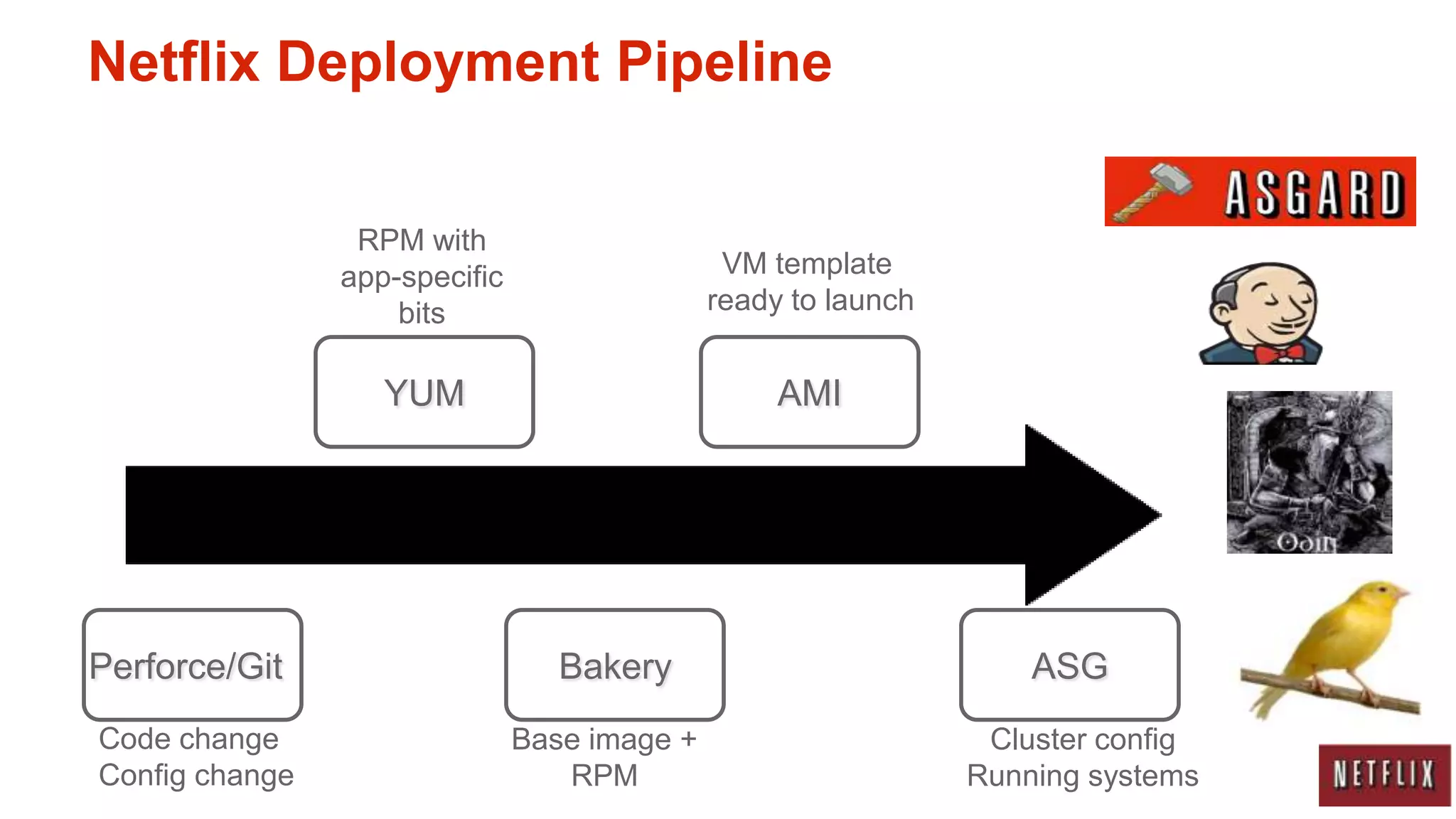
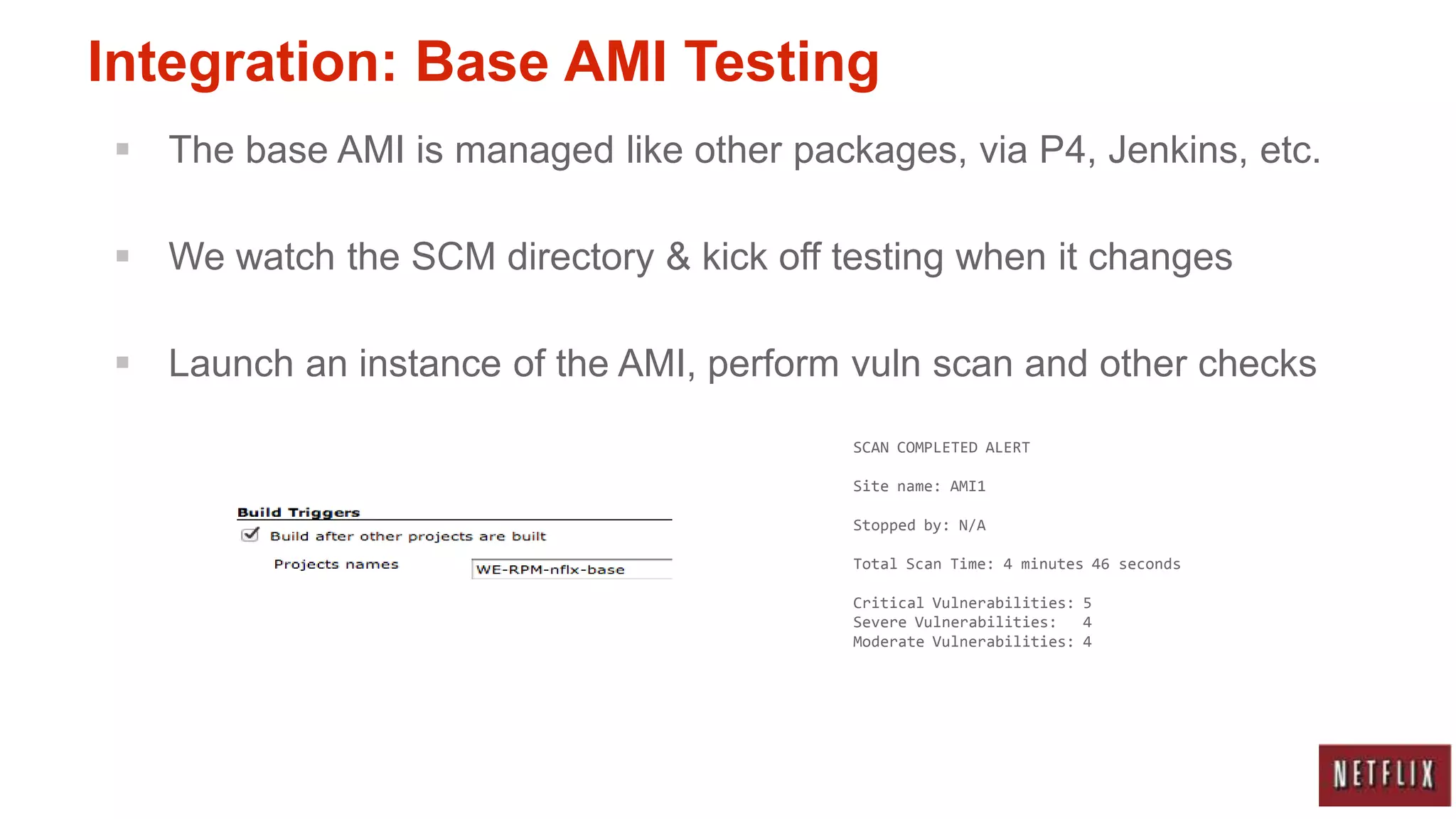
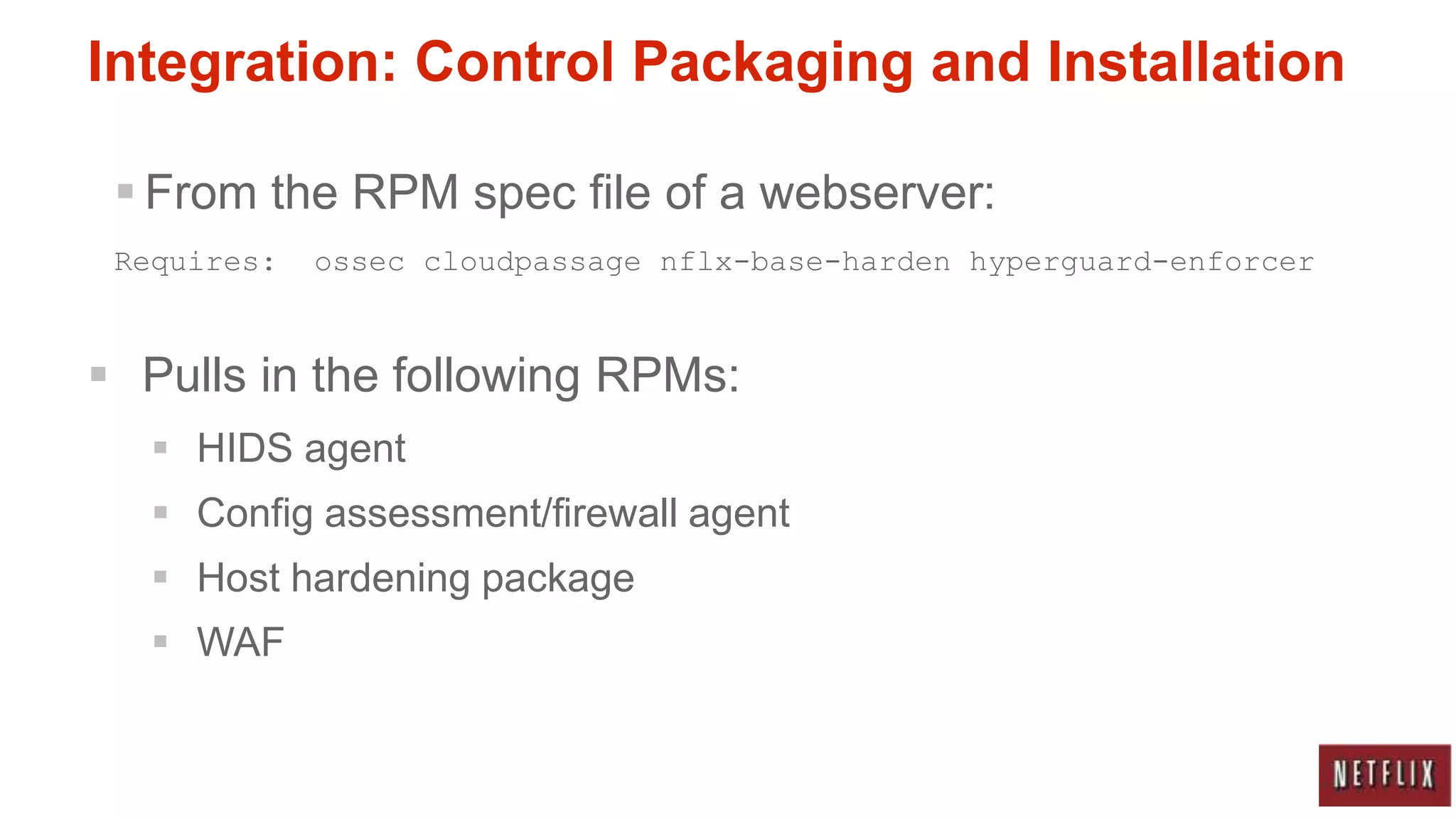
