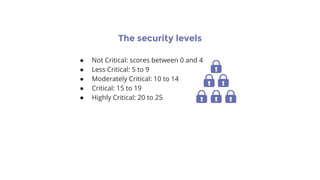
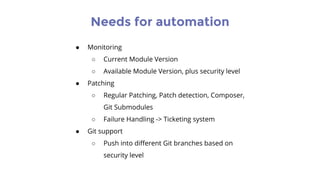
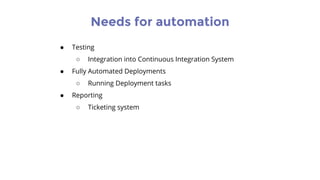
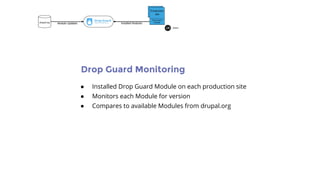
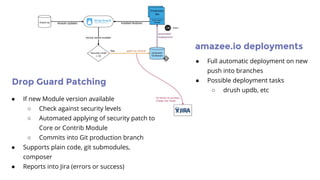
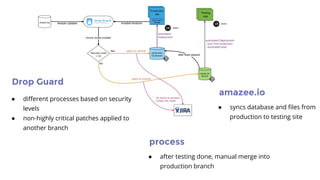
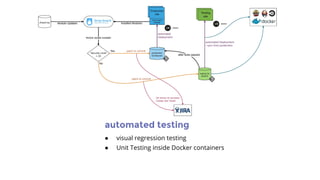
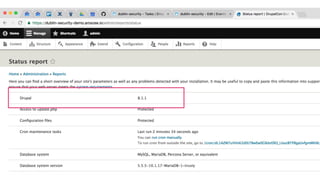
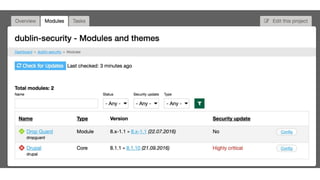
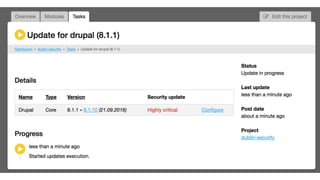
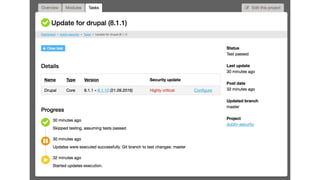
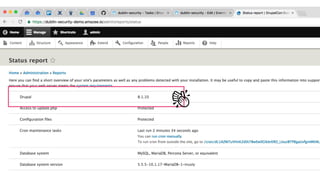
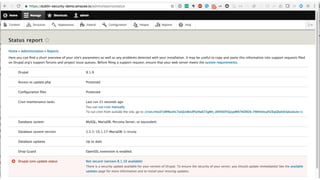
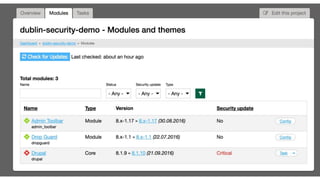
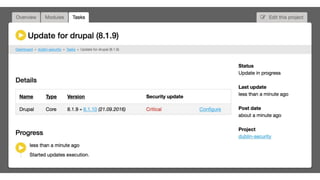
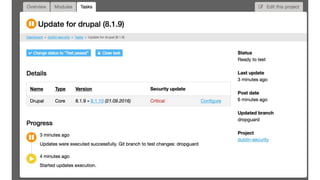
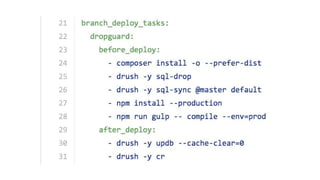
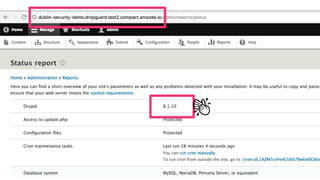
This document discusses Drupal security and how to automate security updates. It describes how security patches are released for Drupal and the need to quickly update sites within hours. It outlines different automation solutions like Drop Guard for monitoring modules, automatically applying security patches based on risk level, and integrating with automated testing and deployment systems. The solutions aim to automate the security update process that currently requires manual work to reduce risk from attacks targeting known vulnerabilities.