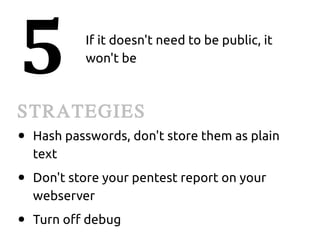
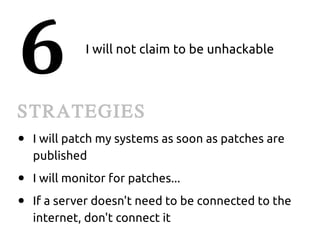
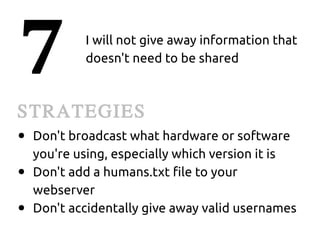
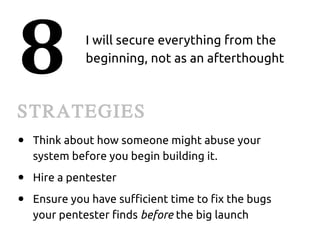
The document provides advice for securing systems and information as an "Evil Overlord" in 100 points. Some of the key strategies suggested include closing all unnecessary ports, revoking all privileges of departed users, not publicly claiming your systems are unhackable, disabling features that allow outsiders to take control, and applying a strict need-to-know policy to segregate and control access to data and systems.