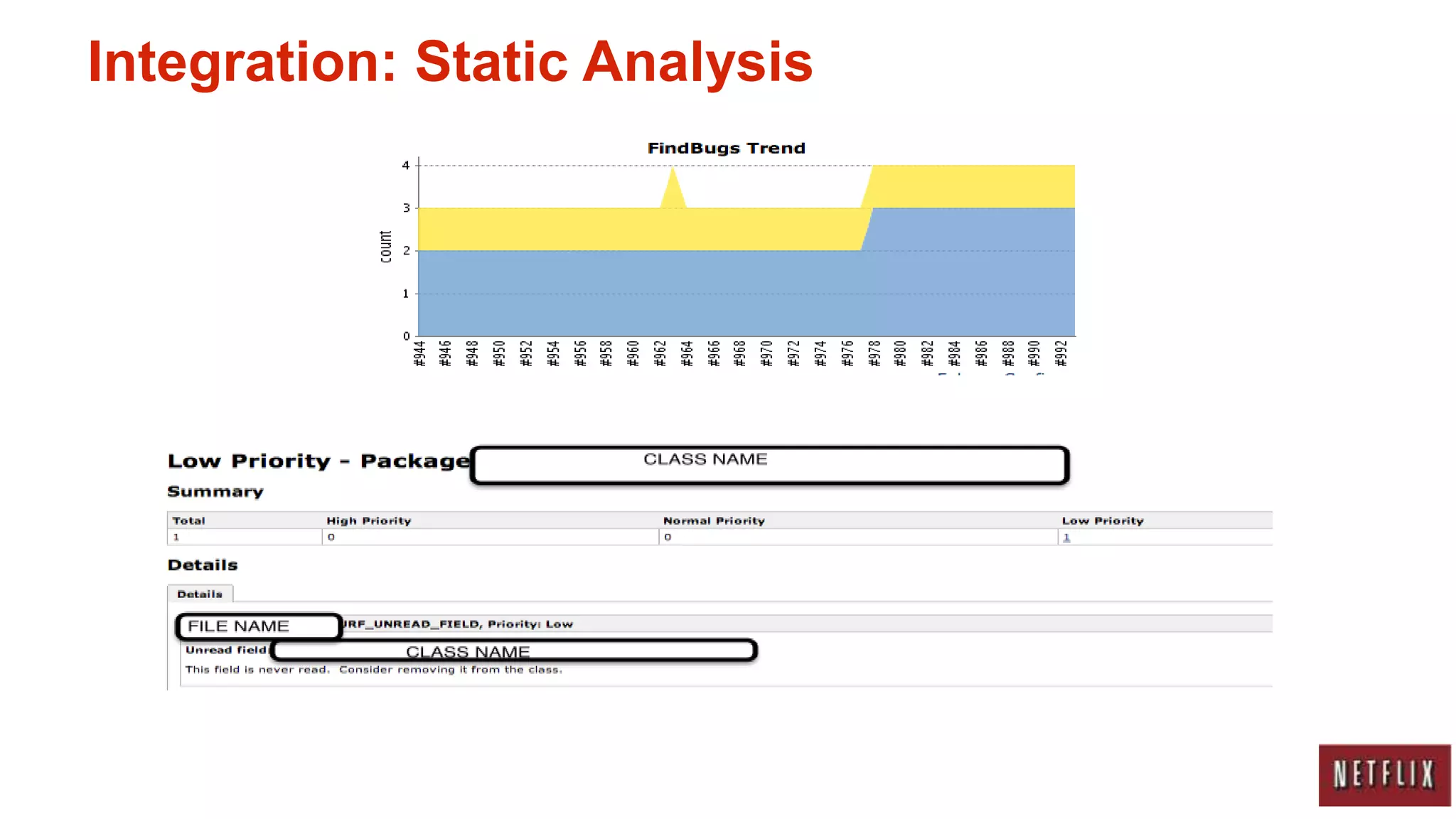
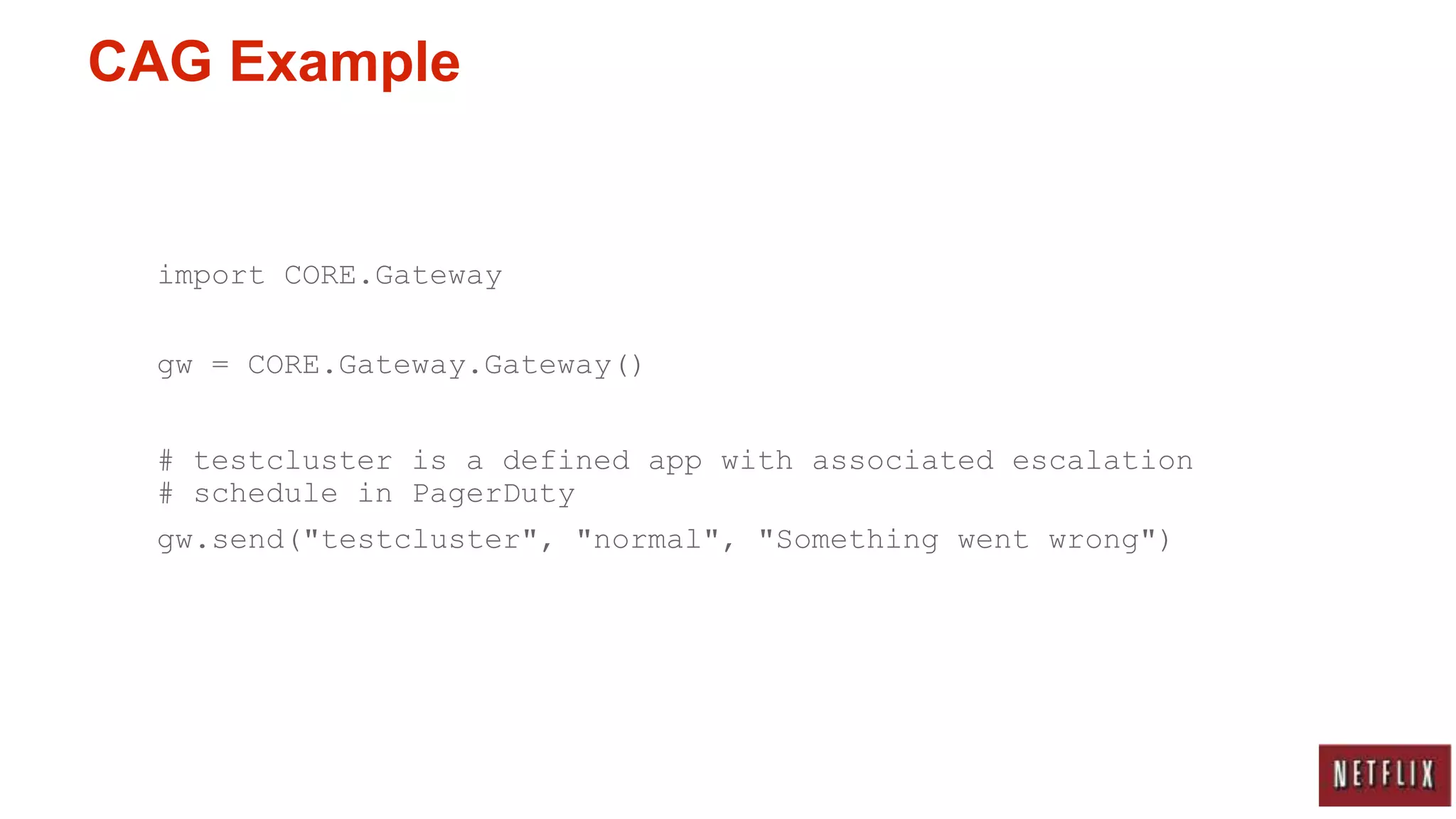
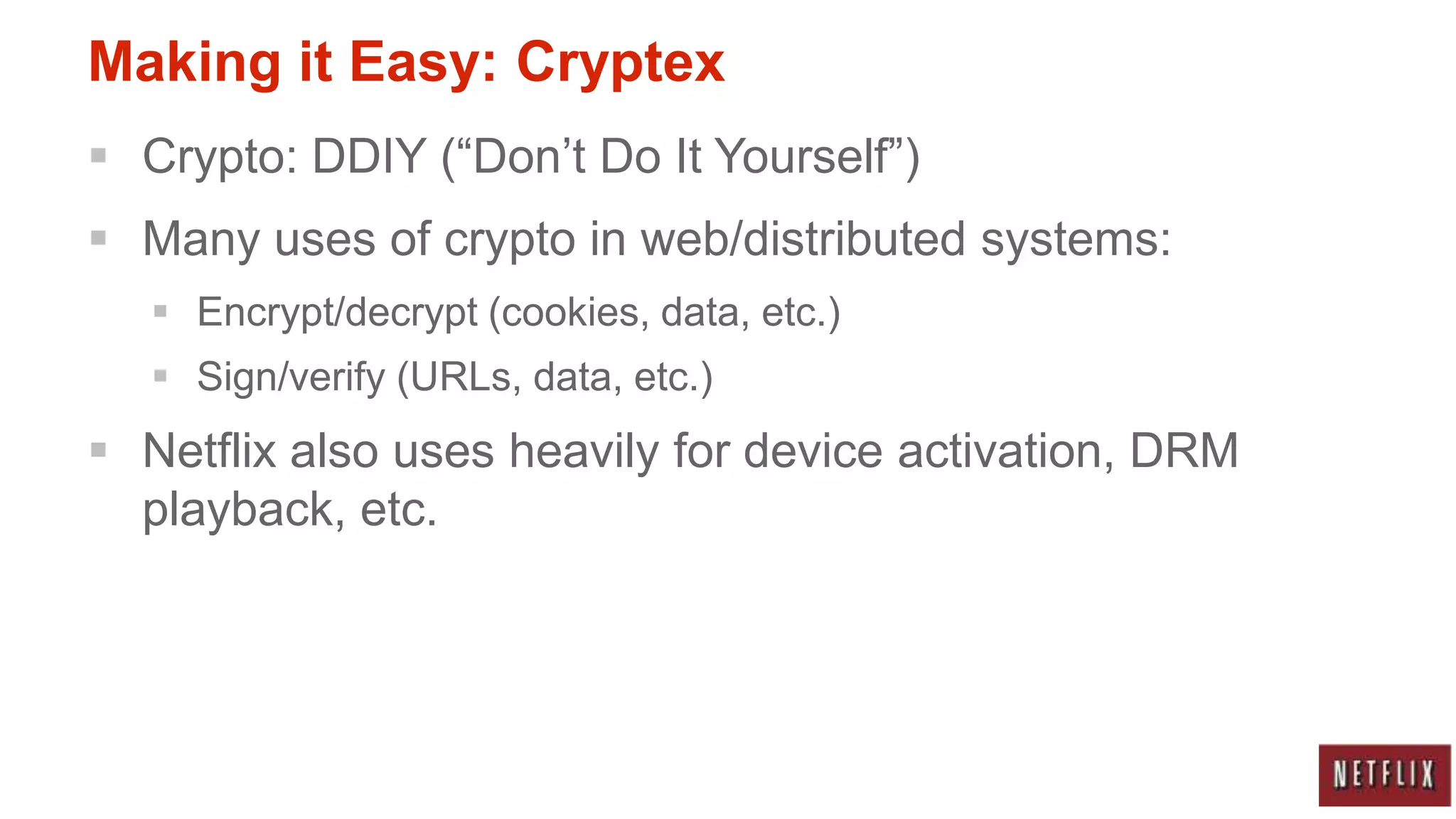
