
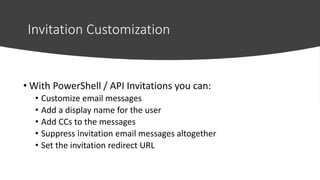
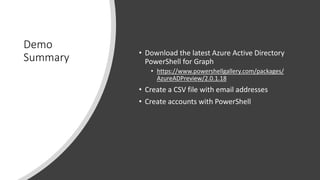
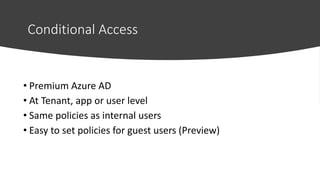
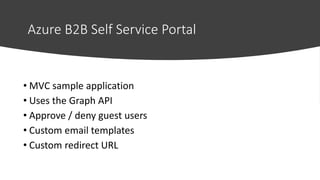
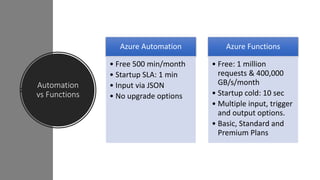
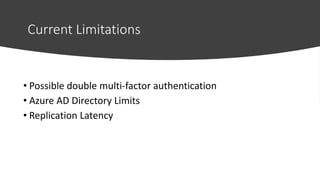
The document discusses Azure Active Directory B2B, highlighting its ability to facilitate secure collaborations between organizations by allowing guest users to access various resources without needing an Azure AD account. It details key features such as ease of invitation, conditional access, and automation through PowerShell and APIs, while providing demonstrations of user onboarding and management processes. Additionally, it touches on limitations related to multi-factor authentication and directory capacities.