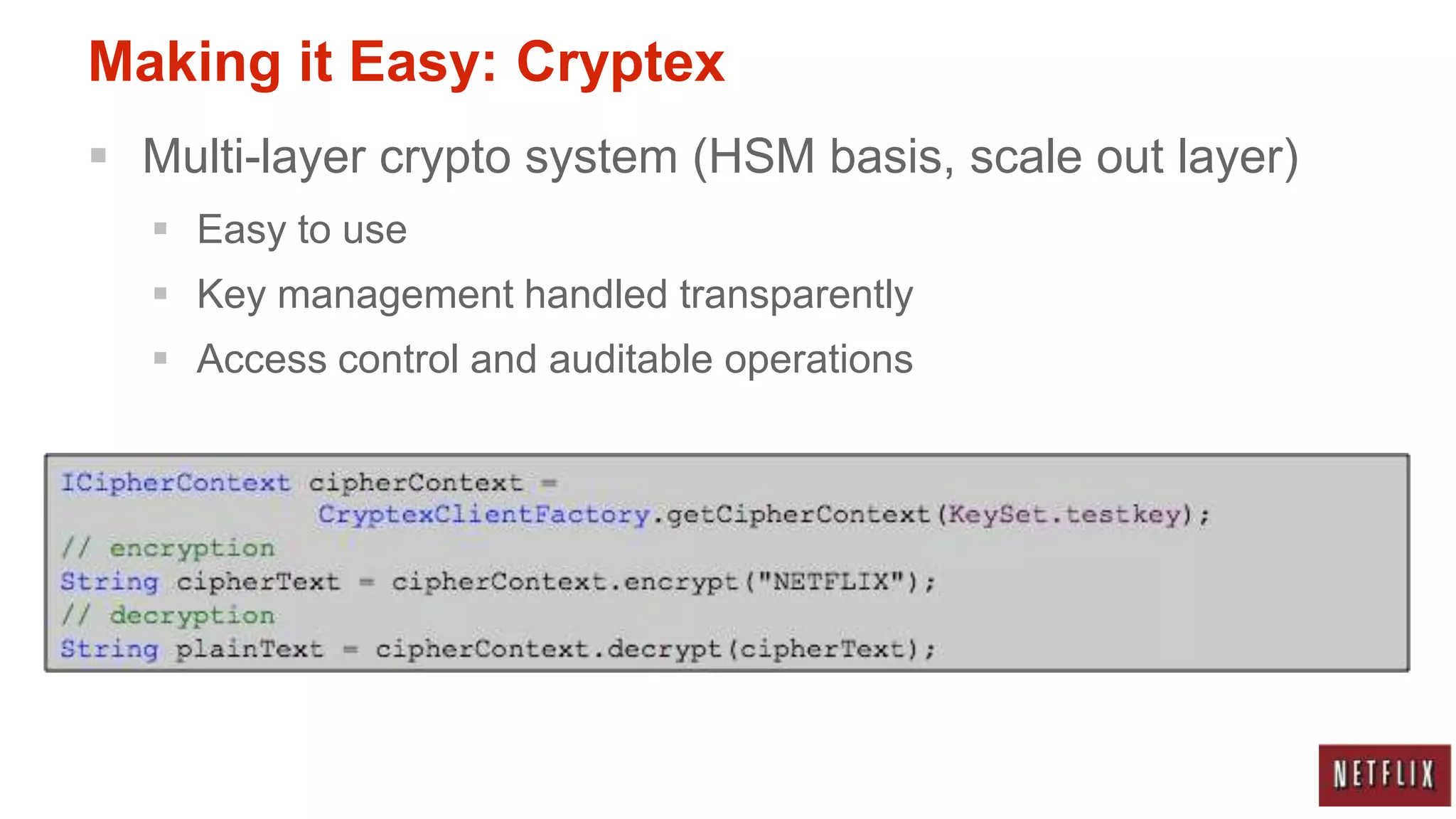
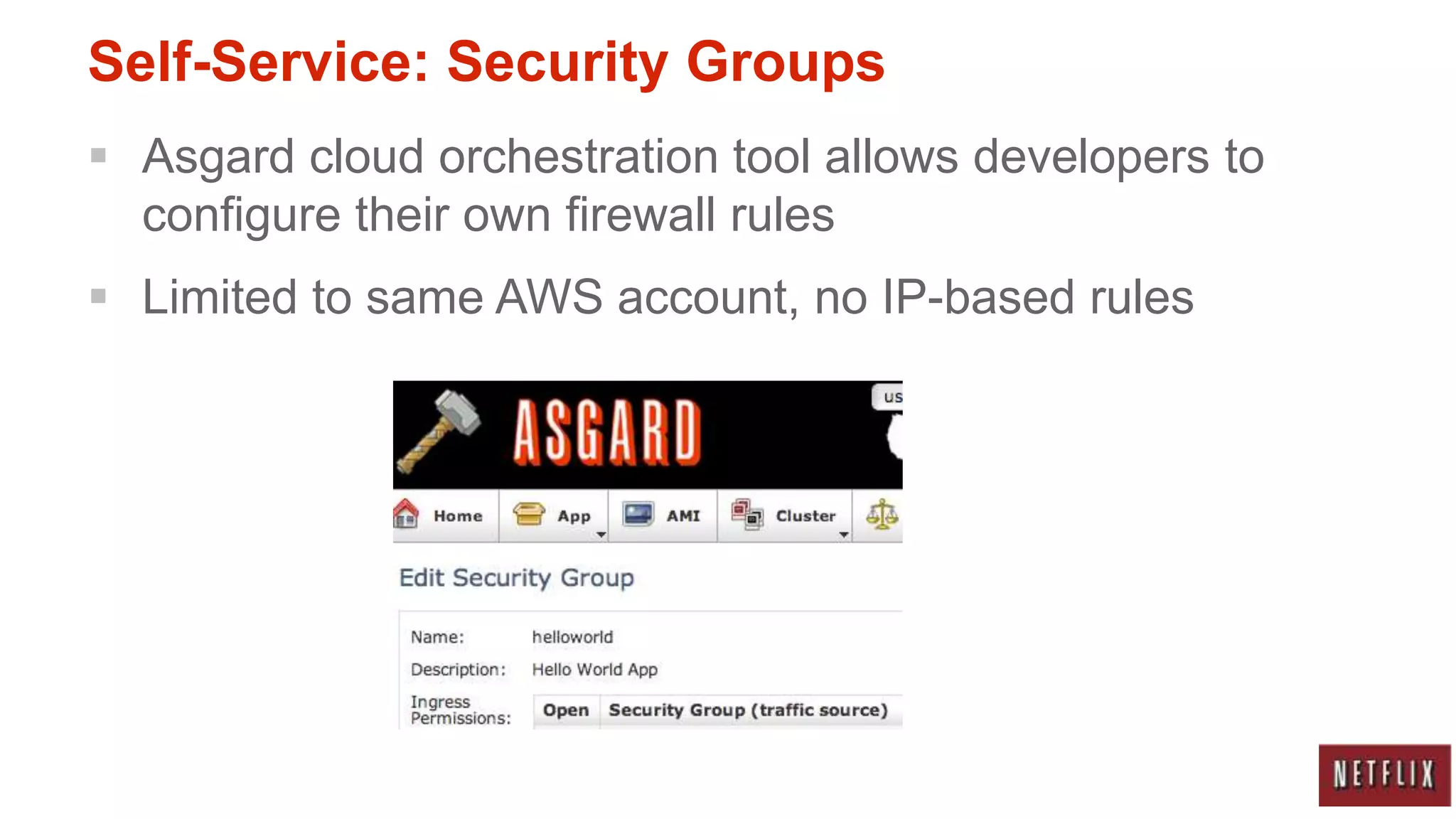
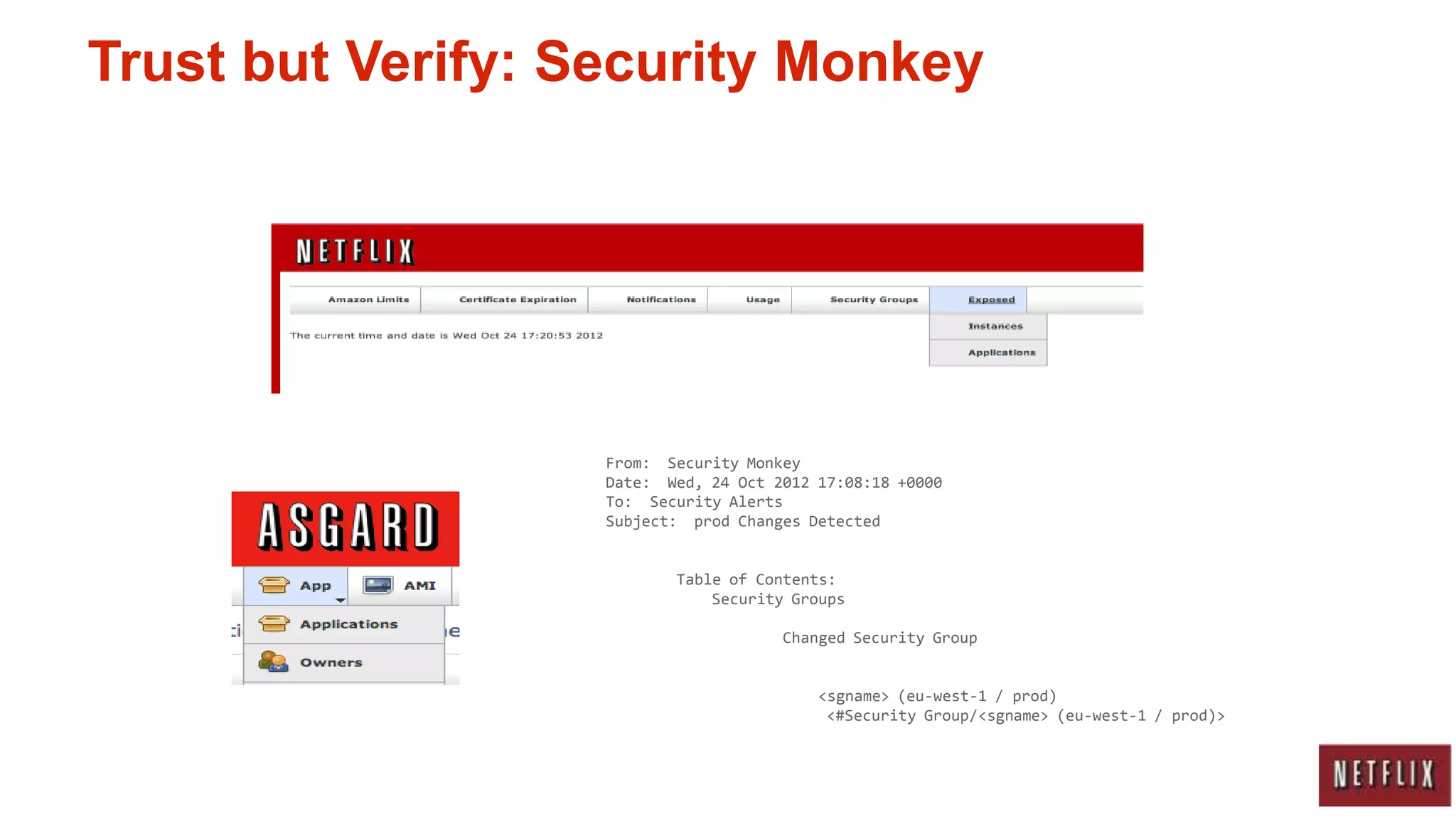
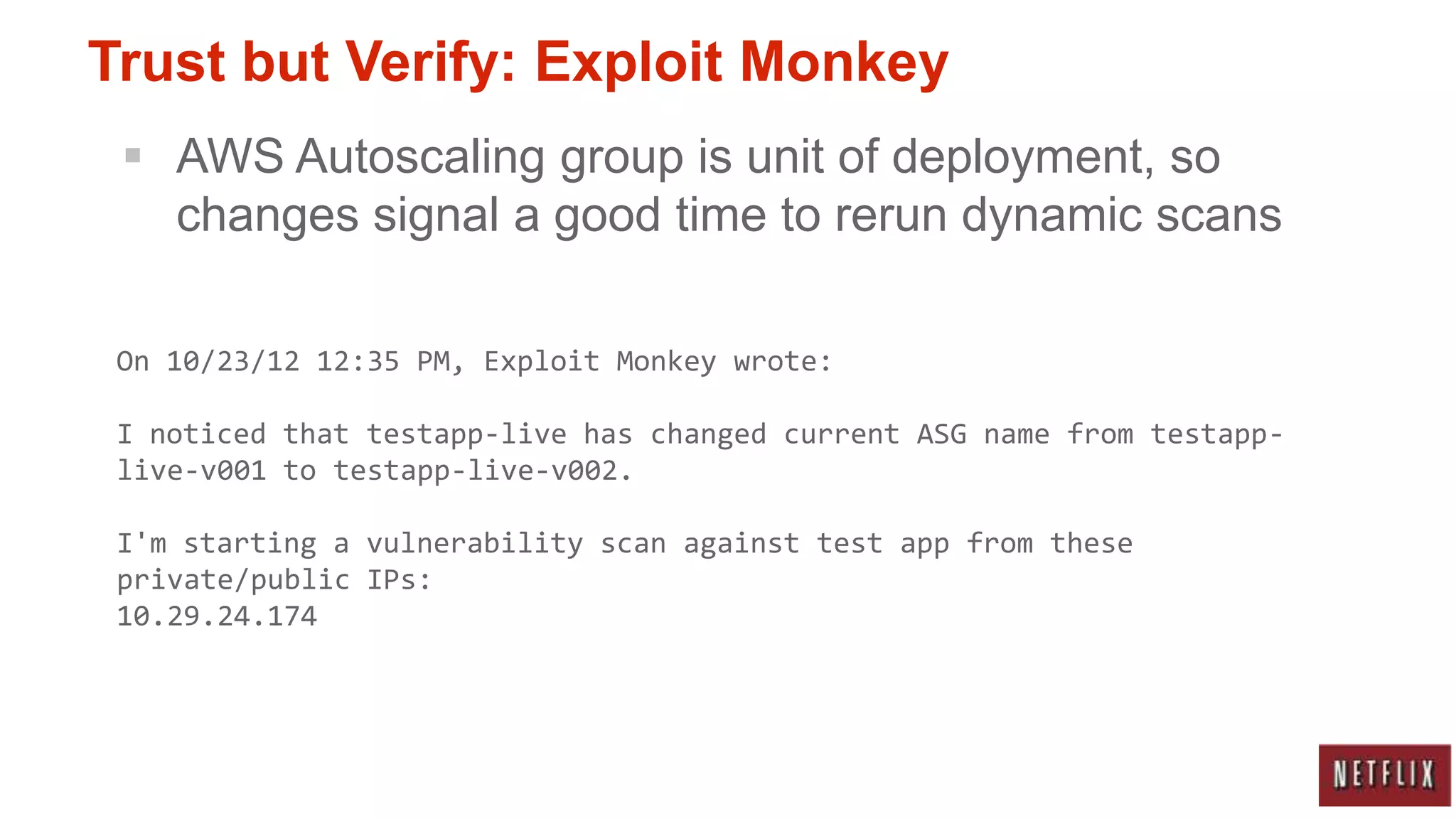
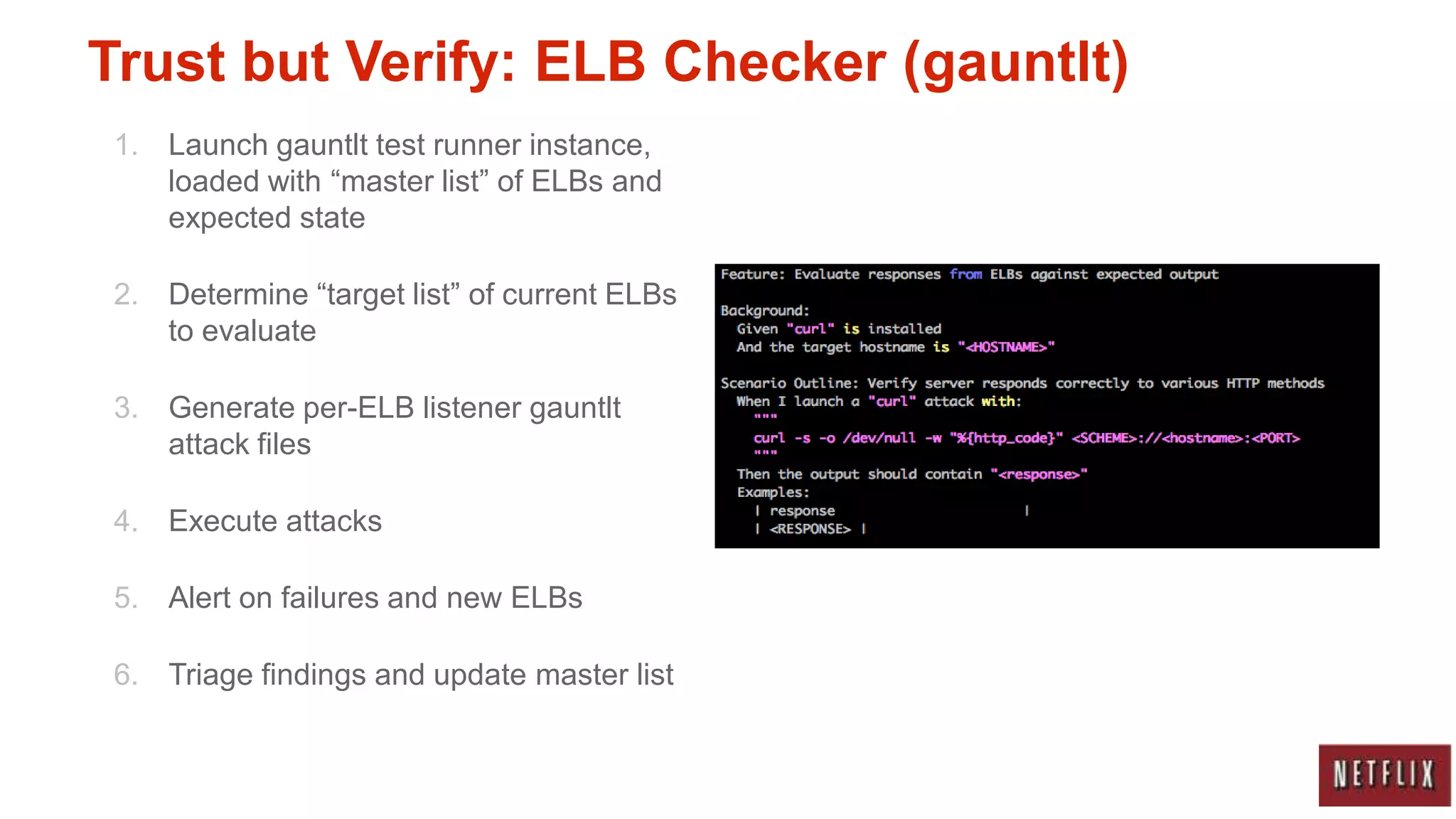
Netflix runs nearly all of its services on AWS and has adapted its security practices to fit its cloud-native architecture and DevOps model. Key aspects of Netflix's approach include integrating security tools into the development workflow, making secure options easy to use through self-service tools, and employing automated verification tools to monitor configurations while still trusting developers. This balance of empowering developers while verifying their work helps security scale alongside Netflix's dynamic cloud environment.